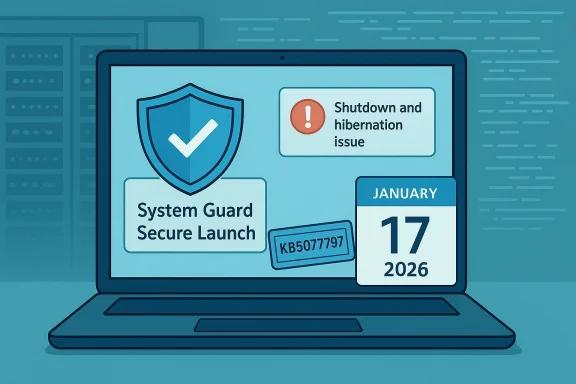
Microsoft’s first Windows 11 update of 2026 disrupted shutdown behavior on a narrow but important slice of devices and forced an out‑of‑band emergency fix hours later; the January 13 Patch Tuesday cumulative (notably KB5073455 for Windows 11 23H2) introduced a configuration‑dependent regression that made some systems reboot instead of powering off or hibernating, and Microsoft shipped targeted OOB packages (including KB5077797) on January 17 to restore expected power‑state and remote‑access behavior.
Background / Overview
The January 2026 Patch Tuesday wave followed Microsoft’s long‑standing monthly cadence but produced two distinct regressions that had immediate operational impact: a shutdown/hibernate regression tied to System Guard Secure Launch on Windows 11 version 23H2, and a broader Remote Desktop / Cloud PC authentication regression affecting several Windows servicing branches and remote‑access clients. Microsoft documented the problems and issued out‑of‑band (OOB) cumulative updates on January 17 to remediate the issues.These events illustrate the trade‑offs in modern platform servicing: monthly security rollups must be deployed quickly to protect customers, but changes that touch early‑boot or authentication subsystems can interact with firmware, virtualization, and cloud brokers in ways that are difficult to reproduce in test labs. The incident affected predominantly enterprise and IoT fleets where Secure Launch is enforced, while consumer devices were comparatively less likely to encounter the fault.
What broke: the two regressions explained
1) Restart instead of Shutdown / Hibernation (Secure Launch interaction)
- Symptom: After installing the January 13 cumulative (KB5073455 on 23H2), some Windows 11 devices configured with System Guard Secure Launch restarted when users selected Shut down or attempted Hibernate, rather than remaining powered off or entering S4/hibernation. In many cases the UI showed a normal shutdown sequence but the machine returned to the sign‑in surface.
- Scope: The behavior was configuration dependent — primarily observed on Windows 11, version 23H2 devices where Secure Launch is enabled (commonly enforced in Enterprise and IoT images). Consumer Home and most Pro installs (which typically do not enable Secure Launch by default) were far less likely to be affected.
- Technical anatomy (plain language): Secure Launch is a virtualization‑based early‑boot hardening feature that changes boot and power‑transition semantics. Windows updates use multi‑phase servicing that stages files during runtime and commits changes during offline transitions (shutdown/reboot). In affected configurations the servicing orchestration failed to preserve the user’s final power intent across the Secure Launch boundary, and the system fell back to a safe but incorrect action: performing a restart so offline commits would complete reliably. That safe fallback violated the explicit shutdown/hibernate request and produced the restart behavior.
2) Remote Desktop / Cloud PC authentication failures
- Symptom: Separate from the power‑state issue, the January rollup introduced authentication failures and repeated credential prompts during Remote Desktop connections, affecting the modern Windows Remote Desktop App and some Cloud PC / Azure Virtual Desktop scenarios. These failures blocked remote sessions for many users and administrators until a fix was deployed.
- Scope: This regression was broader in servicing scope — observed across Windows 11 24H2/25H2 builds, select Windows 10 ESU branches, and Windows Server SKUs — making it an urgent operational problem for organizations relying on remote access and Cloud PC services.
Timeline (verified vendor timeline and community reporting)
- January 13, 2026 — Microsoft published the January Patch Tuesday cumulative updates, including KB5073455 for Windows 11, version 23H2 (OS Build 22631.6491) and companion LCUs for newer servicing branches.
- January 13–16, 2026 — Administrators, telemetry, and community channels reported two repeatable regressions: the Secure Launch restart‑instead‑of‑shutdown symptom and Remote Desktop authentication failures. Microsoft logged the incidents in Release Health and began triage.
- January 17, 2026 — Microsoft shipped out‑of‑band (OOB) remedial cumulative updates (for example KB5077797 for 23H2 and KB5077744 for 24H2/25H2) that bundled the January fixes and added the emergency corrections to restore both correct power‑state handling and remote‑access authentication. Administrators were advised to deploy the OOB packages to affected systems.
