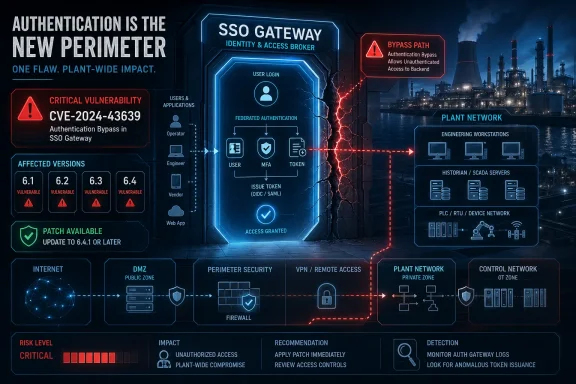
CISA republished ABB’s advisory for CVE-2025-14510 on April 30, 2026, warning that affected ABB Ability OPTIMAX installations using Azure Active Directory single sign-on can be exposed to an authentication bypass in energy and water-sector environments worldwide. The bug is not the largest industrial-control story of the year, but it is a sharp example of a quieter problem: the modern OT security perimeter increasingly runs through identity plumbing. When a plant optimization platform trusts a federated login path, a flaw in that path is not “just an IT issue.” It becomes a route into systems that tune energy, emissions, process control, and operational availability.
ABB Ability OPTIMAX sits in the increasingly crowded layer between industrial assets and business goals. It is not a consumer app with a forgotten password page; it is software used to optimize energy management, emissions, and industrial processes. That makes the vulnerability’s location more interesting than its branding.
CVE-2025-14510 affects OPTIMAX systems that use the Azure Active Directory single sign-on integration. In plain terms, the vulnerable path is not the whole product in every deployment, but the authentication bridge many organizations adopted precisely because centralized identity was supposed to reduce risk. The flaw is classified as CWE-303, an incorrect implementation of an authentication algorithm.
That distinction matters. The advisory does not describe stolen credentials, weak passwords, or careless administrators. It describes an implementation problem in the logic that decides whether a user is allowed through the door.
That last phrase should not be treated as a sedative. High attack complexity often means exploitation requires specific preconditions or careful construction, not that exploitation is unrealistic. In this case, ABB describes three important preconditions: the OPTIMAX system must be configured for Azure Active Directory integration, the attacker must have network communication with OPTIMAX, and the attacker must know a valid non-default OPTIMAX username.
Those constraints make this less like a drive-by internet worm and more like a post-intrusion or targeted-access problem. But that is exactly why OT defenders should care. Many industrial incidents do not begin with a zero-day in the control platform; they begin with access somewhere nearby, then move laterally toward systems whose trust boundaries were drawn years earlier.
That version matrix is not just housekeeping. It is the operational reality of industrial software: supported branches get update packages, older branches get conversations. In ordinary enterprise IT, “upgrade to a supported version” can be an annoying but familiar sentence. In OT, it can mean maintenance windows, vendor coordination, validation testing, rollback planning, and sometimes an argument with production leadership about why a stable system needs to be touched.
This is where vulnerability management stops being a spreadsheet exercise. The most exposed organization may not be the one with the scariest CVSS score; it may be the one running an old but mission-critical branch that nobody has budgeted time to modernize.
But SSO also concentrates trust. A local authentication bug may expose one login form; a flawed SSO integration can expose the assumptions between identity provider, application, and authorization logic. In CVE-2025-14510, the issue is specifically tied to the Azure Active Directory integration, now commonly discussed under Microsoft Entra ID branding even though many advisories and products still use the older Azure AD language.
The lesson is not that federated identity is bad. The lesson is that federated identity is software, and software has failure modes. Once an industrial platform accepts identity assertions from a cloud-connected directory service, the correctness of that handoff becomes part of the plant’s security model.
That range of outcomes is why this advisory deserves more attention than a generic login bug. OPTIMAX is designed to coordinate and optimize assets. If a malicious actor can alter configuration or execute code in that environment, the impact is not limited to confidentiality. Integrity and availability become the central concerns.
For energy and water organizations, optimization systems may not be the final safety layer, but they are still part of the operational fabric. A disruption there can trigger manual workarounds, degraded efficiency, delayed response, or loss of visibility into systems that are already complex under normal conditions.
It is not a reason to wait.
The industrial security world has learned, repeatedly, that the window between disclosure and opportunistic scanning can be short. Even when exploit code is not public, advisories provide attackers with a map of affected products, version ranges, and enabling conditions. In this case, the most important enabling condition is also easy for defenders to inventory: whether OPTIMAX is using Azure Active Directory single sign-on.
