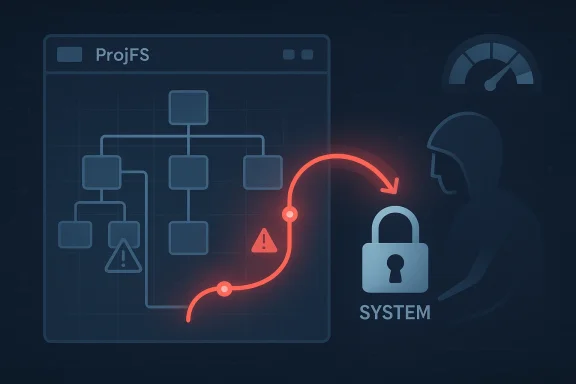
Microsoft’s latest security update guidance around CVE-2026-32069, a Windows Projected File System elevation-of-privilege vulnerability, reflects a familiar but still serious pattern in Windows security: local attackers repeatedly find leverage in filesystem behavior, path handling, and privilege transitions. The case is especially notable because Microsoft has spent the last year hardening Windows against a broader class of redirection-based attacks, including unsafe junction traversal, which suggests this new issue sits in a well-known and actively defended part of the platform. The public MSRC record also uses the confidence metric to frame how certain Microsoft is about the flaw’s existence and technical details, which matters for defenders deciding how urgently to treat it.
Projected File System, or ProjFS, is one of those Windows components that many users never think about, yet it lives close to the plumbing of the operating system and the developer ecosystem. It is used to present virtualized content as if it were a normal filesystem, which makes it useful for large repositories, on-demand file materialization, and sophisticated enterprise workflows. That same proximity to filesystem semantics is why vulnerabilities in this area tend to matter beyond their immediate CVE entry.
A local elevation-of-privilege bug in such a component is not the same as a remote wormable flaw, but it is still highly relevant. In modern Windows attack chains, local privilege escalation is often the second act after phishing, browser exploitation, macro abuse, or lateral movement. Once an attacker gains low-privilege foothold, the ability to cross into SYSTEM or administrator context can turn a contained compromise into a full endpoint takeover.
Microsoft’s recent security narrative around filesystem redirection reinforces that context. In June 2025, MSRC publicly described RedirectionGuard as a mitigation against unsafe junction traversal, calling filesystem redirection attacks a persistent privilege-escalation vector and explaining that attackers often influence privileged processes through filesystem operations they cannot directly perform themselves. That blog post is not about CVE-2026-32069 specifically, but it does show the company’s current threat model and why path-handling flaws remain a priority.
The timing also matters. Windows Server 2025 and the broader Windows platform have seen multiple security-hardening changes in early 2026, including credential autofill restrictions and changes to Windows Deployment Services. Those updates do not prove any relationship to CVE-2026-32069, but they do show Microsoft is still adjusting core behaviors in response to the realities of post-exploitation abuse, especially where local privilege and credential handling intersect. (support.microsoft.com)
That confidence signal is useful because public vulnerability records are not all equally mature. Some entries reflect a complete exploit path. Others are mostly a label around a suspicious behavior. In between are cases where Microsoft has enough evidence to classify the issue, but not enough detail to disclose the exploit mechanics in public.
It also tells incident responders something about attacker readiness. If the details are well understood, then exploit development may already be underway or even completed. If technical knowledge is thin, exploitability may remain limited to researchers or highly skilled operators.
The risk is not merely that a filesystem component exists. The risk is that attackers may be able to manipulate assumptions made by services, installers, sync engines, or developer tools that rely on normal file semantics. Once a component starts projecting or brokering content, every edge case around permissions, links, metadata, and path resolution becomes more important.
That is why Microsoft’s 2025 RedirectionGuard work is so relevant as context. The company explicitly described attackers influencing privileged processes through filesystem operations and explained that junction-based redirection can be used to steer privileged behavior toward attacker-controlled targets. CVE-2026-32069 sits in the same general family of concern, even if the exact primitive is different.
The broader lesson is that Windows security is increasingly about semantic trust, not just ACLs. If a service trusts a path, a file view, or a projected namespace incorrectly, the usual permission checks may be bypassed indirectly.
Microsoft’s own RedirectionGuard blog is a strong acknowledgment of that history. It describes filesystem redirection attacks as a persistent vector and says they have been among the common sources of MSRC cases. That is not just a technical footnote; it is an admission that the operating system has had to evolve defenses around this recurring class of bugs.
