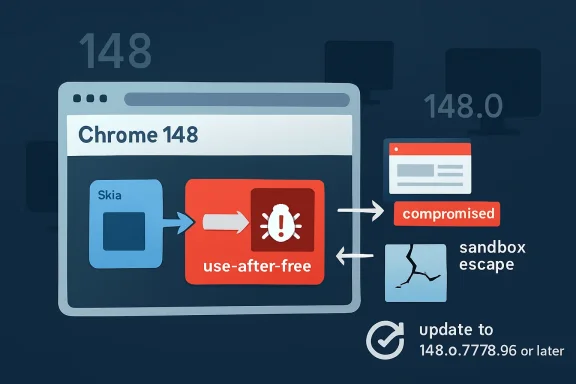
On May 6, 2026, CVE-2026-7920 was published as a high-severity Chromium vulnerability in Skia affecting Google Chrome before version 148.0.7778.96, with Microsoft tracking it for Edge because Edge inherits Chromium’s security debt. The bug is not a garden-variety browser crash. It is a use-after-free flaw that could help an attacker escape the renderer sandbox after first compromising the renderer process. That sequencing matters: the vulnerability is dangerous precisely because modern browser attacks are rarely one bug anymore — they are chains.
CVE-2026-7920 is formally a Chromium issue, but in practical enterprise life there is no such thing as “just a Chrome bug.” Chromium is the engine room for Google Chrome, Microsoft Edge, Brave, Opera, Vivaldi, and a long tail of embedded browser surfaces. When Chromium takes a security update, the race begins for every downstream vendor and every administrator who has standardized on a Chromium-based browser.
The vulnerable component is Skia, Google’s open-source 2D graphics library. Skia is one of those foundational technologies most users will never knowingly touch, yet they rely on it every time a browser paints text, shapes, images, and interface elements. If Blink is the browser’s understanding of the page, Skia is part of how that understanding becomes pixels.
That makes Skia a high-value target. Graphics code consumes a steady stream of complex, attacker-influenced data: fonts, images, CSS effects, canvas operations, SVGs, composited layers, and all the weird edge cases modern web applications generate in the name of looking effortless. The browser’s visual layer is no longer a passive output device. It is a sprawling parser and renderer for hostile input.
The CVE description says exploitation requires a remote attacker who has already compromised the renderer process. That clause may sound reassuring to casual readers, but it should not reassure administrators. It means CVE-2026-7920 is positioned as a second-stage escape route: not necessarily the first door into the browser, but potentially the door from the browser into the wider machine.
A renderer compromise by itself is bad, but it is not automatically catastrophic. The attacker may gain code execution inside a restricted process with limited access to files, devices, credentials, and operating system primitives. The victim has still been compromised, but the browser’s architecture tries to keep that compromise from becoming a full desktop foothold.
Sandbox escapes are the answer to that architecture. They are the bugs that make a renderer exploit worth more. If an attacker can pair an initial renderer vulnerability with a sandbox escape, the attack moves from “the malicious page broke the tab” toward “the malicious page may now break out into the operating system.”
That is why CVE-2026-7920’s phrasing is so important. “Had compromised the renderer process” is not an obscure precondition; it is the language of exploit chaining. The web attack model in 2026 is not a single brilliant bug smashing through every defense. It is staged intrusion, and each stage asks whether the next boundary can be crossed.
This class of bug has haunted C and C++ software for decades because it sits at the intersection of performance and trust. Browsers are performance-obsessed programs that must parse untrusted input at enormous speed, across multiple threads, with caches, GPU acceleration, speculative execution paths, and deeply optimized rendering pipelines. That is fertile ground for object-lifetime mistakes.
The industry has spent years building mitigations around memory corruption: sandboxing, control-flow integrity, hardened allocators, partitioned heaps, MiraclePtr-style protections, site isolation, and fuzzing at industrial scale. Those defenses help. They also explain why a single memory bug may now require specific conditions, timing, or an accompanying exploit to become operationally useful.
But the persistence of use-after-free vulnerabilities in browser advisories tells us something uncomfortable. The browser security model is not failing because nobody understands the problem. It is straining because the problem is embedded in the economics of web compatibility and high-performance native code.
