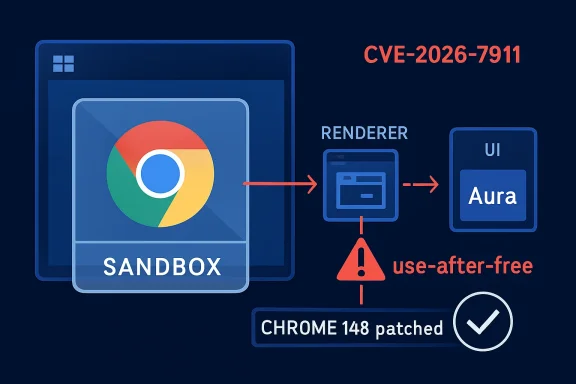
Google Chrome on Windows before version 148.0.7778.96 contains CVE-2026-7911, a high-severity use-after-free flaw in Chromium’s Aura UI layer that could let a remote attacker who already compromised the renderer attempt a sandbox escape through a crafted HTML page. That phrasing is dry, but the security story is not: this is a browser bug that lives beyond the tab. It is not the first-stage “visit a page and lose the machine” nightmare by itself, yet it is exactly the kind of second-stage weakness exploit chains are built to find. For Windows admins, the practical answer is blunt: Chrome 148 is not a feature update to schedule casually; it is a boundary repair.
The most important phrase in the CVE description is not “crafted HTML page.” It is “who had compromised the renderer process.” That means CVE-2026-7911 is not being described as a standalone remote-code-execution bug from an ordinary web page. It is a way for an attacker who has already gained a foothold in Chrome’s renderer to push outward, toward a sandbox escape.
That distinction matters because modern browser exploitation usually comes in chains. One bug gets code running in the renderer, where hostile JavaScript and page content are supposed to be contained. A second bug then tries to break the containment model, reaching a more privileged browser process, operating-system interface, or local resource.
CVE-2026-7911 sits in that second category. It does not make the renderer compromise unimportant; it assumes one. The risk is that once the first wall is breached, this flaw may weaken the next wall at precisely the point where Chrome is supposed to turn a web compromise into a contained incident rather than a system-level one.
For WindowsForum readers, that makes this more than a Chrome-only problem. Chrome is often treated as just another application in endpoint patching dashboards, but the browser is also the largest untrusted-code execution environment most Windows machines run every day. A sandbox escape is where a browser incident starts to resemble an endpoint incident.
That makes it an uncomfortable place to see a use-after-free bug. UI frameworks are busy intersections. They receive events, hold references to objects, mediate lifetimes, and translate between the browser’s cross-platform abstractions and the host operating system’s expectations. If memory ownership gets confused there, the impact is rarely easy to summarize.
A use after free occurs when software continues using memory after it has been released. In safe conditions, freed memory should no longer be trusted. In exploitable conditions, an attacker may influence what occupies that memory next, turning an ordinary logic error into a primitive for code execution, privilege movement, or state corruption.
The CVE’s Windows-only language is notable. Chromium runs everywhere, but Aura’s relationship with platform-specific windowing behavior can make bugs appear differently across operating systems. In this case, the advisory scope says Google Chrome on Windows before 148.0.7778.96 is the exposed combination, which is exactly the sort of platform-specific edge case enterprise teams can miss if they track “Chrome” as one monolithic product.
The high attack complexity is doing real work here. An attacker needs more than a simple drive-by page. The published description says the attacker must already have compromised the renderer process, which implies a separate vulnerability, malicious content primitive, or chained condition. That is why the bug should not be described as a one-click full-system takeover.
But high complexity should not be mistaken for low urgency. Sophisticated browser exploit chains are assembled exactly this way: a renderer bug, a sandbox escape, perhaps a kernel or broker abuse afterward, then persistence or credential access. The exploit developer’s job is to turn a sequence of unlikely events into a repeatable process.
The user-interaction requirement is also less comforting than it sounds. In browser CVEs, user interaction often means visiting or being directed to a malicious page. That is not a high bar in an enterprise where phishing, malvertising, compromised legitimate sites, and abused collaboration links are routine delivery mechanisms.
