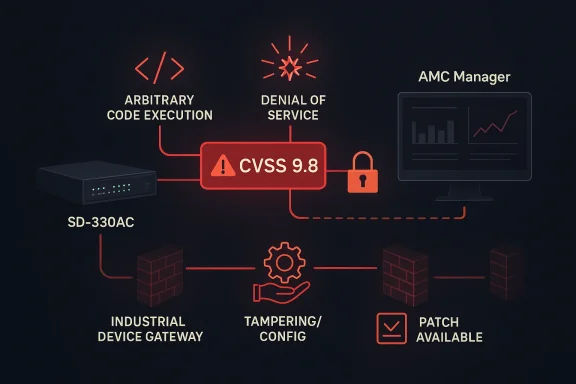
Silex Technology’s SD-330AC and AMC Manager have landed in the spotlight after CISA published a fresh industrial control systems advisory on April 21, 2026, warning that a long list of vulnerabilities could enable arbitrary code execution, denial of service, or unauthorized changes to configuration data. The advisory assigns a CVSS 9.8 severity and says the affected versions include SD-330AC 1.42 and earlier and AMC Manager 5.0.2 and earlier, with a mix of issues ranging from stack and heap overflows to missing authentication, hard-coded cryptographic keys, and XSS. CISA also notes that no known public exploitation has been reported yet, but that should not be mistaken for safety; for network-facing device software, the gap between disclosure and exploitation can be brutally short.
The immediate story is straightforward: CISA has issued an ICS advisory for a Silex Technology product line that sits in a category many organizations still underestimate. SD-330AC is a device connectivity product, and AMC Manager is the management software associated with that ecosystem. In practice, this puts the advisory squarely in the long tail of enterprise and industrial infrastructure where printers, serial devices, embedded gateways, and remote management utilities quietly connect operational systems to larger business networks.
What makes this advisory notable is not just the severity score, but the density of vulnerability types bundled into a single product family. CISA lists a broad set of CVEs, including multiple 2026 issues alongside older entries such as CVE-2015-5621 and CVE-2024-24487. That mix strongly suggests a legacy codebase with accumulated risk rather than a one-off bug, which is often how embedded and appliance security failures become systemic. The result is a threat profile that can span code execution, integrity compromise, and service disruption all at once.
This is also part of a much larger pattern in the market. Forescout has repeatedly warned that routers and connected edge devices are a rich source of exploitable n-day vulnerabilities, and that outdated software components in OT/IoT firmware can expose organizations to chains of weaknesses that are hard to detect and harder to patch. In other words, this Silex advisory is not an isolated embarrassment; it fits a familiar and increasingly expensive category of device risk where the management plane becomes the attack plane.
For security teams, the real issue is exposure management. Microsoft’s OT guidance emphasizes that these kinds of devices should be treated as part of a segmented, monitored, least-privilege environment, with strong segmentation, jump hosts, and careful control of remote access. That lines up closely with CISA’s own recommendation to keep control system devices off the public internet and behind firewalls. The lesson is boring but essential: if a device is built to bridge networks, then it is already part of your trust boundary whether you like it or not.
The challenge is partly technical and partly organizational. Embedded products often ship with constrained update models, legacy web stacks, older crypto libraries, and assumptions that they’ll run in trusted internal networks forever. Those assumptions age badly. Once the management interface, device portal, or companion software is reachable across a flat network, the old “it’s just a printer-adjacent box” mindset stops holding up.
In practice, this means a compromised management interface can become a staging point. An attacker may not need to “own” the network immediately; they may only need to alter configuration, intercept traffic, or drop a payload onto an attached asset. Once a device has a foothold and an administrator trusts it, the hard part is already over.
The most obvious path is the one that starts with the network. CISA’s advisory explicitly recommends minimizing network exposure and placing control system assets behind firewalls. That advice is not generic boilerplate; it reflects the reality that exposed management surfaces are often the shortest path from reconnaissance to impact.
The second problem is operational continuity. Organizations often rely on device connectivity gear because it sits between ordinary IT systems and equipment that cannot be taken offline lightly. That creates pressure to delay updates, widen firewall exceptions, or keep legacy remote access paths open “just until the next maintenance window.” Those exceptions are where a lot of long-lived compromise begins.
A well-run enterprise should already have compensating controls, but this advisory is a reminder that asset inventory is a security control, not an administrative luxury. If you cannot identify every SD-330AC or AMC Manager instance, then you cannot know whether exposure is contained, patched, or actively exploitable. That uncertainty is operational debt.
