Microsoft confirmed in late April 2026 that new Windows security warnings for Remote Desktop
The affected warning is not an old nuisance dialog suddenly getting attention. It is part of Microsoft’s April 2026 security update work around Remote Desktop files, a change meant to make
That is a meaningful shift because RDP files are not merely shortcuts. They can encode connection settings that decide whether a remote machine can see local drives, clipboard contents, cameras, microphones, smart cards, printers, and other resources. In the wrong hands, that makes them a neat phishing vehicle: the victim thinks they are opening a connection profile, while the attacker gets a bridge into local resources.
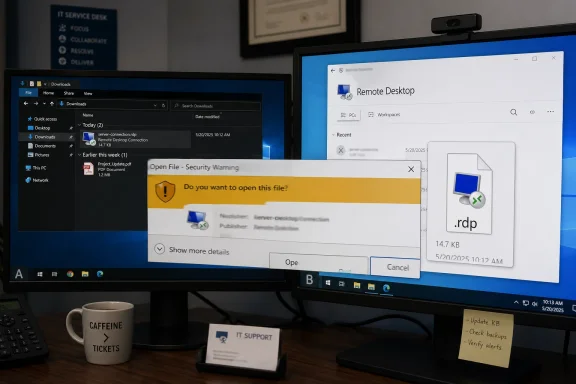
The newly confirmed issue undercuts that design in a very Windows way. On systems with more than one monitor and mismatched display scaling — Microsoft’s example is one monitor at 100 percent and another at 125 percent — the warning window may show overlapping text or partially hidden buttons. In other words, the dialog intended to slow the user down and make risk visible may itself become illegible.
This does not mean RDP is broken, nor does it mean every user who installed April’s cumulative updates will see the problem. It means Microsoft has introduced a security-sensitive UX surface that appears vulnerable to mixed-DPI rendering problems, a class of bugs that has haunted Windows for years as laptops, docking stations, 4K monitors, and hot-desking setups became normal.
The April 2026 change affects file-based Remote Desktop launches, not a user manually typing a host name into Remote Desktop Connection. That distinction matters, but it also explains why enterprises care. Saved RDP files are often generated by portals, password vaults, privileged access systems, RemoteApp deployments, documentation pages, and internal tooling. Many environments have treated them as operational plumbing rather than as executable security decisions.
Microsoft’s new model says that plumbing deserves a warning label. The first time a user opens an RDP file after the update, Windows shows an educational prompt explaining the risk. On subsequent launches, the connection security dialog appears before the connection proceeds, showing details such as the remote computer address, publisher information when available, and requested redirections.
The most important security choice is that those requested redirections are turned off by default. A file that asks to share drives, clipboard, devices, or other local resources no longer gets those channels silently. The user must explicitly enable them. That is the right direction, especially for phishing scenarios where the attack depends on the victim not noticing what the file is asking to share.
But the right direction is not the same as a smooth rollout. If the dialog is misrendered, the user may not be able to see which redirections are being requested or which button actually proceeds. Worse, a frustrated employee may learn the wrong lesson: not “RDP files can be dangerous,” but “Windows has put another broken box in front of my work.”
That ordinariness is precisely why they work as bait. A malicious RDP file can point to an attacker-controlled host and request local-resource redirection. If the client connects and shares the wrong things, the remote side may gain access to files, authentication material, clipboard data, or other sensitive resources exposed through the session.
Microsoft’s own guidance now makes the risk plain: an RDP file can do more than choose a target computer. It can carry settings that share parts of the local device with the remote computer. The April update is therefore not cosmetic. It changes the consent boundary from “the file contains the settings” to “the user sees the settings and must opt in.”
That is a good security pattern. It resembles the broader move across operating systems to make implicit trust explicit: camera prompts, location prompts, clipboard prompts, browser permission prompts, OAuth consent screens, and app sandbox controls. The recurring problem is that consent screens only work when they are rare enough to be taken seriously and clear enough to be understood.
The RDP dialog bug attacks the second condition. A warning that overlaps text or hides buttons is not just ugly; it degrades consent. The user cannot make a good decision if the decision surface is scrambled.
That distinction matters in modern enterprise defense. Organizations have grown better at blocking commodity payloads, scanning Office documents, and detonating suspicious executables. Attackers respond by looking for formats and workflows that defenders allow because the business needs them. RDP sits squarely in that territory.
A signed or unsigned RDP file is not inherently malicious, and most RDP use is mundane. But attackers do not need every user to fall for a trick. They need a plausible pretext, a path through email or collaboration tools, and a victim whose machine can expose something useful once connected to the wrong place. That is why Microsoft’s new dialogs focus not only on the destination but also on the resources the file wants to redirect.
This is also why unsigned files now get a sharper treatment. If the publisher cannot be verified, Windows labels the connection as unknown. If the file is signed, Windows can show publisher information, though Microsoft correctly warns that a signature is not a blessing from the security gods. A file can be signed by an entity with a confusingly similar name, and trusted-looking labels can still mislead.
The bigger point is cultural. Microsoft is trying to make RDP files feel less like harmless shortcuts and more like security-relevant launch objects. That is overdue. But it also means every defect in the warning path carries more symbolic weight than a normal UI bug.
This is not a glamorous failure mode, but it is a consequential one. Security dialogs are not ordinary app chrome. They often run at moments of elevated attention, before trust decisions, installation steps, credential flows, remote connections, or policy changes. If those dialogs are built or tested like routine UI, they inherit routine UI failures.
The irony is sharp because Remote Desktop itself is deeply entangled with display behavior. Multi-monitor support, scaling, resolution negotiation, and remote-session presentation are all part of the RDP universe. Yet the bug here appears in the local warning window before the connection is made, not in the remote session. That makes it feel less like an RDP protocol problem and more like an integration problem between a newly introduced security dialog and the realities of modern Windows display configurations.
This is exactly the kind of bug that can survive testing because the reproduction matrix is fiddly. You need the April update, an RDP file path, the new warning, multiple displays, differing scale factors, and likely particular placement or focus behavior. In a lab, every one of those variables is controllable. In the real world, they combine chaotically across docks, GPUs, remote-work desks, conference rooms, and IT workstations.
For Windows enthusiasts, this is an old grievance in a new costume. The operating system has made real progress on high-DPI behavior over the past decade, but mixed-scaling setups remain a stress test for any dialog that assumes pixels, fonts, and controls will behave politely.
That makes layout and readability part of the security model. If checkboxes are hidden, text overlaps, or buttons drift away from their labels, the interface no longer faithfully represents the choice. Even if Windows still defaults redirections to off, a broken dialog can encourage rushed clicking, help-desk workarounds, or organization-wide attempts to suppress the new behavior.
Microsoft does provide a temporary administrative escape hatch through policy-backed registry configuration that can revert to the previous dialog behavior. The company also warns that support for that setting may be removed in a future update, which is the right warning to attach. A rollback switch is useful during disruption, but it is not a strategy.
The better enterprise response is to treat the new warning as a forcing function. If internal RDP files are unsigned, sign them. If files request unnecessary redirections, remove those requests. If users rely on RDP files generated by third-party systems, validate how those systems sign or distribute them. If help desks are drowning in tickets, fix the trust chain rather than training users to ignore the prompt.
That said, the display bug complicates the ideal response. Admins cannot simply tell users to read the dialog carefully if some users literally cannot read it. Until Microsoft ships a fix, organizations with affected setups need practical guidance: align display scaling temporarily, move the dialog to a monitor with standard scaling if possible, avoid launching unexpected RDP files, and use managed alternatives for high-risk workflows.
Some of that reaction is understandable. If a privileged access management tool or RemoteApp workflow suddenly produces scary warnings for files users have opened for years, ticket volume rises. If the warning is then unreadable on a subset of workstations, the pressure to disable it grows. Security controls that arrive without operational polish often lose the internal political fight, even when the threat model is sound.
This is where Microsoft’s execution matters. The company has to fix the rendering bug quickly, but it also has to keep explaining why the warning exists. The message should not be “sorry for the annoying dialog.” It should be “RDP files can grant access to local resources, and the new dialog makes that visible.” Those are very different narratives.
Administrators have a role too. The worst response would be to globally suppress the new dialog and declare victory. That might restore old workflows, but it also restores the old ambiguity that attackers exploited. The more mature response is to inventory where RDP files come from, sign the ones that are legitimate, reduce redirections to the minimum, and teach users that unknown RDP publishers are not a harmless cosmetic issue.
The display bug is therefore a stress test for security governance. Mature shops will use the temporary pain to clean up RDP handling. Less mature shops will hide the prompt and hope email filtering catches the next malicious file. Hope is not a control.
This will be annoying for environments that grew organically. Many admins have folders full of connection files, scripts that emit
Signing does not make an RDP file safe. Microsoft’s own guidance is careful on this point. A signature identifies the publisher and helps show the file has not changed since signing; it does not prove the destination is benign or the requested redirections are appropriate. But signing gives the user and the operating system a stronger starting point than “Unknown publisher.”
This is where the security dialog can become useful rather than merely tolerated. A well-managed environment should make normal files look normal and abnormal files stand out. If every legitimate file is unsigned, the warning loses signal. If legitimate files are signed and trimmed to necessary redirections, an unknown or overreaching file becomes easier to challenge.
The April update effectively raises the cost of sloppy RDP distribution. That cost is justified, but Microsoft must also respect the fact that enterprise cleanup takes time. The temporary revert option exists because abrupt security UX changes can break real operations. The danger is letting “temporary” become institutional memory.
The RDP warning issue shows the risk of that model. Security teams may celebrate a new safeguard; help desks may experience it as a surge in confused calls; users may experience it as a broken dialog; attackers may experience it as a shrinking window of opportunity. All of those can be true at once.
For Microsoft, the lesson is not to avoid these changes. The old behavior around RDP files was too quiet for the threat landscape. The lesson is that security UX needs the same compatibility discipline as kernel changes, authentication changes, or browser hardening. A prompt that becomes a daily feature of enterprise workflows deserves broad testing across display configurations, accessibility settings, localization, assistive technology, and managed-client scenarios.
For customers, the lesson is to stop treating Windows cumulative updates as invisible maintenance. They increasingly carry workflow changes with security intent. That means pilot rings should include not only application owners and power users, but also the weird desks: multi-monitor admins, high-DPI laptop users, help-desk jump-station operators, and staff who live inside remote access tools all day.
The bug also argues for better communication between security and endpoint teams. If security wants a new prompt to stand, endpoint operations must know how it behaves, what breaks it, and when a workaround is acceptable. Otherwise the workaround will be chosen by whoever is under the most ticket pressure.
For now, the practical posture is to keep the April security updates in place unless an organization has a specific, tested reason to use Microsoft’s temporary fallback. The new RDP protections address a real abuse pattern, and disabling them broadly because of a mixed-scaling bug would be a disproportionate reaction. But Microsoft should move quickly, because every week of broken rendering gives administrators another reason to normalize bypasses.
There is also an opportunity here. The RDP warning can push organizations to modernize how they distribute remote access profiles. Signing, publisher trust, reduced redirection, and user education are not glamorous, but they are precisely the boring controls that make phishing campaigns less profitable.
The most revealing thing about this incident is that it sits at the intersection of two long-running Windows stories. One is Microsoft’s continuing effort to harden old enterprise workflows against modern phishing. The other is the stubborn fragility of desktop UX under the messy conditions where Windows is actually used. The first story is encouraging. The second is why the first one still needs humility.
Source: SC Media Windows security warnings for RDP files may display incorrectly
.rdp files can render incorrectly on supported Windows 11, Windows 10, and Windows Server systems when multi-monitor setups use different display scaling values. The bug is narrow, almost comically specific, but its timing is not. Microsoft has just tried to make RDP file launches more explicit and less phishable; now the warning itself can become hard to read. That turns a sensible security improvement into a familiar Windows dilemma: the safest control is only as good as the interface users can actually understand.
 Microsoft’s New RDP Guardrail Trips Over the Desktop It Runs On
Microsoft’s New RDP Guardrail Trips Over the Desktop It Runs On
The affected warning is not an old nuisance dialog suddenly getting attention. It is part of Microsoft’s April 2026 security update work around Remote Desktop files, a change meant to make .rdp launches more transparent before a connection is made. When a user opens an RDP file, Windows now presents more information about the remote destination, publisher status, and requested local-resource redirections.That is a meaningful shift because RDP files are not merely shortcuts. They can encode connection settings that decide whether a remote machine can see local drives, clipboard contents, cameras, microphones, smart cards, printers, and other resources. In the wrong hands, that makes them a neat phishing vehicle: the victim thinks they are opening a connection profile, while the attacker gets a bridge into local resources.
The newly confirmed issue undercuts that design in a very Windows way. On systems with more than one monitor and mismatched display scaling — Microsoft’s example is one monitor at 100 percent and another at 125 percent — the warning window may show overlapping text or partially hidden buttons. In other words, the dialog intended to slow the user down and make risk visible may itself become illegible.
This does not mean RDP is broken, nor does it mean every user who installed April’s cumulative updates will see the problem. It means Microsoft has introduced a security-sensitive UX surface that appears vulnerable to mixed-DPI rendering problems, a class of bugs that has haunted Windows for years as laptops, docking stations, 4K monitors, and hot-desking setups became normal.
The Bug Is Small, but the Surface Area Is Not
It is tempting to file this as a display annoyance. That would be a mistake. Remote Desktop is not a consumer fringe feature; it is connective tissue for administrators, help desks, outsourced support teams, jump boxes, lab environments, remote apps, legacy workflows, and small businesses that still use saved connection files because they are simple and portable.The April 2026 change affects file-based Remote Desktop launches, not a user manually typing a host name into Remote Desktop Connection. That distinction matters, but it also explains why enterprises care. Saved RDP files are often generated by portals, password vaults, privileged access systems, RemoteApp deployments, documentation pages, and internal tooling. Many environments have treated them as operational plumbing rather than as executable security decisions.
Microsoft’s new model says that plumbing deserves a warning label. The first time a user opens an RDP file after the update, Windows shows an educational prompt explaining the risk. On subsequent launches, the connection security dialog appears before the connection proceeds, showing details such as the remote computer address, publisher information when available, and requested redirections.
The most important security choice is that those requested redirections are turned off by default. A file that asks to share drives, clipboard, devices, or other local resources no longer gets those channels silently. The user must explicitly enable them. That is the right direction, especially for phishing scenarios where the attack depends on the victim not noticing what the file is asking to share.
But the right direction is not the same as a smooth rollout. If the dialog is misrendered, the user may not be able to see which redirections are being requested or which button actually proceeds. Worse, a frustrated employee may learn the wrong lesson: not “RDP files can be dangerous,” but “Windows has put another broken box in front of my work.”
RDP Files Became a Phishing Problem Because They Look Boring
The security industry has spent years teaching users to fear macros, suspicious attachments, fake sign-in pages, and executable files. RDP files occupy a more awkward category. They are text-based configuration files associated with a legitimate Microsoft client, and in many companies they are part of the daily rhythm of remote administration.That ordinariness is precisely why they work as bait. A malicious RDP file can point to an attacker-controlled host and request local-resource redirection. If the client connects and shares the wrong things, the remote side may gain access to files, authentication material, clipboard data, or other sensitive resources exposed through the session.
Microsoft’s own guidance now makes the risk plain: an RDP file can do more than choose a target computer. It can carry settings that share parts of the local device with the remote computer. The April update is therefore not cosmetic. It changes the consent boundary from “the file contains the settings” to “the user sees the settings and must opt in.”
That is a good security pattern. It resembles the broader move across operating systems to make implicit trust explicit: camera prompts, location prompts, clipboard prompts, browser permission prompts, OAuth consent screens, and app sandbox controls. The recurring problem is that consent screens only work when they are rare enough to be taken seriously and clear enough to be understood.
The RDP dialog bug attacks the second condition. A warning that overlaps text or hides buttons is not just ugly; it degrades consent. The user cannot make a good decision if the decision surface is scrambled.
APT29 Made the Case for Microsoft Before Microsoft Shipped the Fix
The pressure behind the change is not theoretical. RDP file abuse has been associated with espionage activity, including campaigns attributed to Russian state-sponsored actors such as APT29. These campaigns showed why a connection file can be a powerful lure: it lets an attacker abuse a trusted Windows component rather than dropping an obvious malware binary.That distinction matters in modern enterprise defense. Organizations have grown better at blocking commodity payloads, scanning Office documents, and detonating suspicious executables. Attackers respond by looking for formats and workflows that defenders allow because the business needs them. RDP sits squarely in that territory.
A signed or unsigned RDP file is not inherently malicious, and most RDP use is mundane. But attackers do not need every user to fall for a trick. They need a plausible pretext, a path through email or collaboration tools, and a victim whose machine can expose something useful once connected to the wrong place. That is why Microsoft’s new dialogs focus not only on the destination but also on the resources the file wants to redirect.
This is also why unsigned files now get a sharper treatment. If the publisher cannot be verified, Windows labels the connection as unknown. If the file is signed, Windows can show publisher information, though Microsoft correctly warns that a signature is not a blessing from the security gods. A file can be signed by an entity with a confusingly similar name, and trusted-looking labels can still mislead.
The bigger point is cultural. Microsoft is trying to make RDP files feel less like harmless shortcuts and more like security-relevant launch objects. That is overdue. But it also means every defect in the warning path carries more symbolic weight than a normal UI bug.
Mixed-DPI Windows Is Still Where Polish Goes to Die
The reported trigger — multiple monitors with different scaling settings — will be instantly familiar to anyone who has docked a high-resolution laptop next to older external displays. One screen wants 150 percent scaling, another wants 100 percent, and Windows has to move legacy and modern UI surfaces across both without mangling layout, fonts, hit boxes, or dialog geometry.This is not a glamorous failure mode, but it is a consequential one. Security dialogs are not ordinary app chrome. They often run at moments of elevated attention, before trust decisions, installation steps, credential flows, remote connections, or policy changes. If those dialogs are built or tested like routine UI, they inherit routine UI failures.
The irony is sharp because Remote Desktop itself is deeply entangled with display behavior. Multi-monitor support, scaling, resolution negotiation, and remote-session presentation are all part of the RDP universe. Yet the bug here appears in the local warning window before the connection is made, not in the remote session. That makes it feel less like an RDP protocol problem and more like an integration problem between a newly introduced security dialog and the realities of modern Windows display configurations.
This is exactly the kind of bug that can survive testing because the reproduction matrix is fiddly. You need the April update, an RDP file path, the new warning, multiple displays, differing scale factors, and likely particular placement or focus behavior. In a lab, every one of those variables is controllable. In the real world, they combine chaotically across docks, GPUs, remote-work desks, conference rooms, and IT workstations.
For Windows enthusiasts, this is an old grievance in a new costume. The operating system has made real progress on high-DPI behavior over the past decade, but mixed-scaling setups remain a stress test for any dialog that assumes pixels, fonts, and controls will behave politely.
The Warning Is a Security Boundary, Not a Compliance Banner
There is a tendency in enterprise software to treat warnings as legal insulation: show the user a box, require a click, and declare the risk disclosed. That attitude is dangerous here. The RDP warning is not just informing the user that danger exists; it is asking the user to choose which local resources to expose to the remote side.That makes layout and readability part of the security model. If checkboxes are hidden, text overlaps, or buttons drift away from their labels, the interface no longer faithfully represents the choice. Even if Windows still defaults redirections to off, a broken dialog can encourage rushed clicking, help-desk workarounds, or organization-wide attempts to suppress the new behavior.
Microsoft does provide a temporary administrative escape hatch through policy-backed registry configuration that can revert to the previous dialog behavior. The company also warns that support for that setting may be removed in a future update, which is the right warning to attach. A rollback switch is useful during disruption, but it is not a strategy.
The better enterprise response is to treat the new warning as a forcing function. If internal RDP files are unsigned, sign them. If files request unnecessary redirections, remove those requests. If users rely on RDP files generated by third-party systems, validate how those systems sign or distribute them. If help desks are drowning in tickets, fix the trust chain rather than training users to ignore the prompt.
That said, the display bug complicates the ideal response. Admins cannot simply tell users to read the dialog carefully if some users literally cannot read it. Until Microsoft ships a fix, organizations with affected setups need practical guidance: align display scaling temporarily, move the dialog to a monitor with standard scaling if possible, avoid launching unexpected RDP files, and use managed alternatives for high-risk workflows.
The Enterprise Risk Is Friction Turning Into Folk Remedies
The security value of the April RDP change depends on adoption. The danger is not only that one dialog renders badly; it is that the rollout teaches organizations to look for ways around the control. In sysadmin culture, a disruptive prompt quickly becomes a registry key, a script, a Group Policy setting, or a wiki page titled “fix annoying RDP warning.”Some of that reaction is understandable. If a privileged access management tool or RemoteApp workflow suddenly produces scary warnings for files users have opened for years, ticket volume rises. If the warning is then unreadable on a subset of workstations, the pressure to disable it grows. Security controls that arrive without operational polish often lose the internal political fight, even when the threat model is sound.
This is where Microsoft’s execution matters. The company has to fix the rendering bug quickly, but it also has to keep explaining why the warning exists. The message should not be “sorry for the annoying dialog.” It should be “RDP files can grant access to local resources, and the new dialog makes that visible.” Those are very different narratives.
Administrators have a role too. The worst response would be to globally suppress the new dialog and declare victory. That might restore old workflows, but it also restores the old ambiguity that attackers exploited. The more mature response is to inventory where RDP files come from, sign the ones that are legitimate, reduce redirections to the minimum, and teach users that unknown RDP publishers are not a harmless cosmetic issue.
The display bug is therefore a stress test for security governance. Mature shops will use the temporary pain to clean up RDP handling. Less mature shops will hide the prompt and hope email filtering catches the next malicious file. Hope is not a control.
Signing RDP Files Is No Longer Optional Housekeeping
One of the quiet consequences of Microsoft’s change is that RDP file signing moves from obscure best practice to practical necessity. If an organization distributes RDP files internally, unsigned files now look suspicious by design. That is not Microsoft being dramatic; it is Microsoft admitting that an unsigned connection profile cannot prove who produced it or whether it has been tampered with.This will be annoying for environments that grew organically. Many admins have folders full of connection files, scripts that emit
.rdp profiles, vendor portals that generate them on demand, and password tools that hand them off as part of a privileged session. Those workflows may have functioned perfectly well before April 2026, but they were often relying on user familiarity rather than cryptographic trust.Signing does not make an RDP file safe. Microsoft’s own guidance is careful on this point. A signature identifies the publisher and helps show the file has not changed since signing; it does not prove the destination is benign or the requested redirections are appropriate. But signing gives the user and the operating system a stronger starting point than “Unknown publisher.”
