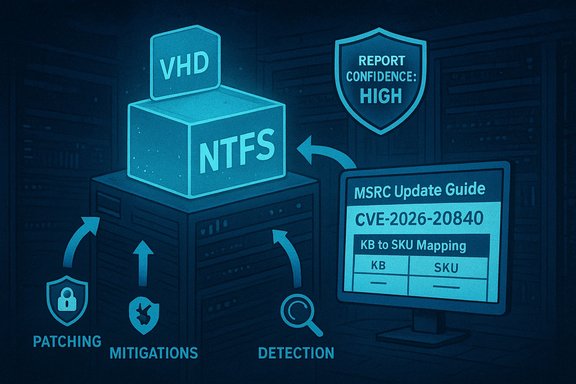
Microsoft’s advisory record for CVE-2026-20840 lists a remote code-execution issue affecting the Windows NTFS stack and attaches Microsoft’s standard “report confidence” metadata to the entry — a signal designed to tell defenders how certain Microsoft is about the problem and how much technical detail is being published. At the time this analysis was prepared, vendor guidance exists in the Microsoft Security Response Center’s Update Guide entry for CVE-2026-20840, but public technical detail and independent corroboration are limited; the MSRC entry is the primary vendor statement and should be treated as the authoritative starting point for triage. This feature explains what the MSRC “report confidence” metric means in practical terms, places CVE-2026-20840 against the recent history of NTFS kernel bugs, evaluates plausible exploitation models, and gives a prioritized operational playbook — patching, mitigations, detection, and hardening — for Windows administrators and security teams. Where independent corroboration exists for technical patterns or historic exploit behavior, those claims are cross-checked with industry trackers and vendor write-ups; where claims about this specific CVE cannot be independently validated, those points are flagged and treated conservatively.
The broad pattern is familiar: an attacker supplies a malicious disk image, mounted VHD, or crafted on-disk metadata that the kernel or privileged services parse in the context of a highly privileged process. Past NTFS advisories (and Microsoft Patch cycles) have included multiple NTFS-related fixes where adversaries exploited VHD mounting or other image-handling flows to trigger heap overflows and information disclosure. Independent vendor write-ups and vulnerability trackers documented this class of exploitation and the patching cadence.
Immediate priorities are simple and pragmatic: consult Microsoft’s Update Guide entry in a browser to capture the KB→SKU mapping, prioritize patching for virtualization hosts and image-processing servers, restrict mounting of untrusted images, and deploy hunting telemetry aimed at kernel oops, unexpected mounts, and suspicious process ancestry. Where MSRC lists the entry as confirmed, patch immediately; where it is corroborated or suspected, escalate priority proportionate to exposure and fallback to conservative mitigations described above. Note on verification: the MSRC Update Guide page is the authoritative vendor statement for CVE-2026-20840; however, at the time of publication independent, widely distributed technical reports referencing the CVE are limited. The historical behaviors and mitigation patterns in this article draw from recent NTFS advisories and vendor analyses; those patterns are validated by independent trackers and incident-response write-ups and are cited where used. Defenders should monitor Microsoft’s Update Guide for any updates to the confidence level, KB mappings, and published mitigations, and should incorporate those changes into an accelerated patch-and-hunt cycle where exposure is highest.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Why NTFS bugs matter now
NTFS is a privileged, kernel-facing component used by virtually all Windows clients and servers. Flaws in filesystem parsing code have repeatedly produced high-impact vulnerabilities — from information disclosure and denial-of-service to heap-based buffer overflows that local attackers (or users tricked into mounting crafted images) can turn into privilege escalation or remote code execution.The broad pattern is familiar: an attacker supplies a malicious disk image, mounted VHD, or crafted on-disk metadata that the kernel or privileged services parse in the context of a highly privileged process. Past NTFS advisories (and Microsoft Patch cycles) have included multiple NTFS-related fixes where adversaries exploited VHD mounting or other image-handling flows to trigger heap overflows and information disclosure. Independent vendor write-ups and vulnerability trackers documented this class of exploitation and the patching cadence.
The vendor “report confidence” signal
Microsoft’s Update Guide records not only the vulnerability identifier and affected products but also a short metadata field that describes the vendor’s degree of confidence in the advisory and how much technical detail is being published publicly. In practice this metric falls into three operational categories:- Suspected / Low confidence: the vendor is aware of an issue or report but has limited corroborating detail. Public write-ups may be minimal or intentionally vague.
- Corroborated / Medium confidence: third‑party research or telemetry supports the vendor’s claim; technical indicators may be available but some details remain unconfirmed.
- Confirmed / High confidence: vendor testing, patch releases, or explicit vendor statements validate the vulnerability and typically provide KB mappings and remediation guidance.
What the MSRC entry says (and what it does not)
Microsoft’s Update Guide entry for CVE-2026-20840 exists as the canonical vendor assertion that the vulnerability is recorded and mapped to security updates. The vendor page typically contains short, deliberate language about the vulnerability class and remediation KBs, while intentionally withholding exploit-level specifics at publication time to reduce short-term weaponization. The MSRC entry is therefore the authoritative source for:- which Windows builds and SKUs are affected,
- the KB security updates that remediate the issue,
- vendor-assigned impact class, and
- Microsoft’s public assessment of confidence / technical detail.