CISA’s recommended practices stress isolating control system networks and remote devices from business networks and avoiding direct internet exposure. That is consistent with longstanding ICS guidance, but the practical importance keeps growing because devices increasingly ship with cloud-friendly admin features and remote management expectations. The more “IT-like” embedded products become, the more they inherit IT-style attack surfaces without always inheriting IT-grade security.
A modern defender therefore has to treat device-management software as a first-class asset. If a vendor issue allows unauthorized configuration changes, then the product is no longer just a convenience layer; it is part of the system of record for physical or operational connectivity. That elevates the urgency of patching and segmentation.
This is part of a broader trend in which specialized OT and IoT security researchers keep surfacing clustered vulnerability sets in embedded ecosystems. Forescout, in particular, has spent years publishing work on device risk, protocol abuse, and firmware-level weaknesses. That body of research gives defenders context: a single advisory is not the whole story, but another data point in a longer pattern of weak assumptions in networked device design.
The practical challenge for researchers is that embedded systems are often under-instrumented. Telemetry is sparse, logs are minimal, and owners may not even know the software is present. That means vulnerability discovery often outpaces asset visibility, and defenders are left racing to understand where the issue lives before attackers do.
The second priority is authentication hardening. If any interface or function remains reachable with weak, default, or missing authentication, then the organization should treat that as an urgent exposure to be corrected or isolated. Microsoft’s guidance on OT and enterprise IoT also points to strong authentication, privileged access controls, and segmented access paths as foundational protections.
The second question is whether vendors and buyers will use disclosures like this to reset expectations for connectivity gear. Enterprises can no longer afford to buy devices that depend on trust, flat networks, and outdated web stacks as their security model. The market keeps moving toward more connected, more remote, and more distributed operations, which means the security bar for these products has to rise with it.
Source: CISA Silex Technology SD-330AC and AMC Manager | CISA
 Background
Background
The immediate story is straightforward: CISA has issued an ICS advisory for a Silex Technology product line that sits in a category many organizations still underestimate. SD-330AC is a device connectivity product, and AMC Manager is the management software associated with that ecosystem. In practice, this puts the advisory squarely in the long tail of enterprise and industrial infrastructure where printers, serial devices, embedded gateways, and remote management utilities quietly connect operational systems to larger business networks.What makes this advisory notable is not just the severity score, but the density of vulnerability types bundled into a single product family. CISA lists a broad set of CVEs, including multiple 2026 issues alongside older entries such as CVE-2015-5621 and CVE-2024-24487. That mix strongly suggests a legacy codebase with accumulated risk rather than a one-off bug, which is often how embedded and appliance security failures become systemic. The result is a threat profile that can span code execution, integrity compromise, and service disruption all at once.
This is also part of a much larger pattern in the market. Forescout has repeatedly warned that routers and connected edge devices are a rich source of exploitable n-day vulnerabilities, and that outdated software components in OT/IoT firmware can expose organizations to chains of weaknesses that are hard to detect and harder to patch. In other words, this Silex advisory is not an isolated embarrassment; it fits a familiar and increasingly expensive category of device risk where the management plane becomes the attack plane.
For security teams, the real issue is exposure management. Microsoft’s OT guidance emphasizes that these kinds of devices should be treated as part of a segmented, monitored, least-privilege environment, with strong segmentation, jump hosts, and careful control of remote access. That lines up closely with CISA’s own recommendation to keep control system devices off the public internet and behind firewalls. The lesson is boring but essential: if a device is built to bridge networks, then it is already part of your trust boundary whether you like it or not.
What CISA Actually Said
CISA’s advisory identifies the affected product versions as SD-330AC <= 1.42 and AMC Manager <= 5.0.2, and it classifies the overall risk as CVSS Vendor Equipment Vulnerabilities v3 9.8. That score implies a network-reachable issue that can often be exploited with little friction if the target is exposed and poorly hardened. CISA’s summary says exploitation could permit arbitrary code execution, denial of service, or unauthorized configuration changes.The vulnerability mix matters
The advisory is especially concerning because the listed issues are not all the same kind of flaw. Among them are stack-based buffer overflow, heap-based buffer overflow, missing authentication for critical functions, hard-coded cryptographic keys, broken or risky cryptographic algorithms, XSS, CRLF injection, and insecure default initialization. That variety implies multiple attack surfaces, not just one code path that needs one fix.Why the score is so high
A 9.8 rating typically reflects a combination of remote reachability, low attack complexity, no privileges required, and significant impact. In a device-management context, that usually means an attacker may be able to interact directly with a web interface, API, or service exposed on the network. If the target is reachable from a business LAN—or worse, from the internet—the practical risk rises fast.- The advisory covers both firmware/device software and management software.
