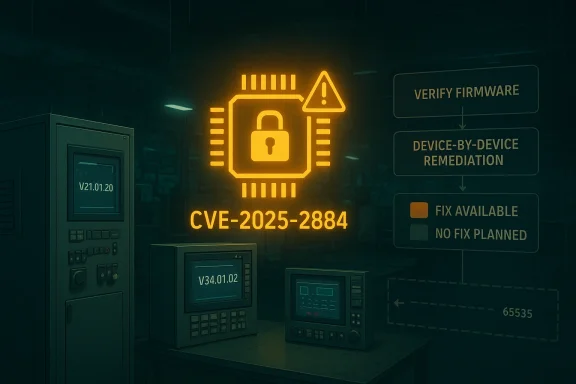
Siemens has published a broad TPM 2.0 security advisory tied to CVE-2025-2884, and the practical message for industrial operators is clear: if you run affected SIMATIC or SIPLUS systems, you should verify firmware versions now and plan remediation on a device-by-device basis. The flaw is an out-of-bounds read in the TCG TPM 2.0 reference implementation’s
The first thing to understand is that this is not a classic “Windows patch Tuesday” bug in the usual desktop sense. It is a firmware-level TPM issue that matters because Siemens’ industrial PCs, engineering devices, and communication nodes often depend on TPM-backed trust chains for secure boot, credential storage, device attestation, and system integrity. When a vulnerability lands in the TPM layer, the blast radius can extend well beyond the chip itself, because the TPM is often a foundational security primitive for the whole platform.
CVE-2025-2884 was assigned by the ecosystem after the Trusted Computing Group identified the issue in its TPM 2.0 reference implementation. TCG’s advisory says the bug can be triggered when inconsistent parameters are used in TPM 2.0 commands, and that the vulnerable code path may allow an attacker to read up to 65,535 bytes past the end of a buffer. That is an unusually concrete indication that the defect is a bounds-checking failure rather than a theoretical logic flaw, and it helps explain why Siemens is treating it as a meaningful industrial-security concern.
Siemens’ advisory is also notable for its mix of remediation states. Some devices can move to specific firmware baselines, such as V21.01.20, V29.01.09, V30.01.10, V32.01.09, or V34.01.02, depending on the product family. Other products are listed as currently no fix available or currently no fix planned, which is exactly the kind of split that complicates plant-floor security operations: one asset class gets a straightforward upgrade path, while another must rely on compensating controls and risk acceptance.
This advisory also reinforces a broader pattern that has become familiar across industrial and enterprise ecosystems: TPM issues are rarely isolated to one vendor. The same reference implementation can propagate across hardware lines, firmware branches, and OEM-customized builds. That means a single code-level flaw can end up producing a long tail of product-specific remediation timelines, which is why industrial operators often experience security incidents as portfolio management problems rather than one-off patch events.
The immediate technical lineage here traces back to the TCG TPM 2.0 reference implementation, which has become a common upstream code base for vendors that ship firmware with TPM functionality. The TCG advisory says the vulnerable code exists in revisions 1.83, 1.59, and 1.38, which tells us this is not a niche derivative issue but a standards-ecosystem concern. In other words, the same conceptual bug can surface in multiple downstream products if a vendor embeds or adapts the affected logic.
Siemens’ advisory republished by CISA is an example of how industrial vulnerability disclosure works in practice. A standards body identifies the defect, a product vendor maps it to its own hardware and firmware estate, and a national cyber agency republishes the information to improve operator visibility. That chain matters because it gives defenders a chance to correlate the low-level TPM problem with the actual Siemens product names they have in their inventories. Without that translation layer, many plant operators would know only that “TPM 2.0” is involved, not which specific SIMATIC or SIPLUS platforms are at risk.
It is also important to note the timing. TCG says its advisory was released on 2025-06-10, while Siemens’ advisory was published on 2026-04-14 and republicized by CISA on 2026-04-21. That gap suggests a long downstream validation and remediation cycle, which is common for industrial systems where firmware updates must be carefully qualified for stability, compatibility, and production continuity. Security teams often want immediate fixes, but operational technology environments usually demand a slower and more deliberate rollout.
In practice, that pushes defenders toward defense-in-depth:
The security implication of an out-of-bounds read is that the software may expose memory contents it should never reveal. Depending on what sits adjacent to the buffer, that can leak sensitive data, trigger instability, or create a denial-of-service condition. In a TPM context, the possibility of information disclosure is especially concerning because the whole purpose of the module is to protect secrets, not spill them.
The caution here is not to overstate exploitability. A medium score does not automatically imply widespread weaponization. It does, however, mean that defenders should not dismiss the bug as cosmetic, because the TPM’s role in trust establishment means even a limited disclosure path can have follow-on effects for credential protection, platform attestation, or attack chain enablement.
The most operationally important detail is that some families have clearly stated fixes, while others do not. For example, the advisory recommends updating IPC427E, IPC477E, IPC477E PRO, and SIPLUS IPC427E to V21.01.20 or later, and recommends V29.01.09, V30.01.10, V32.01.09, or V34.01.02 for several other product lines. By contrast, devices such as SIMATIC Field PG M5/M6, IPC627E/647E/677E/847E, IPC227E, IPC277E, and ITP1000 are listed as affected with no fix available or no fix planned.
The fact that Siemens says a new hardware version FS 05 for CN 4100 is not affected is also revealing. Hardware refreshes sometimes become the only practical long-term remediation for embedded products, especially when older designs are too close to end of support to justify a firmware rewrite. That reality is frustrating for operators, but it is a normal consequence of industrial asset lifecycles.
The practical challenge is that industrial fleets often contain older engineering stations alongside newer embedded PCs, and those machines may not have identical TPM firmware baselines. Organizations should not assume that a generic “update BIOS” process will solve the issue. They need to confirm the exact model string, TPM firmware package, and vendor-qualified update path for each device class. Assumptions are expensive in this part of the stack.
The likely short-term burden is triage. Teams need to decide whether the affected device is internet-facing, remotely reachable, physically accessible only, or heavily shared among technicians. Local-access vulnerabilities become more interesting when the machine is used by multiple staff members, remote support vendors, or contractors. The more people who can interact with the box, the more the local-only assumption starts to fray.
This split between errata and firmware is one reason industrial advisories can appear delayed or fragmented. A vendor may need to reconcile the standards fix with its own validation process, hardware constraints, or support commitments. In a fast-moving software shop, that would be a sprint. In industrial automation, it is a release-engineering effort with higher stakes and more compatibility testing.
The broader ecosystem also feels the effect because TPM implementations are reused across many product categories. A defect in the reference implementation creates a ripple through OEM hardware, operating systems, and management tools. That makes coordinated disclosure essential, but it also exposes a structural truth: the more standardized a security primitive becomes, the more a single coding error can propagate across the stack. Standardization reduces friction, but it can amplify shared risk.
The situation also creates opportunities for better asset governance, because it forces operators to refresh inventories and validate firmware baselines. That can improve security hygiene well beyond this one flaw. In many organizations, a TPM advisory becomes the catalyst for finally cleaning up stale asset records, orphaned engineering stations, and undocumented maintenance laptops.
A related risk is that local-access requirements can be underestimated. On paper, the attack is not remote, but on a shared engineering station or a device exposed to vendor maintenance access, local becomes a more elastic term. Another risk is operational complacency: teams may assume the TPM can be ignored because the issue is “only” an out-of-bounds read. In practice, memory disclosure bugs can become useful building blocks in larger attack chains.
Operators should also watch for clarifications around mitigation effectiveness. In some advisories, vendors later refine which network controls, privilege restrictions, or deployment patterns reduce exposure the most. Finally, organizations should monitor whether their own endpoint and industrial tooling reports any TPM anomalies after firmware updates, because even correct patches can introduce integration surprises in embedded fleets.
For defenders, the immediate task is straightforward: identify affected Siemens models, verify firmware status, and separate devices with available fixes from those that need compensating controls. The strategic task is harder: build a program that treats firmware trust anchors as first-class assets, not invisible plumbing. That shift in mindset is where resilience starts.
