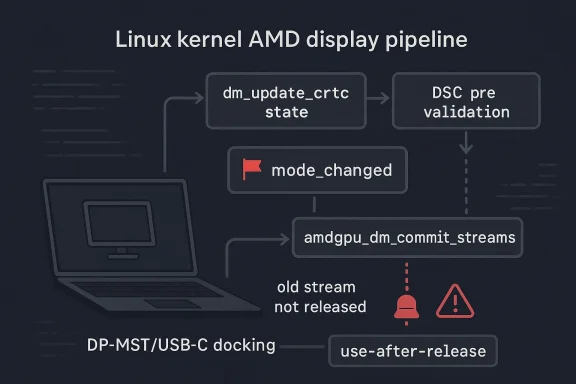
CVE-2026-31488 is a narrowly scoped but operationally serious Linux kernel bug in AMD’s display stack, and it shows how a small state-management mistake can ripple into memory leaks and use-after-free conditions. The flaw centers on drm/amd/display and the way DSC validation handled mode_changed when unrelated display changes were happening in the same atomic commit. In practical terms, a laptop panel’s state could be misclassified just because external MST/DP displays were being attached, and that misclassification could prevent the kernel from releasing or refcounting streams correctly. The published kernel.org description, as reproduced in Microsoft’s vulnerability record, makes clear that the fix is to preserve the earlier value of
The Linux graphics stack is one of those places where correctness is not just about rendering pixels. It is about preserving a precise chain of object lifetimes, reference counts, and transactional state across atomic commits. In AMD’s display code, that transaction model is especially delicate because the driver has to reconcile display mode changes, stream creation, and hardware-specific features like Display Stream Compression while the kernel is still deciding what the final configuration should be. A mistake in that pipeline does not merely create a visual glitch; it can corrupt the bookkeeping that keeps the driver safe.
The CVE description points back to commit 17ce8a6907f7, which added DSC pre-validation in atomic check. That earlier change was well-intentioned: it tried to predict whether DSC configuration changes would alter timing for a stream, and if not, it reset
That distinction matters because atomic display commits are not isolated little events. They are multi-object transactions, and the kernel must keep track of what changed for each CRTC independently. If one CRTC is affected by external monitor attachment while another is changing for a different reason, the driver cannot safely collapse those cases together. The CVE record makes that failure mode explicit:
This is why the issue graduated from a subtle correctness bug into a security-relevant vulnerability. Once the old stream is retained accidentally and the new one never gets its proper reference, the code creates a memory leak at first and then a use-after-free later when the stream is disabled. The CVE text includes a KASAN trace showing the crash in
What makes CVE-2026-31488 particularly interesting is that the flaw is not a simple invalid input bug. It is a state propagation bug, which is often harder to detect and easier to overlook during review. The driver made an assumption about whether a mode change was “real” or just collateral to DSC recomputation, and that assumption was only valid when unrelated changes were absent. In other words, the bug lived in the space between intent and transaction ordering.
The CVE description gives a concrete example: a laptop’s internal panel may behave differently depending on whether external screens are attached. If plugging in DP-MST displays changes the display configuration, the internal panel could also be part of the same atomic update even if its own DSC timing did not change. In that case, clearing
That is where the leak begins. The old stream is never released because the driver no longer thinks the CRTC changed in a way that requires replacing it. Then, because the new stream is not fully referenced by the atomic commit tail, the later teardown path can touch memory that should have been retained, producing the use-after-free seen in the KASAN trace. The bug therefore reflects a classic kernel pattern: a mistaken optimization in one phase becomes a memory-safety bug in a later phase.
The KASAN report in the CVE text is especially important because it shows a concrete fault location in
CVE-2026-31488 is therefore a good example of a bug that starts as a logic error and ends as a memory-safety issue. It does not require attacker-controlled data in the classic sense. Instead, it requires the right display topology and the right sequence of configuration changes. Those conditions are realistic enough in modern laptops, docking stations, and multi-display workstation setups that the issue clearly belongs in the security queue rather than the “mere bug” bin.