Technical analysis: plausible root causes and exploitation models
Because Microsoft has historically grouped NTFS advisories with similar root causes and exploitation patterns, a practical technical analysis for CVE-2026-20840 should consider the following proven exploitation models observed in prior NTFS advisories:- Heap-based buffer overflow when parsing on-disk structures or mounted images. Attackers craft a VHD or raw NTFS image whose metadata causes the NTFS parser or device driver to write past allocated heap buffers. That corruption can be turned into arbitrary code execution under the context of the parsing process if additional primitives (heap grooming, pointer overwrite, token manipulation) are present. Past NTFS RCEs exploited precisely this attack surface.
- Out-of-bounds reads that leak kernel memory. Out-of-bounds or uninitialized reads can expose kernel layout or secrets (KASLR offsets, tokens), which in turn make memory-corruption primitives significantly more reliable for attackers. Several NTFS advisories in the recent patch cycles involved information disclosure from mounted VHDs, and those leaks have been used as exploit accelerants.
- Uninitialized or zeroing-allocation mistakes in call chains. In related filesystem work (notably in Linux’s ntfs3 driver), security patches replaced non-zeroing slab allocations with zeroing versions to eliminate indeterminate memory reads that led to incorrect control flow and potential data leaks; the same class of bug can manifest in other NTFS implementations or processing code paths. This pattern shows how subtle memory-initialization errors can produce logical faults that escalate to security issues.
- Local or image-supply attack surface. The practical attack vector often requires local action — a user mounting a crafted VHD or the system automatically mounting an image supplied via removable media or imported guest disk. In cloud or virtualization environments, however, the attack surface widens: automated image ingestion, CI/CD pipelines, backup appliances, or host-side inspection of guest disks can cause privileged services to parse untrusted NTFS images, making “local-only” bugs far more dangerous at scale.
- whether a public proof-of-concept (PoC) exists,
- whether Microsoft observed in-the-wild exploitation (telemetry evidence),
- the precise memory-corruption primitive (heap overflow vs. integer overflow vs. improper validation), and
- the full list of affected SKUs and KB numbers until the MSRC page is rendered or KB mappings are confirmed.
Threat model and exploitability assessment
To make operational decisions, defenders should consider three axes: attack vector, preconditions, and required interaction.- Attack vector: Based on NTFS precedent, the most likely vectors are local (user mounts VHD, opens attached removable media) or image-supply (malicious disk images ingested by privileged services). For hosts that automatically inspect or mount images, the realistic attack surface becomes effectively network-exposed through supply-chain or guest-image mechanisms.
- Preconditions: Many NTFS RCEs required the ability to mount or loopback an image, or to get a user to interact with a UI that triggers kernel parsing (File Explorer preview, mounting a VHD). Adversaries commonly combine social engineering with malicious images distributed via phishing or compromised downloads. In virtualization/cloud contexts, supplying a crafted guest disk to a host that mounts or scans images can remove the need for interactive users altogether.
- Magnitude and blast radius: Single-desktop exploitation is damaging, but enterprise-scale risk spikes where the vulnerable parsing code runs in services that process many third-party images (CI runners, virtualization hosts, backup appliances). There, a single crafted image can disrupt or compromise multi-tenant infrastructure. Security advisories repeatedly emphasize prioritizing patching in such environments.
- High for virtualization hosts, image ingestion pipelines, and file-processing servers.
- Medium for shared workstations and admin hosts that routinely mount external images.
- Lower (but non-zero) for single‑user desktops that rarely mount untrusted media.
Operational guidance — immediate steps
Until the MSRC KB mapping and full technical details are confirmed, adopt a conservative, prioritized remediation and mitigation approach.1. Confirm vendor mapping and prioritize by exposure (first hour)
- Open Microsoft’s Update Guide entry for CVE-2026-20840 in a browser and extract the KB→SKU mappings. Treat the MSRC page as the canonical source for which updates to apply.
- Inventory systems that automatically mount or inspect NTFS images: virtualization hosts, backup appliances, forensic/image-processing servers, CI/CD runners, and any host that handles third‑party VHDs or disk images. These systems must be prioritized for patching.
2. Patch quickly, with staging (first 24–72 hours)
- Apply the Microsoft security updates that MSRC maps to CVE-2026-20840. Use your usual patch orchestration (WSUS, SCCM/ConfigMgr, Intune, or the Microsoft Update Catalog) and confirm the exact KB for each build before declaring remediation complete. Reboot as recommended.
- If hotpatch or minimal-reboot options are available for critical hosts, evaluate them to reduce downtime while maintaining safety.
3. Short-term compensations (if patching is delayed)
- Restrict mounting privileges so only administrators or a tightly controlled service account can mount disk images or loopback devices. On Windows, review and limit local group memberships and mount capabilities.
- For virtualization hosts or image-ingestion systems, do not mount untrusted guest images directly on the host. Use isolated sandboxes, dedicated analysis VMs, or out-of-band image inspection workflows.