- Multiple CVEs indicate a broader assurance problem.
- The same weaknesses can enable both direct compromise and lateral movement.
- High-severity embedded flaws often remain exploitable long after disclosure.
- Mixed vulnerability classes usually complicate remediation and testing.
Why Embedded Connectivity Gear Is So Hard to Secure
Devices like SD-330AC tend to live in the awkward space between IT and OT. They are not glamorous, but they often sit in the path of workflows that matter: production lines, label printers, device consoles, scanners, access-control endpoints, and other systems that are expensive or disruptive to replace. That makes them a classic example of small device, large blast radius risk.The challenge is partly technical and partly organizational. Embedded products often ship with constrained update models, legacy web stacks, older crypto libraries, and assumptions that they’ll run in trusted internal networks forever. Those assumptions age badly. Once the management interface, device portal, or companion software is reachable across a flat network, the old “it’s just a printer-adjacent box” mindset stops holding up.
The trust-boundary problem
Microsoft’s guidance on OT and enterprise IoT security stresses segmentation, jump hosts, and controlled remote access because unmanaged or semi-managed devices are common lateral-movement footholds. That advice applies here even if the Silex products are deployed outside classic factories, because printers, serial bridges, and device servers often occupy the same architectural niche: they connect things that were never meant to be directly exposed.In practice, this means a compromised management interface can become a staging point. An attacker may not need to “own” the network immediately; they may only need to alter configuration, intercept traffic, or drop a payload onto an attached asset. Once a device has a foothold and an administrator trusts it, the hard part is already over.
Legacy code and accumulated risk
The presence of older CVEs alongside newly numbered ones is a warning sign that the product family may have inherited risk across multiple development cycles. That does not prove negligence, but it does suggest the sort of technical debt that embedded vendors often struggle to retire quickly. For defenders, the key implication is that patching one issue is unlikely to eliminate the broader class of exposure.- Legacy components tend to carry unresolved attack patterns.
- Web interfaces in embedded gear are frequent XSS and injection targets.
- Hard-coded secrets make post-compromise recovery harder.
- Vulnerable third-party components can reintroduce known bugs after vendor fixes.
- Insecure defaults are especially dangerous in fleet deployments.
The Exploit Paths Defenders Should Assume
Even without confirmed public exploitation, defenders should think in terms of plausible attacker workflows. A remote attacker may target the web management plane, discover authentication gaps, and then pivot into configuration changes or arbitrary code execution. If the system exposes vulnerable input handling, then buffer overflows and injection issues become a direct route to takeover or persistent disruption.The most obvious path is the one that starts with the network. CISA’s advisory explicitly recommends minimizing network exposure and placing control system assets behind firewalls. That advice is not generic boilerplate; it reflects the reality that exposed management surfaces are often the shortest path from reconnaissance to impact.
Authentication gaps change the game
A missing authentication for critical function vulnerability can be worse than a memory corruption bug in one sense, because it removes the need to break in before causing damage. If a function intended only for administrators is reachable without proper checks, an attacker may be able to alter configuration, disable services, or create a condition that later facilitates code execution. That is why “no login required” flaws routinely become the first link in real-world intrusion chains.Web bugs are not just cosmetic
The advisory also mentions XSS and CRLF injection, which some organizations still treat as lower-tier issues. On a management interface, that would be a mistake. Cross-site scripting can support session theft, admin impersonation, or malicious action chaining, while CRLF injection can interfere with headers, logs, or request handling in ways that enable broader abuse. In embedded admin panels, “minor” web bugs often become major control issues.- Attackers often chain multiple low-level flaws.
- Web UIs are especially risky when used for device administration.
- Insecure defaults can be exploited at scale against uncustomized deployments.
- Hard-coded keys can break confidentiality even after patching.
- Memory corruption flaws can become remote code execution with the right conditions.
What This Means for Enterprises
For enterprises, the risk profile is usually broader than a single vulnerable device. These devices may be installed in offices, plants, warehouses, hospitals, labs, or branch locations, often by different teams that do not keep a precise inventory. That means the first problem is not merely patching, but finding every instance and understanding how it is connected. Microsoft’s IoT guidance emphasizes visibility into unmanaged devices because blind spots are what attackers exploit first.The second problem is operational continuity. Organizations often rely on device connectivity gear because it sits between ordinary IT systems and equipment that cannot be taken offline lightly. That creates pressure to delay updates, widen firewall exceptions, or keep legacy remote access paths open “just until the next maintenance window.” Those exceptions are where a lot of long-lived compromise begins.