A malicious page can shape layout, trigger repaint paths, animate transitions, manipulate canvas, load web fonts, apply filters, stress compositing, and exercise uncommon code paths that normal browsing may rarely touch. The more expressive the web becomes, the more states the renderer must support. Skia sits in the path of that expressiveness.
Skia also appears beyond Chrome. It is used across Google’s ecosystem and in other projects, and its design reflects the reality that graphics libraries are shared infrastructure. A vulnerability in such a library can matter differently depending on the embedding application, the sandbox around it, and the reachable code path. In Chrome’s case, the CVE specifically frames the risk as a sandbox escape after renderer compromise.
That distinction should shape response. This is not a reason to panic about every Skia-using application. It is a reason to patch Chromium-based browsers promptly, because the browser is where Skia receives hostile web content by design.
For consumers, browser auto-update is supposed to make this nearly invisible. Chrome downloads, relaunches, and the version number advances. For IT teams, invisibility is not enough. They need to know whether managed endpoints have actually moved, whether dormant browsers have updated, and whether secondary Chromium-based browsers are lagging behind.
The Chrome 148 release is also broader than CVE-2026-7920. Reporting around the release notes pointed to a large security haul, including more than 100 fixes and several critical issues. CVE-2026-7920 is one entry in that larger patch wave, but it is notable because it touches the sandbox boundary and because Microsoft’s ecosystem inevitably amplifies the relevance for Windows shops.
That is the recurring awkwardness of Chromium security. Google may publish the canonical Chrome fix, but the operational footprint extends into Edge policies, Windows images, virtual desktops, application control baselines, vulnerability scanners, and compliance dashboards. The patch is a browser update; the work is fleet management.
Microsoft’s security update process for Edge often tracks Chromium fixes through MSRC and Edge release notes. When a Chromium vulnerability appears, Edge administrators must watch for whether Microsoft has shipped the corresponding Edge stable or extended stable update. The lag may be brief, but in high-severity browser bugs, brief is still a measurable exposure window.
CVE-2026-7920 is therefore a reminder that “Microsoft browser security” in 2026 is partly a supply-chain question. The vulnerable code may originate upstream. The advisory may be mirrored or referenced through MSRC. The patch may arrive through Edge Update rather than Windows Update. The inventory evidence may live in Intune, Defender, ConfigMgr, third-party EDR, or a vulnerability management platform.
That fragmentation is manageable, but only if administrators treat browsers as first-class software, not accessories. Edge is part of the Windows security perimeter now. So is Chrome, if it is installed. So is any Chromium-based browser approved, tolerated, or merely forgotten on endpoints.
A CPE entry is useful for scanners and compliance tools, but it can flatten reality. Chrome on Windows, Chrome on macOS, Chrome on Linux, Edge on Windows, Edge on macOS, embedded Chromium components, Electron applications, and Linux distributions’ Chromium packages all sit at different points in the same dependency ecosystem. A CVE may begin in Chromium, but its appearance in inventory depends on product packaging and vendor mapping.
That is why administrators should be cautious about treating a single CPE match as the whole exposure story. If a scanner detects vulnerable Google Chrome, good. If it misses Edge because the CVE is tracked through a different vendor mapping, bad. If it ignores an unmanaged portable browser in a user profile, worse.
The right lesson is not that CPEs are useless. They are indispensable. The lesson is that CPEs are a starting point for asset intelligence, not a substitute for it.
Those constraints reduce the likelihood of a trivial one-click catastrophe. They do not make the bug low priority. Browser exploit chains routinely combine a renderer flaw with an escape flaw, and user interaction in a web context can mean little more than persuading someone to visit a page or click a link. That is the daily operating environment of phishing, malvertising, compromised websites, and watering-hole attacks.
The CISA ADP score of 8.3 reflects that balance: high impact across confidentiality, integrity, and availability, but high attack complexity because the attacker needs a particular chain of conditions. In plain English, CVE-2026-7920 is probably not the easiest bug in the Chrome 148 batch to weaponize. It may still be one of the more valuable bugs to an attacker who already has the first half of the chain.
That is exactly how defenders should think about it. Patch not because every vulnerability is equally exploitable, but because exploit developers assemble portfolios. A sandbox escape sitting unpatched on endpoints is useful inventory for the wrong side.
Chrome’s rapid release cycle and Edge’s Chromium-based cadence have normalized frequent browser changes. That creates regression anxiety, especially in environments with legacy web apps, brittle browser extensions, kiosk modes, VDI images, or tightly controlled desktops. But delaying browser patches now means accepting exposure to bugs that are often directly reachable from the public internet.
The real choice is not between stability and security. It is between disciplined update rings and unmanaged delay. Enterprises can test with beta and extended stable channels, stage deployment by cohort, monitor crash and helpdesk signals, and enforce relaunch deadlines. What they cannot safely do is allow browser versions to drift because browser patching feels less formal than Patch Tuesday.
CVE-2026-7920 is a good example because the fix lands outside the mental model many Windows admins still carry. It is not primarily a cumulative Windows update. It is a Chromium browser update that matters to Windows endpoints.
A slower channel can be safer operationally if it prevents chaos. It can be riskier if it becomes an excuse for delayed security response. The question is not whether an organization uses Stable or Extended Stable; the question is whether it has a policy for exceptions when Chromium ships high-impact security patches.
For a vulnerability like CVE-2026-7920, the key control is not merely “which channel are we on?” It is “how quickly can we prove every browser crossed the fixed version boundary?” That proof matters because browser updates often require a restart or relaunch. A machine may have downloaded the update without applying it to running sessions.
This is where policy meets user behavior. Administrators can push updates, but users can leave browsers open for days. The last mile of browser patching is often not download; it is process replacement.
That gap matters because attackers do not care which browser procurement approved. They care which executable a user can run and which one can reach the network. A patched Edge default is excellent, but it does not neutralize an unpatched Chrome installation used by a developer for testing or a portable browser bundled with a vendor tool.
Electron complicates the picture further, though CVE applicability depends on the Chromium version and reachable components in each application. Security teams should avoid simplistic claims that every Electron app is affected by every Chrome CVE. But they should also avoid the opposite mistake: pretending that browser engine vulnerabilities only matter in full browsers.
The defensible middle position is inventory. Know which Chromium-based surfaces exist, who updates them, and how quickly they pick up upstream fixes. If the answer is “we do not know,” CVE-2026-7920 is another reason to find out.
On unmanaged home systems, the path is simple: open the browser’s About page and let the updater do its work, then relaunch. On managed systems, the work is more procedural. Confirm update policies, enforce relaunch where necessary, query inventory, and look for stragglers.
The most dangerous machines are not always the ones that fail loudly. They are the laptops asleep during deployment, the VDI images refreshed from stale gold masters, the kiosks with locked-down UI but neglected browser engines, and the servers where a browser was installed once for troubleshooting and then forgotten.
A vulnerability like this should trigger a hunt for those edge cases. Not because CVE-2026-7920 is known to be exploited in the wild — public evidence may not show that — but because the cost of leaving a sandbox escape available is not justified by the inconvenience of browser hygiene.
Every major browser release is both a product release and a security event. New APIs expand what web applications can do. Performance work shifts code paths. GPU acceleration changes trust boundaries. Privacy features reshape storage and identity mechanisms. Compatibility requirements keep old behaviors alive long after engineers would prefer to bury them.
Skia’s presence in this advisory fits that pattern. A graphics library is not a glamorous attack surface in the way a JavaScript engine is, but it is deeply exposed and deeply optimized. The web’s demand for richer visuals and smoother interfaces ensures that rendering code will remain an attractive target.
The uncomfortable bargain is that users want browsers to behave like operating systems inside operating systems. They want documents, applications, games, video editors, messengers, password managers, conferencing platforms, and admin consoles to live in tabs. The more the browser becomes the universal application runtime, the more every browser CVE becomes an endpoint security issue.
There is no sign in the public description that CVE-2026-7920 is a simple standalone remote-code execution bug from a cold start. The attacker needs a renderer compromise first. That is the distinction between an urgent patch and a fire alarm. But the browser threat model is built around chains, and sandbox escapes are chain-enablers.
The most mature security programs will not treat this as an isolated ticket. They will use it to test whether browser inventory is accurate, whether update telemetry is timely, whether relaunch enforcement works, and whether exception handling identifies users who are stuck on vulnerable builds for business reasons.
That is the difference between patching and resilience. Patching fixes this bug. Resilience makes the next browser bug less chaotic.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The Browser Bug That Starts in Chrome but Lands on Windows Desks
The Browser Bug That Starts in Chrome but Lands on Windows Desks
CVE-2026-7920 is formally a Chromium issue, but in practical enterprise life there is no such thing as “just a Chrome bug.” Chromium is the engine room for Google Chrome, Microsoft Edge, Brave, Opera, Vivaldi, and a long tail of embedded browser surfaces. When Chromium takes a security update, the race begins for every downstream vendor and every administrator who has standardized on a Chromium-based browser.The vulnerable component is Skia, Google’s open-source 2D graphics library. Skia is one of those foundational technologies most users will never knowingly touch, yet they rely on it every time a browser paints text, shapes, images, and interface elements. If Blink is the browser’s understanding of the page, Skia is part of how that understanding becomes pixels.
That makes Skia a high-value target. Graphics code consumes a steady stream of complex, attacker-influenced data: fonts, images, CSS effects, canvas operations, SVGs, composited layers, and all the weird edge cases modern web applications generate in the name of looking effortless. The browser’s visual layer is no longer a passive output device. It is a sprawling parser and renderer for hostile input.
The CVE description says exploitation requires a remote attacker who has already compromised the renderer process. That clause may sound reassuring to casual readers, but it should not reassure administrators. It means CVE-2026-7920 is positioned as a second-stage escape route: not necessarily the first door into the browser, but potentially the door from the browser into the wider machine.
The Sandbox Is the Wall Attackers Keep Trying to Climb
Modern browsers assume the web is malicious. That is why Chrome and Edge split work across privileged and unprivileged processes, isolate sites, limit renderer privileges, and wrap web content in a sandbox designed to contain the blast radius of a renderer compromise. The renderer is where hostile JavaScript, HTML, CSS, and media meet enormous complexity. The sandbox is supposed to make that danger tolerable.A renderer compromise by itself is bad, but it is not automatically catastrophic. The attacker may gain code execution inside a restricted process with limited access to files, devices, credentials, and operating system primitives. The victim has still been compromised, but the browser’s architecture tries to keep that compromise from becoming a full desktop foothold.
Sandbox escapes are the answer to that architecture. They are the bugs that make a renderer exploit worth more. If an attacker can pair an initial renderer vulnerability with a sandbox escape, the attack moves from “the malicious page broke the tab” toward “the malicious page may now break out into the operating system.”
That is why CVE-2026-7920’s phrasing is so important. “Had compromised the renderer process” is not an obscure precondition; it is the language of exploit chaining. The web attack model in 2026 is not a single brilliant bug smashing through every defense. It is staged intrusion, and each stage asks whether the next boundary can be crossed.
Use-After-Free Remains the Old Ghost in New Code
A use-after-free vulnerability is a memory safety failure in which software continues to use an object after the memory backing it has been released. In benign cases, that produces a crash. In adversarial cases, the freed memory may be reused in a way that lets an attacker influence what the program reads, writes, or calls next.This class of bug has haunted C and C++ software for decades because it sits at the intersection of performance and trust. Browsers are performance-obsessed programs that must parse untrusted input at enormous speed, across multiple threads, with caches, GPU acceleration, speculative execution paths, and deeply optimized rendering pipelines. That is fertile ground for object-lifetime mistakes.
The industry has spent years building mitigations around memory corruption: sandboxing, control-flow integrity, hardened allocators, partitioned heaps, MiraclePtr-style protections, site isolation, and fuzzing at industrial scale. Those defenses help. They also explain why a single memory bug may now require specific conditions, timing, or an accompanying exploit to become operationally useful.
But the persistence of use-after-free vulnerabilities in browser advisories tells us something uncomfortable. The browser security model is not failing because nobody understands the problem. It is straining because the problem is embedded in the economics of web compatibility and high-performance native code.
Skia Is Not a Side Component; It Is Part of the Web’s Attack Surface
It is tempting to think of Skia as “graphics,” and therefore somehow peripheral to browser security. That is the wrong mental model. Rendering is not the end of the pipeline; it is an attack surface fed by almost everything a page can do.A malicious page can shape layout, trigger repaint paths, animate transitions, manipulate canvas, load web fonts, apply filters, stress compositing, and exercise uncommon code paths that normal browsing may rarely touch. The more expressive the web becomes, the more states the renderer must support. Skia sits in the path of that expressiveness.
Skia also appears beyond Chrome. It is used across Google’s ecosystem and in other projects, and its design reflects the reality that graphics libraries are shared infrastructure. A vulnerability in such a library can matter differently depending on the embedding application, the sandbox around it, and the reachable code path. In Chrome’s case, the CVE specifically frames the risk as a sandbox escape after renderer compromise.
That distinction should shape response. This is not a reason to panic about every Skia-using application. It is a reason to patch Chromium-based browsers promptly, because the browser is where Skia receives hostile web content by design.
Chrome 148 Is a Security Release Wearing a Feature Release’s Clothes
Google’s stable-channel update to Chrome 148 arrived for Windows, macOS, and Linux with version 148.0.7778.96 on Linux and 148.0.7778.96 or 148.0.7778.97 on Windows and macOS. As usual, the rollout language allowed for updates over days or weeks. That gradualism is sensible for reliability, but it complicates security messaging.For consumers, browser auto-update is supposed to make this nearly invisible. Chrome downloads, relaunches, and the version number advances. For IT teams, invisibility is not enough. They need to know whether managed endpoints have actually moved, whether dormant browsers have updated, and whether secondary Chromium-based browsers are lagging behind.
The Chrome 148 release is also broader than CVE-2026-7920. Reporting around the release notes pointed to a large security haul, including more than 100 fixes and several critical issues. CVE-2026-7920 is one entry in that larger patch wave, but it is notable because it touches the sandbox boundary and because Microsoft’s ecosystem inevitably amplifies the relevance for Windows shops.
That is the recurring awkwardness of Chromium security. Google may publish the canonical Chrome fix, but the operational footprint extends into Edge policies, Windows images, virtual desktops, application control baselines, vulnerability scanners, and compliance dashboards. The patch is a browser update; the work is fleet management.
Microsoft Edge Turns Chromium Debt Into Windows Debt
Microsoft’s Edge is now Chromium-based, which means it benefits from Google’s browser engineering while inheriting much of Chromium’s vulnerability stream. This trade was strategically rational: Microsoft gained compatibility, performance, and a seat closer to the web platform’s center of gravity. It also meant that Windows administrators could no longer treat Edge security as a purely Microsoft-native matter.Microsoft’s security update process for Edge often tracks Chromium fixes through MSRC and Edge release notes. When a Chromium vulnerability appears, Edge administrators must watch for whether Microsoft has shipped the corresponding Edge stable or extended stable update. The lag may be brief, but in high-severity browser bugs, brief is still a measurable exposure window.
CVE-2026-7920 is therefore a reminder that “Microsoft browser security” in 2026 is partly a supply-chain question. The vulnerable code may originate upstream. The advisory may be mirrored or referenced through MSRC. The patch may arrive through Edge Update rather than Windows Update. The inventory evidence may live in Intune, Defender, ConfigMgr, third-party EDR, or a vulnerability management platform.
That fragmentation is manageable, but only if administrators treat browsers as first-class software, not accessories. Edge is part of the Windows security perimeter now. So is Chrome, if it is installed. So is any Chromium-based browser approved, tolerated, or merely forgotten on endpoints.
The CPE Question Reveals a Bigger Inventory Problem
The NVD change history for CVE-2026-7920 includes a CPE configuration for Google Chrome versions before 148.0.7778.96 across Windows, Linux, and macOS. The user-facing “Are we missing a CPE here?” prompt is routine NVD plumbing, but it points at a real operational headache: vulnerability identity and product identity do not always line up neatly.A CPE entry is useful for scanners and compliance tools, but it can flatten reality. Chrome on Windows, Chrome on macOS, Chrome on Linux, Edge on Windows, Edge on macOS, embedded Chromium components, Electron applications, and Linux distributions’ Chromium packages all sit at different points in the same dependency ecosystem. A CVE may begin in Chromium, but its appearance in inventory depends on product packaging and vendor mapping.
That is why administrators should be cautious about treating a single CPE match as the whole exposure story. If a scanner detects vulnerable Google Chrome, good. If it misses Edge because the CVE is tracked through a different vendor mapping, bad. If it ignores an unmanaged portable browser in a user profile, worse.
The right lesson is not that CPEs are useless. They are indispensable. The lesson is that CPEs are a starting point for asset intelligence, not a substitute for it.
The “Renderer Must Already Be Compromised” Clause Is Not a Get-Out-of-Patching Card
Security teams sometimes triage vulnerabilities by reading for friction. Does exploitation require authentication? Local access? User interaction? A prior compromise? CVE-2026-7920 includes two important constraints: the attacker must compromise the renderer process, and exploitation requires a crafted HTML page with user interaction in the CVSS vector.Those constraints reduce the likelihood of a trivial one-click catastrophe. They do not make the bug low priority. Browser exploit chains routinely combine a renderer flaw with an escape flaw, and user interaction in a web context can mean little more than persuading someone to visit a page or click a link. That is the daily operating environment of phishing, malvertising, compromised websites, and watering-hole attacks.
The CISA ADP score of 8.3 reflects that balance: high impact across confidentiality, integrity, and availability, but high attack complexity because the attacker needs a particular chain of conditions. In plain English, CVE-2026-7920 is probably not the easiest bug in the Chrome 148 batch to weaponize. It may still be one of the more valuable bugs to an attacker who already has the first half of the chain.
That is exactly how defenders should think about it. Patch not because every vulnerability is equally exploitable, but because exploit developers assemble portfolios. A sandbox escape sitting unpatched on endpoints is useful inventory for the wrong side.
Patch Cadence Is Now a Security Control, Not an Administrative Preference
For years, organizations treated browser updates as a nuisance to be scheduled around line-of-business compatibility. That world is gone. The browser is the most exposed client application in the enterprise, and its update cadence is part of the security architecture.Chrome’s rapid release cycle and Edge’s Chromium-based cadence have normalized frequent browser changes. That creates regression anxiety, especially in environments with legacy web apps, brittle browser extensions, kiosk modes, VDI images, or tightly controlled desktops. But delaying browser patches now means accepting exposure to bugs that are often directly reachable from the public internet.
The real choice is not between stability and security. It is between disciplined update rings and unmanaged delay. Enterprises can test with beta and extended stable channels, stage deployment by cohort, monitor crash and helpdesk signals, and enforce relaunch deadlines. What they cannot safely do is allow browser versions to drift because browser patching feels less formal than Patch Tuesday.
CVE-2026-7920 is a good example because the fix lands outside the mental model many Windows admins still carry. It is not primarily a cumulative Windows update. It is a Chromium browser update that matters to Windows endpoints.
Extended Stable Is a Trade, Not a Shield
Extended Stable channels exist because enterprises need predictability. They slow the feature churn and reduce the number of disruptive changes administrators must validate. They do not eliminate the need to ingest urgent security fixes, and they should not be mistaken for a safer channel by default.A slower channel can be safer operationally if it prevents chaos. It can be riskier if it becomes an excuse for delayed security response. The question is not whether an organization uses Stable or Extended Stable; the question is whether it has a policy for exceptions when Chromium ships high-impact security patches.
For a vulnerability like CVE-2026-7920, the key control is not merely “which channel are we on?” It is “how quickly can we prove every browser crossed the fixed version boundary?” That proof matters because browser updates often require a restart or relaunch. A machine may have downloaded the update without applying it to running sessions.
This is where policy meets user behavior. Administrators can push updates, but users can leave browsers open for days. The last mile of browser patching is often not download; it is process replacement.
The Quiet Risk Lives in Secondary Browsers and Forgotten Runtimes
Most enterprises know whether they deploy Edge. Many know whether they allow Chrome. Fewer have a clean picture of secondary browsers, developer-installed builds, portable versions, unmanaged user-space installations, and Chromium-derived runtimes embedded in applications.That gap matters because attackers do not care which browser procurement approved. They care which executable a user can run and which one can reach the network. A patched Edge default is excellent, but it does not neutralize an unpatched Chrome installation used by a developer for testing or a portable browser bundled with a vendor tool.
Electron complicates the picture further, though CVE applicability depends on the Chromium version and reachable components in each application. Security teams should avoid simplistic claims that every Electron app is affected by every Chrome CVE. But they should also avoid the opposite mistake: pretending that browser engine vulnerabilities only matter in full browsers.
The defensible middle position is inventory. Know which Chromium-based surfaces exist, who updates them, and how quickly they pick up upstream fixes. If the answer is “we do not know,” CVE-2026-7920 is another reason to find out.
Windows Shops Should Treat This as an Edge-and-Chrome Event
For WindowsForum readers, the practical response begins with version verification. Chrome should be at least 148.0.7778.96, with Windows and macOS installations possibly showing 148.0.7778.97 depending on channel and rollout. Edge administrators should follow Microsoft’s Edge security release notes and MSRC tracking to confirm when the relevant Chromium fixes have been incorporated into the deployed Edge build.On unmanaged home systems, the path is simple: open the browser’s About page and let the updater do its work, then relaunch. On managed systems, the work is more procedural. Confirm update policies, enforce relaunch where necessary, query inventory, and look for stragglers.
The most dangerous machines are not always the ones that fail loudly. They are the laptops asleep during deployment, the VDI images refreshed from stale gold masters, the kiosks with locked-down UI but neglected browser engines, and the servers where a browser was installed once for troubleshooting and then forgotten.
A vulnerability like this should trigger a hunt for those edge cases. Not because CVE-2026-7920 is known to be exploited in the wild — public evidence may not show that — but because the cost of leaving a sandbox escape available is not justified by the inconvenience of browser hygiene.
The Security Story Is Bigger Than One CVE
The industry’s response to browser vulnerabilities often feels rote: advisory appears, version number advances, scanner plugin updates, admins chase compliance, and everyone waits for the next CVE. That routine is necessary, but it can obscure the larger story. Browser security is now a continuous campaign against complexity.Every major browser release is both a product release and a security event. New APIs expand what web applications can do. Performance work shifts code paths. GPU acceleration changes trust boundaries. Privacy features reshape storage and identity mechanisms. Compatibility requirements keep old behaviors alive long after engineers would prefer to bury them.
Skia’s presence in this advisory fits that pattern. A graphics library is not a glamorous attack surface in the way a JavaScript engine is, but it is deeply exposed and deeply optimized. The web’s demand for richer visuals and smoother interfaces ensures that rendering code will remain an attractive target.
The uncomfortable bargain is that users want browsers to behave like operating systems inside operating systems. They want documents, applications, games, video editors, messengers, password managers, conferencing platforms, and admin consoles to live in tabs. The more the browser becomes the universal application runtime, the more every browser CVE becomes an endpoint security issue.
The Fixed Version Is the Only Version That Matters This Week
Security advisories can invite over-analysis. Teams debate CVSS, exploitability, exploit maturity, affected platforms, and compensating controls. Those debates have value, but they should not delay the obvious action here: move affected Chrome installations to 148.0.7778.96 or later and track the corresponding Edge update status until all managed endpoints are covered.There is no sign in the public description that CVE-2026-7920 is a simple standalone remote-code execution bug from a cold start. The attacker needs a renderer compromise first. That is the distinction between an urgent patch and a fire alarm. But the browser threat model is built around chains, and sandbox escapes are chain-enablers.
The most mature security programs will not treat this as an isolated ticket. They will use it to test whether browser inventory is accurate, whether update telemetry is timely, whether relaunch enforcement works, and whether exception handling identifies users who are stuck on vulnerable builds for business reasons.
That is the difference between patching and resilience. Patching fixes this bug. Resilience makes the next browser bug less chaotic.
The Version Number Is the Message Administrators Can Act On
CVE-2026-7920 is technical, but the response should be concrete. The advisory language can be reduced to a few operational facts that matter more than the surrounding noise.- Chrome versions before 148.0.7778.96 are the affected line identified for this Skia use-after-free vulnerability.
- The bug is dangerous because it may support a sandbox escape after the renderer process has already been compromised.
- The attack path involves a crafted HTML page, so web browsing remains the relevant exposure surface.
- Windows, macOS, and Linux fleets should be checked because the Chrome stable update applies across desktop platforms.
- Microsoft Edge administrators should track Edge security updates separately, because Edge receives Chromium fixes through Microsoft’s release process.
- Vulnerability scanners should be treated as evidence, not certainty, unless they can account for secondary browsers and unmanaged Chromium-based installations.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center