The absence of known exploitation should shape triage, not eliminate it. Organizations do not need to treat every OPTIMAX deployment as compromised. They do need to know, quickly, whether they have the vulnerable configuration.
Disabling SSO can affect user workflows, account governance, audit expectations, and emergency access procedures. If users are accustomed to centralized identity, shifting back to local authentication may require password resets, role validation, and renewed attention to account hygiene. It may also create tension with enterprise security teams that have spent years trying to eliminate local credential islands.
That does not make the workaround wrong. It means it should be treated as a controlled change, not a panic toggle. For some environments, disabling SSO until patching is complete may be the right move. For others, segmentation and rapid update deployment may be cleaner.
They should not.
CVE-2025-14510 is precisely the kind of vulnerability those controls are meant to contain. The bug is network exploitable, but it requires network communication with the affected OPTIMAX system. If that system is tightly segmented, monitored, and reachable only from expected management paths, the attack surface shrinks dramatically. If it is reachable from broad corporate networks, partner VPNs, or poorly governed remote-access paths, the vulnerability becomes more worrying.
Segmentation is sometimes sold as an old idea, less glamorous than AI-driven detection or identity analytics. In OT, it remains one of the few controls that can turn a severe software flaw into a constrained operational problem.
That distinction matters for responsibility and remediation. Patching Entra ID will not fix vulnerable OPTIMAX builds. Rotating cloud identity settings may not address the underlying issue. The fix lives in ABB’s product updates or in disabling the affected integration path.
Still, Microsoft’s presence in the architecture is important. Industrial environments are steadily absorbing enterprise identity patterns: SSO, conditional access, centralized groups, cloud-managed accounts, and hybrid directory synchronization. Each adoption can improve security, but each also creates a seam where OT software must correctly interpret IT identity signals. The seam is where this vulnerability lives.
Energy optimization, emissions management, production analytics, and asset coordination all depend on data moving between operational systems and higher-level software. These platforms need access, visibility, and integration. They also often need to serve users who are not sitting at a local engineering workstation inside the plant.
That hybrid middle is useful, profitable, and hard to secure. It inherits expectations from IT — single sign-on, remote access, dashboards, centralized user management — while touching environments where downtime and configuration drift have physical consequences. A bug in this layer may not trip a breaker by itself, but it can give an attacker leverage in a place defenders cannot ignore.
That is standard vendor language, but it exposes a strategic problem for asset owners. Industrial software often outlives the assumptions made when it was deployed. A system installed for a long-running facility may remain stable enough that nobody wants to disturb it, while its support status quietly becomes a security liability.
Unsupported does not mean unused. It means fewer easy answers when the security landscape changes. If an organization discovers that its OPTIMAX deployment is on 6.1 or 6.2 and relies on Azure AD SSO, the question is no longer just “Can we apply the patch?” It becomes “What is our modernization plan, and why did this system remain outside it?”
If OPTIMAX is not using the Azure AD integration, this specific vulnerability may not be directly exploitable as described. If it is using the integration and the version is affected, the organization has a real remediation decision. If the system is also broadly reachable from corporate networks or remote-access infrastructure, the urgency rises.
This is where mature vulnerability management earns its keep. The right answer is not “patch everything immediately” in the abstract; it is “identify the affected configuration, reduce reachable attack paths, deploy the fixed version where supported, and use a controlled workaround where patching cannot happen fast enough.”
But applying an update in an industrial environment is also a test of process. Teams should validate backups, confirm rollback steps, coordinate with operations, and document any temporary authentication changes. If SSO is disabled as a workaround, access control should not become a free-for-all of shared local accounts.
The best patching programs in OT are boring by design. They make the risky change look routine because the inventories, owners, maintenance windows, and test plans already exist. The worst programs discover all of those dependencies after the advisory lands.
They do not.
Applications must validate tokens correctly, map users correctly, enforce roles correctly, and handle authentication scripts or middleware safely. A strong identity provider cannot compensate for a vulnerable relying party that mishandles the login process. In that sense, CVE-2025-14510 is a reminder that identity security is end-to-end, not a badge applied at the directory layer.
Windows and Microsoft identity admins should therefore be part of the conversation when OT platforms integrate with Entra ID. They may not own the plant software, but they understand sign-in logs, group mappings, conditional access behavior, and the blast radius of identity misconfiguration. Leaving them out creates a gap attackers are happy to explore.
That audience should resist both overreaction and complacency. CVE-2025-14510 is not described as actively exploited, and exploitation requires conditions that may not exist in every deployment. But the potential impact includes configuration modification and arbitrary code execution, which puts it well above the category of advisory noise.