That is a classic kernel fix philosophy: when the code cannot infer the full truth at a later stage, preserve the earlier truth before the state machine gets blurred by intermediate logic. It is not flashy, but it is robust. The patch also has the advantage of being narrowly targeted. Rather than redesigning the display state machine, it simply corrects the point at which one flag is normalized. That is the sort of change stable maintainers prefer because it minimizes regression risk.
This sort of fix also illustrates a broader display-driver truth: local correctness is not enough. A helper can be “correct” in isolation and still be wrong in the larger commit sequence. The AMD patch acknowledges that the point of no return had already passed by the time DSC pre-validation ran, so the only safe move was to restore earlier context instead of trusting a narrower recomputation.
This interaction also exposes a common kernel engineering problem: a helper designed around one subsystem’s invariants can become unsafe when a second subsystem’s assumptions are layered on top. DSC logic wants to know whether timing changed. MST logic wants to know whether the attached display tree changed. The atomic commit framework, meanwhile, needs to preserve both truths and decide whether the overall CRTC state changed. When any one layer oversimplifies, the others inherit the mistake.
That is why the mode flag had to survive DSC pre-validation unchanged unless there was a reliable reason to clear it. The driver was not just managing a compression decision; it was managing the integrity of the full atomic transaction. The patch fixes precisely that boundary.
For enterprise users, the stakes are higher because display stacks are often part of a broader operational workflow: hot-desking, conference-room setups, virtualized desktops, engineering workstations, and thin-client environments all depend on predictable graphics state transitions. A leak in the display driver may not sound like a server-class outage, but in practice it can affect device reliability, break user sessions, and trigger crashes that are hard to attribute quickly. In managed fleets, that kind of intermittent issue is expensive.
That is also why the issue matters beyond AMD hardware enthusiasts. Enterprises tend to deploy a mix of hardware profiles, and graphics regressions often show up first in support desks rather than vulnerability scanners. If a patch affects a large enough share of AMD-based laptops or workstations, it quickly becomes a fleet-management concern rather than a niche driver bug.
Backports also tell us the problem was cleanly understood. Stable maintainers do not usually like patches that depend on speculative behavior or broad redesigns. The fact that this fix was selected suggests that the root cause was narrow enough to isolate and the repair was modest enough to carry into maintained branches. That is usually reassuring for operators because it means the patch can spread without introducing large new behavior changes.
In other words, the existence of the stable fix is the real operational takeaway. It tells downstream vendors and distro maintainers that the issue is not just a theoretical coding mistake upstream. It is a bug with a known repair path that is already suitable for maintained kernels. That makes patch deployment a straightforward priority for anyone shipping AMD graphics support.
There is also a broader opportunity here for display-driver maintainers to examine adjacent transaction paths for the same class of bug. Whenever a helper function mutates shared commit flags after partial analysis, it is worth asking whether it is discarding context it should preserve. The AMD case is a useful reminder that atomic graphics code needs a strong memory of what happened before each sub-analysis ran.
A second concern is that memory-safety issues in graphics code can look harmless until they are not. A leak may be dismissed as a cleanup problem, but once the wrong object lifetime reaches a later teardown path, the impact becomes much more severe. The KASAN trace included in the record is a reminder that kernel display bugs can cross from correctness to safety without warning.
There is also the familiar risk of patch lag. Even when the fix is already in stable branches, downstream vendors and OEMs may take time to absorb it into signed or certified builds. For AMD-based laptops in managed environments, that means the real exposure window is determined less by upstream publication and more by the speed of vendor delivery.
It will also be worth watching whether additional AMD display fixes appear in the same area. When one transaction-state bug is uncovered in a subsystem as complex as DRM, it often prompts maintainers to inspect neighboring paths for similar flag-handling mistakes. That does not mean the graphics stack is unstable in general; it means the code is mature enough that the remaining bugs are increasingly about edge-case sequencing rather than broad architectural errors.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
mode_changed instead of blindly clearing it during DSC pre-validation.
