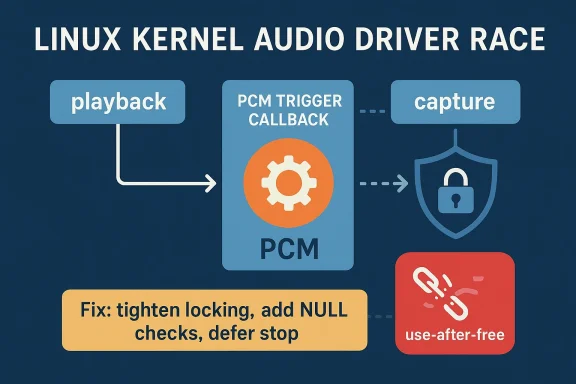
The page for CVE-2026-23191 is currently unavailable on Microsoft’s update guide, but the underlying Linux kernel issue is identifiable: ALSA: aloop: Fix racy access at PCM trigger. The upstream stable patch says the PCM trigger callback in the aloop driver was checking PCM state and stopping the tied substream outside the cable lock, creating a race that could lead to a use-after-free when a program triggered streams frequently while opening and closing the paired path. The fix tightens locking in
The snd-aloop driver is ALSA’s software loopback card: it presents a pair of virtual PCM devices that can be wired together for capture, playback, testing, and routing workflows. That makes it a useful but specialized component, and in practice it tends to show up in audio testing, virtualized desktop stacks, automation harnesses, and any setup that needs to route sound entirely in software. The driver’s convenience is also what makes concurrency mistakes matter so much; when both ends of a virtual cable are being manipulated quickly, the code has to keep state transitions perfectly ordered.
The patch trail for CVE-2026-23191 points to a classic kernel pattern: a small synchronization gap that is harmless in slow-path use, but dangerous under stress or fuzzing. Greg Kroah-Hartman’s stable posting explains that the trigger path checked the PCM state and attempted to stop the tied substream without holding the cable lock for the whole sequence, which could produce a UAF if the stream was opened or closed at the same time. That is exactly the kind of bug that modern fuzzers are good at finding, even when it is hard for humans to reproduce manually. (spinics.net)
The broader significance is that Linux audio bugs are not merely “sound problems.” In kernel space, a race in one driver can become a system stability issue, a denial-of-service vector, or a possible security issue depending on the exact memory lifetime behavior. The stable patch description explicitly states that the vulnerable path could be triggered by frequent stream operations, which makes it more than a theoretical edge case for environments that automate audio device creation and teardown. (spinics.net)
This also fits a wider pattern in 2026 kernel security work: many high-interest fixes are not flashy buffer overflows, but precise lifetime and locking corrections. That is important because it changes how operators should think about risk. If a driver is exposed through ordinary device access, then even “boring” races can be operationally significant when untrusted local code, containers, or CI jobs can exercise the device stack repeatedly. (spinics.net)
The fix also changes the logic around the capture side. Instead of stopping the capture stream while still inside the hot critical section, the patch records whether the capture stream should be stopped and performs
In practical terms, this is the kind of engineering that kernel maintainers rely on to turn a flaky concurrency bug into a deterministic flow. The code now explicitly checks whether both playback and capture substreams exist, whether their runtimes are live, and whether the capture side is still running before attempting to stop it. That is much safer than assuming the underlying objects will stay stable across multiple calls. (spinics.net)
The code also adds more robust early returns. If the cable is not valid or the expected playback/capture objects are missing, the function now bails out instead of continuing down a path that could dereference stale memory. These checks are not glamorous, but in kernel code they are often the difference between a recoverable fault and a crashing machine. (spinics.net)
The final result is a safer trigger path that preserves the driver’s intended behavior while narrowing the race window. This matters because the old code likely behaved correctly most of the time; the bug was in the timing, not in the high-level design. Those are the hardest bugs to catch in testing, and the easiest to dismiss until fuzzing or production load makes them visible. (spinics.net)
It is also a reminder that CVE tracking across ecosystems is messy. One vendor may assign or reference a CVE before another has fully published the advisory page, and third-party databases may briefly outrun the primary vendor portal. That is normal, especially in the kernel world where stable fixes move quickly and advisories catch up afterward. (spinics.net)
For enterprise admins, this means the safest workflow is to validate against upstream patch notes and distribution advisories, then confirm package versions once the downstream vendor publishes guidance. Waiting on a single portal can leave a patch window open longer than necessary. In the security operations world, slow confirmation is still delay. (spinics.net)
In enterprises, the picture changes. Build farms, automated QA labs, virtual desktop infrastructure, and media processing systems often use loopback audio to synthesize input, capture output, or test routing behavior. On those systems, a race that requires rapid stream open/close cycles is not exotic at all; it can happen naturally under automation.