Security teams should also avoid treating the “high attack complexity” label as a reason to defer indefinitely. Complex attacks become easier when attackers have time, documentation, internal footholds, or a specific target. Critical infrastructure operators have to assume that at least some adversaries are willing to do the homework.
Source: CISA ABB Ability OPTIMAX | CISA
 The Cloud Login Became Part of the Control Room
The Cloud Login Became Part of the Control Room
ABB Ability OPTIMAX sits in the increasingly crowded layer between industrial assets and business goals. It is not a consumer app with a forgotten password page; it is software used to optimize energy management, emissions, and industrial processes. That makes the vulnerability’s location more interesting than its branding.CVE-2025-14510 affects OPTIMAX systems that use the Azure Active Directory single sign-on integration. In plain terms, the vulnerable path is not the whole product in every deployment, but the authentication bridge many organizations adopted precisely because centralized identity was supposed to reduce risk. The flaw is classified as CWE-303, an incorrect implementation of an authentication algorithm.
That distinction matters. The advisory does not describe stolen credentials, weak passwords, or careless administrators. It describes an implementation problem in the logic that decides whether a user is allowed through the door.
A High Score With a Narrower Doorway
The vulnerability carries a CVSS v3.1 base score of 8.1, rated high. ABB’s advisory also lists a CVSS v4.0 score of 9.2, which places it in critical territory under the newer scoring system. The vector is notable: network attack vector, no privileges required, no user interaction required, but high attack complexity.That last phrase should not be treated as a sedative. High attack complexity often means exploitation requires specific preconditions or careful construction, not that exploitation is unrealistic. In this case, ABB describes three important preconditions: the OPTIMAX system must be configured for Azure Active Directory integration, the attacker must have network communication with OPTIMAX, and the attacker must know a valid non-default OPTIMAX username.
Those constraints make this less like a drive-by internet worm and more like a post-intrusion or targeted-access problem. But that is exactly why OT defenders should care. Many industrial incidents do not begin with a zero-day in the control platform; they begin with access somewhere nearby, then move laterally toward systems whose trust boundaries were drawn years earlier.
The Affected Versions Tell a Lifecycle Story
The affected versions are ABB Ability OPTIMAX 6.1 and 6.2 in all versions, OPTIMAX 6.3 before 6.3.1-251120, and OPTIMAX 6.4 before 6.4.1-251120. ABB says the fixed versions are 6.3.1-251120 and 6.4.1-251120. Customers still on unsupported 6.1 or 6.2 are directed to contact ABB to determine a path forward.That version matrix is not just housekeeping. It is the operational reality of industrial software: supported branches get update packages, older branches get conversations. In ordinary enterprise IT, “upgrade to a supported version” can be an annoying but familiar sentence. In OT, it can mean maintenance windows, vendor coordination, validation testing, rollback planning, and sometimes an argument with production leadership about why a stable system needs to be touched.
This is where vulnerability management stops being a spreadsheet exercise. The most exposed organization may not be the one with the scariest CVSS score; it may be the one running an old but mission-critical branch that nobody has budgeted time to modernize.
Single Sign-On Is Not a Security Blanket
Single sign-on became popular because it solved real problems. It lets organizations centralize access control, enforce stronger authentication policies, disable users once instead of twenty times, and reduce the sprawl of local credentials. In hybrid IT and OT environments, that is attractive.But SSO also concentrates trust. A local authentication bug may expose one login form; a flawed SSO integration can expose the assumptions between identity provider, application, and authorization logic. In CVE-2025-14510, the issue is specifically tied to the Azure Active Directory integration, now commonly discussed under Microsoft Entra ID branding even though many advisories and products still use the older Azure AD language.
The lesson is not that federated identity is bad. The lesson is that federated identity is software, and software has failure modes. Once an industrial platform accepts identity assertions from a cloud-connected directory service, the correctness of that handoff becomes part of the plant’s security model.
Authentication Bypass Is Worse in Optimization Software Than It Sounds
“Authentication bypass” can sound sterile, as if the attacker merely skips a login screen. ABB’s advisory is more concrete. Successful exploitation could allow an attacker to bypass user authentication and potentially shut down the system, modify system configuration, or install and run arbitrary code.That range of outcomes is why this advisory deserves more attention than a generic login bug. OPTIMAX is designed to coordinate and optimize assets. If a malicious actor can alter configuration or execute code in that environment, the impact is not limited to confidentiality. Integrity and availability become the central concerns.
For energy and water organizations, optimization systems may not be the final safety layer, but they are still part of the operational fabric. A disruption there can trigger manual workarounds, degraded efficiency, delayed response, or loss of visibility into systems that are already complex under normal conditions.
The “No Known Exploitation” Clause Is Reassuring, Not Exculpatory
CISA states that no known public exploitation specifically targeting this vulnerability has been reported to the agency at this time. ABB similarly says it had not received reports of exploitation when the advisory was issued. That is good news.It is not a reason to wait.
The industrial security world has learned, repeatedly, that the window between disclosure and opportunistic scanning can be short. Even when exploit code is not public, advisories provide attackers with a map of affected products, version ranges, and enabling conditions. In this case, the most important enabling condition is also easy for defenders to inventory: whether OPTIMAX is using Azure Active Directory single sign-on.
The absence of known exploitation should shape triage, not eliminate it. Organizations do not need to treat every OPTIMAX deployment as compromised. They do need to know, quickly, whether they have the vulnerable configuration.
The Workaround Is Simple Only on Paper
ABB’s recommended workaround is to deactivate the Azure Active Directory integration and fall back to OPTIMAX’s standard user authentication mechanism. From a pure vulnerability perspective, that removes the exposed integration path. From an operations perspective, it may create a new set of problems.Disabling SSO can affect user workflows, account governance, audit expectations, and emergency access procedures. If users are accustomed to centralized identity, shifting back to local authentication may require password resets, role validation, and renewed attention to account hygiene. It may also create tension with enterprise security teams that have spent years trying to eliminate local credential islands.
That does not make the workaround wrong. It means it should be treated as a controlled change, not a panic toggle. For some environments, disabling SSO until patching is complete may be the right move. For others, segmentation and rapid update deployment may be cleaner.
CISA’s Generic ICS Advice Still Applies Because the Pattern Has Not Changed
CISA’s recommendations are familiar: minimize network exposure, keep control systems off the public internet, isolate control networks from business networks, place remote access behind secure methods such as VPNs, and perform impact analysis before deploying defensive measures. These phrases appear so often in ICS advisories that they can blur into wallpaper.They should not.
CVE-2025-14510 is precisely the kind of vulnerability those controls are meant to contain. The bug is network exploitable, but it requires network communication with the affected OPTIMAX system. If that system is tightly segmented, monitored, and reachable only from expected management paths, the attack surface shrinks dramatically. If it is reachable from broad corporate networks, partner VPNs, or poorly governed remote-access paths, the vulnerability becomes more worrying.
Segmentation is sometimes sold as an old idea, less glamorous than AI-driven detection or identity analytics. In OT, it remains one of the few controls that can turn a severe software flaw into a constrained operational problem.
Microsoft Is in the Story, But This Is Not a Microsoft Vulnerability
Because the affected integration involves Azure Active Directory, it is tempting to frame this as another Microsoft identity problem. That would be too simple. The vulnerability is in ABB Ability OPTIMAX’s implementation of single sign-on integration, not a disclosed flaw in Microsoft’s identity platform.That distinction matters for responsibility and remediation. Patching Entra ID will not fix vulnerable OPTIMAX builds. Rotating cloud identity settings may not address the underlying issue. The fix lives in ABB’s product updates or in disabling the affected integration path.
Still, Microsoft’s presence in the architecture is important. Industrial environments are steadily absorbing enterprise identity patterns: SSO, conditional access, centralized groups, cloud-managed accounts, and hybrid directory synchronization. Each adoption can improve security, but each also creates a seam where OT software must correctly interpret IT identity signals. The seam is where this vulnerability lives.
The Real Risk Is the Hybrid Middle
The old mental model divided the world into IT and OT. Business systems lived on one side; control systems lived on the other. That model has been eroding for years, and OPTIMAX sits in the middle of the erosion.Energy optimization, emissions management, production analytics, and asset coordination all depend on data moving between operational systems and higher-level software. These platforms need access, visibility, and integration. They also often need to serve users who are not sitting at a local engineering workstation inside the plant.
That hybrid middle is useful, profitable, and hard to secure. It inherits expectations from IT — single sign-on, remote access, dashboards, centralized user management — while touching environments where downtime and configuration drift have physical consequences. A bug in this layer may not trip a breaker by itself, but it can give an attacker leverage in a place defenders cannot ignore.
Unsupported Branches Are Where Strategy Becomes Debt
ABB’s handling of versions 6.1 and 6.2 deserves special attention. The advisory says those branches are affected, but the fixed versions named are in the 6.3 and 6.4 lines. Customers still using the unsupported older versions are told to contact ABB.That is standard vendor language, but it exposes a strategic problem for asset owners. Industrial software often outlives the assumptions made when it was deployed. A system installed for a long-running facility may remain stable enough that nobody wants to disturb it, while its support status quietly becomes a security liability.
