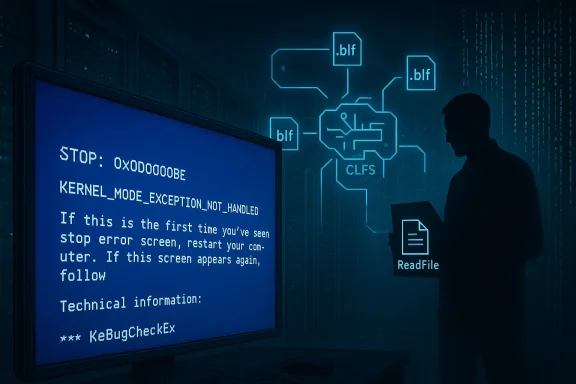
Security researchers have publicly released a working proof‑of‑concept (PoC) that reliably forces a Windows host into an unrecoverable Blue Screen of Death (BSoD) by abusing a logic bug in the Common Log File System driver (CLFS.sys), tracked as CVE‑2026‑2636 — a locally‑triggerable Denial‑of‑Service that requires only standard user privileges but can bring down shared and multi‑user hosts on demand.
The Windows Common Log File System (CLFS) is a kernel‑mode logging subsystem used by Windows components and third‑party applications to manage transactional logs stored in .blf files. Because CLFS runs in kernel context and services a wide variety of system features, bugs inside CLFS carry outsized reliability and security impact. The CVE‑2026‑2636 issue is not a memory corruption that yields remote code execution; instead it is a logic flaw that causes CLFS to reach an unrecoverable state and invoke the kernel crash routine KeBugCheckEx when certain flags on an I/O request are missing or incorrect.
A coordinated review of forum threads and internal discussion files confirms that CLFS has been historically — researchers and exploit authors have repeatedly probed it for kernel‑level issues — and that vendors and researchers continue to monitor it closely.
Because CLFS operates in kernel mode, logic failures can still cause severe outcomes — here the driver itself asks the kernel to crash rather than risking data corruption or other undefined behavior.
If you cannot patch immediately, implement compensating controls and monitoring:
Media outlets reported the PoC and summarized the risk; journalists and secondary outlets help raise awareness but sometimes omit technical nuance. Administrators should rely on the primary research write‑up and vendor updates for precise remediation steps.
Administrators should treat this as a patch + posture problem: verify the presence of the September 2025 cumulative updates (and any subsequent rollups) across all Windows 10/11 and server assets, prioritize systems that host multiple low‑privilege users, and implement compensating detection controls to quickly identify suspicious ReadFile activity against CLFS logs. If you manage VDI, RDS, or multi‑user services, assume higher exposure and treat remediation as urgent.
A note to operational teams: deterministic kernel crashes are noisy, disruptive, and easy to weaponize. The remedy here is straightforward — patch and validate — but the surrounding work (inventory, EDR tuning, incident readiness) is what separates a quick recovery from costly downtime. Act now, and validate thoroughly.
Source: Cyber Press PoC Published for Microsoft Windows Flaw That Allows Low-Privileged Users to Force Irrecoverable BSODs
 Background / Overview
Background / Overview
The Windows Common Log File System (CLFS) is a kernel‑mode logging subsystem used by Windows components and third‑party applications to manage transactional logs stored in .blf files. Because CLFS runs in kernel context and services a wide variety of system features, bugs inside CLFS carry outsized reliability and security impact. The CVE‑2026‑2636 issue is not a memory corruption that yields remote code execution; instead it is a logic flaw that causes CLFS to reach an unrecoverable state and invoke the kernel crash routine KeBugCheckEx when certain flags on an I/O request are missing or incorrect.A coordinated review of forum threads and internal discussion files confirms that CLFS has been historically — researchers and exploit authors have repeatedly probed it for kernel‑level issues — and that vendors and researchers continue to monitor it closely.
What the PoC does (technical summary)
How the flaw is triggered
- A non‑privileged user obtains a handle to an opened CLFS log file (a .blf file) and issues a crafted ReadFile call against that handle.
- Internally, CLFS dispatches the request and evaluates bits in the I/O Request Packet (IRP), notably the IRP_PAGING_IO and IRP_INPUT_OPERATION flags. These flags tell the driver how to treat the operation (paging vs. normal input), and are required for the internal routines to take the correct processing path.
- In the PoC scenario the ReadFile call is performed such that the expected IRP bits are not set. CLFS then follows an incorrect internal branch, reaches a critical consistency check where a particular CPU register (reported as AL == 0x0 in the researcher’s trace) forces the code to call KeBugCheckEx, producing a deterministic BSoD.
Why this is notable
- The crash is deterministic and reproducible — it does not rely on race conditions or fragile heap grooming. That makes weaponization easier for insiders or automated scripts.
- The vulnerability is exploitable with low privileges and requires no special user interaction beyond issuing the crafted read. The published PoC is intentionally small: two API calls are sufficient to demonstrate the condition in a test environment.