The most relevant risk category is therefore not “everyone with Linux audio” but “systems that use kernel loopback audio as infrastructure.” That distinction matters for prioritization. Security teams should not treat the issue as a universal emergency, but neither should they ignore it simply because the module sounds specialized.
The more subtle danger is false confidence. A system can appear stable during light testing and still be exposed under stress, especially if loopback devices are only exercised during special workflows. That makes this the kind of issue that can sit quietly in release engineering pipelines until a high-frequency workload or fuzzer stumbles into it. (spinics.net)
For teams running Linux audio in containers or ephemeral CI images, the takeaway is simple: if your automation mounts or loads
It also shows why the kernel’s stable process matters so much. A bug found in upstream development is one thing; a bug that gets quickly packaged for stable branches is another. The faster that synchronization fix travels downstream, the less time there is for distributions and OEM builds to carry the vulnerable code. (spinics.net)
The patch’s careful structure is also a reminder that memory safety issues do not always come from obvious allocator misuse. Sometimes they come from correct-looking code that makes an assumption about object lifetime across a handful of lines. That kind of bug is hard to spot in review, which is why fuzzing and stress testing remain indispensable. (spinics.net)
For vendors building appliances or appliances-like Linux systems, the lesson is similar. If your product exposes kernel audio modules as part of a larger media, conferencing, or virtualization stack, then an ALSA bug can become a product stability issue even if the driver is not front-and-center in marketing materials. The dependency chain matters more than the feature label.
For competitors and adjacent technologies, this kind of fix is a reminder that alternative audio stacks are only as safe as the kernel plumbing they depend on. PipeWire, JACK, PulseAudio, and virtualization layers may not be the buggy component, but they still benefit from a better-behaved kernel loopback path. In other words, a tiny ALSA fix can improve confidence across the whole Linux audio ecosystem.
The larger story is more interesting. Linux kernel security in 2026 continues to be shaped by concurrency correctness, not just classic memory corruption primitives. That means teams should expect more CVEs that look tiny in diff size but large in operational consequences, especially in drivers and subsystems that most admins rarely think about. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center
loopback_check_format(), adds NULL checks, and defers stopping the capture stream until after the critical section. (spinics.net)
 Background
Background
The snd-aloop driver is ALSA’s software loopback card: it presents a pair of virtual PCM devices that can be wired together for capture, playback, testing, and routing workflows. That makes it a useful but specialized component, and in practice it tends to show up in audio testing, virtualized desktop stacks, automation harnesses, and any setup that needs to route sound entirely in software. The driver’s convenience is also what makes concurrency mistakes matter so much; when both ends of a virtual cable are being manipulated quickly, the code has to keep state transitions perfectly ordered.The patch trail for CVE-2026-23191 points to a classic kernel pattern: a small synchronization gap that is harmless in slow-path use, but dangerous under stress or fuzzing. Greg Kroah-Hartman’s stable posting explains that the trigger path checked the PCM state and attempted to stop the tied substream without holding the cable lock for the whole sequence, which could produce a UAF if the stream was opened or closed at the same time. That is exactly the kind of bug that modern fuzzers are good at finding, even when it is hard for humans to reproduce manually. (spinics.net)
The broader significance is that Linux audio bugs are not merely “sound problems.” In kernel space, a race in one driver can become a system stability issue, a denial-of-service vector, or a possible security issue depending on the exact memory lifetime behavior. The stable patch description explicitly states that the vulnerable path could be triggered by frequent stream operations, which makes it more than a theoretical edge case for environments that automate audio device creation and teardown. (spinics.net)
This also fits a wider pattern in 2026 kernel security work: many high-interest fixes are not flashy buffer overflows, but precise lifetime and locking corrections. That is important because it changes how operators should think about risk. If a driver is exposed through ordinary device access, then even “boring” races can be operationally significant when untrusted local code, containers, or CI jobs can exercise the device stack repeatedly. (spinics.net)
What the Vulnerability Actually Was
The stable patch is unusually direct about the failure mode. The ALSA aloop trigger callback tried to examine one stream and stop the paired stream in the corresponding cable, but those checks and actions were not fully serialized. The result was a window where the code could act on stream state that was already changing underneath it, which is why the fix adds stronger locking around most ofloopback_check_format() and checks for valid substream pointers before proceeding. (spinics.net)Why the race mattered
