Millions of Windows gamers woke up to worse frame rates and unexplained stutters after January’s cumulative, and the fastest way back to smooth play is methodical: confirm the cause, update or reinstall the GPU driver cleanly, and only use Windows rollback as a last‑resort temporary step while watching for a vendor fix.
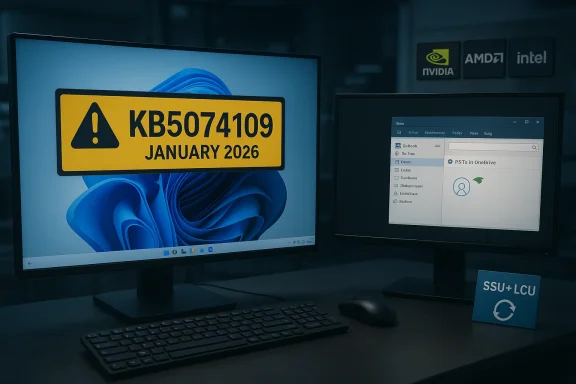
Microsoft’s January 13, 2026 cumulative update for Windows 11—published as KB5074109 and delivering OS builds 26200.7623 (25H2) and 26100.7623 (24H2)—is a routine security and quality rollup. It fixes dozens of security issues and some non‑security quality problems, but a subset of gaming rigs reported new symptoms after installing it: sustained FPS drops (commonly 10–30% in affected titles), momentary black‑screen freezes, nvlddmkm driver crashes, and degraded frame pacing. Microsoft’s KB entry documents the update contents and mitigations but does not list gaming performance as a documented known‑issue at the time of writing. Independent consumer reporting and forum threads show clusters of gamers linking degraded FPS and brief display freezes to KB5074109. Several outlets and community threads aggregated these reports and recommended practical mitigations (driver clean installs, temporary uninstall of the LCU, or toggling specific system features), while warning that removing a security cumulative is a stopgap that reduces system defenses. This pattern is not new: past Windows servicing cycles (for example, October 2025’s KB5066835) also produced heterogeneous GPU performance regressions for subsets of systems, and vendors (notably NVIDIA) have historically responded with targeted hotfix drivers to restore expected gaming performance while deeper triage continued. That October incident prompted NVIDIA to ship GeForce Hotfix 581.94 as a focused mitigation; the playbook for January follows much the same logic.
The balance of risk falls to administrators and competitive players who must weigh temporary security exposure (rollback) versus immediate functional restoration. For the majority of home users, the least risky immediate step is a clean driver update and DDU reinstall; for enterprise fleets, stage and pilot the update and keep rollback playbooks available. As always, collect objective measurements before and after any change so you can make informed, reproducible decisions.
If vendors publish a hotfix that explicitly addresses KB5074109, that will be the preferred path. Until then, follow the ordered steps above, document results, and escalate with recorded telemetry so vendors can triage any remaining outliers.
Conclusion: methodical verification, a clean driver path (DDU → fresh install), and cautious use of rollback are the practical steps that restore playability for most affected NVIDIA rigs while keeping security choices explicit and time‑limited.
Source: Sportskeeda Tech https://tech.sportskeeda.com/gaming...gpu-fps-drop-due-windows-january-2026-update/
 Background / Overview
Background / Overview
Microsoft’s January 13, 2026 cumulative update for Windows 11—published as KB5074109 and delivering OS builds 26200.7623 (25H2) and 26100.7623 (24H2)—is a routine security and quality rollup. It fixes dozens of security issues and some non‑security quality problems, but a subset of gaming rigs reported new symptoms after installing it: sustained FPS drops (commonly 10–30% in affected titles), momentary black‑screen freezes, nvlddmkm driver crashes, and degraded frame pacing. Microsoft’s KB entry documents the update contents and mitigations but does not list gaming performance as a documented known‑issue at the time of writing. Independent consumer reporting and forum threads show clusters of gamers linking degraded FPS and brief display freezes to KB5074109. Several outlets and community threads aggregated these reports and recommended practical mitigations (driver clean installs, temporary uninstall of the LCU, or toggling specific system features), while warning that removing a security cumulative is a stopgap that reduces system defenses. This pattern is not new: past Windows servicing cycles (for example, October 2025’s KB5066835) also produced heterogeneous GPU performance regressions for subsets of systems, and vendors (notably NVIDIA) have historically responded with targeted hotfix drivers to restore expected gaming performance while deeper triage continued. That October incident prompted NVIDIA to ship GeForce Hotfix 581.94 as a focused mitigation; the playbook for January follows much the same logic.What’s happening and why it matters
- Symptom cluster: sudden average FPS drops, worse 1%/0.1% lows (stutter), periodic short black‑screen freezes, and occasional nvlddmkm or driver crash events. These generally appear only after the January 13 cumulative was applied. Reports are heterogeneous: not every machine is affected, and severity varies by GPU model, game, overlays, anti‑cheat drivers, BIOS settings (for example ReBAR), and background software.