Looking ahead, this issue will likely be remembered less for its CVSS score than for what it reveals about industrial supply chains. A single bounds-checking error in a TPM reference implementation can ripple across embedded hardware, engineering workstations, and automation infrastructure. That is a reminder that in modern industrial IT, the smallest component can still carry the largest strategic weight.
Source: CISA Siemens TPM 2.0 | CISA
CryptHmacSign helper, with possible outcomes that include information disclosure or a denial of service of the TPM. Siemens says it has released fixes for some product lines, while other affected products currently have no fix or no planned fix yet.
 Overview
Overview
The first thing to understand is that this is not a classic “Windows patch Tuesday” bug in the usual desktop sense. It is a firmware-level TPM issue that matters because Siemens’ industrial PCs, engineering devices, and communication nodes often depend on TPM-backed trust chains for secure boot, credential storage, device attestation, and system integrity. When a vulnerability lands in the TPM layer, the blast radius can extend well beyond the chip itself, because the TPM is often a foundational security primitive for the whole platform.CVE-2025-2884 was assigned by the ecosystem after the Trusted Computing Group identified the issue in its TPM 2.0 reference implementation. TCG’s advisory says the bug can be triggered when inconsistent parameters are used in TPM 2.0 commands, and that the vulnerable code path may allow an attacker to read up to 65,535 bytes past the end of a buffer. That is an unusually concrete indication that the defect is a bounds-checking failure rather than a theoretical logic flaw, and it helps explain why Siemens is treating it as a meaningful industrial-security concern.
Siemens’ advisory is also notable for its mix of remediation states. Some devices can move to specific firmware baselines, such as V21.01.20, V29.01.09, V30.01.10, V32.01.09, or V34.01.02, depending on the product family. Other products are listed as currently no fix available or currently no fix planned, which is exactly the kind of split that complicates plant-floor security operations: one asset class gets a straightforward upgrade path, while another must rely on compensating controls and risk acceptance.
This advisory also reinforces a broader pattern that has become familiar across industrial and enterprise ecosystems: TPM issues are rarely isolated to one vendor. The same reference implementation can propagate across hardware lines, firmware branches, and OEM-customized builds. That means a single code-level flaw can end up producing a long tail of product-specific remediation timelines, which is why industrial operators often experience security incidents as portfolio management problems rather than one-off patch events.
Background
TPMs sit in a particularly sensitive place in modern computing. They help establish the root of trust for a system, and in industrial environments they can support secure boot, key sealing, attestation, and device identity functions that are used by automation platforms and engineering workstations alike. That is why TPM bugs tend to draw more attention than their technical severity score might suggest; even a medium-severity flaw can have outsized consequences if it undermines the trust anchor for a control system. Medium does not mean minor when the vulnerable component is part of the security substrate.The immediate technical lineage here traces back to the TCG TPM 2.0 reference implementation, which has become a common upstream code base for vendors that ship firmware with TPM functionality. The TCG advisory says the vulnerable code exists in revisions 1.83, 1.59, and 1.38, which tells us this is not a niche derivative issue but a standards-ecosystem concern. In other words, the same conceptual bug can surface in multiple downstream products if a vendor embeds or adapts the affected logic.
Siemens’ advisory republished by CISA is an example of how industrial vulnerability disclosure works in practice. A standards body identifies the defect, a product vendor maps it to its own hardware and firmware estate, and a national cyber agency republishes the information to improve operator visibility. That chain matters because it gives defenders a chance to correlate the low-level TPM problem with the actual Siemens product names they have in their inventories. Without that translation layer, many plant operators would know only that “TPM 2.0” is involved, not which specific SIMATIC or SIPLUS platforms are at risk.
It is also important to note the timing. TCG says its advisory was released on 2025-06-10, while Siemens’ advisory was published on 2026-04-14 and republicized by CISA on 2026-04-21. That gap suggests a long downstream validation and remediation cycle, which is common for industrial systems where firmware updates must be carefully qualified for stability, compatibility, and production continuity. Security teams often want immediate fixes, but operational technology environments usually demand a slower and more deliberate rollout.