The important point is not just that a race existed, but that the race could affect a pointer lifetime. The patch note says the issue could result in a UAF when a program repeatedly triggered streams while opening and closing the tied stream. That means the bug was not limited to incorrect audio behavior; it crossed into memory-safety territory, which is why it was treated as a security issue rather than a mere bugfix. (spinics.net)The fix also changes the logic around the capture side. Instead of stopping the capture stream while still inside the hot critical section, the patch records whether the capture stream should be stopped and performs
snd_pcm_stop() afterward. That is a subtle but important redesign: it shortens the time spent under lock while making sure the potentially dangerous state transition happens only after the state has been revalidated. (spinics.net)In practical terms, this is the kind of engineering that kernel maintainers rely on to turn a flaky concurrency bug into a deterministic flow. The code now explicitly checks whether both playback and capture substreams exist, whether their runtimes are live, and whether the capture side is still running before attempting to stop it. That is much safer than assuming the underlying objects will stay stable across multiple calls. (spinics.net)
How the Fix Works
The patch is not a wholesale rewrite. It is a carefully scoped synchronization repair with three main moves: broaden locking in the format-check path, add defensive NULL checks, and separate the “decide” and “act” phases for stopping the tied stream. That kind of surgical change is typical for stable kernels, where maintainers prefer minimal risk fixes that can be backported across supported branches. (spinics.net)Locking the critical section
The first important change is the use ofscoped_guard(spinlock_irqsave, &cable->lock). This effectively ensures the function inspects the relevant substream pointers and runtime fields while the cable state is protected. The patch also tightens access to get_setup() and the card state, which reduces the chance that one thread sees partially updated data while another thread is closing a stream. (spinics.net)The code also adds more robust early returns. If the cable is not valid or the expected playback/capture objects are missing, the function now bails out instead of continuing down a path that could dereference stale memory. These checks are not glamorous, but in kernel code they are often the difference between a recoverable fault and a crashing machine. (spinics.net)
Deferring the stop operation
The second key fix is behavioral: the patch introduces astop_capture flag and postpones the actual stop call. That is a common concurrency tactic because it reduces the amount of work done while a lock is held, and it avoids doing heavy operations in a window where other code may also be touching the same objects. In effect, the code now says, decide under lock, execute outside it. (spinics.net)The final result is a safer trigger path that preserves the driver’s intended behavior while narrowing the race window. This matters because the old code likely behaved correctly most of the time; the bug was in the timing, not in the high-level design. Those are the hardest bugs to catch in testing, and the easiest to dismiss until fuzzing or production load makes them visible. (spinics.net)
Why Microsoft’s Missing Page Matters
Microsoft’s update guide page returning not found is frustrating, but it does not mean the vulnerability is imaginary. In cases like this, the CVE identifier can still map to a Linux kernel patch even when the MSRC landing page is temporarily unavailable or not yet populated. The upstream stable patch gives us the authoritative technical content needed to understand what was fixed. (spinics.net)Reading the signal, not the missing page
For defenders, the absence of a Microsoft page means you should be careful not to over-interpret product naming or severity labels until the entry is published. But the kernel patch itself is already enough to confirm that the issue sits in the ALSA loopback driver and involves a race at PCM trigger time. That is the part that drives patching decisions, not the web page’s availability status. (spinics.net)It is also a reminder that CVE tracking across ecosystems is messy. One vendor may assign or reference a CVE before another has fully published the advisory page, and third-party databases may briefly outrun the primary vendor portal. That is normal, especially in the kernel world where stable fixes move quickly and advisories catch up afterward. (spinics.net)
For enterprise admins, this means the safest workflow is to validate against upstream patch notes and distribution advisories, then confirm package versions once the downstream vendor publishes guidance. Waiting on a single portal can leave a patch window open longer than necessary. In the security operations world, slow confirmation is still delay. (spinics.net)
Who Is Affected
The direct exposure is limited to systems that actually load and use the snd-aloop kernel module. That is good news for the average desktop user, because many machines will never touch the loopback driver at all. But in environments that do use it, the impact can be much broader than the apparent niche would suggest.Enterprise vs. consumer exposure