- Plausible engineering mechanisms: when Microsoft changes low‑level kernel or system servicing behavior, timing and scheduling semantics can shift in ways that affect driver submission/present paths, overlay hooks, or anti‑cheat interactions. That can lead to lower GPU utilization or disrupted frame pacing in particular workloads. Vendors typically approach this by adjusting driver behavior to align with the revised OS expectations; hotfix drivers are the rapid mitigation channel for that. Historical precedent (October 2025) shows this is an effective short‑term approach, but it is not a complete explanation until vendors publish a joint post‑mortem.
- Practical impact: competitive players and streamers see the problem as high‑impact; casual players may encounter occasional stutter or lower average framerate. For IT admins, mass deployment of the January cumulative without pilot testing risks an increase in support incidents on affected machines.
Quick triage checklist (what to do first)
- Confirm the correlation.
- Check Windows build: Settings → System → About and verify you are on a 24H2/25H2 build that matches KB5074109 (build 26100.7623 / 26200.7623).
- Reproduce the symptom in a consistent scene/benchmark (same map, same settings) and record numbers (average FPS, 1%/0.1% lows, frametimes). Tools that help: CapFrameX, PresentMon, in‑game overlays or the Windows Game Bar. Recording before/after measurements avoids guesswork.
- Reboot and test again.
- Simple reboots have fixed transient cases; if the freeze or drop was a one‑off, don’t leap to radical changes. Community reports indicate a small percentage of cases resolve after one or more restarts.
- Update GPU drivers (first line of vendor support).
- Open the NVIDIA app (formerly GeForce Experience) or download the latest Game Ready / Hotfix driver from NVIDIA’s driver page. Install using Custom → Clean Install if available. Test again. If an NVIDIA hotfix addressing the Windows cumulative is published, it will be listed in the driver release notes. As of the first wave of reports, vendors advised installing the latest official driver while they evaluate targeted hotfixes.
In‑depth remediation: step‑by‑step
Below are ordered steps starting from low‑risk to higher‑impact actions. Always create a restore point and note your current driver and Windows build before making changes.1. Safe restart and overlays check
- Close overlays and background capture tools: GeForce/NVIDIA overlay, Discord overlay, Steam overlay, OBS/Streamlabs, Xbox Game Bar functions, and any third‑party frame capture tools.
- Launch the game and benchmark. Overlays interact with the display stack and sometimes amplify regressions; disabling them is a low‑cost diagnostic.
2. Update NVIDIA driver (clean install)
- Download the latest driver package directly from NVIDIA or use the NVIDIA app.
- Run the installer → choose Custom → Clean Install to remove driver remnants.
- Reboot and retest your games.
- If the driver installer fails or the update does not help, proceed to DDU (next step). Community testing shows driver reinstalls frequently resolve regression symptoms when vendors have released mitigations.
3. Perform a DDU clean uninstall and fresh driver install (Safe Mode)
- Download Display Driver Uninstaller (DDU) from a trusted source and extract it.
- Boot Windows into Safe Mode (hold Shift while selecting Restart → Troubleshoot → Advanced → Startup Settings → Safe Mode).
- Run DDU and choose GPU → NVIDIA → Clean and restart.
- After reboot, immediately install the latest NVIDIA driver with Custom → Clean Install.
- Reboot and retest benchmarks.
- DDU is the most reliable way to remove potentially corrupted driver state and third‑party overlay hooks before a fresh install.
4. If driver reinstall does not help — temporary OS rollback (diagnostic only)
- Use Windows Update → Update history → Uninstall updates and look for “Security Update for Microsoft Windows (KB5074109)”; uninstall and reboot.
- If the update does not appear in Settings, boot to Windows Recovery Environment → Troubleshoot → Advanced Options → Uninstall Updates → select the most recent quality update.
- Command line: to uninstall the LCU package by package name, the Microsoft KB notes you can use DISM /online /remove‑package /packagename:<package> (use DISM /online /get‑packages to discover the exact package name). Note: combined SSU + LCU packages cannot be removed using wusa /uninstall when the SSU is present; Microsoft documents the proper DISM removal procedures.
5. Wider system tweaks that can help in specific setups
- Toggle Hardware‑accelerated GPU Scheduling: Settings → System → Display → Graphics → Change default graphics settings → turn HAGS off (or on, test both). Some users saw improvements toggling this setting after large servicing changes.
- Set NVIDIA Control Panel → Manage 3D settings → Power management mode → Prefer maximum performance.
- Disable Resizable BAR (ReBAR) in BIOS temporarily if you use it—some reports show ReBAR interactions change behavior after Windows servicing; disabling it is a blunt workaround and can lower performance in other titles, so test carefully.
- Use Clean Boot to eliminate third‑party services: msconfig → Services → Hide all Microsoft services → Disable all → Restart and test.