This is also why the Windows update cadence matters. Microsoft often addresses local security issues through cumulative updates rather than standalone one-off fixes, because the underlying weakness may be shared across subsystems. The January 2026 Windows Server 2025 update, for example, folded in multiple security and hardening changes, including behavior changes for WDS and credentials autofill. (support.microsoft.com)
There is a strategic implication here as well. Microsoft increasingly prefers platform mitigations over one-off bug repairs. That suggests the company sees a class problem, not just an isolated defect.
In other words, Microsoft has acknowledged enough to classify the issue, but not enough to hand out a complete exploit recipe. That is normal for MSRC, especially when technical details could help attackers. It also means that anyone reading the advisory should avoid over-interpreting the lack of detail as evidence of low severity.
The absence of public technical detail does not imply the absence of real risk. In fact, it often means the opposite: Microsoft is alerting defenders to something real while keeping enough back for patching and investigation.
This is why the confidence metric should be read alongside the vulnerability class itself. A local elevation-of-privilege issue in a filesystem component is rarely cosmetic. Even when the exploit path is not public, the operational stakes are obvious.
If a local user can escalate through a filesystem component, the consequences may include endpoint tampering, privilege theft, or attacker persistence at a level that complicates remediation. That is especially true on systems where developers, admins, or service accounts routinely interact with projected or virtualized file paths.
That does not mean all of them are vulnerable. It does mean the blast radius of any local EoP flaw can be wider than it looks on paper. The vulnerability may be exploited by one component, but the impact may land in another.
Microsoft’s recent Windows hardening behavior changes show that the company knows this. The January 2026 update, for instance, altered behavior around credential autofill in remote support and automated authentication workflows, indicating a willingness to break convenience to reduce abuse. (support.microsoft.com)
A sensible enterprise response usually includes:
Once an attacker has limited access, a local escalation flaw becomes the next step toward ransomware deployment, credential harvesting, or persistence. The user may never know the original foothold was low privilege; they only see the aftermath.
Small businesses face a similar problem, but with less administrative depth. They may not have full-time endpoint security teams or rapid patch orchestration. That can turn a “local only” flaw into a practical business risk.
The issue also lands in a year where Microsoft is doing substantial platform hardening. That can improve security over time, but it can also create compatibility friction and confusion for users who do not know why something changed. The January 2026 update already caused cloud-storage-related file issues for some users, showing that even protective changes can have side effects. (support.microsoft.com)
The existence of CVE-2026-32069 suggests that mitigation and vulnerability discovery are moving in parallel. New security controls can reduce exploitability, but they also uncover edge cases that were previously hidden inside normal behavior. That is often what happens when a platform starts enforcing stricter assumptions.
That balance is visible in the way Windows updates are now described. The January 2026 update includes not just fixes, but also behavior changes and known-issue notes. That suggests Microsoft is increasingly comfortable changing runtime behavior to close attack paths even when the result is some short-term friction. (support.microsoft.com)
In security terms, that is the right direction. Compatibility pain is painful; compromise is worse.
That matters because ProjFS-like components often sit inside developer and enterprise workflows. If a security fix changes the trust model, software that was built around prior assumptions may need updates. In the short term, that can create friction. In the long term, it can improve baseline safety across the platform.
The same dynamic applies to enterprise software vendors. A solution that shells out to privileged file operations or depends on projected namespace behavior may need to be tested against patch changes. If not, customers may see breakage after updates, even when the security fix is correct.
Microsoft’s recent Windows update notes show that this is not hypothetical. The January 2026 release already addressed issues involving cloud storage file access and RemoteApp connections, which demonstrates how security and usability can intersect in unexpected ways. (support.microsoft.com)
It will also be worth watching whether Microsoft folds additional hardening into cumulative updates rather than leaving the issue to a narrow hotfix. That would be consistent with its recent strategy. For enterprises, the practical question is not just whether the patch exists, but whether future updates change runtime assumptions in ways that affect their software stack.
The broader lesson is that Windows security is increasingly being won or lost in the details of path handling, namespace projection, and privilege-aware file operations. CVE-2026-32069 is one more reminder that the filesystem is not just storage; it is a security boundary, an attack surface, and a place where small mistakes can have very large consequences. If Microsoft’s mitigation strategy continues to mature, the long-term result may be a sturdier Windows platform, but the short-term reality remains the same: defenders need to patch quickly, test carefully, and assume that anything involving privileged filesystem behavior deserves close scrutiny.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Projected File System, or ProjFS, is one of those Windows components that many users never think about, yet it lives close to the plumbing of the operating system and the developer ecosystem. It is used to present virtualized content as if it were a normal filesystem, which makes it useful for large repositories, on-demand file materialization, and sophisticated enterprise workflows. That same proximity to filesystem semantics is why vulnerabilities in this area tend to matter beyond their immediate CVE entry.A local elevation-of-privilege bug in such a component is not the same as a remote wormable flaw, but it is still highly relevant. In modern Windows attack chains, local privilege escalation is often the second act after phishing, browser exploitation, macro abuse, or lateral movement. Once an attacker gains low-privilege foothold, the ability to cross into SYSTEM or administrator context can turn a contained compromise into a full endpoint takeover.
Microsoft’s recent security narrative around filesystem redirection reinforces that context. In June 2025, MSRC publicly described RedirectionGuard as a mitigation against unsafe junction traversal, calling filesystem redirection attacks a persistent privilege-escalation vector and explaining that attackers often influence privileged processes through filesystem operations they cannot directly perform themselves. That blog post is not about CVE-2026-32069 specifically, but it does show the company’s current threat model and why path-handling flaws remain a priority.
The timing also matters. Windows Server 2025 and the broader Windows platform have seen multiple security-hardening changes in early 2026, including credential autofill restrictions and changes to Windows Deployment Services. Those updates do not prove any relationship to CVE-2026-32069, but they do show Microsoft is still adjusting core behaviors in response to the realities of post-exploitation abuse, especially where local privilege and credential handling intersect. (support.microsoft.com)
What Microsoft Is Signaling
Microsoft’s MSRC write-up uses a specific confidence framing for the vulnerability, and that is important. The company is essentially telling defenders how much technical certainty it has about the issue and, by extension, how much attackers may already know. When a flaw is fully confirmed and the root cause is understood, the operational risk is usually higher than when the issue is merely suspected or inferred.That confidence signal is useful because public vulnerability records are not all equally mature. Some entries reflect a complete exploit path. Others are mostly a label around a suspicious behavior. In between are cases where Microsoft has enough evidence to classify the issue, but not enough detail to disclose the exploit mechanics in public.
Why the confidence metric matters
The metric is more than a bureaucratic detail. It helps defenders distinguish between a CVE that is theoretically possible and one that is technically grounded. For enterprise patch planning, that distinction can influence whether a flaw is treated as routine maintenance or as a priority exposure requiring accelerated rollout.It also tells incident responders something about attacker readiness. If the details are well understood, then exploit development may already be underway or even completed. If technical knowledge is thin, exploitability may remain limited to researchers or highly skilled operators.
- Higher confidence usually means greater certainty of real-world risk
- Better-understood bugs are often easier to weaponize
- Ambiguous entries still deserve attention, but with more caution
- Local privilege escalation flaws often become chain links, not standalone events
Why Projected File System Is Sensitive
Projected File System is part of a broader ecosystem of Windows filesystem extensibility, and extensibility often brings security complexity. Any component that influences how files appear, how they are materialized, or how access is brokered between user-mode and kernel-assisted behavior can become a security boundary problem. That is especially true when less-privileged code can trigger privileged operations indirectly.The risk is not merely that a filesystem component exists. The risk is that attackers may be able to manipulate assumptions made by services, installers, sync engines, or developer tools that rely on normal file semantics. Once a component starts projecting or brokering content, every edge case around permissions, links, metadata, and path resolution becomes more important.
The attack surface behind the abstraction
From an attacker’s point of view, filesystem abstractions are attractive because they often hide complexity from the application developer. A privileged service may believe it is reading a simple path, writing a harmless cache, or enumerating a benign directory. Under the hood, though, the filesystem stack can expose redirection, overlay, or virtualization behavior that changes the target of the operation.That is why Microsoft’s 2025 RedirectionGuard work is so relevant as context. The company explicitly described attackers influencing privileged processes through filesystem operations and explained that junction-based redirection can be used to steer privileged behavior toward attacker-controlled targets. CVE-2026-32069 sits in the same general family of concern, even if the exact primitive is different.
The broader lesson is that Windows security is increasingly about semantic trust, not just ACLs. If a service trusts a path, a file view, or a projected namespace incorrectly, the usual permission checks may be bypassed indirectly.
