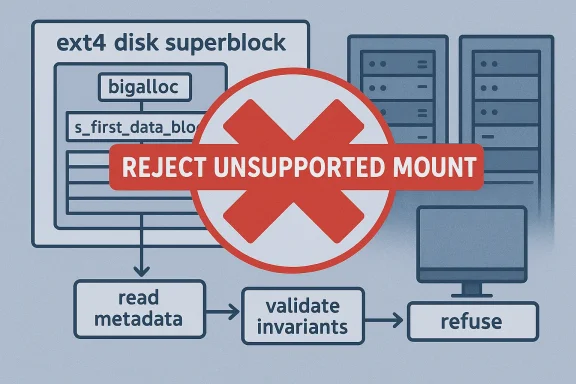
The Linux kernel’s ext4 filesystem is now facing a newly published CVE that closes off an unsupported mount configuration before it can do damage. CVE-2026-31447 addresses a specific mismatch between bigalloc and a nonzero s_first_data_block, and the fix is simple in spirit: refuse to mount a filesystem that violates an invariant ext4 does not support. That sounds narrow, but narrow filesystem bugs often matter because they live at the boundary between malformed on-disk state and trusted kernel behavior. The public record shows the issue was recently published by NVD, with Microsoft’s vulnerability guide linking back to the upstream kernel fix and stable backports is one of the most widely deployed Linux filesystems, and that alone gives even small mount-path bugs outsized operational weight. The filesystem is mature, heavily reviewed, and generally conservative by design, but it still has advanced features that complicate the trust model. Bigalloc is one of those features: instead of allocating storage one block at a time, ext4 can allocate in clusters, which is useful for large-file workloads and reduces metadata overhead on suitably configured volumes.
The vulnerability description is unusually direct. The kernel change resolves the condition by stating that bigalloc with s_first_data_block != 0 is not supported, reject mounting it. In other words, the bug is not a subtle arithmetic drift deep in allocation logic; it is a bad configuration combination that should never have been accepted in the first place. That makes the fix a classic example of defensive validation: fail early, before the filesystem has a chance to inmetadata as legitimate state.
That approach matters because ext4’s superblock fields define core layout assumptions. The
From an operational perspective, CVE-2026-31447 is less about exploit drama and more about making sure the kernel does not accept a filesystem image whose layout it cannot safely interpret. That may sound mundane, but mundane rejection is often the best possible security outcome. A mount denial is frustrating; a silently accepted but misinterpreted filesystem is worse.
The CVE record shows the issue was published on April 22, 2026, and Miceflects the same upstream kernel-originated description and linked stable commits. For administrators, that means the issue is fresh enough that backport status is the immediate question, not just the abstract vulnerability class.
The timing also fits a broader pattern in Linux storage hardening. Recent kernel work has continued to refine filesystems not only for performance but for safe refusal when a configuration falls outside supported semantics. That philosophy is especially important for ext4 because its compatibility promise means it will often be asked to mount volumes created by older tools, third-party images, or opaque appliance workflows.
Bigalloc is one of ext4’s more specialized options. Kernel documentation explains that it groups blocks into clusters, making each bitmap bit represent a larger allocation unit and reducing metadata overhead for large-file workloads. The tradeoff is obvious: the filesystem gains efficiency when the workload fits the model, but the margin for layout oddities gets smaller because more of the filesystem’s internal math assumes a specific relationship between cluster geometry and block placement.
The
Historically, ext4 has tended to prefer validation at mount time rather than trying to compensate for structurally unsupported layouts later. That is a healthy design choice. Filesystem code lives in the kernel’s trust boundary, and if the on-disk metadata does not satisfy the filesystem’s own invariants, refusing to mount is usually the safest possible response. The alternative is allowing invalid state to propagate into allocation, journaling, or recovery code, where the consequences can be harder to predict and harder to diagnose.