Verification: how to measure success
- Use PresentMon / CapFrameX / FrameView to capture:
- Average FPS
- 1% and 0.1% lows
- Frame times and histograms
- Run the identical scene multiple times and average results; compare before/after numbers. Don’t rely on a single in‑game counter—frametime spikes and low percentiles reveal frame‑pacing problems that average FPS hides.
Enterprise and tournament guidance
- Stage the update: pilot KB5074109 across a representative fleet before full deployment. If you’ve already observed regressions on representative hardware, hold the rollout until vendor mitigations are validated. Use Known Issue Rollback (KIR) options and Microsoft‑documented Group Policy mitigations if they become available.
- Keep rollback images and tested recovery plans available for arena rigs and critical streaming workstations; hotfix drivers and Windows rollbacks are stopgaps and must be validated under competition conditions.
What vendors have said (and what they haven’t)
- Microsoft’s KB for KB5074109 lists the update contents and some known behavioral issues in enterprise scenarios; it does not list gaming performance as a confirmed known issue in the public KB at time of reporting. The KB does explain how the servicing stack and combined packages behave when attempting removals, which matters for rollbacks.
- Vendor and community reporting (Windows Latest, Sportskeeda, Reddit and forum threads) documented user experiences of FPS drops and black screens after KB5074109; those sources have been the primary signal that prompted recommendations to update display drivers or perform a rollback.
- NVIDIA historically responded to a similar October 2025 regression with GeForce Hotfix 581.94 and announced that hotfixes would be merged into subsequent WHQL Game Ready drivers. As of the first wave of January reports there was no widely published NVIDIA hotfix explicitly citing KB5074109; users should check NVIDIA’s official driver release notes for the most recent guidance and any hotfix that mentions KB5074109 by name. If NVIDIA does publish a targeted hotfix, it will be the preferable remediation for affected GeForce systems.
Risks and trade‑offs — what you must understand before changing things
- Uninstalling a cumulative security update (KB5074109) removes dozens of security fixes and is not a long‑term solution. Use rollback only to confirm causation and only for short windows while you apply compensating controls and await a vendor fix. Document and re‑apply security mitigations promptly.
- Hotfix drivers restore functionality faster but run a compressed QA cycle; they can introduce secondary edge‑case regressions. For mission‑critical rigs, stage a hotfix in a small pilot group first and keep a tested rollback image.
- DDU removes all driver traces and third‑party overlay hooks. It is effective but disruptive—expect to reinstall other software (e.g., NVIDIA Control Panel settings, streaming overlays) after the driver reinstall. Back up profiles/settings if you rely on them.
If nothing here fixes it — escalation checklist
- Collect objective logs:
- DxDiag, Event Viewer logs around the crash time, PresentMon/CapFrameX captures, and GPU‑utilization telemetry (GPU-Z / Task Manager).
- Reproduce and record: capture a short video showing symptoms, record exact Windows and driver versions, and provide reproducible steps.
- File vendor tickets: open a NVIDIA Support ticket with logs and a link to recorded data; include OS build, driver version, GPU model, BIOS version, and exact game and graphics settings.
- If enterprise, open a coordinated partner case with Microsoft and NVIDIA and request telemetry triage and KIR guidance.
Practical recommended checklist (concise)
- Check Windows build (Settings → System → About).
- Update NVIDIA driver to the latest Game Ready/WHQL/hotfix (prefer driver notes that mention fixes for Windows updates).
- If the latest driver doesn’t help, use DDU in Safe Mode then clean‑install the driver.
- Disable overlays and test.
- If still broken and immediate recovery is required, temporarily uninstall KB5074109 (diagnostic only) and re‑test, then re‑apply security controls and monitor for an official fix.
- Pilot any fixes across a representative set of systems before mass deployment.
Final analysis and verdict
The January 2026 cumulative (KB5074109) correlates with a reproducible set of GPU‑related symptoms on a minority of configurations; community reports and forum threads provide credible, repeated signals that justify a pragmatic remediation path: update drivers first, perform clean reinstalls with DDU if needed, and only consider uninstalling the Windows cumulative as a short‑term diagnostic when driver changes fail. This mirrors vendor playbooks used through 2025: hotfix drivers are fast, targeted mitigations, not substitutes for a coordinated root‑cause fix.The balance of risk falls to administrators and competitive players who must weigh temporary security exposure (rollback) versus immediate functional restoration. For the majority of home users, the least risky immediate step is a clean driver update and DDU reinstall; for enterprise fleets, stage and pilot the update and keep rollback playbooks available. As always, collect objective measurements before and after any change so you can make informed, reproducible decisions.
If vendors publish a hotfix that explicitly addresses KB5074109, that will be the preferred path. Until then, follow the ordered steps above, document results, and escalate with recorded telemetry so vendors can triage any remaining outliers.
Conclusion: methodical verification, a clean driver path (DDU → fresh install), and cautious use of rollback are the practical steps that restore playability for most affected NVIDIA rigs while keeping security choices explicit and time‑limited.
Source: Sportskeeda Tech https://tech.sportskeeda.com/gaming...gpu-fps-drop-due-windows-january-2026-update/