That scale matters. A single CVE can look isolated on a vulnerability-management screen, but Chrome 148 is a broad security release. CVE-2026-7911 is one tile in a mosaic of memory-safety, validation, and implementation fixes across a codebase that now functions as a near-operating-system runtime for much of the modern desktop.
The release also demonstrates Google’s familiar disclosure posture. The public record identifies the affected component, weakness class, version boundary, and broad attack condition, while detailed bug links may remain restricted until enough users have updated. That frustrates defenders who want full technical detail immediately, but it is also a recognition that a patch diff can become an exploit guide.
This is the browser security bargain in 2026: vendors patch fast, disclose narrowly, and rely on automatic update plumbing to close the window before reverse engineers widen it. Enterprises that interrupt that plumbing inherit the risk. If Chrome updates are delayed for testing, packaging, or change-control reasons, the organization is effectively choosing to sit in the interval between “the bug is known” and “the exploit is commoditized.”
That distinction is operationally important. Waiting for Windows Update alone is the wrong response if the vulnerable product is Chrome. A fully patched Windows machine can still be running an exposed Chrome build if third-party application updates are lagging, blocked, or pinned.
The CPE note in the NVD change history is also worth parsing carefully. The listed configuration combines Google Chrome versions up to but excluding 148.0.7778.96 with Microsoft Windows. That is not saying Windows itself contains the vulnerable code. It is saying the vulnerable software configuration is Chrome on Windows.
This is where asset inventory often goes sideways. Security teams that manage Microsoft patches with discipline sometimes have weaker visibility into browser variants, user-installed builds, unmanaged profiles, portable browsers, and Chromium-based derivatives. CVE-2026-7911 is the kind of bug that rewards boring hygiene: know which browsers are installed, know which channel they are on, and know whether they actually updated.
The responsible move is to check each vendor’s release notes and version mapping rather than mechanically applying Chrome’s version number to every Chromium product. Edge, for example, follows its own release cadence and versioning even when it integrates Chromium fixes. Other vendors may lag by hours or days, particularly around major stable updates.
This is especially relevant for organizations that standardize on Edge but leave Chrome installed “just in case,” or vice versa. The second browser tends to receive less policy attention and less user education, yet it remains a full attack surface. A dormant browser with an old version is not dormant if a URL handler, embedded workflow, or user habit wakes it up.
The same logic applies to software that embeds Chromium. Not every embedded Chromium runtime is affected by this specific CVE, and the Windows Chrome/Aura wording should keep us from overgeneralizing. But the broader lesson is that Chromium has become infrastructure. Treating it as a single consumer app understates how many places its code can appear.
Still, exploitability changes after disclosure. Once a patch ships, attackers can study changed code, infer the flaw, and test whether vulnerable builds remain common enough to justify weaponization. Browser bugs age badly because the delta between fixed and unfixed machines becomes the attacker’s market map.
The phrase “sandbox escape” should also focus attention on endpoint detection. A renderer compromise alone may look like browser weirdness, a crashed tab, or an exploit attempt blocked by containment. A successful escape is more likely to interact with files, processes, tokens, IPC mechanisms, or OS APIs in ways that endpoint tools can observe.
That means patching is step one, not the entire defense. Security teams should watch for suspicious browser child-process behavior, unexpected process spawning, unusual command-line patterns, and browser-to-system transitions that do not match ordinary user activity. The less you know about the exploit details, the more you lean on behavioral detection around the boundary it is trying to cross.
For CVE-2026-7911, the target state is simple: Chrome on Windows should be at 148.0.7778.96 or later, with extended stable environments on the corresponding fixed build. The hard part is proving that state across real machines. Browser version reporting in endpoint-management platforms can lag, users can keep sessions open, and some update mechanisms require a browser restart before the patched binary is actually in use.
This is where a surprising number of organizations fail. They deploy the update package, mark the job complete, and never verify that users relaunched. Chrome may download the patch, but the old process can remain alive. In a vulnerability involving web content and browser process boundaries, that distinction is not clerical.
Admins should also resist the temptation to treat “high attack complexity” as a reason to wait. High-complexity bugs are often the ones that separate opportunistic crime from serious operators. If your threat model includes targeted phishing, credential theft, espionage, or ransomware crews buying access from exploit brokers, the complexity belongs to the attacker’s engineering team, not your risk register.
Google has spent years investing in sandboxing, site isolation, fuzzing, MiraclePtr-style mitigations, hardened allocators, and gradual memory-safety improvements. Those efforts have made exploitation harder. They have not made memory bugs disappear.
The uncomfortable truth is that mitigations change the shape of exploitation more than they end it. A use-after-free that might once have been straightforward remote code execution may now require heap grooming, renderer compromise, object-shape knowledge, and a second primitive. That is progress. It is also why the CVE reads like a chain component rather than a complete attack.
For defenders, this means severity should be interpreted in context. A high-severity sandbox escape may be more strategically important than a flashier bug with a simpler description. The browser’s security model is layered; flaws that connect layers are valuable.
The modern Windows desktop is also browser-mediated in a way that did not exist a decade ago. SaaS admin portals, device-management consoles, cloud dashboards, HR systems, ticketing platforms, developer tools, and internal applications all run through tabs. Compromise the right browser session and the attacker may not need to install much at all.
That is why the “remote attacker” language should not be read narrowly. The remote attacker may be delivering a page, but the prize is local context: the user’s session, the machine’s trust relationships, and the browser’s position as an authenticated control plane. Even without a full operating-system takeover, escaping a renderer can open paths that defenders would rather keep sealed.
Windows shops should pair patch deployment with session hygiene. Force browser restarts where policy allows. Confirm version compliance. Revisit whether high-risk users—administrators, finance staff, developers, help-desk personnel—are allowed to run stale browser sessions indefinitely. The browser is now privileged by proximity, even when the OS does not formally treat it that way.
That makes the operational guidance unusually straightforward.
Chrome 148 closes this particular hole, but the larger direction is clear: attackers will keep looking for the seams between renderer isolation, UI frameworks, operating-system integration, and enterprise delay. The winners will not be the organizations that memorize every Chromium component name. They will be the ones that can turn a vendor’s fixed version into a verified fleet state before a quiet sandbox bug becomes the second act of someone else’s exploit chain.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Chrome’s Latest Windows Bug Is Really About the Space Between Sandboxes
Chrome’s Latest Windows Bug Is Really About the Space Between Sandboxes
The most important phrase in the CVE description is not “crafted HTML page.” It is “who had compromised the renderer process.” That means CVE-2026-7911 is not being described as a standalone remote-code-execution bug from an ordinary web page. It is a way for an attacker who has already gained a foothold in Chrome’s renderer to push outward, toward a sandbox escape.That distinction matters because modern browser exploitation usually comes in chains. One bug gets code running in the renderer, where hostile JavaScript and page content are supposed to be contained. A second bug then tries to break the containment model, reaching a more privileged browser process, operating-system interface, or local resource.
CVE-2026-7911 sits in that second category. It does not make the renderer compromise unimportant; it assumes one. The risk is that once the first wall is breached, this flaw may weaken the next wall at precisely the point where Chrome is supposed to turn a web compromise into a contained incident rather than a system-level one.
For WindowsForum readers, that makes this more than a Chrome-only problem. Chrome is often treated as just another application in endpoint patching dashboards, but the browser is also the largest untrusted-code execution environment most Windows machines run every day. A sandbox escape is where a browser incident starts to resemble an endpoint incident.
Aura Is Obscure Because It Is Supposed to Be Invisible
Aura is not a household name, even among many Chrome users who can recite V8, Blink, Skia, and WebGPU from memory. It is part of Chromium’s UI infrastructure, abstracting windowing and event handling across platforms including Windows. In plain English, Aura helps Chrome deal with windows, input, surfaces, focus, and the machinery that lets a browser feel like a native desktop app rather than a pile of web engines duct-taped to a title bar.That makes it an uncomfortable place to see a use-after-free bug. UI frameworks are busy intersections. They receive events, hold references to objects, mediate lifetimes, and translate between the browser’s cross-platform abstractions and the host operating system’s expectations. If memory ownership gets confused there, the impact is rarely easy to summarize.