- While the CVSS base score assigned by researchers and aggregators is 5.5 (Medium), that numeric score understates the real‑world availability impact: repeated, on‑demand host crashes in VDI, Remote Desktop Session Host (RDS), or terminal server contexts can cause major operational disruptions and SLA violations.
Root cause and classification
The flaw has been attributed to improper handling of special or invalid elements in CLFS’s internal logic — a condition aligned with CWE‑159 (Improper Handling of Special Elements). In plain terms, CLFS validates or expects specific IRP flags to be present, and when they are absent the code takes an incorrect processing path that leads to an unrecoverable internal inconsistency. This is a logic validation failure rather than an exploitable memory corruption.Because CLFS operates in kernel mode, logic failures can still cause severe outcomes — here the driver itself asks the kernel to crash rather than risking data corruption or other undefined behavior.
Affected products and patch status
- The CVE was publicly recorded on February 25, 2026, with Fortra/Core Security listed as the reporting source. Aggregators and the U.S. NVD entry mirror the same technical summary.
- According to Core Security’s analysis and the NVD entry, Microsoft addressed this code path as part of the September 2025 cumulative updates. The vendor‑supplied combined servicing stack + cumulative update bundles shipped in September 2025 included the fix for CLFS on Windows 11 2024 LTSC and Windows Server 2025; other SKU coverage depends on whether the September 2025 LCU was applied to those systems. Administrators who never deployed the September 2025 rollups remain at risk.
- Public CVE trackers and vulnerability feeds list the vulnerability with a CVSS v3.1 vector of AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H (exploit requires local access but results in high availability impact).
Operational risk analysis
Availability and operational impact
- The weakness produces an immediate system halt (KeBugCheckEx) rather than a recoverable error. That makes it availability‑critical, particularly for hosts providing sessions or desktop services to many users.
- Environments at elevated risk include:
- Virtual Desktop Infrastructure (VDI) farms and session hosts where individual users share physical or virtual hosts.
- Multi‑user terminal servers, Citrix/RDS farms, and cloud‑delivered Windows sessions.
- Shared development or testing infrastructure where many low‑privilege user accounts exist.
- Because the PoC is small and deterministic, an insider or automated agent could easily orchestrate repeated outages, escalate operational response costs, or use downtime as a distraction during multi‑stage intrusions.
Exploitability and attacker model
- Attack complexity is low: an authenticated local user can run the PoC without special conditions beyond access to a CLFS .blf handle on the host.
- This is not a remote code execution or privilege elevation vector; it is a local Denial‑of‑Service. But the simplicity and reliability of the PoC increases its operational risk profile despite the medium CVSS numeric rating.
Broader threat scenarios
- Insider abuse: disgruntled employees or compromised user accounts with local access can weaponize the PoC to cause selective or repeated outages.
- Availability as a force multiplier: an attacker who wants to interrupt incident response, patching, or forensic activity can force reboots and wipe volatile telemetry, complicating response.
- Distraction: availability events can hide delicate stages of an attack or be used to create operational chaos during lateral movement or data exfiltration attempts.
Mitigation and detection: recommended actions for administrators
Apply the September 2025 cumulative updates (LCU + SSU) immediately across all affected Windows 10 and Windows 11 assets where the update is applicable. Prioritize systems that host multiple users or provide session services. Confirm the installed package content by checking the exact LCU/SSU versions rather than relying only on calendar month labeling.If you cannot patch immediately, implement compensating controls and monitoring:
- Immediate mitigations (short term)
- Restrict access to hosts where untrusted or external users have local login rights.
- Harden file permissions on directories that contain CLFS .blf files where practical; limit access to only trusted system accounts. Note that this may not be possible for all system logs, and kernel drivers can be accessed by legitimate OS subsystems, so this is a partial mitigation.
- Adjust bastion and jump host usage to reduce the number of devices where low‑privilege users can execute arbitrary binaries.
- Detection recommendations
- Monitor for an unexpected spike in system crashes and bugcheck events. Correlate sudden increases in BSoD occurrences with user activity on affected hosts (e.g., new logins, automated runs).
- Use EDR/XDR telemetry to flag local processes that open .blf handles and issue synchronous ReadFile operations in unusual contexts — particularly from user‑space processes that normally should not read CLFS internals. Create an alert rule for unusual patterns of ReadFile/NtReadFile calls against .blf objects originating from non‑system processes.
- Capture and preserve minidumps and memory dumps for forensic triage; repeated crashes will generate valuable forensic artifacts that help determine whether an outage was accidental, a PoC test, or malicious. However, note that repeated crashes may overwrite or truncate volatile evidence; rapid collection after an event is essential.
- Long‑term remediation
- Patch fleet devices to the latest cumulative updates and ensure servicing‑stack updates (SSUs) are also applied. Confirm with update management tools and the Microsoft Update Catalog / Security Update Guide metadata.
- Harden local account policies to reduce the number of users who can log on interactively to session hosts or VDI templates.