- Block or inspect file types commonly used as attack vectors (VHD, VHDX, and raw disk images) on email gateways and file-upload services; consider dropping automatic thumbnailing/preview pipelines for untrusted uploads temporarily.
4. Detection and hunting (concurrent)
- Monitor kernel logs for filesystem-related oops/panic messages referencing NTFS or related drivers; these often surface exploitation attempts or triggering crashes. Configure telemetry to forward kernel oops and blue-screen signatures to central logging.
- Hunt for anomalous image-mount activity originating from non-privileged accounts or from automation services that do not normally mount images. Correlate with process creation events and unexpected SYSTEM-level process spawns.
- For endpoint telemetry, look for unexpected process ancestry where user-level processes spawn privileged actions (PowerShell or cmd under SYSTEM contexts) shortly after a mounted image event.
Why the “report confidence” metric changes how you triage
Microsoft’s confidence label matters because it signals how trustworthy and complete the vendor’s public statement is:- If Microsoft classifies the entry as confirmed, it usually means the vendor has validated the root cause and shipped fixes — treat it as high urgency and patch immediately.
- If the vendor marks the entry as corroborated (for example, independent researchers have published details), the advisory often contains enough public technical detail to enable rapid weaponization; patch and hunt rapidly.
- If the advisory remains suspected or the technical details are intentionally limited, the immediate priority depends on impact classification (RCE is high) and environmental exposure; conservative assumptions (treat as weaponizable) are prudent until more detail appears.
Strengths, uncertainties, and risks
Notable strengths in the current posture
- Microsoft’s Update Guide provides a single canonical location to map CVEs to KBs and affected Windows builds; relying on that mapping reduces confusion and helps enforce correct patching. Administrators should always confirm KB numbers per SKU before deployment.
- The security community’s recent NTFS advisories and vendor write-ups provide clear operational patterns (VHD mounting, image ingestion exposure) that let defenders prioritize high-risk hosts without waiting for exploit code.
Key uncertainties for CVE-2026-20840
- Public corroboration beyond the MSRC entry is limited at time of writing. There is no widely published PoC or multiple independent technical analyses referencing this CVE in major trackers (as of this article’s preparation). That absence increases the importance of following Microsoft’s guidance and treating the MSRC entry as authoritative.
- Without explicit exploit telemetry, it is unknown whether attackers have weaponized the issue or if targeted campaigns are underway. This uncertainty argues for conservative triage when the impact classification is remote code execution.
Risks to operations if action is delayed
- A single exploited NTFS RCE on a virtualization host or image ingestion pipeline can yield a high blast radius, enabling lateral movement into tenant workloads or persistent compromise of infrastructure.
- Delays in mapping MSRC KBs to your inventory increase the chance of missing vulnerable hosts, especially in mixed fleets or bespoke images where components may be present unexpectedly. Use host-level verification to confirm presence of vulnerable components if vendor mapping is unclear.
Longer-term defenses and lessons learned
- Harden image ingestion and virtualization workflows: treat any third-party disk image as untrusted by default; process images in disposable sandboxes and avoid host-side mounting for analysis.
- Reduce attack surface via least privilege: limit which accounts and services can mount or loopback images, and restrict direct access to host-level mount operations.
- Apply defense-in-depth for kernel exposures: enforce application allow-listing for administrative tools, deploy endpoint detection capable of spotting token manipulation and kernel exploit signatures, and maintain strong segmentation between development/test systems and production virtualization hosts.
- Track vendor confidence metadata as an input to triage SLA: confirmed RCEs should trigger immediate patch windows; corroborated disclosures should trigger dual-track response (patch + active hunting); suspected entries should be monitored and mapped to exposure.
Conclusion
CVE-2026-20840 is recorded in Microsoft’s Update Guide as an NTFS-area remote code-execution entry and carries the vendor’s “report confidence” metadata that is crucial for triage. Because NTFS parsing vulnerabilities have a well-established history of being weaponized — particularly where malicious images are mounted or processed by privileged services — defenders must treat the advisory seriously even when public exploit detail is limited.Immediate priorities are simple and pragmatic: consult Microsoft’s Update Guide entry in a browser to capture the KB→SKU mapping, prioritize patching for virtualization hosts and image-processing servers, restrict mounting of untrusted images, and deploy hunting telemetry aimed at kernel oops, unexpected mounts, and suspicious process ancestry. Where MSRC lists the entry as confirmed, patch immediately; where it is corroborated or suspected, escalate priority proportionate to exposure and fallback to conservative mitigations described above. Note on verification: the MSRC Update Guide page is the authoritative vendor statement for CVE-2026-20840; however, at the time of publication independent, widely distributed technical reports referencing the CVE are limited. The historical behaviors and mitigation patterns in this article draw from recent NTFS advisories and vendor analyses; those patterns are validated by independent trackers and incident-response write-ups and are cited where used. Defenders should monitor Microsoft’s Update Guide for any updates to the confidence level, KB mappings, and published mitigations, and should incorporate those changes into an accelerated patch-and-hunt cycle where exposure is highest.
Source: MSRC Security Update Guide - Microsoft Security Response Center