The fix is narrow, but narrow fixes are often the most valuable in storage code because they reduce ambiguity. If a filesystem format combination is unsupported, it should be rejected deterministically, not partially accepted and then handled inconsistently by different subsystems. That principle is especially important in Linux, where filesystems are expected to survive crashes, remounts, and recovery sequences without making heroic guesses about what the metadata “probably meant.”
Why
The important thing is not that ext4 is “broken” in the abstract. The important thing is that the filesystem had been willing to accept a metadata combination that its bigalloc logic does not fully support. Once you accept that combination, the rest of the mount path inherits that ambiguity.
That is good security hygiene for a filesystem with a huge deployment footprint. The logic is not glamorous, but it is exactly the kind of front-loaded validation that prevents hard-to-debug corruption later.
That pattern is not merely conservative. It is practical. Once mount succeeds, every later code path has to assume the filesystem’s layout is coherent. If the layout is not coherent, the kernel may end up chasing symptoms in allocation, inode handling, or journaling when the real problem was decided at mount time.
Key implications include:
That pattern is important because filesystem mount bugs are not only theoretical. They matter most on systems that must mount unknown or externally supplied volumes: rescue environments, appliance images, migration hosts, and cloud instances that boot from prebuilt disk images. In those environments, a mount rejection is often the first and only chance to keep invalid metadata from being trusted.
That distinction can be easy to miss in public CVE chatter. People often associate “critical” only with code execution, but kernel engineers know better. A filesystem that can be made to accept unsupported on-disk structure is a risk to data integrity, recovery confidence, and operational continuity.
The enterprise consequence is simple: fail fast, fail loud, fail safely. That is better than accepting a volume and discovering metadata confusion after a crash, reboot, or migration.
The practical lesson for consumer users is don’t ignore mount errors. If the kernel refuses a filesystem that used to mount elsewhere, the issue may be a metadata/layout mismatch rather than a broken cable or transient hardware problem.
This CVE is a reminder that compatibility policies are part of the security model. If the rules are too permissive, the kernel becomes responsible for making sense of data it never promised to support.
A second thing to watch is whether filesystem creation tools add better validation around bigalloc and
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
The vulnerability description is unusually direct. The kernel change resolves the condition by stating that bigalloc with s_first_data_block != 0 is not supported, reject mounting it. In other words, the bug is not a subtle arithmetic drift deep in allocation logic; it is a bad configuration combination that should never have been accepted in the first place. That makes the fix a classic example of defensive validation: fail early, before the filesystem has a chance to inmetadata as legitimate state.
That approach matters because ext4’s superblock fields define core layout assumptions. The
s_first_data_block field determines where the filesystem’s first usable data block begins, and in ext4’s on-disk format the bigalloc feature changes how allocation metadata is interpreted at a fundamental level. The kernel documentation notes that bigalloc stores cluster size in the superblock and changes the block allocator’s unit of accounting, which is exactly the kind of feature that magnifies any inconsistency in layout assumptions.From an operational perspective, CVE-2026-31447 is less about exploit drama and more about making sure the kernel does not accept a filesystem image whose layout it cannot safely interpret. That may sound mundane, but mundane rejection is often the best possible security outcome. A mount denial is frustrating; a silently accepted but misinterpreted filesystem is worse.
 Why this is relevant now
Why this is relevant now
The CVE record shows the issue was published on April 22, 2026, and Miceflects the same upstream kernel-originated description and linked stable commits. For administrators, that means the issue is fresh enough that backport status is the immediate question, not just the abstract vulnerability class.The timing also fits a broader pattern in Linux storage hardening. Recent kernel work has continued to refine filesystems not only for performance but for safe refusal when a configuration falls outside supported semantics. That philosophy is especially important for ext4 because its compatibility promise means it will often be asked to mount volumes created by older tools, third-party images, or opaque appliance workflows.
Background
ext4 has long occupied an unusual place in Linux storage. It is both conservative and feature-rich, supporting journaling, extents, delayed allocation, and optional features that stretch the original ext3 model without abandoning its basic compatibility goals. That balance is part of why ext4 remains the default or default-adjacent choice on many Linux distributions and embedded systems.Bigalloc is one of ext4’s more specialized options. Kernel documentation explains that it groups blocks into clusters, making each bitmap bit represent a larger allocation unit and reducing metadata overhead for large-file workloads. The tradeoff is obvious: the filesystem gains efficiency when the workload fits the model, but the margin for layout oddities gets smaller because more of the filesystem’s internal math assumes a specific relationship between cluster geometry and block placement.
The
s_first_data_block field is part of that geometry. In the ext4 superblock, it defines the first data block, and other layout fields are interpreted relative to that starting point. The on-disk documentation lists it among the core superblock members, alongside s_log_cluster_size, which explicitly determines cluster size when bigalloc is enabled. That is why a nonzero first data block can become dangerous once bigalloc enters the picture: the feature combination can invalidate assumptions the mount path expects to hold.Historically, ext4 has tended to prefer validation at mount time rather than trying to compensate for structurally unsupported layouts later. That is a healthy design choice. Filesystem code lives in the kernel’s trust boundary, and if the on-disk metadata does not satisfy the filesystem’s own invariants, refusing to mount is usually the safest possible response. The alternative is allowing invalid state to propagate into allocation, journaling, or recovery code, where the consequences can be harder to predict and harder to diagnose.
What changed in practice
The published CVE description does not suggest a new attack primitive or a memory corruption flaw. Instead, it says the kernel now rejects a mount when it encounters a bigalloc filesystem with a nonzeros_first_data_block. That is an important distinction.The fix is narrow, but narrow fixes are often the most valuable in storage code because they reduce ambiguity. If a filesystem format combination is unsupported, it should be rejected deterministically, not partially accepted and then handled inconsistently by different subsystems. That principle is especially important in Linux, where filesystems are expected to survive crashes, remounts, and recovery sequences without making heroic guesses about what the metadata “probably meant.”
The Bigalloc Invariant
Bigalloc’s promise is straightforward: use clusters instead of single blocks to reduce allocation overhead and fragmentation for large-file workloads. The kernel documentation describes it as a way to shrink bitmap size and improve efficiency on filesystems storing mostly large objects. But that efficiency comes with a price: the underlying layout has to remain consistent with the cluster-aware model.Why s_first_data_block matters
**s_first_data_block** is not just bookkeeping. It defines the offset where the filesystem’s usable data region begins, and that offset influences how group descriptors, bitmaps, and allocation boundaries line up. In ordinary ext4 layouts, that relationship is well understood. In bigalloc mode, however, cluster accounting changes the assumptions the allocator can safely make, so a nonzero first data block can create a geometry the code was never meant to support.The important thing is not that ext4 is “broken” in the abstract. The important thing is that the filesystem had been willing to accept a metadata combination that its bigalloc logic does not fully support. Once you accept that combination, the rest of the mount path inherits that ambiguity.
What the rejection accomplishes
Rejecting the mount prevents several classes of downstream problems at once. It avoids misinterpreting on-disk structures, keeps allocation logic from operating on unsupported geometry, and reduces the chance of recovery code facing a layout it cannot reconcile cleanly. In practice, the kernel is saying, this filesystem image is not valid for this feature set, so we will not proceed.That is good security hygiene for a filesystem with a huge deployment footprint. The logic is not glamorous, but it is exactly the kind of front-loaded validation that prevents hard-to-debug corruption later.
Mount-Time Validation as a Security Boundary
Filesystem mount paths are a security boundary whether they are treated that way or not. The kernel reads metadata from disk, interprets it as a valid structure, and then uses it to govern allocations, journaling, recovery, and user-visible behavior. If that interpretation step is too permissive, the filesystem may accept inconsistent state and only discover the mismatch after data structures have already been trusted.Early rejection is the right pattern
CVE-2026-31447 follows the same design philosophy used across other robust kernel subsystems: validate the input as close to the boundary as possible. In this case, the boundary is the mount operation itself. If bigalloc requires a zero first data block, then any other value is not a recoverable corner case; it is an unsupported configuration that should be refused immediately.That pattern is not merely conservative. It is practical. Once mount succeeds, every later code path has to assume the filesystem’s layout is coherent. If the layout is not coherent, the kernel may end up chasing symptoms in allocation, inode handling, or journaling when the real problem was decided at mount time.
Why this matters to administrators
For enterprise users, mount-time rejection is better than latent corruption. A rejected volume is visible, diagnosable, and operationally manageable. A wrongly mounted volume can produce silent damage that shows up hours or days later, possibly after backups have run or application data has already been updated.Key implications include:
- The failure is likely to be deterministic rather than intermittent.
- The problem is more about unsupported geometry than active exploitation.
- Remediation will probably be a mix of kernel update and filesystem image correction.
- Operators should verify whether affected images were created by old tooling or unusual provisioning workflows.
- Appliance and embedded fleets may feel the impact more than desktop users.
- Recovery tooling may need updates if it can generate the unsupported layout.
Upstrh Trail
The public CVE entry indicates the issue came from kernel.org and was rapidly linked to multiple stable-tree references, which is what you want to see for a filesystem invariant bug. The record includes several stable commit references, suggesting maintainers treated this as something that should be corrected across supported branches rather than left as a mainline-only cleanup.That pattern is important because filesystem mount bugs are not only theoretical. They matter most on systems that must mount unknown or externally supplied volumes: rescue environments, appliance images, migration hosts, and cloud instances that boot from prebuilt disk images. In those environments, a mount rejection is often the first and only chance to keep invalid metadata from being trusted.
How this differs from exploit-focused CVEs
This is not the kind of bug that usually yields a dramatic proof-of-concept exploit. Instead, it is a correctness defect that can produce reliability and integrity problems. Those still count as serious security issues because storage is the substrate on which everything else depends.That distinction can be easy to miss in public CVE chatter. People often associate “critical” only with code execution, but kernel engineers know better. A filesystem that can be made to accept unsupported on-disk structure is a risk to data integrity, recovery confidence, and operational continuity.
Enterprise Impact
For enterprises, the main question is not whether this CVE allows direct compromise. The real question is whether a kernel in production can be trusted to mount storage safely across heterogeneous fleets. On that front, this kind of issue is significant because it sits in the path that every storage-backed workload depends on.Storage fleets feel this first
Storage arrays, virtual machine images, and container hosts all rely on predictable mount semantics. If a volume image is created with a mismatched ext4 layout, a permissive kernel might appear to work until later when recovery or resize operations fail. By rejecting the mount early, the kernel prevents a class of delayed failures that are much more expensive to debug.The enterprise consequence is simple: fail fast, fail loud, fail safely. That is better than accepting a volume and discovering metadata confusion after a crash, reboot, or migration.
Operational scenarios where this matters
- Migration from older provisioning tools that may have created unusual layouts.
- Disaster-recovery restores involving disk images from other environments.
- Embedded or appliance systems using scripted filesystem creation.
- Virtualized fleets where images are cloned across hardware generations.
- Support cases where the on-disk geometry is not obvious to the operator.
- Forensic or rescue mounts of third-party ext4 volumes.
Consumer and Desktop Impact
Consumer users are less likely to hit this bug than administrators dealing with custom disk images or specialized storage provisioning. Most desktop ext4 filesystems are created by mainstream tools that use standard settings, so the risky combination described by CVE-2026-31447 is unlikely to appear by accident.When a home user might notice
The most plausible consumer scenario is a manually created disk image, a backup restored from another environment, or a removable drive prepared by a nonstandard tool. In those cases, the user might see a mount failure rather than data loss. That outcome is inconvenient, but it is preferable to a filesystem that mounts and then behaves unpredictably.The practical lesson for consumer users is don’t ignore mount errors. If the kernel refuses a filesystem that used to mount elsewhere, the issue may be a metadata/layout mismatch rather than a broken cable or transient hardware problem.
Reliability, Compatibility, and Policy
CVE-2026-31447 reinforces a broader truth about Linux filesystems: compatibility is not the same thing as universal acceptability. ext4 can read a lot of old layouts and survive a lot of rough edges, but not every combination of features is valid. When the kernel detects one of those unsupported combinations, it must choose correctness over leniency.Why policy belongs in the mount path
A filesystem mount is effectively a policy decision. The kernel decides whether the metadata on disk fits the contract of the filesystem driver. That contract includes feature compatibility, layout rules, and feature interactions. If the mount code relaxes those rules too much, it risks normalizing invalid state.This CVE is a reminder that compatibility policies are part of the security model. If the rules are too permissive, the kernel becomes responsible for making sense of data it never promised to support.
A numbered view of the safety model
- Detect the filesystem feature set.
- Verify layout constraints against that feature set.
- Reject unsupported combinations before they reach allocation logic.
- Keep recovery and journaling code from inheriting invalid assumptions.
- Preserve user trust by making failures explicit rather than silent.
Strengths and Opportunities
The good news here is that the fix is clean, the scope is narrow, and the operational message is easy to understand. ext4 is not being redesigned; it is being taught to reject a combination it should not have accepted. That is a sign of healthy maintenance, not panic.- Simple remediation: the kernel can block the invalid mount condition without changing ext4’s core design.
- Low regression risk: early rejection is usually safer than trying to “handle” unsupported geometry later.
- Clear operator guidance: administrators can look for nonstandard bigalloc layouts and correct provisioning.
- Stable-backport friendly: mount validation fixes are often easier to backport than deeper data-path changes.
- Improved data integrity: refusing bad metadata prevents downstream corruption or recovery ambiguity.
- Good fit for enterprise policies: the fix aligns with conservative storage-validation standards.
- Better tooling pressure: filesystem creation tools are nudged toward valid, supportable layouts.
Risks and Concerns
Even a narrow filesystem CVE can create real-world headaches, especially when it affects images or deployments that are already in circulation. The main risk is that unsupported filesystems may exist in backup archives, appliance bundles, or obscure provisioning paths long before anyone notices the issue.- Hidden exposure in legacy or vendor-built images.
- Backport delays on long-term kernel branches.
- Inconsistent behavior across distros if some branches are patched sooner than others.
- Operator confusion when a mount starts failing after a kernel update.
- Tooling gaps if filesystem creators do not clearly validate the unsupported combination.
- Rescue-environment friction when recovery kernels reject a disk that previously mounted elsewhere.
- Potential for misdiagnosis if the mount failure is mistaken for hardware trouble instead of metadata incompatibility.
What to Watch Next
The immediate question is how fast downstream kernels absorb the fix and how clearly vendors communicate the unsupported layout rule. Because this is a mount-path issue, the real-world impact will depend heavily on whether the affected filesystem images are already deployed or still sitting in build pipelines.A second thing to watch is whether filesystem creation tools add better validation around bigalloc and
s_first_data_block. If the kernel is now rejecting the combination, the ecosystem benefits when mkfs-style tooling helps prevent it from being generated in the first place. That would reduce the chance of operators ever encountering the error in production.Watch list
- Stable backports in long-term Linux branches.
- Distribution advisories mapping the CVE to shipped kernel versions.
- Any mkfs or provisioning-tool validation updates.
- Reports from appliance and embedded vendors using ext4 bigalloc.
- Clarifications from maintainers about whether the mount refusal is universal across supported branches.
- Follow-on hardening in ext4 mount-time validation paths.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center