Why TPM bugs hit industrial environments hard
A TPM defect can be difficult to exploit at scale, but that does not make it unimportant. The reason is that industrial assets frequently remain deployed for many years, and their firmware update cadence is much slower than that of consumer laptops or cloud servers. When a vendor says some models have no fix planned, that usually means the asset will live with compensating controls for the remainder of its operational life.In practice, that pushes defenders toward defense-in-depth:
- isolate the device from untrusted networks,
- reduce local attacker opportunities,
- harden administrative access,
- and keep firmware, OS, and management tooling in sync.
What the vulnerability actually is
At the code level, the issue is an out-of-bounds read in theCryptHmacSign helper function. Siemens summarizes the defect as a lack of validation between the signature scheme and the signature key’s algorithm, while TCG says the reference code failed to implement an appropriate consistency check. That is the sort of bug that typically appears when one input is assumed to match another, but the code never verifies the assumption before using the data.The security implication of an out-of-bounds read is that the software may expose memory contents it should never reveal. Depending on what sits adjacent to the buffer, that can leak sensitive data, trigger instability, or create a denial-of-service condition. In a TPM context, the possibility of information disclosure is especially concerning because the whole purpose of the module is to protect secrets, not spill them.
Why the CVSS score matters, but does not tell the whole story
The advisory assigns a CVSS v3.1 base score of 6.6, which lands in the medium range. The vector — AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:H — suggests local access, low complexity, low privileges, and a required user interaction step. That combination is a reminder that this is not an internet-worm style vulnerability. But in industrial fleets, “local access” can still be meaningful, especially on systems used for engineering, maintenance, diagnostics, or shared operator workstations.The caution here is not to overstate exploitability. A medium score does not automatically imply widespread weaponization. It does, however, mean that defenders should not dismiss the bug as cosmetic, because the TPM’s role in trust establishment means even a limited disclosure path can have follow-on effects for credential protection, platform attestation, or attack chain enablement.
A note on the “read up to 65535 bytes” detail
TCG’s advisory includes an unusually specific impact note: the attacker may be able to read up to 65535 bytes beyond the end of the buffer passed toExecuteCommand. That figure should not be read as a guarantee of easy exploitation, but it does indicate that the flaw was serious enough for the standards body to spell out the potential memory over-read range. In security terms, that is a red flag because it implies the bug is not a tiny fencepost error; it is a potentially substantial boundary failure.Affected Siemens product families
Siemens’ product mapping is broad, and that breadth is the real operational story. The advisory names SIMATIC CN 4100, SIMATIC Field PG M5, SIMATIC Field PG M6, multiple SIMATIC IPC families, and SIPLUS IPC427E as affected. For some devices, every version is impacted; for others, only firmware below a specific threshold is vulnerable. That split tells us Siemens’ TPM implementation is not monolithic across the portfolio.The most operationally important detail is that some families have clearly stated fixes, while others do not. For example, the advisory recommends updating IPC427E, IPC477E, IPC477E PRO, and SIPLUS IPC427E to V21.01.20 or later, and recommends V29.01.09, V30.01.10, V32.01.09, or V34.01.02 for several other product lines. By contrast, devices such as SIMATIC Field PG M5/M6, IPC627E/647E/677E/847E, IPC227E, IPC277E, and ITP1000 are listed as affected with no fix available or no fix planned.
Fixable versus non-fixable product groups
That distinction matters because it changes the remediation playbook. Where firmware is available, the decision is a classic lifecycle question: validate compatibility, test regression behavior, then roll the update in a controlled window. Where no fix exists, the decision becomes one of containment rather than elimination. You are no longer managing a patch; you are managing exposure.The fact that Siemens says a new hardware version FS 05 for CN 4100 is not affected is also revealing. Hardware refreshes sometimes become the only practical long-term remediation for embedded products, especially when older designs are too close to end of support to justify a firmware rewrite. That reality is frustrating for operators, but it is a normal consequence of industrial asset lifecycles.
