CVE-2026-31686 is a small Linux kernel memory-management fix with outsized operational relevance for anyone running POWER, persistent memory, or security-instrumented kernels in enterprise environments. The issue sits in KASAN page-table teardown logic, where an incorrect assumption about page-table alignment can lead to a double free during PMEM unmapping. Although the public record is still awaiting full NVD enrichment and has no NVD CVSS score yet, the stable-kernel backports show that maintainers considered the fix important enough to carry across multiple supported kernel lines.
The Linux kernel has spent the past decade expanding its defensive debugging infrastructure, and Kernel Address Sanitizer is one of the most important parts of that effort. KASAN instruments kernel memory accesses and tracks poisoned or freed regions so developers can catch use-after-free, out-of-bounds, and double-free bugs before they become production incidents. It is not merely a developer convenience; it has become part of how complex kernel subsystems are validated across architectures.
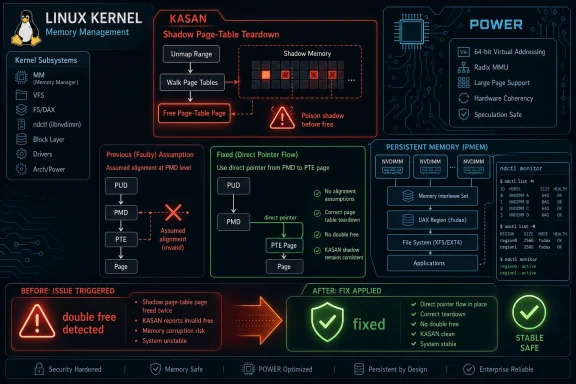
CVE-2026-31686 concerns the kernel’s
The reported failure path involved PowerPC with 64K pages, where a PUD table of 4096 bytes can come from a slab cache rather than mapping cleanly to the expected page-aligned object. In the observed case, PMEM operations through
Historically, kernel security teams have had to balance portability with performance in the memory-management layer. The page-table hierarchy is already architecture-sensitive, and KASAN adds another translation layer through shadow memory. CVE-2026-31686 is a reminder that debugging infrastructure is still kernel code, and kernel code inherits all the sharp edges of architecture-specific memory allocation.
The affected functions live in KASAN initialization and teardown code, not in a network stack, browser-facing parser, or typical remote attack surface. That matters for prioritization. This looks like a local kernel correctness and stability issue first, with security relevance because double frees are a classic memory-corruption class.
The public crash trace shows the failure during PMEM namespace teardown, with
Key technical elements include:
The significance of CVE-2026-31686 is therefore not limited to machines booted with sanitizer instrumentation. The bug highlights a mismatch between generic memory-management assumptions and architecture-specific page-table allocation. If the assumption is wrong under KASAN, maintainers must ask whether adjacent code paths make similar assumptions elsewhere.
There is also a subtle trust issue. Security teams rely on sanitizers to tell them when memory state is unsafe, so the sanitizer’s own bookkeeping must be especially robust. A crash in KASAN support code can obscure the original workload being tested and slow down root-cause analysis.
For WindowsForum readers, the Windows connection is indirect but real. Microsoft’s security ecosystem increasingly surfaces third-party and open-source CVEs through vulnerability-management portals, Defender exposure views, Azure workloads, and hybrid fleet inventories. A Linux kernel CVE appearing in Microsoft-facing security workflows does not mean Windows itself is vulnerable, but it does mean administrators may see Linux exposure inside Microsoft tooling.
Practical takeaways for security teams include:
The bug appears when page-table structures do not match the alignment model assumed by the KASAN freeing path. With 64K pages, a 4096-byte PUD table can be served by a slab cache named for page-table objects rather than by a simple page-aligned allocation. When the cleanup code derives the object address incorrectly, it can attempt to free the same slab-backed object twice.
Persistent memory adds another important dimension. PMEM and DAX-style deployments blur the line between storage and memory, allowing applications or filesystems to map durable media into address spaces with fewer traditional block-layer boundaries. That gives administrators performance and latency benefits, but it also exercises kernel memory-remapping paths that ordinary storage may never touch.