What Microsoft released and how to get it
Microsoft delivered targeted OOB cumulative packages that are cumulative (they include the January fixes plus corrective code). The notable packages reported in vendor notes and community reporting include:- KB5073455 — January 13 LCU for Windows 11, version 23H2 (the update that introduced the Secure Launch regression in certain configurations).
- KB5077797 — January 17 OOB cumulative for Windows 11, 23H2; explicitly includes fixes for the Secure Launch restart‑instead‑of‑shutdown regression and Remote Desktop sign‑in failures.
- KB5077744 — companion OOB for Windows 11 24H2/25H2 branches addressing Remote Desktop authentication regressions and including January fixes.
Caveat: Some early independent articles occasionally referenced incorrect KB numbers; reconcile vendor KB listings with Microsoft’s official release notes and Release Health entries before deploying. If a secondary source names a KB that doesn’t match Microsoft’s pages, treat that as a reporting error and verify against Microsoft’s update documentation.
Immediate mitigation and remediation guidance
The practical steps below are prioritized for IT teams and advanced users managing Windows fleets; domestic home users can follow the simplified end‑user advice.For administrators (enterprise / managed fleets)
- Inventory and triage
- Identify devices that have the January LCU installed and check whether System Guard Secure Launch is enabled. Use msinfo32 or OS provisioning reports to detect Secure Launch status.
- Flag devices in critical roles (kiosks, point‑of‑sale, field service devices, test rigs) where deterministic power state matters most.
- Pilot the OOB package
- Validate the remedial OOB (KB5077797 / KB5077744) in a representative pilot ring that includes OEM/firmware diversity; Secure Launch interacts with firmware, so different OEM firmware versions may behave differently.
- Deploy with rollback plan
- Roll out the OOB to progressively larger rings once pilot validation is successful. Keep update rollback/playbooks ready in case of follow‑on regressions.
- For cloud / AVD authentication regressions, prefer Known Issue Rollback (KIR) guidance where applicable rather than uninstalling entire LCUs. KIR can be less disruptive for large-scale environments.
- Communicate with users
- Notify impacted end users about the issue and the interim workaround (below), and instruct them to save work frequently until fixes are applied.
- Backup and change control
- Back up critical user data and PST files before mass remediation operations that could affect mail clients or data. Test business‑critical apps in pilot rings.
For individual end users and help‑desk responders
- Interim workaround (shutdown): If a device exhibits the restart‑instead‑of‑shutdown behavior, run an elevated Command Prompt and execute:
- shutdown /s /t 0
- That command forces an immediate, deterministic shutdown and is the vendor‑documented interim method. Note: Microsoft warned that there was no workaround for hibernation at the time of the advisory, so avoid relying on hibernation until the remedial update is applied.
- If Remote Desktop / Cloud PC authentication fails:
- Check for the OOB remedial package and apply it if your device’s servicing branch is covered.
- For AVD scenarios, follow Microsoft’s guidance for KIR or temporary workarounds to restore connectivity without uninstalling the entire LCU.
Detection: how to confirm exposure
- Check OS build and update history for the January LCU (KB5073455 or the branch‑appropriate package). Verify on each endpoint whether the January LCU is installed and whether the OOB remedial has been applied.
- Confirm Secure Launch status:
- Open System Information (msinfo32).
- In the System Summary pane, look for entries that indicate System Guard Secure Launch, VBS / Virtualization‑Based Security status, and related platform security features.
- Devices showing Secure Launch enabled are the primary risk group for the restart behavior.
- For fleets: export telemetry and patch‑compliance reports and cross‑reference with firmware/OEM model reports to identify at‑risk populations (kiosks, IoT, secured imaging).
Testing and deployment guidance (operational playbook)
- Build test rings that include:
- Representative OEM firmware versions (conservative + recent).
- Enterprise images with Secure Launch enabled.
- Cloud PC / AVD client variants used by your organization.
- Test checklist:
- Verify shutdown and hibernation behavior after staging updates; test both UI‑initiated and command‑line shutdowns.
- Validate Remote Desktop and Cloud PC authentication flows post‑update.
- Monitor device boot logs, servicing logs, and Event Viewer entries for errors related to servicing, winlogon, or virtualization boundaries.
- Rollback planning:
- Document rollback steps for each management channel (WSUS, SCCM, Intune).
- Ensure offline access or local admin recovery paths in case remote management is impaired by RDP issues.
- Post‑deployment monitoring:
- Watch for anomalous battery drain reports, scheduled‑task failures, and remote‑access help‑desk tickets as primary signals of residual impact.