On consumer systems, the main risk is relatively low unless an application or audio stack explicitly loads the loopback driver. Most people are unlikely to encounter it in everyday playback or conferencing. Still, systems running custom audio setups, virtualization tools, or niche recording software may be more exposed than a generic home PC.In enterprises, the picture changes. Build farms, automated QA labs, virtual desktop infrastructure, and media processing systems often use loopback audio to synthesize input, capture output, or test routing behavior. On those systems, a race that requires rapid stream open/close cycles is not exotic at all; it can happen naturally under automation.
The most relevant risk category is therefore not “everyone with Linux audio” but “systems that use kernel loopback audio as infrastructure.” That distinction matters for prioritization. Security teams should not treat the issue as a universal emergency, but neither should they ignore it simply because the module sounds specialized.
Operational Impact
From an operations standpoint, a kernel UAF in a driver is never just a crash in isolation. It can interrupt jobs, reset VMs, poison test results, or force service restarts in places where deterministic audio routing is part of the workflow. The stable patch’s mention of fuzzers and frequent trigger/open-close cycles suggests that the bug may be easier to trip in automated systems than in manual use. (spinics.net)What failure might look like
The most obvious symptom would be an application fault or kernel instability during repeated PCM trigger activity. Depending on the surrounding stack, that could present as audio device errors, hung jobs, or a full system panic if the memory corruption path becomes severe enough. Because the bug touches stream lifetime and runtime structures, the visible symptom may not obviously point to ALSA at all. (spinics.net)The more subtle danger is false confidence. A system can appear stable during light testing and still be exposed under stress, especially if loopback devices are only exercised during special workflows. That makes this the kind of issue that can sit quietly in release engineering pipelines until a high-frequency workload or fuzzer stumbles into it. (spinics.net)
For teams running Linux audio in containers or ephemeral CI images, the takeaway is simple: if your automation mounts or loads
snd-aloop, you need to treat kernel update cadence as part of the test plan, not as an afterthought. Kernel races are often workload-dependent, and the workloads that reveal them are increasingly common in modern DevOps environments.What the Patch Tells Us About Kernel Quality
This fix is a good example of how the kernel community handles concurrency bugs in mature drivers. The maintainers did not redesign the loopback subsystem; they narrowed the unsafe window and added the minimum synchronization needed to keep pointer lifetimes coherent. That is a sign of a codebase that values stability and backportability over theoretical elegance. (spinics.net)Fuzzers as first-class security tools
The patch explicitly says the issue was spotted by fuzzers, with syzbot credited as the reporter. That reinforces the fact that kernel quality today is heavily shaped by automated adversarial testing. These tools are finding the sort of race conditions that once lurked unnoticed for years, especially in drivers that are rarely stressed in pathological ways by real users. (spinics.net)It also shows why the kernel’s stable process matters so much. A bug found in upstream development is one thing; a bug that gets quickly packaged for stable branches is another. The faster that synchronization fix travels downstream, the less time there is for distributions and OEM builds to carry the vulnerable code. (spinics.net)
The patch’s careful structure is also a reminder that memory safety issues do not always come from obvious allocator misuse. Sometimes they come from correct-looking code that makes an assumption about object lifetime across a handful of lines. That kind of bug is hard to spot in review, which is why fuzzing and stress testing remain indispensable. (spinics.net)
Competitive and Ecosystem Implications
Because ALSA is foundational Linux audio infrastructure, even driver-level fixes ripple across a large ecosystem. Distributions, cloud images, embedded vendors, and workstation builders all inherit the need to backport and validate the patch wheresnd-aloop is shipped or selectable. That is especially true for long-term support kernels, which may keep older code alive long after upstream has moved on. (spinics.net)Why downstreams care
For distro maintainers, the challenge is not just applying the patch, but confirming that it does not disturb existing audio workflows. Loopback audio is often used in unconventional setups, so a “simple” locking fix can still interact with real-world edge cases. That makes downstream regression testing more important than usual. (spinics.net)For vendors building appliances or appliances-like Linux systems, the lesson is similar. If your product exposes kernel audio modules as part of a larger media, conferencing, or virtualization stack, then an ALSA bug can become a product stability issue even if the driver is not front-and-center in marketing materials. The dependency chain matters more than the feature label.