Remediation and version targeting
Siemens’ firmware guidance is specific enough to be useful, but only if organizations map product instances accurately. The advisory points administrators toward the Siemens support release package at 109763408 and gives version cutoffs by family. In a mixed environment, that means patching is not one action; it is a matrix of model, firmware, and deployment constraints.The practical challenge is that industrial fleets often contain older engineering stations alongside newer embedded PCs, and those machines may not have identical TPM firmware baselines. Organizations should not assume that a generic “update BIOS” process will solve the issue. They need to confirm the exact model string, TPM firmware package, and vendor-qualified update path for each device class. Assumptions are expensive in this part of the stack.
A defensible rollout sequence
A sensible sequence for defenders would look like this:- Inventory all Siemens devices that expose TPM 2.0 functionality.
- Identify which product family and firmware branch each device uses.
- Check whether the product has a fixed version or only compensating controls.
- Test the vendor update in a controlled maintenance window.
- Roll out the change in phases, prioritizing exposed or high-value assets.
Why version pinning matters
Version pinning is especially important here because the advisory gives multiple fixed baselines rather than a single universal build. A security team that only sees “Siemens TPM 2.0” may miss the fact that one platform needs V21.01.20, while another needs V34.01.02. The safest interpretation is that the fix is embedded in product-specific firmware generations, not in a single cross-platform package.Operational impact for enterprises and plants
For enterprise IT, the impact is mostly about trust, credential protection, and system hardening. For plant-floor operators, the concern is broader: TPM instability can affect engineering stations, industrial PCs, and the devices that support automation lifecycles. The TPM is often invisible when everything works, which is exactly why a TPM issue can be disruptive when it surfaces.The likely short-term burden is triage. Teams need to decide whether the affected device is internet-facing, remotely reachable, physically accessible only, or heavily shared among technicians. Local-access vulnerabilities become more interesting when the machine is used by multiple staff members, remote support vendors, or contractors. The more people who can interact with the box, the more the local-only assumption starts to fray.
Consumer impact is limited, but not zero
This is not a mass consumer vulnerability in the usual sense, but the lessons spill over into mainstream Windows ecosystems. TPM issues can show up as unexplained boot, attestation, or security-module behavior, and users often blame the OS when the fault lies lower in firmware. Siemens’ advisory is therefore a reminder that endpoint security depends on coordinated firmware hygiene, not just antivirus, patching, or OS baselines.Why the TCG errata path matters
TCG’s remediation guidance points operators to Errata Version 2.0 or higher for revision 1.83, Errata Version 1.7 or higher for revision 1.59, and Errata Version 1.15 or higher for revision 1.38. That matters because standards-driven fixes often arrive as specification updates before they appear in downstream vendor firmware. The standards body is effectively saying, “This is the right long-term behavior model,” while vendors must still implement and ship the code in their own release trains.This split between errata and firmware is one reason industrial advisories can appear delayed or fragmented. A vendor may need to reconcile the standards fix with its own validation process, hardware constraints, or support commitments. In a fast-moving software shop, that would be a sprint. In industrial automation, it is a release-engineering effort with higher stakes and more compatibility testing.
The standards-to-firmware pipeline
The pipeline usually works like this:- a vulnerability is discovered in reference code,
- the standards group publishes guidance or errata,
- vendors assess impact on their products,
- firmware is revised and signed,
- and customers get a model-specific update.
Competitive and ecosystem implications
There is a competitive angle here too. Vendors that can ship patched firmware quickly gain trust with industrial customers who increasingly evaluate cybersecurity posture as part of procurement. Conversely, vendors that leave multiple families in a “no fix available” state may face tougher questions about support depth, hardware refresh strategy, and product longevity. Security advisories are no longer just technical notices; they are part of a vendor’s credibility profile.The broader ecosystem also feels the effect because TPM implementations are reused across many product categories. A defect in the reference implementation creates a ripple through OEM hardware, operating systems, and management tools. That makes coordinated disclosure essential, but it also exposes a structural truth: the more standardized a security primitive becomes, the more a single coding error can propagate across the stack. Standardization reduces friction, but it can amplify shared risk.