Critical analysis: strengths and risks of Microsoft’s response
Strengths
- Rapid detection and response: Microsoft’s move to publish OOB cumulative fixes within four days demonstrates responsiveness and an ability to coordinate emergency servicing across multiple branches quickly. It preserved the security fixes shipped with the January rollup while surgically addressing the regressions.
- Vendor transparency: Microsoft recorded the known issues and published interim guidance (including a documented command‑line workaround) to reduce end‑user impact while fixes were prepared. That clarity helped administrators triage and prioritize remediation.
- Granular fixes: Using targeted OOB packages allowed Microsoft to address the regressions without forcing rollback of the entire monthly security wave, maintaining protection against the vulnerabilities addressed in the January cumulative.
Risks and weaknesses
- Regression surface area: The incident highlights an ongoing risk with low‑level security hardening features (like Secure Launch) — features that change boot semantics increase the test surface and can create configuration‑dependent regressions that are hard to catch in standard validation suites. Enterprises that enforce Secure Launch at scale must accept a higher testing burden.
- Operational friction: The restart‑instead‑of‑shutdown behavior, although limited in scope, had disproportionate operational consequences for devices that require deterministic power states — kiosks, PoS systems, field devices, and test automation rigs. The interim workaround forced help‑desk involvement and extra communication overhead.
- Dependency on fast OOB fixes: Frequent OOB releases can strain enterprise change‑management processes; administrators must balance speed of deployment with careful testing, and episodes like this reinforce the need for robust pilot testing and rollback capabilities.
Broader implications: patching, hardening, and testing in 2026
This incident is not an outlier; it is an operational stress test for modern Windows servicing and security hardening:- Security vs reliability trade‑off: Deep platform hardening (VBS, Secure Launch, Secured-core features) raises baseline security but also increases the chance that servicing changes will produce unforeseen interactions with firmware and virtualization. Organizations must accept that upgrades to security posture demand commensurate investments in integration testing.
- Inventory and telemetry matter: Organizations that maintain detailed inventories of which devices run Secure Launch, firmware levels, and OEM images will recover faster from configuration‑dependent regressions. Passive telemetry that tracks power‑state transitions and remote‑access failures can serve as early warning signals.
- Update rings are essential: The incident reinforces the value of staged update rings and pilot cohorts that include the most constrained device profiles (kiosks, IoT, secured images) — those are the likely early casualties of this class of regression.
Practical checklist (what organizations should do now)
- Inventory endpoints for January LCU presence and Secure Launch status.
- Prioritize pilot validation of the OOB remedial packages (KB5077797 / KB5077744) on devices that match the at‑risk fingerprint.
- Apply remedial OOB updates to production rings after successful pilot testing.
- Communicate interim workarounds (shutdown /s /t 0) to impacted users and support staff.
- Monitor power‑state, battery drain, and remote‑access telemetry for residual anomalies.
- Update testing matrices to include Secure Launch and early‑boot variations with OEM firmware permutations.
Flagging unverifiable or uncertain claims
- Some early news summaries and social posts reported incorrect KB numbers or conflated unrelated KBs with the January 2026 wave. Any KB reference used in management scripts should be verified directly against Microsoft’s official update documentation and Release Health before deployment. Where independent outlets disagree, prefer vendor KB entries.
- While community telemetry strongly points to Secure Launch as the immediate trigger for the restart regression, the exact low‑level race conditions involve firmware/driver interplay that can vary by OEM. Expect variation in behavior across hardware models; do not assume identical results across a heterogeneous fleet.
Conclusion
The January 2026 Windows servicing episode is a compact case study in the operational realities of modern platform security: rapid security delivery matters, but so does the ability to detect and surgically remediate configuration‑dependent regression quickly. Microsoft’s emergency out‑of‑band response (delivering remedial fixes such as KB5077797 on January 17) addressed the immediate symptoms — restoring correct shutdown/hibernate semantics on Secure Launch systems and repairing Remote Desktop authentication for affected branches — but the event also reinforces practical lessons for administrators: inventory, pilot, communicate, and maintain robust rollback and monitoring capabilities.For administrators the immediate priorities are clear: inventory devices for exposure, validate the remedial OOB in representative pilot rings (including firmware and OEM diversity), and deploy the fix to affected rings while communicating interim workarounds to end users. For organizations pursuing advanced hardening like Secure Launch, this incident is a reminder that hardening is not a set‑and‑forget activity — it increases the required depth of testing and the operational maturity of update processes.
Apply the OOB updates after validation, monitor closely for residual issues, and treat this episode as a prompt to strengthen test coverage for early‑boot features going forward.
Source: Mezha The first Windows 11 update in 2026 caused PC shutdown problems – Microsoft has already released an emergency patch