Enterprise vs. consumer impact
For consumers, the practical impact may be limited to home-office gear, small business printers, or niche connectivity setups. For enterprises, however, a vulnerable device manager can sit inside a privileged internal network and touch critical workflows. The same vulnerability can therefore move from nuisance to serious business risk simply based on where it is deployed.A well-run enterprise should already have compensating controls, but this advisory is a reminder that asset inventory is a security control, not an administrative luxury. If you cannot identify every SD-330AC or AMC Manager instance, then you cannot know whether exposure is contained, patched, or actively exploitable. That uncertainty is operational debt.
Inventory and segmentation come first
Before patching, many teams should ask two basic questions: where is it, and who can reach it? Microsoft recommends limiting connections between networks and devices to a small number of jump hosts, securing those hosts with MFA and privileged access management, and segmenting network access to reduce lateral movement. That is exactly the kind of structure that prevents a device flaw from turning into a network-wide incident.- Identify every deployment and software version.
- Map management interfaces and exposed ports.
- Remove direct internet exposure immediately.
- Restrict access to trusted admin paths only.
- Verify backup and rollback procedures before updating.
Implications for OT and Critical Infrastructure
Although the advisory names the Information Technology sector and says the products are deployed worldwide, the mitigation language reads like a classic OT warning because the same architectural weaknesses appear there. Device connectivity products often bridge multiple environments, and that bridge is exactly where attackers look for leverage. In critical infrastructure, a compromised management plane is never just a software problem; it can become a reliability problem, a safety problem, or both.CISA’s recommended practices stress isolating control system networks and remote devices from business networks and avoiding direct internet exposure. That is consistent with longstanding ICS guidance, but the practical importance keeps growing because devices increasingly ship with cloud-friendly admin features and remote management expectations. The more “IT-like” embedded products become, the more they inherit IT-style attack surfaces without always inheriting IT-grade security.
Why the threat model is changing
Forescout’s research has repeatedly highlighted how vulnerable routers and connected edge devices widen the attack surface for both enterprise and operational environments. That matters because the path into OT is frequently not through a PLC or controller directly, but through the plumbing around it. Connectivity gear, management software, and remote administration tools become the soft underbelly.A modern defender therefore has to treat device-management software as a first-class asset. If a vendor issue allows unauthorized configuration changes, then the product is no longer just a convenience layer; it is part of the system of record for physical or operational connectivity. That elevates the urgency of patching and segmentation.
Governance and procurement lessons
There is also a procurement story here. Organizations that buy embedded connectivity products should ask harder questions about update cadence, third-party component hygiene, cryptographic design, and support horizon. Insecure defaults and hard-coded keys are not merely implementation flaws; they are signs that security may not have been built into the product lifecycle early enough. The cheapest device can become the most expensive if it forces a network redesign later.- Require vendor disclosure on patch cadence.
- Ask for SBOM-related information where available.
- Verify authentication and crypto design during procurement.
- Treat administrative interfaces as sensitive attack surfaces.
- Plan for replacement, not just patching, for legacy gear.
The Researcher and the Disclosure Pipeline
CISA says the vulnerabilities were reported by Francesco La Spina of Forescout Technologies, which is a useful reminder that much of the modern defensive ecosystem depends on private-sector research teams willing to dig through obscure product families. Those researchers often find the issues that vendors and customers would prefer not to think about until an incident forces the conversation.This is part of a broader trend in which specialized OT and IoT security researchers keep surfacing clustered vulnerability sets in embedded ecosystems. Forescout, in particular, has spent years publishing work on device risk, protocol abuse, and firmware-level weaknesses. That body of research gives defenders context: a single advisory is not the whole story, but another data point in a longer pattern of weak assumptions in networked device design.
Why coordinated disclosure still matters
The good news is that these issues are being formally documented before widespread exploitation is publicly confirmed. The bad news is that documentation alone does not reduce exposure unless customers act on it quickly. CISA’s note that no known public exploitation has been reported is reassuring only in the narrowest sense; many of the most damaging device campaigns begin quietly, then scale after defenders have already learned the hard lesson.The practical challenge for researchers is that embedded systems are often under-instrumented. Telemetry is sparse, logs are minimal, and owners may not even know the software is present. That means vulnerability discovery often outpaces asset visibility, and defenders are left racing to understand where the issue lives before attackers do.