For competitors and adjacent technologies, this kind of fix is a reminder that alternative audio stacks are only as safe as the kernel plumbing they depend on. PipeWire, JACK, PulseAudio, and virtualization layers may not be the buggy component, but they still benefit from a better-behaved kernel loopback path. In other words, a tiny ALSA fix can improve confidence across the whole Linux audio ecosystem.
Strengths and Opportunities
This fix is narrowly targeted, but that narrowness is a strength. It addresses the actual race instead of papering over symptoms, and it does so in a way that should be realistic for stable backports. For operators, that means the remediation path is clear and likely to be low-friction once the patched kernel lands. (spinics.net)- Precise scope: the patch targets the PCM trigger race without reshaping the whole driver. (spinics.net)
- Better lifetime safety: stronger locking and NULL checks reduce UAF risk. (spinics.net)
- Stable-friendly design: the change is suitable for long-term support backports. (spinics.net)
- Fuzzer-driven hardening: syzbot reporting suggests the issue was found before wider exploitation. (spinics.net)
- Low consumer blast radius: ordinary desktops may never use the affected module.
- Clear mitigation path: update the kernel and avoid unnecessary exposure of
snd-aloop. (spinics.net) - Ecosystem benefit: downstream audio and virtualization stacks get a safer substrate.
Risks and Concerns
Even though this is a relatively focused kernel bug, it still belongs in the security category because it can crash or destabilize systems under the right conditions. The biggest concern is that environments using loopback audio heavily may not realize they are exercising a vulnerable path until after an incident. (spinics.net)- Use-after-free potential: the original code path could dereference freed state during rapid stream transitions. (spinics.net)
- Automation exposure: CI, VDI, and test rigs may trigger the bug more readily than humans. (spinics.net)
- Hidden dependency: systems may load
snd-aloopindirectly through higher-level audio tooling. - Patch lag: downstream vendors may take time to backport and certify the fix. (spinics.net)
- Misleading severity perception: a niche driver can still create serious operational damage. (spinics.net)
- Incomplete visibility: a missing vendor CVE page can slow response if teams rely on one source.
- Regression risk: audio timing and trigger behavior can be sensitive to locking changes. (spinics.net)
Looking Ahead
The most likely next step is straightforward: downstream distributions and vendors will align on patched kernels, and administrators will need to verify whether their builds include the aloop fix. Because the upstream change is already in the stable stream, this should eventually become a routine update item rather than a prolonged incident. Still, the timing of that rollout will matter for anyone running automated audio or virtualization workflows. (spinics.net)The larger story is more interesting. Linux kernel security in 2026 continues to be shaped by concurrency correctness, not just classic memory corruption primitives. That means teams should expect more CVEs that look tiny in diff size but large in operational consequences, especially in drivers and subsystems that most admins rarely think about. (spinics.net)
- Confirm whether your kernel build loads snd-aloop.
- Track your vendor’s backport status for the fix.
- Test audio automation after updating, not before.
- Watch for follow-on advisories that clarify severity or affected releases.
- Reassess CI and VDI images that rely on loopback audio. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: