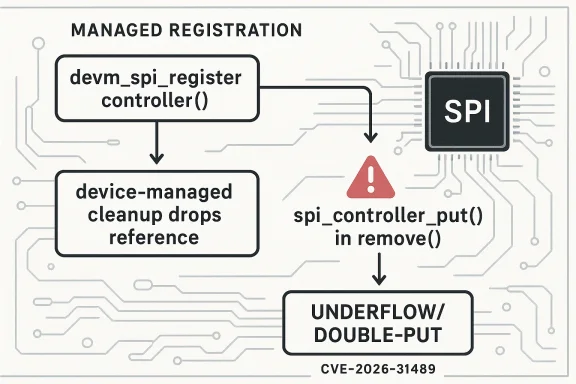
The Linux kernel’s newly published CVE-2026-31489 is a small-looking bug with a very familiar shape: a reference-counting mistake in driver teardown that can become a correctness and stability problem in production. The public description says the meson-spicc SPI controller driver registers itself with
That distinction maernel teardown paths are notoriously fragile. Many drivers were written across multiple eras of kernel APIs, and maintainers have spent years moving them toward devm-managed resource lifetimes. The more the kernel uses managed allocation and registration helpers, the less room there is for manual cleanup to remain in sync. But that migration also creates a subtle risk: a driver that was once correct with manual reference handling can become wrong after a later conversion to a managed helper. The bug in meson-spicc appears to be exactly that kind of drift.
The public CVE text makes the mechanics plain.
In practical terms, the risk profile here is more about reliability, crash potential, and teardown correctness than about remote compromise. That does not make the issue unimportant. Kernel bugs that affect object lifetime can still trigger panics, memory corruption in edge cases, or unpredictable behavior on embedded devices and production appliances. In other words, this is exactly the sort of bug operators hate because it hides in shutdown logic, but can still destabiworst possible moment.
The meson-spicc driver serves Amlogic Meson SoCs, where SPI is commonly used for attached flash, sensors, controllers, and other embedded peripherals. Drivers in this space often evolve across years of incremental kernel changes, and that evolution is where many reference-handling bugs are born. As the kernel migrated more subsystems toward managed resource helpers, driver authors increasingly had to decide whether a resource should be released manually or by framework-owned teardown. That decision is often obvious in hindsight and surprisingly easy to.
Managed registration helpers exist for a reason. They reduce boilerplate, shrink error paths, and make probe failures safer to unwind. But they also create a contract: once a resource is registered via a managed helper, the driver should stop pretending it owns the final release. The devm subsystem keeps track of what must be cleaned up and when. A second explicit release call can therefore be not just redundant but harmful. That is the core of this CVE.
There is also a broader kernel-history angle. The Linux kernel has been steadily converting drivers to devm patterns for years because manual cleanup code is a recurring source of bugs. One reason is that probe and remove paths are easy to reason about in isolation but harder to keep correct once they interact with failure handling, deferred probing, hotplug, and power management. The more helpers that own resources automatically, the fewer places remain where a human has to remember to free something exactly once. That is an enormous quality-of-life improvement, but only if the old manual calls are removed consistently.
The CVE record itself reflects the standard Linux security workflow. The kernel project’s CVE policy notes that CVEs are typically assigned after a fix is available and applied to stable trees, and that the identifier tracks the commit that resolves the bug. That makes the vulnerability record less about dramatic disclosure and more about traceable maintenance. In this case, the record is anchored to stable references, which usually means downstream distributors can pick up the patch with relatively little conceptual risk.
The real issue is not just “too many puts.” It is the broader violation of the lifetime model. Once a managed helper has taken responsibility for teardown, the manual path must step aside. Leaving both paths active invites underflow, use-after-free conditions in other contexts, or at minimum undefined teardown behavior. In kernel code, that is the sort of defect that can remain dormant until a very specific combination of remove and cleanup events occurs.
This kind of fix is usually prized by stable maintainers because it is narrow and easy to reason about. It does not alter SPI protocol semantics, transfer scheduling, or controller behavior. It only corrects the teardown bookkeeping. That makes it much less likely to introduce regressions than a broader refactor would. In kernel maintenance terms, that is the sweet spot: fix the lifecycle bug, preserve everything else.
That distinction is subtle enough that it often survives code review. A driver author may see a lingering `spi_controe it is still necessary from the earlier manual-registration era. But once the registration call changes, the cleanup call must change too. CVE-2026-31489 is a good example of why resource ownership audits matter whenever kernel code is modernized.
It is also worth noting that cleanup bugs are often more dangerous than their line count suggests. A device removal path may be infrequently used during normal operation, but it is essential during upgrades, suspend/resume cycles, hotplug events, module reloads, and failure recovery. That means the bug can remain invisible in simple “it boots and runs” validation while still being quite real in the field.
Embedded Linux also tends to use SPI heavily. Flash chips, display controllers, power-management components, and board-specific peripherals are all frequently attached via SPI. That means the SPI controller driver is part of a fairly central hardware path, not some obscure optional subsystem. A bug in the controller’s lifecycle can therefore have outsized consequences compared with its short commit message.
There is another wrinkle: vendor kernels often lag upstream. Even when the fix is accepted quickly into stable branches, downstream appliances may ship older trees or delayed backports. That means the real exposure window is often determined less by upstream patching than by the vendor’s maintenance cadence. This is a recurring reality for kernel CVEs, and one reason why stable references matter so much.
The broader lesson is that kernel hardening is often about consistency more than complexity. Once a subsystem adopts managed registration, every related remove path needs to be audited for residual manual teardown. Otherwise the kernel ends up with mixed models, and mixed models are where reference bugs live.
Stable backports are especially important here because the fix is compact. There is no broad driver redesign, no new interface, and no behavior change outside teardown. That makes the patch suitable for supported branches where maintainers are trying to minimize regression risk. For downstream vendors, this is the ideal kind of kernel security fix: simple to cherry-pick, easy to verify, and low-risk to deploy.
That matters for patch triage. Security teams often rank vulnerabilities based on exploitability, but lifecycle bugs deserve attention because they can cause outages that are operationally equivalent to an attack. A kernel panic during a driver unload might not be a classic “exploit,” but the end result for a service owner can be the same: downtime, recovery work, and possible data loss.
That pattern is why code review alone is not enough. Automated analysis, testing under hotplug and module churn, and careful subsystem-specific auditing are all needed to keep these bugs out of supported releases. The existence of this CVE is less a sign of failure than a reminder that object of the kernel’s hardest problems.
It also strengthens the case for managed-resource adoption across kernel subsystems. The more drivers move to devm helpers, the more the kernel can standardize teardown behavior and reduce one-off cleanup mistakes. That does not eliminate bugs, but it narrows the surface where they can occur. The downside is that any leftover manual cleanup becomes more conspicuous—and more dangerous.
Platform vendors also care because SPI controllers often sit on core board-support-package paths. A teardown bug can therefore show up as a boot-to-shutdown reliability issue rather than an obvious runtime crash. That makes it easy for a quality team to miss in broad testing and hard for customers to debug later. These are the kinds of bugs that generate support load long after the original code change has faded from memory.
That is especially true when the update lands in a driver that participates in board initialization or peripheral control. If the driver controls flash, sensors, or other critical SPI-attached hardware, a teardown error can undermine the reliability of the entire platform. Enterprises tend to discover that sort of problem only after a maintenance window, which is exactly when they least want surprises.
It also gives downstream teams a chance to test whether their board-supplated similar inconsistencies. Often, the exact bug is less important than the pattern it exposes. If one manual put slipped through after a managed-registration conversion, there may be others in neighboring drivers or older vendor forks.
Another concern is patch lag. Upstream and stable fixes are one thing; deployed reality is another. Many customers do not run raw upstream kernels, and vendor backports can lag by weeks or months. If a device family ships a kernel with this exact remove-path bug, the exposure may continue quietly even after the CVE is public.
A second risk is that the bug may be hidden in vendor derivatives rather than obvious mainline code. Embedded ecosystems often carry local patches, and those patches can obscure whether the device-managed cleanup model is actually being used everywhere it should be. That makes asset inventory and kernel provenance tracking more important than usual.
It will also be worth watching whether this CVE prompts a wider cleanup sweep across other SPI drivers. Whenever maintainers find a manual release left behind after a devm conversion, the obvious follow-up is to check for the same mistake elsewhere. That kind of audit is one of the healthiest outcomes of kernel vulnerability work, because it turnto a subsystem-wide quality improvement.
CVE-2026-31489 is not the sort of kernel flaw that headlines dramatic exploitation, but it is exactly the kind of bug that separates robust platforms from fragile ones. When ownership rules are wrong, shutdown becomes uncertain, and uncertainty in kernel teardown is never benign. The fix is small, the lesson is large, and the broader message is clear: in the Linux kernel, lifecycle bugs are security bugs when they threaten the stability of the systems people depend on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
devm_spi_register_controller, which means the device-managed cleanup path already drops the controller reference; calling spi_controller_put again in meson_spicc_remove creates a double-put scenario. That is exactly the kind of lifecycle bug that can sit quietly for years and then surface only when systems unload, reprobe, suspend, or otherwise churn devices. 26-31489 sits in a class of kernel defects that often look mundane at first glance but matter a great deal in the real world. The issue is not a flashy memory corruption primitive or an obvious remote exploit chain. Instead, it is about ownership semantics: who is responsible for releasing an object, and whether that responsibility has already been transferred to a managed cleanup framework. In this case, the kernel record says the answer is “yes, the managed path already owns teardown,” which makes the extra spi_controller_put call wrong by construction.That distinction maernel teardown paths are notoriously fragile. Many drivers were written across multiple eras of kernel APIs, and maintainers have spent years moving them toward devm-managed resource lifetimes. The more the kernel uses managed allocation and registration helpers, the less room there is for manual cleanup to remain in sync. But that migration also creates a subtle risk: a driver that was once correct with manual reference handling can become wrong after a later conversion to a managed helper. The bug in meson-spicc appears to be exactly that kind of drift.
The public CVE text makes the mechanics plain.
meson_spicc_probe registers the SPI controller using devm_spi_register_controller, and the teardown path in meson_spicc_remove still performs an explicit spi_controller_put. In managed-resource terms, that is double accounting. The cleanup system will already release the controller when the device goes away, so a second put can underflow the reference count, or at minimum put the object into an invalid lifecycle state. That is why the fix is described so narrowly: remove the extra manual put and let the devm framework do its also worth noting. The CVE record was published on April 22, 2026, and the NVD entry notes references to multiple stable kernel commits, suggesting the issue was already propagated through the Linux security workflow rather than being an isolated upstream curiosity. The Linux kernel documentation explains that CVEs are routinely assigned to fixes that have already landed in stable trees, which is why many kernel CVEs read like disciplined bug-fix records rather than standalone vulnerability narratives.In practical terms, the risk profile here is more about reliability, crash potential, and teardown correctness than about remote compromise. That does not make the issue unimportant. Kernel bugs that affect object lifetime can still trigger panics, memory corruption in edge cases, or unpredictable behavior on embedded devices and production appliances. In other words, this is exactly the sort of bug operators hate because it hides in shutdown logic, but can still destabiworst possible moment.
 Background
Background
The meson-spicc driver serves Amlogic Meson SoCs, where SPI is commonly used for attached flash, sensors, controllers, and other embedded peripherals. Drivers in this space often evolve across years of incremental kernel changes, and that evolution is where many reference-handling bugs are born. As the kernel migrated more subsystems toward managed resource helpers, driver authors increasingly had to decide whether a resource should be released manually or by framework-owned teardown. That decision is often obvious in hindsight and surprisingly easy to.Managed registration helpers exist for a reason. They reduce boilerplate, shrink error paths, and make probe failures safer to unwind. But they also create a contract: once a resource is registered via a managed helper, the driver should stop pretending it owns the final release. The devm subsystem keeps track of what must be cleaned up and when. A second explicit release call can therefore be not just redundant but harmful. That is the core of this CVE.
There is also a broader kernel-history angle. The Linux kernel has been steadily converting drivers to devm patterns for years because manual cleanup code is a recurring source of bugs. One reason is that probe and remove paths are easy to reason about in isolation but harder to keep correct once they interact with failure handling, deferred probing, hotplug, and power management. The more helpers that own resources automatically, the fewer places remain where a human has to remember to free something exactly once. That is an enormous quality-of-life improvement, but only if the old manual calls are removed consistently.
The CVE record itself reflects the standard Linux security workflow. The kernel project’s CVE policy notes that CVEs are typically assigned after a fix is available and applied to stable trees, and that the identifier tracks the commit that resolves the bug. That makes the vulnerability record less about dramatic disclosure and more about traceable maintenance. In this case, the record is anchored to stable references, which usually means downstream distributors can pick up the patch with relatively little conceptual risk.
Why double-put bugs are dangerous
Reference-count bugs in the kernel are tricky because they do not always fail immediately. A double-put may look harmless in a small test, especially if the object survives long enough that no obvious crash appears. But teardown races are exactly where latent bugs become visible. If a controller’s final put happens twice, the resulting state can depend on timing, prioether other paths still hold references. That is why a bug like this is treated seriously even when the public description is concise.The real issue is not just “too many puts.” It is the broader violation of the lifetime model. Once a managed helper has taken responsibility for teardown, the manual path must step aside. Leaving both paths active invites underflow, use-after-free conditions in other contexts, or at minimum undefined teardown behavior. In kernel code, that is the sort of defect that can remain dormant until a very specific combination of remove and cleanup events occurs.
What the Vulnerability Changes
The public description suggests a very small code change with a disproportionately important effect: stop manually putting the controller inmeson_spicc_remove. That is the correct fix because the controller is already registered w The managed framework will release it during device cleanup, so the driver should not do that work twice. The practical effect is to realign code with ownership.This kind of fix is usually prized by stable maintainers because it is narrow and easy to reason about. It does not alter SPI protocol semantics, transfer scheduling, or controller behavior. It only corrects the teardown bookkeeping. That makes it much less likely to introduce regressions than a broader refactor would. In kernel maintenance terms, that is the sweet spot: fix the lifecycle bug, preserve everything else.
Managed teardown versus manual teardown
A managed helper likedevm_spi_register_controller says, in effect, “the device framework will own cleanup for this object.” That changes the driver’s obligations. The remove path can still perform hardware-specific shutdown, but it should not redundantly free objects the framework already owns. The same principle applies across the devm family: once the framework has attached a resource to a device, manual finalization becomes a liability unless explicitly required by the API.That distinction is subtle enough that it often survives code review. A driver author may see a lingering `spi_controe it is still necessary from the earlier manual-registration era. But once the registration call changes, the cleanup call must change too. CVE-2026-31489 is a good example of why resource ownership audits matter whenever kernel code is modernized.
What could happen in practice
The public record does not spell out a dramatic exploit scenario, and that is important. We should not overstate the case. The most likely consequences are stability issues, teardown-time faultsior on affected systems, especially those that exercise remove/reprobe paths regularly. On embedded boards, industrial appliances, or test environments that reload drivers often, that can still become operationally significant.It is also worth noting that cleanup bugs are often more dangerous than their line count suggests. A device removal path may be infrequently used during normal operation, but it is essential during upgrades, suspend/resume cycles, hotplug events, module reloads, and failure recovery. That means the bug can remain invisible in simple “it boots and runs” validation while still being quite real in the field.
Why This Matters for Embedded Linux
The Amlogic Meson family is widely associated with embedded and consumer hardware, which changes the importance of a bug like this. Desktop users may never notice it. Embedr, often depend on long-lived kernels, vendor trees, and custom device stacks where a small driver bug can persist for years. In those environments, a teardown problem is not theoretical; it can affect device resets, upgrades, and firmware refresh cycles.Embedded Linux also tends to use SPI heavily. Flash chips, display controllers, power-management components, and board-specific peripherals are all frequently attached via SPI. That means the SPI controller driver is part of a fairly central hardware path, not some obscure optional subsystem. A bug in the controller’s lifecycle can therefore have outsized consequences compared with its short commit message.
Consumer devices versus industrial systems
For consumers, the practical effect may be limited to a subset of devices and a narrower set of triggers. A home appliance or set-top box may never exercise the remove path in e flaw. But industrial and enterprise embedded systems are different. They may routinely reload drivers during updates, and they may be expected to survive hotplug or failover scenarios without a reboot. That is where a double-put bug becomes much more than a code review footnote.There is another wrinkle: vendor kernels often lag upstream. Even when the fix is accepted quickly into stable branches, downstream appliances may ship older trees or delayed backports. That means the real exposure window is often determined less by upstream patching than by the vendor’s maintenance cadence. This is a recurring reality for kernel CVEs, and one reason why stable references matter so much.
Why managed APIs help, but only if used consistently
Managed APIs are one of the Linux kernel’s best defenses against lifetime bugs, but they are not self-enforcing. They rely on developers removing obsolete manual cleanup calls everywhere they matter. If one strayput survives a transition to devm, the code may look correct on casual inspection while still violating the ownership model. That is precisely the sort of mismatch that security teams and maintainers need to hunt down systematically. ([d://docs.kernel.org/process/cve.html)The broader lesson is that kernel hardening is often about consistency more than complexity. Once a subsystem adopts managed registration, every related remove path needs to be audited for residual manual teardown. Otherwise the kernel ends up with mixed models, and mixed models are where reference bugs live.
Stable Backporting and Patch Hygiene
One of the strongest signs that this CVE is being handled as a serious kernel maintenance issue is the presence of multiple stable references. The Linux kernel security process is built around fixing bugs in stable trees after the fix exists upstream, and then using the CVE identifier to tie the advisory to a specific commit lineage. That is exactly the kind of traceability defenders want when deciding whether a distro or appliance build is covered.Stable backports are especially important here because the fix is compact. There is no broad driver redesign, no new interface, and no behavior change outside teardown. That makes the patch suitable for supported branches where maintainers are trying to minimize regression risk. For downstream vendors, this is the ideal kind of kernel security fix: simple to cherry-pick, easy to verify, and low-risk to deploy.
Why small fixes still deserve attention
It is tempting to dismiss a double-put bug as “just cleanup,” but that is a mistake. In kernel code, cleanup is part of the control plane. If teardown is wrong, then probes, reloads, and shutdowns all become less reliable. The bug may not show up during a normal workload, yet still destabilize a system exactly when the operator expects the machine to be quiet and safe.That matters for patch triage. Security teams often rank vulnerabilities based on exploitability, but lifecycle bugs deserve attention because they can cause outages that are operationally equivalent to an attack. A kernel panic during a driver unload might not be a classic “exploit,” but the end result for a service owner can be the same: downtime, recovery work, and possible data loss.
A familiar pattern in kernel security
This CVE fits a broader pattern we see repeatedly in Linux: a helper API changes the ownership model, and a stale manual call lingers behind. The code is not malicious, and it may even look tidy in isolation, but the underlying abstraction has shifted. When that happens, bugs tend to cluster around rems, and rollback logic. Those are the places where the kernel’s discipline is tested most severely.That pattern is why code review alone is not enough. Automated analysis, testing under hotplug and module churn, and careful subsystem-specific auditing are all needed to keep these bugs out of supported releases. The existence of this CVE is less a sign of failure than a reminder that object of the kernel’s hardest problems.
Competitive and Ecosystem Implications
Although this is a Linux kernel issue, it matters across the broader ecosystem because many products ship Linux under the hood. Consumer electronics vendors, industrial-controller makers, and embedded platform suppliers all depend on kernel maintenance quality. A bug like this can therefore affect the reputation of an entire hardware family if it causes instability in field devices or makes teardown behavior unreliable.It also strengthens the case for managed-resource adoption across kernel subsystems. The more drivers move to devm helpers, the more the kernel can standardize teardown behavior and reduce one-off cleanup mistakes. That does not eliminate bugs, but it narrows the surface where they can occur. The downside is that any leftover manual cleanup becomes more conspicuous—and more dangerous.
What rivals and vendors will care about
Vendors that maintain downstream kernels will care about how cleanly the fix backports. If the patch is truly just the removal of an obsoletespi_controller_put, the update should be straightforward. If there are surrounding dependencies or older trees with different probe/remove semantics, then the vendor has to test more carhis is the sort of fix that rewards disciplined backporting and punishes guesswork.Platform vendors also care because SPI controllers often sit on core board-support-package paths. A teardown bug can therefore show up as a boot-to-shutdown reliability issue rather than an obvious runtime crash. That makes it easy for a quality team to miss in broad testing and hard for customers to debug later. These are the kinds of bugs that generate support load long after the original code change has faded from memory.
The enterprise angle
For enterprises, the main issue is not whether the CVE sounds dramatic. It is whether the affected kernel is in a fleet of appliances, edge devices, or specialized boards that may not get patched on the same schedule as mainstream servers. In those environments, even a narrow teardown bug can create a surprisingly largeThe safest assumption is that any kernel update involving reference-count fixes deserves standard validation before being rolled into production.That is especially true when the update lands in a driver that participates in board initialization or peripheral control. If the driver controls flash, sensors, or other critical SPI-attached hardware, a teardown error can undermine the reliability of the entire platform. Enterprises tend to discover that sort of problem only after a maintenance window, which is exactly when they least want surprises.
Strengths and Opportunities
The good news is that this is the kind of kernel issue that is usually fixable with a very small patch and a very clear ownership model. It is also a useful reminder that managed helpers are doing exactly what they are supposed to do—provided the legacy manual cleanup is removed at the same time. The presence of stable references suggests the fix is already moving through the normal maintenance pipeline, which should help downstream adopters.- The fix is surgical and unlikely to alter normal SPI behavior.
- The bug is easy to understand once the devm ownership model is recognized.
- Backporting should be relatively straightforward for stable branches.
- The issue reinforces the value of managed cleanup in kernel drivers.
- The CVE helps operators audit other drivers for leftover manual puts.
- It is a good candidate for automated lifetime and teardown testing.
- The patch should be low-risk for vendors shipping embedded Linux.
Why this is an opportunity, not just a bug
The larger opportunity is process improvemens gives maintainers another concrete example of where a subsystem has not fully shed its older manual cleanup habits. That can drive broader audits, more consistent devm conversions, and better static analysis rules for reference counting. In a mature kernel, those incremental improvements matter a lot.It also gives downstream teams a chance to test whether their board-supplated similar inconsistencies. Often, the exact bug is less important than the pattern it exposes. If one manual put slipped through after a managed-registration conversion, there may be others in neighboring drivers or older vendor forks.
Risks and Concerns
The main concern is that a bug like this can be underestimated because it does not read like a classic exploit. That is dangerous thinking. Kernel reference-count mistakes can become crashes, memory corruption, or unpredictable teardown behavior, and even when they do not lead to code execution, they can still take down important devices. In embedded and industrial settings, that is a real security and availability problem.Another concern is patch lag. Upstream and stable fixes are one thing; deployed reality is another. Many customers do not run raw upstream kernels, and vendor backports can lag by weeks or months. If a device family ships a kernel with this exact remove-path bug, the exposure may continue quietly even after the CVE is public.
- Teams may dismiss the issue as “just a teardown bug.”
- Older vendor kernels may retain the flaw longer than upstream trees.
- Similar lifecycle mistakes may exist in nearby SPI drivers.
- Cleanup-path crashes are often missed in routine testing.
- Embedded fleets may not have easy visibility into kernel versions.
- Device churn and hotplug can make the bug harder to reproduce.
- Mixed manual and managed teardown models invite future regressions.
Why teardown bugs are so slippery
Teardown paths usually get less test coverage thse systems spend more time starting than stopping during everyday validation. But in the field, shutdown and reprobe events are common. Power cycling, maintenance upgrades, and recovery from peripheral faults all drive driver removal logic, which is exactly where this vulnerability sits. That asymmetry makes lifecycle bugs frustratingly persistent.A second risk is that the bug may be hidden in vendor derivatives rather than obvious mainline code. Embedded ecosystems often carry local patches, and those patches can obscure whether the device-managed cleanup model is actually being used everywhere it should be. That makes asset inventory and kernel provenance tracking more important than usual.
Looking Ahead
The next thing to watch is how quickly downstream vendors fold the fix into supported releases. Because the patch appears to be compact and directly tied to a clear ownership mistake, it should move cleanly through stable trees and into distro kernels. The real question is not whether the fix exists upstream; it is whether every ship that uses meson-spicc actually gets the updated build.It will also be worth watching whether this CVE prompts a wider cleanup sweep across other SPI drivers. Whenever maintainers find a manual release left behind after a devm conversion, the obvious follow-up is to check for the same mistake elsewhere. That kind of audit is one of the healthiest outcomes of kernel vulnerability work, because it turnto a subsystem-wide quality improvement.
Items to monitor
- Stable backports across supported Linux branches.
- Vendor BSP updates for Amlogic-based devices.
- Any follow-on cleanup patches in SPI controller drivers.
- Reports of remove/reprobe instability on affected hardware.
- Distribution advisories that map the CVE to kernel package versions.
CVE-2026-31489 is not the sort of kernel flaw that headlines dramatic exploitation, but it is exactly the kind of bug that separates robust platforms from fragile ones. When ownership rules are wrong, shutdown becomes uncertain, and uncertainty in kernel teardown is never benign. The fix is small, the lesson is large, and the broader message is clear: in the Linux kernel, lifecycle bugs are security bugs when they threaten the stability of the systems people depend on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center