What rivals may do differently
Competing industrial vendors will likely use advisories like this to emphasize their own firmware update cadence, hardware isolation model, or TPM supply-chain choices. Some may point to proprietary implementations; others may stress faster validation cycles. In the industrial market, these details can influence buying decisions almost as much as raw throughput or interface count.Strengths and Opportunities
Siemens’ handling of the issue shows several strengths that matter to defenders. The advisory is specific, product-mapped, and versioned, which makes it actionable rather than generic. It also acknowledges where fixes are unavailable, which is more honest than pretending every affected platform has a clean patch path.The situation also creates opportunities for better asset governance, because it forces operators to refresh inventories and validate firmware baselines. That can improve security hygiene well beyond this one flaw. In many organizations, a TPM advisory becomes the catalyst for finally cleaning up stale asset records, orphaned engineering stations, and undocumented maintenance laptops.
- Clear version-specific remediation improves operational planning.
- The advisory distinguishes between fixable and non-fixable product lines.
- The FS 05 hardware note gives CN 4100 owners a long-term path.
- The vulnerability is documented by both TCG and Siemens, which strengthens confidence in the technical characterization.
- The CISA republication increases visibility for industrial defenders.
- The issue reinforces the value of defense-in-depth and network segmentation.
- The advisory gives teams enough detail to build a targeted response matrix.
Risks and Concerns
The biggest concern is that some affected devices have no fix available, which leaves operators dependent on compensating controls for an indefinite period. That is uncomfortable because TPM issues are foundational; you cannot simply firewall away every consequence of a compromised trust anchor. The second concern is that industrial environments often have long replacement cycles, so “eventual hardware refresh” may not be a realistic near-term mitigation.A related risk is that local-access requirements can be underestimated. On paper, the attack is not remote, but on a shared engineering station or a device exposed to vendor maintenance access, local becomes a more elastic term. Another risk is operational complacency: teams may assume the TPM can be ignored because the issue is “only” an out-of-bounds read. In practice, memory disclosure bugs can become useful building blocks in larger attack chains.
- Some product families have no fix planned.
- The flaw can enable information disclosure and denial of service.
- Local-access bugs are still dangerous on shared industrial systems.
- Firmware updates may require extensive compatibility testing.
- Older assets may stay exposed until their hardware refresh cycle.
- A medium CVSS score can cause underreaction in security programs.
- TPM issues can affect trust chains, not just one isolated function.
What to Watch Next
The next thing to watch is whether Siemens issues additional firmware branches for currently unpatched product families. That would not be surprising, because industrial vendors often continue refining remediation after the first advisory publication. A second priority is whether other OEMs that reuse the same TPM reference code publish parallel notices. That would confirm the issue’s ecosystem breadth and help defenders assess whether Siemens is an outlier or one node in a wider wave.Operators should also watch for clarifications around mitigation effectiveness. In some advisories, vendors later refine which network controls, privilege restrictions, or deployment patterns reduce exposure the most. Finally, organizations should monitor whether their own endpoint and industrial tooling reports any TPM anomalies after firmware updates, because even correct patches can introduce integration surprises in embedded fleets.
- Additional Siemens firmware releases for currently unpatched models.
- Vendor confirmations from other TPM-based hardware makers.
- Follow-up guidance from CERT/CC or other coordination bodies.
- Any reports of post-update compatibility or boot issues.
- Evidence of real-world exploitation, if it emerges.
- New hardware revisions that silently supersede affected designs.
Looking Ahead
The larger lesson from CVE-2025-2884 is that industrial cybersecurity is increasingly about the integrity of shared foundational components. TPM firmware is one of those layers that many organizations never inspect until something goes wrong, yet it underpins the security claims of the whole machine. That makes advisories like this especially important, even when the headline severity is not extreme.For defenders, the immediate task is straightforward: identify affected Siemens models, verify firmware status, and separate devices with available fixes from those that need compensating controls. The strategic task is harder: build a program that treats firmware trust anchors as first-class assets, not invisible plumbing. That shift in mindset is where resilience starts.
Looking ahead, this issue will likely be remembered less for its CVSS score than for what it reveals about industrial supply chains. A single bounds-checking error in a TPM reference implementation can ripple across embedded hardware, engineering workstations, and automation infrastructure. That is a reminder that in modern industrial IT, the smallest component can still carry the largest strategic weight.
Source: CISA Siemens TPM 2.0 | CISA