This matters for enterprise Linux support teams because the affected scenario is operationally plausible. A storage administrator using
A reasonable exposure checklist should include:
That distinction is crucial when the object was allocated from a slab cache. Slab allocators manage objects that may be smaller than a full page, grouped within compound pages, or represented in ways that do not preserve the assumptions made by page-level conversion helpers. A page-table object is not always interchangeable with the page that contains it.
The fix also clears the upper-level page-table entry after freeing, preserving the intended teardown sequence. In other words, the patch does not redesign KASAN shadow-memory management. It narrows the free operation to the correct allocation identity.
That makes the fix attractive for stable backporting. It is low complexity, localized, and tied to a reproducible crash. The danger of the old behavior is serious enough to fix, while the risk of the new behavior appears limited because the start pointer is already available and intended for exactly that level of page-table teardown.
A simplified sequence looks like this:
The lack of a CVSS score should push teams toward context-based triage. A double free in kernel memory management is a serious bug class, but this specific report is constrained by architecture, configuration, and trigger path. It is not currently presented as a remotely exploitable flaw, and the public information points to a reliability and correctness fix around PMEM teardown.
That said, kernel memory bugs often receive CVEs because they can represent security boundaries under the right circumstances. Local actors with access to device management interfaces, privileged namespace operations, or test infrastructure may be able to trigger crash conditions. Whether that rises to practical privilege escalation depends on details not established in the public record.
The safest phrasing is that CVE-2026-31686 is a kernel double-free vulnerability resolved by upstream stable patches, with exploitation characteristics still not fully characterized by NVD. Enterprises should patch where applicable, but they should not treat this as a broad internet-facing emergency.
Triage teams should classify it using these factors:
For traditional Windows desktop administrators, CVE-2026-31686 should not be read as a Windows kernel defect. It does not describe
For WSL users, the answer is more nuanced. WSL2 uses a Microsoft-provided Linux kernel, but exposure would depend on whether that kernel includes the affected code path, whether KASAN is enabled, and whether relevant PMEM-style operations are even possible in the environment. Typical consumer WSL2 usage is unlikely to resemble the POWER PMEM scenario described in the report.
For Azure and hybrid infrastructure teams, the story is broader. Linux VMs, specialized HPC deployments, SAP-on-Linux environments, and IBM POWER-adjacent estates may be tracked alongside Windows Server assets. If a scanner flags CVE-2026-31686, the next step is not to patch Windows; it is to identify the Linux kernel package, architecture, and vendor advisory chain.
Recommended workflow for Microsoft-centric teams:
Enterprise teams should take it more seriously, but still with precision. Large organizations often maintain validation kernels, hardware enablement labs, specialized database servers, and unusual architecture mixes. Those are exactly the places where a narrow kernel memory bug can waste engineering time or disrupt maintenance.
The most exposed groups are likely distribution maintainers, hardware vendors, cloud platform teams, QA labs, and administrators of POWER systems with PMEM. Their concern is less about a mass exploit wave and more about stability, correctness, and confidence in memory-management behavior. When a teardown path can double-free a page-table object, the fix belongs in the next safe maintenance window.
Consumers should:
In this case, the public patch history makes the issue understandable. The code changed in one file, the reproducer involved PMEM namespace manipulation, and the affected assumption was clearly described. That level of transparency is a competitive strength for Linux in enterprise environments, especially where customers demand root-cause detail.
Windows follows a more centralized disclosure model. Microsoft can deliver a cleaner administrative experience through Patch Tuesday, Windows Update, and the Security Update Guide, but external open-source components still complicate that model. Hybrid environments now blend both worlds: Linux transparency and Microsoft dashboarding.
For rivals in the server market, the incident reinforces a persistent theme. Architecture diversity is powerful, but it raises the burden on kernel correctness. x86 dominates many commodity workloads, yet POWER, ARM64, RISC-V, and mainframe architectures keep exposing assumptions that generic code might otherwise hide.
Market implications include:
Administrators should avoid making remediation decisions from the CVE page alone. A scanner may flag a kernel version range, but your distribution may already have backported the fix without changing the upstream version number in an obvious way. That is common in enterprise Linux, where package changelogs matter more than headline kernel numbers.
For custom-kernel shops, the patch is a straightforward candidate for cherry-picking, but only after confirming the surrounding KASAN code matches the targeted branch. Memory-management patches are not the place for casual manual edits. Even small changes deserve a full boot, PMEM, and architecture-specific regression pass.
A practical remediation sequence is:
Linux distribution advisories are equally important. Enterprise teams should watch Red Hat, SUSE, Ubuntu, Debian, Oracle, IBM, and other relevant vendors for package-specific backports. In many environments, the visible kernel version will not tell the whole story because distributions routinely carry fixes behind stable package revisions.
Watch these items over the next release cycle:
CVE-2026-31686 is a reminder that modern infrastructure security often depends on obscure-looking fixes in deep kernel code. For most users, it will arrive quietly through routine Linux updates; for POWER, PMEM, and validation-kernel operators, it deserves a deliberate check. The best response is measured but not passive: identify the systems that match the risk profile, confirm the vendor fix, and use the incident to strengthen cross-platform vulnerability triage before the next specialized kernel CVE lands in a general-purpose security dashboard.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux kernel has spent the past decade expanding its defensive debugging infrastructure, and Kernel Address Sanitizer is one of the most important parts of that effort. KASAN instruments kernel memory accesses and tracks poisoned or freed regions so developers can catch use-after-free, out-of-bounds, and double-free bugs before they become production incidents. It is not merely a developer convenience; it has become part of how complex kernel subsystems are validated across architectures.CVE-2026-31686 concerns the kernel’s
mm/kasan code, specifically the logic used when KASAN removes shadow mappings for page-table structures. The vulnerable behavior appears when kasan_free_pxd() assumes that a page-table object is always aligned like a full struct page. That assumption is convenient, but it is not universally true across all architectures and page-size configurations.The reported failure path involved PowerPC with 64K pages, where a PUD table of 4096 bytes can come from a slab cache rather than mapping cleanly to the expected page-aligned object. In the observed case, PMEM operations through
ndctl triggered kasan_remove_zero_shadow(), and KASAN itself reported a double free in the page-table teardown path. That makes this bug especially interesting: the detector found a bug in the surrounding machinery used to manage its own shadow mappings.Historically, kernel security teams have had to balance portability with performance in the memory-management layer. The page-table hierarchy is already architecture-sensitive, and KASAN adds another translation layer through shadow memory. CVE-2026-31686 is a reminder that debugging infrastructure is still kernel code, and kernel code inherits all the sharp edges of architecture-specific memory allocation.
What CVE-2026-31686 Actually Fixes
A bad assumption in page-table freeing
At the center of the fix is a deceptively simple change: instead of deriving the page-table address throughpage_to_virt(pxd_page()), the patched code directly passes the start address of the page-table level that was already supplied as the first argument. That change applies across the PTE, PMD, PUD, and P4D freeing helpers. In practical terms, the kernel stops recalculating an address through a path that may be wrong for slab-backed page-table allocations.The affected functions live in KASAN initialization and teardown code, not in a network stack, browser-facing parser, or typical remote attack surface. That matters for prioritization. This looks like a local kernel correctness and stability issue first, with security relevance because double frees are a classic memory-corruption class.
The public crash trace shows the failure during PMEM namespace teardown, with
ndctl involved in the workflow. That means the bug is not just theoretical code hygiene. It was reproduced under a concrete storage-management sequence involving persistent memory and the kernel’s memory-remapping paths.Key technical elements include:
- Subsystem: Linux kernel memory management and KASAN.
- Failure type: double free in shadow page-table removal.
- Observed trigger: PMEM namespace create-and-destroy workflow.
- Notable architecture: PowerPC with 64K page size.
- Fix style: pass the known page-table start pointer directly.
- Operational impact: kernel warning, taint, and possible instability in affected test or deployment configurations.
Why KASAN Matters Beyond Debug Kernels
Sanitizers are part of the security supply chain
KASAN is often described as a development-time bug detector, but that undersells its role in modern kernel assurance. Large vendors, cloud providers, silicon companies, and distribution maintainers routinely use sanitizer-enabled builds to stress-test kernel code before shipping updates. When KASAN finds a double free, the result often becomes a stable-kernel fix even if most production kernels do not enable KASAN.The significance of CVE-2026-31686 is therefore not limited to machines booted with sanitizer instrumentation. The bug highlights a mismatch between generic memory-management assumptions and architecture-specific page-table allocation. If the assumption is wrong under KASAN, maintainers must ask whether adjacent code paths make similar assumptions elsewhere.
There is also a subtle trust issue. Security teams rely on sanitizers to tell them when memory state is unsafe, so the sanitizer’s own bookkeeping must be especially robust. A crash in KASAN support code can obscure the original workload being tested and slow down root-cause analysis.
For WindowsForum readers, the Windows connection is indirect but real. Microsoft’s security ecosystem increasingly surfaces third-party and open-source CVEs through vulnerability-management portals, Defender exposure views, Azure workloads, and hybrid fleet inventories. A Linux kernel CVE appearing in Microsoft-facing security workflows does not mean Windows itself is vulnerable, but it does mean administrators may see Linux exposure inside Microsoft tooling.
Practical takeaways for security teams include:
- Do not dismiss sanitizer CVEs as irrelevant just because KASAN is often disabled in production.
- Check vendor kernels, not only upstream mainline branches.
- Treat architecture qualifiers seriously, especially on non-x86 fleets.
- Separate Windows exposure from Linux guest exposure in dashboards.
- Watch for false urgency when automated tools show a CVE without full scoring.
- Document PMEM and DAX usage, because storage topology can determine exposure.
The POWER and PMEM Angle
A specialized bug with enterprise consequences
The crash report specifically mentions IBM POWER10-class hardware, PowerPC radix MMU behavior, and persistent-memory operations. That combination will not describe the average laptop, gaming desktop, or even most commodity servers. Yet in enterprise computing, specialized does not mean obscure; POWER systems often sit under databases, analytics platforms, and high-value workloads.The bug appears when page-table structures do not match the alignment model assumed by the KASAN freeing path. With 64K pages, a 4096-byte PUD table can be served by a slab cache named for page-table objects rather than by a simple page-aligned allocation. When the cleanup code derives the object address incorrectly, it can attempt to free the same slab-backed object twice.
Persistent memory adds another important dimension. PMEM and DAX-style deployments blur the line between storage and memory, allowing applications or filesystems to map durable media into address spaces with fewer traditional block-layer boundaries. That gives administrators performance and latency benefits, but it also exercises kernel memory-remapping paths that ordinary storage may never touch.
This matters for enterprise Linux support teams because the affected scenario is operationally plausible. A storage administrator using
ndctl to create and destroy namespaces during maintenance, testing, or provisioning could hit a KASAN double-free report on an affected debug or validation kernel. In a production kernel without KASAN, the exact symptom may differ, but the underlying address-assumption bug still deserves correction.A reasonable exposure checklist should include:
- POWER or PowerPC systems using 64K page configurations.
- PMEM namespaces managed with
ndctl. - DAX or devmap workloads that exercise memory hotplug and remap paths.
- KASAN-enabled validation kernels used by engineering or QA teams.
- Long-term stable kernels that recently received the backport.
- Distribution kernels that carry architecture-specific memory-management changes.
How the Patch Changes the Risk Profile
Small diff, large semantic correction
The patch is compact: it replaces address reconstruction with the pointer already known to represent the start of the page-table object. That is an important semantic shift. Instead of asking, “What virtual address corresponds to the page represented by this page-table entry?” the code now says, “Free the exact page-table object we were passed.”That distinction is crucial when the object was allocated from a slab cache. Slab allocators manage objects that may be smaller than a full page, grouped within compound pages, or represented in ways that do not preserve the assumptions made by page-level conversion helpers. A page-table object is not always interchangeable with the page that contains it.
The fix also clears the upper-level page-table entry after freeing, preserving the intended teardown sequence. In other words, the patch does not redesign KASAN shadow-memory management. It narrows the free operation to the correct allocation identity.
That makes the fix attractive for stable backporting. It is low complexity, localized, and tied to a reproducible crash. The danger of the old behavior is serious enough to fix, while the risk of the new behavior appears limited because the start pointer is already available and intended for exactly that level of page-table teardown.
A simplified sequence looks like this:
- A PMEM mapping causes KASAN shadow page tables to be established.
- Namespace removal or device unbinding triggers shadow mapping teardown.
- The old code calculates a free address through page-level conversion.
- On affected configurations, that calculated address can identify the wrong allocation boundary.
- KASAN detects a double free when the slab-backed page-table object is released again.
- The patched code frees the passed-in page-table start pointer instead.
Severity, Scoring, and the NVD Gap
Awaiting enrichment does not mean awaiting action
As of April 29, 2026, the NVD entry for CVE-2026-31686 is still marked as awaiting enrichment, with no NIST CVSS vector or base score published. That absence can confuse vulnerability-management teams because many dashboards treat “no score” as either low priority or unknown priority. In reality, missing enrichment simply means the public scoring pipeline has not completed its work.The lack of a CVSS score should push teams toward context-based triage. A double free in kernel memory management is a serious bug class, but this specific report is constrained by architecture, configuration, and trigger path. It is not currently presented as a remotely exploitable flaw, and the public information points to a reliability and correctness fix around PMEM teardown.
That said, kernel memory bugs often receive CVEs because they can represent security boundaries under the right circumstances. Local actors with access to device management interfaces, privileged namespace operations, or test infrastructure may be able to trigger crash conditions. Whether that rises to practical privilege escalation depends on details not established in the public record.
The safest phrasing is that CVE-2026-31686 is a kernel double-free vulnerability resolved by upstream stable patches, with exploitation characteristics still not fully characterized by NVD. Enterprises should patch where applicable, but they should not treat this as a broad internet-facing emergency.
Triage teams should classify it using these factors:
- Known affected context: Linux kernel KASAN page-table teardown.
- Public exploit status: no broadly documented exploit in the public record.
- Likely access requirement: local or administrative trigger paths in known reproductions.
- Configuration dependency: architecture and page-size behavior matter.
- Business criticality: higher for POWER, PMEM, and DAX deployments.
- Patch confidence: strong, because stable backports reference a narrow upstream fix.
Microsoft Ecosystem Implications
Why Windows admins may still see this CVE
The user-facing source for many administrators may be Microsoft’s Security Update Guide or a Microsoft vulnerability-management surface, even though the bug is in the Linux kernel. That reflects the way modern fleets are inventoried. Windows, Linux, containers, Azure VMs, WSL instances, appliances, and third-party components increasingly appear in one security dashboard.For traditional Windows desktop administrators, CVE-2026-31686 should not be read as a Windows kernel defect. It does not describe
ntoskrnl, Windows memory management, or a Microsoft-authored driver. The relevant assets are Linux systems or Linux-based environments that your Microsoft tooling happens to monitor.For WSL users, the answer is more nuanced. WSL2 uses a Microsoft-provided Linux kernel, but exposure would depend on whether that kernel includes the affected code path, whether KASAN is enabled, and whether relevant PMEM-style operations are even possible in the environment. Typical consumer WSL2 usage is unlikely to resemble the POWER PMEM scenario described in the report.
For Azure and hybrid infrastructure teams, the story is broader. Linux VMs, specialized HPC deployments, SAP-on-Linux environments, and IBM POWER-adjacent estates may be tracked alongside Windows Server assets. If a scanner flags CVE-2026-31686, the next step is not to patch Windows; it is to identify the Linux kernel package, architecture, and vendor advisory chain.
Recommended workflow for Microsoft-centric teams:
- Confirm the asset type before assigning remediation.
- Identify the kernel version and vendor build, not just the CVE ID.
- Check whether the machine is Linux, WSL, container host, or appliance firmware.
- Separate Microsoft reporting from Microsoft responsibility for the code fix.
- Map the affected host to its Linux distribution update channel.
- Suppress or downgrade irrelevant findings only after documenting architecture and kernel state.
Enterprise Versus Consumer Impact
Most consumers can watch, not panic
For consumers, CVE-2026-31686 is unlikely to require direct manual action. The average Linux desktop user does not run sanitizer-enabled kernels on POWER10 hardware with persistent-memory namespaces. The average Windows user will not encounter this vulnerability unless a security dashboard reports it for a Linux component somewhere in their environment.Enterprise teams should take it more seriously, but still with precision. Large organizations often maintain validation kernels, hardware enablement labs, specialized database servers, and unusual architecture mixes. Those are exactly the places where a narrow kernel memory bug can waste engineering time or disrupt maintenance.
The most exposed groups are likely distribution maintainers, hardware vendors, cloud platform teams, QA labs, and administrators of POWER systems with PMEM. Their concern is less about a mass exploit wave and more about stability, correctness, and confidence in memory-management behavior. When a teardown path can double-free a page-table object, the fix belongs in the next safe maintenance window.
Consumers should:
- Apply normal distribution updates when they arrive.
- Avoid manually cherry-picking kernel patches unless they build custom kernels.
- Ignore Windows panic messaging if the flagged asset is not actually affected.
- Review WSL updates normally, especially on managed systems.
- Wait for vendor packages rather than building from upstream unless necessary.
- Inventory POWER and PMEM usage across production and lab environments.
- Check long-term stable kernel branches for the backported fix.
- Validate distribution errata before closing tickets.
- Run targeted regression tests on PMEM namespace workflows.
- Coordinate storage, Linux, and security teams because the trigger crosses domains.
Competitive and Market Context
Linux’s openness cuts both ways
Linux kernel CVEs often look messy compared with vendor advisories for closed platforms. Mailing-list patches, stable backports, NVD enrichment delays, distribution errata, and third-party dashboards can all appear at different times. That fragmentation frustrates security teams, but it also gives defenders unusual visibility into the technical fix.In this case, the public patch history makes the issue understandable. The code changed in one file, the reproducer involved PMEM namespace manipulation, and the affected assumption was clearly described. That level of transparency is a competitive strength for Linux in enterprise environments, especially where customers demand root-cause detail.
Windows follows a more centralized disclosure model. Microsoft can deliver a cleaner administrative experience through Patch Tuesday, Windows Update, and the Security Update Guide, but external open-source components still complicate that model. Hybrid environments now blend both worlds: Linux transparency and Microsoft dashboarding.
For rivals in the server market, the incident reinforces a persistent theme. Architecture diversity is powerful, but it raises the burden on kernel correctness. x86 dominates many commodity workloads, yet POWER, ARM64, RISC-V, and mainframe architectures keep exposing assumptions that generic code might otherwise hide.
Market implications include:
- Hardware diversity remains a testing challenge for kernel maintainers.
- Enterprise Linux vendors can differentiate through backport speed and architecture expertise.
- Microsoft security tooling gains value when it accurately classifies non-Windows findings.
- Cloud providers must handle niche CVEs without flooding customers with irrelevant alerts.
- Open disclosure helps engineering teams evaluate risk faster than opaque advisories.
- Specialized platforms need specialized validation, especially around memory and storage.
Patch Management Guidance
Turn a vague CVE into a concrete remediation plan
The first challenge with CVE-2026-31686 is turning a sparse vulnerability record into an actionable plan. Because NVD enrichment is pending, teams should lean on kernel vendor updates, stable-branch status, and distribution errata. The presence of stable review patches across multiple kernel lines suggests the fix is not limited to experimental mainline users.Administrators should avoid making remediation decisions from the CVE page alone. A scanner may flag a kernel version range, but your distribution may already have backported the fix without changing the upstream version number in an obvious way. That is common in enterprise Linux, where package changelogs matter more than headline kernel numbers.