- Apply least‑privilege on file shares and session templates to shrink the attack surface available to non‑privileged accounts.
- Update incident response runbooks to explicitly include procedures for investigating deterministic kernel crashes that may be triggered by local activity.
Responsible disclosure and public PoC considerations
Core Security (Fortra) published a full technical write‑up with reproduction details and noted that the PoC triggers an immediate crash when run as an unprivileged user. The blog post contains sanitized reproduction details and indicates that a PoC with sources was made available in a controlled manner by the researcher. Public disclosure of PoC code increases the urgency for administrators to verify patch deployment quickly because the exploit does not require advanced skills to run.Media outlets reported the PoC and summarized the risk; journalists and secondary outlets help raise awareness but sometimes omit technical nuance. Administrators should rely on the primary research write‑up and vendor updates for precise remediation steps.
Critical analysis: strengths of the disclosure and residual concerns
Strengths
- Clear, reproducible research: The researcher provided an explicit call stack, IRP flag analysis, and a reproducible reproduction path that demonstrates deterministic behavior. This clarity helps vendors produce a surgical fix and helps defenders validate remediation.
- Responsible linking to vendor fixes: The disclosure explicitly notes that the code path was fixed as part of the September 2025 cumulative updates, allowing operators with good update hygiene to already be protected. This reduces immediate crisis volume to some extent.
- Moderate CVSS but high operational impact: The community has applied a medium base score (5.5), which is correct for a local DoS in technical terms, but the public write‑up rightly emphasizes the real‑world availability risk in shared environments.
Residual concerns and attack surface realities
- Silent patching and visibility: Core Security and NVD both note the fix existed in the September 2025 rollup, which means some fleets may already be safe — but silent or unpublicized fixes create an uneven window where some operators believe they are patched while others are exposed. Operators cannot assume safe state; they must validate the presence of the fix on every affected SKU.
- Public PoC increases abuse potential: The PoC’s small size and determinism mean a low‑skilled insider or an automated script can weaponize the crash quickly. That shifts the risk profile from theoretical to practical for high‑availability workloads.
- Monitoring and mitigation gaps: Not all organizations have fine‑grained EDR rules that can distinguish legitimate CLFS reads from malicious PoC runs. Implementing such rules requires careful testing to avoid false positives because legitimate system components and logging services also interact with CLFS.
Practical checklist for administrators (actionable steps)
- Inventory: Identify Windows hosts that run multi‑user session services, terminal servers, VDI hosts, and critical servers that accept non‑admin logins.
- Validate patch level:
- Confirm that the September 2025 cumulative update (LCU + SSU) or a later monthly rollup is installed on each asset, or that the OS build includes the CLFS fix. Use update management tools and the Microsoft Update Catalog/KB metadata to validate.
- Deploy patches where missing and schedule reboots as required.
- Short‑term containment:
- Restrict interactive logon and unsupervised low‑privilege code execution on shared hosts.
- Temporarily limit exposure of host templates used for VDI/persistent sessions.
- Detection:
- Create EDR/XDR rules to flag unusual ReadFile/NtReadFile activity targeting .blf objects from non‑system processes.
- Monitor and alert on sudden increases in bugcheck codes, especially when correlated with known user activity.
- Forensic readiness:
- Ensure crash dumps are collected and preserved off‑host immediately after an event.
- Refresh incident response playbooks to include a BSoD investigation path tied to local user activity.
What administrators should not do
- Do not attempt to run the public PoC on production systems. The PoC intentionally causes an unrecoverable kernel crash and will interrupt services and could complicate incident response and forensic analysis.
- Do not rely solely on endpoint telemetry that is not configured to capture pre‑crash artifacts — immediate remediation requires preserved dumps and EDR telemetry from just before the crash.
Final assessment and takeaways
CVE‑2026‑2636 is a prime example of how a seemingly modest logic bug in a kernel driver can produce outsized operational impact. The technical root cause — improper handling of IRP flag combinations in CLFS — is well documented in the researcher’s write‑up and in vulnerability aggregators; the PoC is small, deterministic, and available publicly. That combination makes this a high‑urgency availability risk for multi‑tenant and shared Windows environments even though the CVSS base score is rated as medium.Administrators should treat this as a patch + posture problem: verify the presence of the September 2025 cumulative updates (and any subsequent rollups) across all Windows 10/11 and server assets, prioritize systems that host multiple low‑privilege users, and implement compensating detection controls to quickly identify suspicious ReadFile activity against CLFS logs. If you manage VDI, RDS, or multi‑user services, assume higher exposure and treat remediation as urgent.
A note to operational teams: deterministic kernel crashes are noisy, disruptive, and easy to weaponize. The remedy here is straightforward — patch and validate — but the surrounding work (inventory, EDR tuning, incident readiness) is what separates a quick recovery from costly downtime. Act now, and validate thoroughly.
Source: Cyber Press PoC Published for Microsoft Windows Flaw That Allows Low-Privileged Users to Force Irrecoverable BSODs