A use after free occurs when software continues using memory after it has been released. In safe conditions, freed memory should no longer be trusted. In exploitable conditions, an attacker may influence what occupies that memory next, turning an ordinary logic error into a primitive for code execution, privilege movement, or state corruption.
The CVE’s Windows-only language is notable. Chromium runs everywhere, but Aura’s relationship with platform-specific windowing behavior can make bugs appear differently across operating systems. In this case, the advisory scope says Google Chrome on Windows before 148.0.7778.96 is the exposed combination, which is exactly the sort of platform-specific edge case enterprise teams can miss if they track “Chrome” as one monolithic product.
The CVSS Score Tells You the Exploit Chain Is the Product
CISA’s ADP scoring gives CVE-2026-7911 a CVSS 3.1 base score of 8.3, rated high, with network attack vector, high attack complexity, no privileges required, and required user interaction. The scope is changed, and the confidentiality, integrity, and availability impacts are all rated high. That is a compact way of saying: this is not trivially exploitable in isolation, but if the pieces line up, the consequences are serious.The high attack complexity is doing real work here. An attacker needs more than a simple drive-by page. The published description says the attacker must already have compromised the renderer process, which implies a separate vulnerability, malicious content primitive, or chained condition. That is why the bug should not be described as a one-click full-system takeover.
But high complexity should not be mistaken for low urgency. Sophisticated browser exploit chains are assembled exactly this way: a renderer bug, a sandbox escape, perhaps a kernel or broker abuse afterward, then persistence or credential access. The exploit developer’s job is to turn a sequence of unlikely events into a repeatable process.
The user-interaction requirement is also less comforting than it sounds. In browser CVEs, user interaction often means visiting or being directed to a malicious page. That is not a high bar in an enterprise where phishing, malvertising, compromised legitimate sites, and abused collaboration links are routine delivery mechanisms.
Chrome 148 Looks Like a Routine Rollout Until You Count the Repairs
Chrome 148 landed on the stable desktop channel on May 5, 2026, with version 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS. The extended stable channel for Windows and macOS moved to 148.0.7778.97. Reporting around the release noted more than 100 security fixes, with several critical vulnerabilities elsewhere in the browser stack.That scale matters. A single CVE can look isolated on a vulnerability-management screen, but Chrome 148 is a broad security release. CVE-2026-7911 is one tile in a mosaic of memory-safety, validation, and implementation fixes across a codebase that now functions as a near-operating-system runtime for much of the modern desktop.
The release also demonstrates Google’s familiar disclosure posture. The public record identifies the affected component, weakness class, version boundary, and broad attack condition, while detailed bug links may remain restricted until enough users have updated. That frustrates defenders who want full technical detail immediately, but it is also a recognition that a patch diff can become an exploit guide.
This is the browser security bargain in 2026: vendors patch fast, disclose narrowly, and rely on automatic update plumbing to close the window before reverse engineers widen it. Enterprises that interrupt that plumbing inherit the risk. If Chrome updates are delayed for testing, packaging, or change-control reasons, the organization is effectively choosing to sit in the interval between “the bug is known” and “the exploit is commoditized.”
Microsoft’s Appearance in the Record Is a Signal, Not a Windows Patch
The MSRC listing may confuse some readers because the CVE is about Google Chrome, not a Windows component. Microsoft tracks browser and Chromium-related vulnerabilities where they matter to Microsoft customers, especially because Chromium underpins Microsoft Edge and because Windows fleets often inventory CVEs through Microsoft-centered tooling. But the fix boundary in the description is Chrome before 148.0.7778.96 on Windows.That distinction is operationally important. Waiting for Windows Update alone is the wrong response if the vulnerable product is Chrome. A fully patched Windows machine can still be running an exposed Chrome build if third-party application updates are lagging, blocked, or pinned.
The CPE note in the NVD change history is also worth parsing carefully. The listed configuration combines Google Chrome versions up to but excluding 148.0.7778.96 with Microsoft Windows. That is not saying Windows itself contains the vulnerable code. It is saying the vulnerable software configuration is Chrome on Windows.
This is where asset inventory often goes sideways. Security teams that manage Microsoft patches with discipline sometimes have weaker visibility into browser variants, user-installed builds, unmanaged profiles, portable browsers, and Chromium-based derivatives. CVE-2026-7911 is the kind of bug that rewards boring hygiene: know which browsers are installed, know which channel they are on, and know whether they actually updated.
Edge, Chromium Derivatives, and the Lag Problem
The advisory names Google Chrome, but Chromium vulnerabilities rarely stay conceptually confined to one brand. Microsoft Edge, Brave, Vivaldi, Opera, and other Chromium-based browsers share large portions of the underlying codebase, though exposure depends on whether the vulnerable component is present, enabled, modified, or reachable in that product. Administrators should not assume immunity simply because the browser icon is different.The responsible move is to check each vendor’s release notes and version mapping rather than mechanically applying Chrome’s version number to every Chromium product. Edge, for example, follows its own release cadence and versioning even when it integrates Chromium fixes. Other vendors may lag by hours or days, particularly around major stable updates.
This is especially relevant for organizations that standardize on Edge but leave Chrome installed “just in case,” or vice versa. The second browser tends to receive less policy attention and less user education, yet it remains a full attack surface. A dormant browser with an old version is not dormant if a URL handler, embedded workflow, or user habit wakes it up.
The same logic applies to software that embeds Chromium. Not every embedded Chromium runtime is affected by this specific CVE, and the Windows Chrome/Aura wording should keep us from overgeneralizing. But the broader lesson is that Chromium has become infrastructure. Treating it as a single consumer app understates how many places its code can appear.
The Real Risk Is Not Today’s Bug but Tomorrow’s Chain
There is no public indication in the provided record that CVE-2026-7911 is being exploited in the wild. That matters, and it should keep defenders from overstating the case. This is a high-severity vulnerability with serious chaining potential, not a confirmed emergency zero-day based on the current public description.Still, exploitability changes after disclosure. Once a patch ships, attackers can study changed code, infer the flaw, and test whether vulnerable builds remain common enough to justify weaponization. Browser bugs age badly because the delta between fixed and unfixed machines becomes the attacker’s market map.
The phrase “sandbox escape” should also focus attention on endpoint detection. A renderer compromise alone may look like browser weirdness, a crashed tab, or an exploit attempt blocked by containment. A successful escape is more likely to interact with files, processes, tokens, IPC mechanisms, or OS APIs in ways that endpoint tools can observe.
That means patching is step one, not the entire defense. Security teams should watch for suspicious browser child-process behavior, unexpected process spawning, unusual command-line patterns, and browser-to-system transitions that do not match ordinary user activity. The less you know about the exploit details, the more you lean on behavioral detection around the boundary it is trying to cross.
The Patch Management Lesson Is Brutally Mundane
Chrome’s auto-update model is one of the most effective security mechanisms on the consumer web. In enterprises, it is often partially disabled, deferred, proxied, repackaged, or subordinated to patch windows. Those choices may be necessary, but they convert Google’s update velocity into the organization’s operational risk.For CVE-2026-7911, the target state is simple: Chrome on Windows should be at 148.0.7778.96 or later, with extended stable environments on the corresponding fixed build. The hard part is proving that state across real machines. Browser version reporting in endpoint-management platforms can lag, users can keep sessions open, and some update mechanisms require a browser restart before the patched binary is actually in use.
This is where a surprising number of organizations fail. They deploy the update package, mark the job complete, and never verify that users relaunched. Chrome may download the patch, but the old process can remain alive. In a vulnerability involving web content and browser process boundaries, that distinction is not clerical.
Admins should also resist the temptation to treat “high attack complexity” as a reason to wait. High-complexity bugs are often the ones that separate opportunistic crime from serious operators. If your threat model includes targeted phishing, credential theft, espionage, or ransomware crews buying access from exploit brokers, the complexity belongs to the attacker’s engineering team, not your risk register.
Memory Safety Keeps Sending the Same Invoice
CVE-2026-7911 is another reminder that browser security remains haunted by memory lifetime bugs. Use-after-free vulnerabilities have been with us for decades because high-performance C and C++ code makes object ownership both powerful and perilous. Browsers intensify the problem by combining enormous codebases, asynchronous events, untrusted input, graphics pipelines, UI frameworks, sandbox brokers, and platform integration.Google has spent years investing in sandboxing, site isolation, fuzzing, MiraclePtr-style mitigations, hardened allocators, and gradual memory-safety improvements. Those efforts have made exploitation harder. They have not made memory bugs disappear.
The uncomfortable truth is that mitigations change the shape of exploitation more than they end it. A use-after-free that might once have been straightforward remote code execution may now require heap grooming, renderer compromise, object-shape knowledge, and a second primitive. That is progress. It is also why the CVE reads like a chain component rather than a complete attack.
For defenders, this means severity should be interpreted in context. A high-severity sandbox escape may be more strategically important than a flashier bug with a simpler description. The browser’s security model is layered; flaws that connect layers are valuable.
Windows Is Where Browser Bugs Become Fleet Problems
The Windows specificity in CVE-2026-7911 gives this issue a particular enterprise flavor. Windows desktops remain the default knowledge-worker endpoint, the place where browsers, identity providers, password managers, collaboration suites, VPN clients, EDR agents, and legacy line-of-business applications all converge. A browser sandbox escape on Windows is not just a browser story; it is an identity and endpoint story.The modern Windows desktop is also browser-mediated in a way that did not exist a decade ago. SaaS admin portals, device-management consoles, cloud dashboards, HR systems, ticketing platforms, developer tools, and internal applications all run through tabs. Compromise the right browser session and the attacker may not need to install much at all.
That is why the “remote attacker” language should not be read narrowly. The remote attacker may be delivering a page, but the prize is local context: the user’s session, the machine’s trust relationships, and the browser’s position as an authenticated control plane. Even without a full operating-system takeover, escaping a renderer can open paths that defenders would rather keep sealed.
Windows shops should pair patch deployment with session hygiene. Force browser restarts where policy allows. Confirm version compliance. Revisit whether high-risk users—administrators, finance staff, developers, help-desk personnel—are allowed to run stale browser sessions indefinitely. The browser is now privileged by proximity, even when the OS does not formally treat it that way.
The Quiet Fix That Should Change the Week’s Patch Priorities
CVE-2026-7911 will not be the most dramatic vulnerability name of the year. It has no logo, no catchy exploit brand, and no public proof-of-concept attached to the basic advisory record. Its importance comes from where it sits: inside the browser UI substrate, on Windows, at the sandbox boundary, in a release packed with other security repairs.That makes the operational guidance unusually straightforward.
- Chrome on Windows should be updated to 148.0.7778.96 or later, and administrators should verify the running browser version after restart rather than trusting deployment status alone.
- The vulnerability should be treated as a potential exploit-chain component, because the public description requires a prior renderer compromise before the sandbox escape path becomes relevant.
- Windows Update alone is not a sufficient mitigation for Google Chrome installations, even when the CVE appears in Microsoft security tracking.
- Chromium-based browsers and embedded runtimes should be reviewed separately, because shared code does not always mean identical exposure or identical patch timing.
- Security monitoring should pay attention to browser process behavior that crosses expected boundaries, especially child-process launches, unusual command lines, and suspicious interactions with local resources.
- Change-control policies that delay browser updates should be revisited for high-severity sandbox escapes, because the patch-diff window is often where attacker interest accelerates.
Chrome 148 closes this particular hole, but the larger direction is clear: attackers will keep looking for the seams between renderer isolation, UI frameworks, operating-system integration, and enterprise delay. The winners will not be the organizations that memorize every Chromium component name. They will be the ones that can turn a vendor’s fixed version into a verified fleet state before a quiet sandbox bug becomes the second act of someone else’s exploit chain.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center