For custom-kernel shops, the patch is a straightforward candidate for cherry-picking, but only after confirming the surrounding KASAN code matches the targeted branch. Memory-management patches are not the place for casual manual edits. Even small changes deserve a full boot, PMEM, and architecture-specific regression pass.
A practical remediation sequence is:
- Identify affected hosts by architecture, kernel package, and PMEM usage.
- Check vendor advisories and changelogs for the KASAN pXds fix.
- Prioritize POWER systems with 64K page configurations and persistent-memory workflows.
- Patch non-production validation kernels first to confirm workload stability.
- Schedule production updates according to normal kernel reboot policy.
- Retest
ndctlnamespace create-and-destroy operations where PMEM is deployed. - Close scanner findings only after package-level evidence confirms the fix.
Strengths and Opportunities
CVE-2026-31686 shows the Linux kernel process working in a way that enterprises should appreciate: a real crash was reported, the root cause was narrowed to a bad architectural assumption, the patch was reviewed, and stable backports followed. The opportunity now is to use this case to improve how organizations triage specialized kernel CVEs without waiting passively for NVD scoring.- Clear root cause: the bug centers on a specific page-table address assumption.
- Localized fix: the patch changes a narrow KASAN teardown path rather than redesigning memory management.
- Stable backport attention: multiple supported kernel branches received or reviewed the fix.
- Good diagnostic signal: KASAN produced a detailed double-free report with useful allocation context.
- Architecture learning: the case improves awareness of PowerPC 64K page behavior.
- Inventory improvement: teams can use the CVE to identify overlooked PMEM and DAX deployments.
- Dashboard hygiene: Microsoft-centric shops can refine how Linux CVEs are routed and owned.
Risks and Concerns
The main risk is not that every Linux machine is suddenly exposed to an easy attack. The bigger concern is that organizations may misclassify the issue because it has no NVD score yet, appears in Microsoft tooling, and affects a specialized Linux subsystem. That combination is fertile ground for both neglect and unnecessary escalation.- No NVD score yet: automated severity workflows may mishandle the finding.
- Specialized trigger path: teams may overlook affected PMEM systems because the average host is unaffected.
- Architecture dependency: x86-heavy assumptions can hide POWER-specific exposure.
- Scanner ambiguity: Microsoft dashboards may surface the CVE without explaining Linux ownership.
- Custom kernels: hand-maintained kernel trees may miss stable backports.
- Testing blind spots: PMEM namespace teardown may not be included in routine regression suites.
- Memory-corruption class: double free bugs deserve respect even when exploitation is not established.
What to Watch Next
The next important development will be enrichment and vendor packaging. Once NVD assigns CVSS metadata, vulnerability-management platforms will likely update severity, affected-product mapping, and remediation recommendations. That may change dashboard behavior even if the underlying technical facts remain the same.Linux distribution advisories are equally important. Enterprise teams should watch Red Hat, SUSE, Ubuntu, Debian, Oracle, IBM, and other relevant vendors for package-specific backports. In many environments, the visible kernel version will not tell the whole story because distributions routinely carry fixes behind stable package revisions.
Watch these items over the next release cycle:
- NVD enrichment for CVSS vector, CWE mapping, and affected configurations.
- Distribution kernel changelogs confirming the KASAN pXds fix.
- Microsoft vulnerability-management behavior for Linux and hybrid assets.
- PMEM regression reports from POWER and other non-x86 users.
- Follow-on kernel patches that audit similar page-table alignment assumptions.
CVE-2026-31686 is a reminder that modern infrastructure security often depends on obscure-looking fixes in deep kernel code. For most users, it will arrive quietly through routine Linux updates; for POWER, PMEM, and validation-kernel operators, it deserves a deliberate check. The best response is measured but not passive: identify the systems that match the risk profile, confirm the vendor fix, and use the incident to strengthen cross-platform vulnerability triage before the next specialized kernel CVE lands in a general-purpose security dashboard.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center