Unsupported does not mean unused. It means fewer easy answers when the security landscape changes. If an organization discovers that its OPTIMAX deployment is on 6.1 or 6.2 and relies on Azure AD SSO, the question is no longer just “Can we apply the patch?” It becomes “What is our modernization plan, and why did this system remain outside it?”
A Vulnerability Inventory Beats a Panic Patch
The first practical response is not dramatic. Asset owners should determine whether ABB Ability OPTIMAX is deployed, which version is running, and whether Azure Active Directory SSO is enabled. That is the fork in the road.If OPTIMAX is not using the Azure AD integration, this specific vulnerability may not be directly exploitable as described. If it is using the integration and the version is affected, the organization has a real remediation decision. If the system is also broadly reachable from corporate networks or remote-access infrastructure, the urgency rises.
This is where mature vulnerability management earns its keep. The right answer is not “patch everything immediately” in the abstract; it is “identify the affected configuration, reduce reachable attack paths, deploy the fixed version where supported, and use a controlled workaround where patching cannot happen fast enough.”
The Patch Is Also a Test of Change Control
ABB says the issue is corrected in OPTIMAX v6.4.1-251120 and v6.3.1-251120 or later. The update prevents injection vectors in the authentication script used for Azure Active Directory integration. That is a clear remediation story for organizations on supported versions.But applying an update in an industrial environment is also a test of process. Teams should validate backups, confirm rollback steps, coordinate with operations, and document any temporary authentication changes. If SSO is disabled as a workaround, access control should not become a free-for-all of shared local accounts.
The best patching programs in OT are boring by design. They make the risky change look routine because the inventories, owners, maintenance windows, and test plans already exist. The worst programs discover all of those dependencies after the advisory lands.
Windows Admins Should Read This as an Identity Warning
For WindowsForum readers, the most interesting angle may be the identity connection. Many admins have spent the last decade moving users toward SSO, MFA, conditional access, and cloud directory governance. That work is still sound. But it has encouraged a sometimes dangerous assumption that once identity is centralized, downstream applications become automatically safer.They do not.
Applications must validate tokens correctly, map users correctly, enforce roles correctly, and handle authentication scripts or middleware safely. A strong identity provider cannot compensate for a vulnerable relying party that mishandles the login process. In that sense, CVE-2025-14510 is a reminder that identity security is end-to-end, not a badge applied at the directory layer.
Windows and Microsoft identity admins should therefore be part of the conversation when OT platforms integrate with Entra ID. They may not own the plant software, but they understand sign-in logs, group mappings, conditional access behavior, and the blast radius of identity misconfiguration. Leaving them out creates a gap attackers are happy to explore.
The Advisory’s Most Important Sentences Are Operational
The concrete facts are straightforward: affected versions, fixed builds, CVSS scores, no known exploitation, and a workaround. The operational implications are messier. This is not a vulnerability that every household user or small business needs to understand. It is a vulnerability for organizations where energy management software intersects with industrial uptime and centralized identity.That audience should resist both overreaction and complacency. CVE-2025-14510 is not described as actively exploited, and exploitation requires conditions that may not exist in every deployment. But the potential impact includes configuration modification and arbitrary code execution, which puts it well above the category of advisory noise.
Security teams should also avoid treating the “high attack complexity” label as a reason to defer indefinitely. Complex attacks become easier when attackers have time, documentation, internal footholds, or a specific target. Critical infrastructure operators have to assume that at least some adversaries are willing to do the homework.
The OPTIMAX Lesson Fits on One Maintenance Window
The practical message for ABB customers is narrow enough to act on, but broad enough to matter beyond this product. This is a vulnerability about trust between an industrial platform and an enterprise identity system, and the fix is as much about architecture as it is about versions.- Organizations should identify whether ABB Ability OPTIMAX is deployed and whether Azure Active Directory single sign-on is enabled.
- Installations running OPTIMAX 6.3 before 6.3.1-251120 or 6.4 before 6.4.1-251120 should be prioritized for the fixed ABB updates.
- Installations still running OPTIMAX 6.1 or 6.2 need vendor engagement because those branches are affected and no simple in-branch fixed version is listed.
- If patching cannot be completed quickly, disabling the Azure Active Directory integration and reverting to standard OPTIMAX authentication can reduce exposure, but it should be managed as a controlled operational change.
- Network segmentation, restricted remote access, and firewall enforcement are not generic boilerplate here; they directly affect whether an attacker can reach the vulnerable service path.
- The absence of known exploitation lowers the temperature, but it does not remove the need for inventory, remediation, and monitoring.
Source: CISA ABB Ability OPTIMAX | CISA