What makes this family interesting
The breadth of CVEs listed in the advisory suggests the research found more than one class of weakness, which usually indicates a substantial review rather than a narrow trigger. That makes the result more credible and also more alarming. It suggests the issue is not a single misread pointer or misplaced check, but a deeper set of design and implementation problems.- Disclosure is only valuable if asset owners can operationalize it.
- Research into embedded devices often exposes hidden attack surfaces.
- Clustered CVEs usually indicate systemic code quality issues.
- Public advisories help defenders prioritize scarce remediation time.
- Vendor response speed often determines whether disclosure becomes incident prevention.
Practical Defense Priorities
The first practical priority is exposure reduction. CISA says not to leave control system devices accessible from the internet, and that should be taken literally. If an SD-330AC or AMC Manager instance is reachable remotely without a tightly controlled jump host or VPN path, then the architecture itself is part of the problem, not just the software version.The second priority is authentication hardening. If any interface or function remains reachable with weak, default, or missing authentication, then the organization should treat that as an urgent exposure to be corrected or isolated. Microsoft’s guidance on OT and enterprise IoT also points to strong authentication, privileged access controls, and segmented access paths as foundational protections.
A sensible response sequence
- Identify all SD-330AC and AMC Manager installations and versions.
- Isolate exposed management interfaces from broad network access.
- Patch or upgrade to the first unaffected versions once validated.
- Audit configuration changes, credentials, and admin access paths.
- Monitor for abnormal requests, unexpected reboots, or service instability.
Detection and monitoring
Defenders should also look for signs of brute-force probing, unusual web requests, and configuration drift. If logging is sparse, network-based monitoring may be the only reliable lens. Microsoft’s Defender for IoT guidance notes that OT and IoT monitoring relies heavily on agentless visibility and behavior baselining, which is exactly why these devices need to be brought into the monitoring perimeter rather than exempted from it.- Watch for unexpected admin logins.
- Review outbound connections from device-management hosts.
- Alert on configuration changes outside maintenance windows.
- Baseline normal web and protocol traffic to the device.
- Verify backups before applying vendor fixes.
Strengths and Opportunities
There is one encouraging aspect of this disclosure cycle: the vulnerability set is now public, named, and actionable, which gives defenders a clear place to start. A second positive is that CISA’s advisory gives explicit mitigation guidance, and Microsoft’s OT guidance reinforces the same architecture-first approach, making the defensive playbook unusually coherent. If organizations use this moment to improve segmentation and inventory, they can reduce not just this risk but a whole class of future device exposures.- CISA has identified specific affected versions.
- The severity rating makes prioritization straightforward.
- Multiple mitigation pathways are already documented.
- Inventory projects can pay off across many embedded assets.
- Segmentation improves resilience beyond this single advisory.
- Better remote access design reduces exposure to future flaws.
- Security teams can use this as a catalyst for OT/IoT governance.
Risks and Concerns
The biggest concern is that device fleets like this are often hidden in plain sight, so the first failure is visibility, not patching. A second risk is that organizations may assume an internal management utility is safe simply because it is not internet-facing, even though a compromised workstation or misconfigured VLAN can still reach it. The third concern is that older or hard-to-replace deployments may linger well past the window when vendors expect customers to upgrade.- Flat networks can turn internal-only flaws into enterprise-wide issues.
- Legacy systems may be difficult to patch promptly.
- Missing authentication issues can be exploited very quickly.
- Hard-coded keys can leave lasting compromise even after a fix.
- Weak logging makes incident reconstruction difficult.
- Vendor support timelines may not match customer replacement cycles.
- Security teams may underestimate “small” embedded appliances.
Looking Ahead
The most important question now is not whether this advisory exists, but how many organizations will treat it as a device-management issue rather than a security emergency. That distinction matters because management-plane flaws tend to be normalized until they are exploited, and by then the response options are narrower. The organizations that move first will be the ones that already know where the device is, who owns it, and how it reaches the rest of the network.The second question is whether vendors and buyers will use disclosures like this to reset expectations for connectivity gear. Enterprises can no longer afford to buy devices that depend on trust, flat networks, and outdated web stacks as their security model. The market keeps moving toward more connected, more remote, and more distributed operations, which means the security bar for these products has to rise with it.
- Locate every affected device and software instance.
- Check for internet exposure and remove it.
- Validate vendor remediation steps before deployment.
- Harden remote access around privileged jump hosts.
- Add device-management software to vulnerability monitoring.
- Review procurement standards for embedded security requirements.
Source: CISA Silex Technology SD-330AC and AMC Manager | CISA