This is where the security dialog can become useful rather than merely tolerated. A well-managed environment should make normal files look normal and abnormal files stand out. If every legitimate file is unsigned, the warning loses signal. If legitimate files are signed and trimmed to necessary redirections, an unknown or overreaching file becomes easier to challenge.
The April update effectively raises the cost of sloppy RDP distribution. That cost is justified, but Microsoft must also respect the fact that enterprise cleanup takes time. The temporary revert option exists because abrupt security UX changes can break real operations. The danger is letting “temporary” become institutional memory.
Microsoft’s Patch Cadence Is Now a UX Cadence
Patch Tuesday used to be thought of primarily as a vulnerability and stability event. In 2026, it is also a user-experience deployment mechanism for security policy. A cumulative update can change not only what Windows blocks but what users see, what they must approve, and how administrators must document routine work.The RDP warning issue shows the risk of that model. Security teams may celebrate a new safeguard; help desks may experience it as a surge in confused calls; users may experience it as a broken dialog; attackers may experience it as a shrinking window of opportunity. All of those can be true at once.
For Microsoft, the lesson is not to avoid these changes. The old behavior around RDP files was too quiet for the threat landscape. The lesson is that security UX needs the same compatibility discipline as kernel changes, authentication changes, or browser hardening. A prompt that becomes a daily feature of enterprise workflows deserves broad testing across display configurations, accessibility settings, localization, assistive technology, and managed-client scenarios.
For customers, the lesson is to stop treating Windows cumulative updates as invisible maintenance. They increasingly carry workflow changes with security intent. That means pilot rings should include not only application owners and power users, but also the weird desks: multi-monitor admins, high-DPI laptop users, help-desk jump-station operators, and staff who live inside remote access tools all day.
The bug also argues for better communication between security and endpoint teams. If security wants a new prompt to stand, endpoint operations must know how it behaves, what breaks it, and when a workaround is acceptable. Otherwise the workaround will be chosen by whoever is under the most ticket pressure.
The April RDP Lesson Microsoft Should Not Waste
The concrete lesson is simple, but it cuts across security, IT operations, and Windows engineering: a warning about trust must itself be trustworthy. If the user cannot read it, interpret it, or operate it confidently, the warning becomes another prompt in the long history of prompts people learn to dismiss.For now, the practical posture is to keep the April security updates in place unless an organization has a specific, tested reason to use Microsoft’s temporary fallback. The new RDP protections address a real abuse pattern, and disabling them broadly because of a mixed-scaling bug would be a disproportionate reaction. But Microsoft should move quickly, because every week of broken rendering gives administrators another reason to normalize bypasses.
There is also an opportunity here. The RDP warning can push organizations to modernize how they distribute remote access profiles. Signing, publisher trust, reduced redirection, and user education are not glamorous, but they are precisely the boring controls that make phishing campaigns less profitable.
The most revealing thing about this incident is that it sits at the intersection of two long-running Windows stories. One is Microsoft’s continuing effort to harden old enterprise workflows against modern phishing. The other is the stubborn fragility of desktop UX under the messy conditions where Windows is actually used. The first story is encouraging. The second is why the first one still needs humility.
The RDP Prompt Is a Test of Operational Discipline
The safest organizations will not treat this as a choice between security and convenience. They will keep the security intent, work around the display defect narrowly, and use the disruption to remove ambiguity from their RDP workflows.- Microsoft’s April 2026 updates added new warnings for RDP files because those files can redirect sensitive local resources to a remote system.
- The confirmed display bug mainly affects multi-monitor systems with different scaling settings, where warning text and buttons may render incorrectly.
- The issue affects supported Windows client and server versions, but it does not mean all Remote Desktop connections are broken.
- Organizations should sign legitimate RDP files, minimize requested redirections, and avoid teaching users to ignore unknown-publisher warnings.
- Temporary fallback settings may reduce disruption, but relying on them broadly weakens the security improvement Microsoft is trying to make.
Source: SC Media Windows security warnings for RDP files may display incorrectly