 Background
Background
The Linux graphics stack is one of those places where correctness is not just about rendering pixels. It is about preserving a precise chain of object lifetimes, reference counts, and transactional state across atomic commits. In AMD’s display code, that transaction model is especially delicate because the driver has to reconcile display mode changes, stream creation, and hardware-specific features like Display Stream Compression while the kernel is still deciding what the final configuration should be. A mistake in that pipeline does not merely create a visual glitch; it can corrupt the bookkeeping that keeps the driver safe.The CVE description points back to commit 17ce8a6907f7, which added DSC pre-validation in atomic check. That earlier change was well-intentioned: it tried to predict whether DSC configuration changes would alter timing for a stream, and if not, it reset
mode_changed to false. The problem was that this logic assumed DSC was the only important variable in play. In real systems, however, a single KMS commit can combine a DSC-related topology change with an entirely unrelated mode change elsewhere in the same display pipeline.That distinction matters because atomic display commits are not isolated little events. They are multi-object transactions, and the kernel must keep track of what changed for each CRTC independently. If one CRTC is affected by external monitor attachment while another is changing for a different reason, the driver cannot safely collapse those cases together. The CVE record makes that failure mode explicit:
dm_update_crtc_state() may already have created new streams for CRTCs with DSC-independent changes, but amdgpu_dm_commit_streams() will later fail to release the old stream if mode_changed was zeroed too early.This is why the issue graduated from a subtle correctness bug into a security-relevant vulnerability. Once the old stream is retained accidentally and the new one never gets its proper reference, the code creates a memory leak at first and then a use-after-free later when the stream is disabled. The CVE text includes a KASAN trace showing the crash in
dc_stream_release() during destruction, which confirms that the bug is not theoretical. It is a live memory-safety failure that can surface under real workload transitions.Why AMD display bugs deserve attention
Display drivers often look less threatening than networking or filesystem code because their failures are usually associated with visual artifacts, not data theft. That impression is misleading. Modern graphics stacks are deeply stateful and heavily concurrent, and they frequently touch memory management paths that are shared with the rest of the kernel. A bad transition in the display core can cascade into refcount problems just as easily as a bad transition in any other subsystem.What makes CVE-2026-31488 particularly interesting is that the flaw is not a simple invalid input bug. It is a state propagation bug, which is often harder to detect and easier to overlook during review. The driver made an assumption about whether a mode change was “real” or just collateral to DSC recomputation, and that assumption was only valid when unrelated changes were absent. In other words, the bug lived in the space between intent and transaction ordering.
- The vulnerable path is in AMD’s display manager.
- The failure depends on mixed atomic commits.
- The bug can produce both a leak and a use-after-free.
- The issue was serious enough for a stable backport.
- The fix is small, but the consequences were not.
How the Bug Happens
The core of the problem is thatpre_validate_dsc() was treating a stream as if it had no meaningful mode change if DSC recomputation produced no timing change. That sounds reasonable in isolation. If a stream’s timing is stable, why mark it as changed? The answer is that timing stability is not the same thing as commit-wide state stability, and the kernel had already moved past the point where it could safely infer the rest of the transaction from that one signal.The CVE description gives a concrete example: a laptop’s internal panel may behave differently depending on whether external screens are attached. If plugging in DP-MST displays changes the display configuration, the internal panel could also be part of the same atomic update even if its own DSC timing did not change. In that case, clearing
mode_changed for the internal panel would be wrong because the panel’s state was still part of a broader transaction involving unrelated mode changes.The transaction-ordering trap
The subtlety here is that the commit path is not a single monolithic decision. First,dm_update_crtc_state() builds new stream objects for the CRTCs that need them. Then pre_validate_dsc() may rewrite a flag based on a narrower DSC-specific conclusion. By the time the driver reaches amdgpu_dm_commit_streams(), the state machine has already been partially advanced. If the flag has been cleared incorrectly, the rest of the commit logic will make the wrong lifetime decisions.That is where the leak begins. The old stream is never released because the driver no longer thinks the CRTC changed in a way that requires replacing it. Then, because the new stream is not fully referenced by the atomic commit tail, the later teardown path can touch memory that should have been retained, producing the use-after-free seen in the KASAN trace. The bug therefore reflects a classic kernel pattern: a mistaken optimization in one phase becomes a memory-safety bug in a later phase.
- DSC timing stability was treated as a proxy for full transaction stability.
- That proxy failed when unrelated mode changes were present.
- The wrong
mode_changedvalue distorted later lifetime management. - The failure path produced both resource leakage and unsafe teardown.
The Memory-Safety Impact
It is easy to underestimate a bug like this because the first visible symptom may be a leak, not a crash. But in kernel code, leaks are often only the first domino. When a stream object is kept alive or discarded incorrectly, later code may release it twice, use stale pointers, or skip reference acquisition entirely. That is exactly the kind of chain that turns a bookkeeping error into a use-after-free.The KASAN report in the CVE text is especially important because it shows a concrete fault location in
dc_stream_release(). That matters for triage: it tells maintainers that the problem is not just a theoretical mismatch between state flags, but a real invalid memory access on teardown. The presence of a workqueue path in the trace also reinforces that this kind of bug can surface asynchronously, after the commit that caused it has already “succeeded” from the user’s perspective.Why use-after-free follows leaks so often
In kernel systems, leaks and use-after-free conditions are often linked by the same bad ownership decision. If an object is not released when it should be, later code may assume it still exists and try to interact with it as though it had been safely tracked all along. Conversely, if a new object is created but never fully referenced, a later cleanup path may discard it too early. That combination is especially dangerous in display stacks, where multiple objects represent one visual transaction.CVE-2026-31488 is therefore a good example of a bug that starts as a logic error and ends as a memory-safety issue. It does not require attacker-controlled data in the classic sense. Instead, it requires the right display topology and the right sequence of configuration changes. Those conditions are realistic enough in modern laptops, docking stations, and multi-display workstation setups that the issue clearly belongs in the security queue rather than the “mere bug” bin.
- The first visible symptom may be a leak.
- The hidden danger is the later use-after-free.
- Asynchronous teardown makes the bug harder to reproduce.
- The crash trace confirms the bug is not purely theoretical.
The Fix Strategy
The fix is elegant because it does not try to solve a problem the kernel cannot reliably observe. The CVE text explicitly says there is no reliable way to know whether a CRTC has unrelated mode changes pending when DSC validation runs. That means the driver should stop guessing. Instead, it should remember the value ofmode_changed from before the point where the CRTC was marked as potentially affected by DSC changes, and restore that earlier value inside pre_validate_dsc().That is a classic kernel fix philosophy: when the code cannot infer the full truth at a later stage, preserve the earlier truth before the state machine gets blurred by intermediate logic. It is not flashy, but it is robust. The patch also has the advantage of being narrowly targeted. Rather than redesigning the display state machine, it simply corrects the point at which one flag is normalized. That is the sort of change stable maintainers prefer because it minimizes regression risk.
Why “remember and restore” works
The restored value acts as a guardrail against overfitting DSC validation to a single concern. DSC validation can still determine whether compression-specific timing changed, but it no longer gets to erase evidence that the CRTC was already participating in a broader mode change. That preserves the distinction between DSC-related effects and unrelated atomic changes, which is exactly the distinction the old code blurred.This sort of fix also illustrates a broader display-driver truth: local correctness is not enough. A helper can be “correct” in isolation and still be wrong in the larger commit sequence. The AMD patch acknowledges that the point of no return had already passed by the time DSC pre-validation ran, so the only safe move was to restore earlier context instead of trusting a narrower recomputation.
- Preserve the pre-existing mode_changed state.
- Do not let DSC validation erase unrelated changes.
- Keep the fix surgical so it backports cleanly.
- Prefer restoring earlier context over late-stage inference.
Why MST and DSC Interact Badly
Multi-Stream Transport and Display Stream Compression are each complex on their own. Together, they create a state space that is much harder to reason about because external display attachment can alter the topology while compression decisions are being recalculated. The bug description’s laptop-panel example is a reminder that internal and external displays are not isolated worlds; one can affect the other through shared policy and shared atomic commit logic.This interaction also exposes a common kernel engineering problem: a helper designed around one subsystem’s invariants can become unsafe when a second subsystem’s assumptions are layered on top. DSC logic wants to know whether timing changed. MST logic wants to know whether the attached display tree changed. The atomic commit framework, meanwhile, needs to preserve both truths and decide whether the overall CRTC state changed. When any one layer oversimplifies, the others inherit the mistake.
Internal panels are not “simple” panels
Integrated panels are often treated as stable, static devices compared with external monitors, but modern laptops make them part of a more dynamic display policy. Features like HDR enablement can depend on whether external displays are present, whether bandwidth is constrained, and how the compositor wants to allocate resources. In that context, it is completely plausible for an internal panel to be logically affected by an external MST event even if its own timing parameters stay the same.That is why the mode flag had to survive DSC pre-validation unchanged unless there was a reliable reason to clear it. The driver was not just managing a compression decision; it was managing the integrity of the full atomic transaction. The patch fixes precisely that boundary.
- MST changes can reshape the display topology.
- DSC validation only sees part of the story.
- Internal panels may be indirectly affected by external attachments.
- Shared state across displays makes naive flag resets dangerous.
Enterprise and Consumer Impact
For consumers, the most likely visible effects are instability, display glitches, or a system crash under the right docking and multi-monitor conditions. A typical single-monitor desktop is less likely to stumble into the vulnerable path. But consumers with laptops, docking stations, and mixed internal/external HDR configurations are exactly the sort of users who could trigger the bug without doing anything obviously unusual.For enterprise users, the stakes are higher because display stacks are often part of a broader operational workflow: hot-desking, conference-room setups, virtualized desktops, engineering workstations, and thin-client environments all depend on predictable graphics state transitions. A leak in the display driver may not sound like a server-class outage, but in practice it can affect device reliability, break user sessions, and trigger crashes that are hard to attribute quickly. In managed fleets, that kind of intermittent issue is expensive.
Docking, hot-plugging, and real-world triggers
The conditions that expose CVE-2026-31488 are not exotic. External display hot-plugging is normal behavior on modern laptops, especially in office environments where DP-MST hubs and USB-C docks are common. The CVE’s example is compelling precisely because it maps onto everyday usage: one monitor is attached, another is removed, and the kernel has to reconcile multiple display changes at once.That is also why the issue matters beyond AMD hardware enthusiasts. Enterprises tend to deploy a mix of hardware profiles, and graphics regressions often show up first in support desks rather than vulnerability scanners. If a patch affects a large enough share of AMD-based laptops or workstations, it quickly becomes a fleet-management concern rather than a niche driver bug.
- Consumer risk is highest on dock-heavy laptops.
- Enterprise risk is highest where hot-plug workflows are common.
- The bug may appear as instability before it appears as a security event.
- Mixed-display policies make the issue easier to trigger in managed environments.
What the Stable Backport Signals
The CVE record shows that the fix was cherry-picked from commit cc7c7121ae082b7b82891baa7280f1ff2608f22b, and Microsoft’s record includes multiple stable references. That is an important signal. It means upstream maintainers considered the issue important enough to be backported without waiting for a future feature release, which is typically a marker of seriousness and reproducibility.Backports also tell us the problem was cleanly understood. Stable maintainers do not usually like patches that depend on speculative behavior or broad redesigns. The fact that this fix was selected suggests that the root cause was narrow enough to isolate and the repair was modest enough to carry into maintained branches. That is usually reassuring for operators because it means the patch can spread without introducing large new behavior changes.
Why stable matters more than headline severity
The NVD entry was still effectively waiting on enrichment at the time of publication, with no final CVSS score provided in the record shown here. That should not be mistaken for low importance. Kernel CVEs often arrive before scoring is finalized, and stable backporting is often a better signal of practical urgency than a placeholder severity label.In other words, the existence of the stable fix is the real operational takeaway. It tells downstream vendors and distro maintainers that the issue is not just a theoretical coding mistake upstream. It is a bug with a known repair path that is already suitable for maintained kernels. That makes patch deployment a straightforward priority for anyone shipping AMD graphics support.
- Stable inclusion suggests the bug was well understood.
- The fix was small enough to backport.
- Placeholder NVD scoring does not reduce the operational need to patch.
- Downstream vendors can ship the correction with low behavioral risk.
Strengths and Opportunities
The strongest aspect of this fix is its restraint. It does not try to teach the validation code a broader theory of everything; it simply restores the previously known state that was present before DSC pre-validation made a narrower judgment. That is usually the best kind of kernel patch: small, precise, and easy to reason about when backporting into long-term branches.There is also a broader opportunity here for display-driver maintainers to examine adjacent transaction paths for the same class of bug. Whenever a helper function mutates shared commit flags after partial analysis, it is worth asking whether it is discarding context it should preserve. The AMD case is a useful reminder that atomic graphics code needs a strong memory of what happened before each sub-analysis ran.
- Narrow fix with low regression risk.
- Clear root cause and clear remediation.
- Good candidate for stable and vendor backports.
- Useful precedent for auditing other atomic display helpers.
- Strengthens confidence in AMD display transaction handling.
- Reinforces the importance of preserving earlier commit context.
- Demonstrates a clean separation between DSC-specific and unrelated mode changes.
Risks and Concerns
The most obvious concern is that this is the kind of bug that can survive testing for a long time. It only appears when a specific combination of display topology changes and unrelated mode changes happen in the same commit. That makes it difficult to reproduce on demand and easy to miss in ordinary QA cycles, especially if test labs do not use MST-heavy docking setups or HDR-sensitive panel policies.A second concern is that memory-safety issues in graphics code can look harmless until they are not. A leak may be dismissed as a cleanup problem, but once the wrong object lifetime reaches a later teardown path, the impact becomes much more severe. The KASAN trace included in the record is a reminder that kernel display bugs can cross from correctness to safety without warning.
Operational risks for fleets
Enterprise fleets may face delayed visibility because the failure can emerge only under certain docking and display-change patterns. That means a device can appear healthy in inventory tools while still harboring the bug. If the system is only intermittently hot-plugged or if users do not regularly move between single and multi-monitor configurations, the issue may remain latent until a real-world support event triggers it.There is also the familiar risk of patch lag. Even when the fix is already in stable branches, downstream vendors and OEMs may take time to absorb it into signed or certified builds. For AMD-based laptops in managed environments, that means the real exposure window is determined less by upstream publication and more by the speed of vendor delivery.
- The bug is hard to reproduce in ordinary QA.
- It can remain hidden until docking and hot-plug conditions line up.
- A leak can become a use-after-free later in the lifecycle.
- Vendor patch latency may keep systems exposed longer than expected.
- Fleet inventory may not reveal which users can actually trigger the path.
- Graphics issues often masquerade as random instability before they are recognized as security-relevant.
Looking Ahead
The key thing to watch now is how quickly downstream Linux distributions and OEM kernels absorb the backport. The fix itself is already clear, but what matters for real-world exposure is which shipping kernel builds contain it. For end users, that usually means paying closer attention to vendor firmware and distro kernel updates than to the raw upstream commit history.It will also be worth watching whether additional AMD display fixes appear in the same area. When one transaction-state bug is uncovered in a subsystem as complex as DRM, it often prompts maintainers to inspect neighboring paths for similar flag-handling mistakes. That does not mean the graphics stack is unstable in general; it means the code is mature enough that the remaining bugs are increasingly about edge-case sequencing rather than broad architectural errors.
Practical things to monitor
- Kernel updates from distro and OEM channels that include the backport.
- Any additional AMD display fixes involving
mode_changedor DSC validation. - Reports from dock-heavy laptop fleets and multi-monitor workstation deployments.
- Regression chatter around external display hot-plug, HDR, or MST topologies.
- Evidence that the same bug was present in vendor-stable graphics branches.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center