- Filesystem abstraction can obscure security-relevant behavior
- Privileged services often make assumptions about path stability
- Redirection and projection can create TOCTOU-like confusion
- Local attackers often need only one misstep from a trusted process
Historical Context: Windows and Filesystem Escalation
Windows has a long history of elevation-of-privilege bugs rooted in filesystem behavior. Junctions, symbolic links, path traversal, directory races, and privileged file operations have repeatedly shown up in MSRC advisories and research papers. The pattern persists because file I/O is one of the most common operations in the operating system, and common operations are where edge cases hide.Microsoft’s own RedirectionGuard blog is a strong acknowledgment of that history. It describes filesystem redirection attacks as a persistent vector and says they have been among the common sources of MSRC cases. That is not just a technical footnote; it is an admission that the operating system has had to evolve defenses around this recurring class of bugs.
Why local EoP keeps returning
Local elevation of privilege bugs often survive because they sit at the intersection of complexity and convenience. Developers want services to read and write files in flexible ways. Attackers want those same operations to happen in privileged contexts. A small logic error, a missing validation step, or a flawed trust assumption can become a full escalation path.This is also why the Windows update cadence matters. Microsoft often addresses local security issues through cumulative updates rather than standalone one-off fixes, because the underlying weakness may be shared across subsystems. The January 2026 Windows Server 2025 update, for example, folded in multiple security and hardening changes, including behavior changes for WDS and credentials autofill. (support.microsoft.com)
There is a strategic implication here as well. Microsoft increasingly prefers platform mitigations over one-off bug repairs. That suggests the company sees a class problem, not just an isolated defect.
A familiar playbook for attackers
Attackers who gain local execution on Windows typically do not need an exotic exploit to finish the job. They need a path from standard user to higher privilege, and filesystem flaws are among the oldest ways to get there. Once that escalation happens, they can disable defenses, dump credentials, deploy persistence, or move laterally with greater freedom.- Local EoP is often the pivot from foothold to full compromise
- Filesystem bugs are durable because the OS depends on file operations everywhere
- Mitigations reduce risk, but they do not eliminate whole classes of abuse
- Platform hardening is now part of the vulnerability response lifecycle
What We Know About the Public Record
The public information around CVE-2026-32069 is still limited, and that limitation itself is meaningful. Microsoft’s update guide identifies the flaw as a Windows Projected File System elevation-of-privilege vulnerability, but the most visible public description emphasizes the confidence metric rather than a detailed exploit narrative. That means the advisory is currently more useful as a defender’s alert than as a researcher’s blueprint.In other words, Microsoft has acknowledged enough to classify the issue, but not enough to hand out a complete exploit recipe. That is normal for MSRC, especially when technical details could help attackers. It also means that anyone reading the advisory should avoid over-interpreting the lack of detail as evidence of low severity.
The role of disclosure discipline
Microsoft’s disclosure style often separates classification from exploitation details. This can frustrate researchers who want more context, but it is also a practical security choice. Detailed root-cause descriptions can become a roadmap for copycat exploitation, and local EoP bugs are especially valuable to attackers because they chain so well with other initial access vectors.The absence of public technical detail does not imply the absence of real risk. In fact, it often means the opposite: Microsoft is alerting defenders to something real while keeping enough back for patching and investigation.
This is why the confidence metric should be read alongside the vulnerability class itself. A local elevation-of-privilege issue in a filesystem component is rarely cosmetic. Even when the exploit path is not public, the operational stakes are obvious.
- The advisory is publicly classified
- The exploit mechanics are not publicly explained in depth
- Microsoft is signaling seriousness without oversharing
- The issue likely matters most in chained attack scenarios
Enterprise Impact
For enterprises, the primary concern is not whether a home PC user will notice the issue. It is whether the flaw can be used to break out of a low-privilege compromise on managed endpoints, developer workstations, or servers running file-heavy workflows. In modern environments, those systems often host sensitive tokens, administrative sessions, and automation tooling.If a local user can escalate through a filesystem component, the consequences may include endpoint tampering, privilege theft, or attacker persistence at a level that complicates remediation. That is especially true on systems where developers, admins, or service accounts routinely interact with projected or virtualized file paths.
Why managed environments are exposed
Enterprises tend to have more complexity than consumer systems. They also have more software that touches the filesystem in privileged contexts: backup agents, EDR tools, dev tooling, sync platforms, deployment systems, and service wrappers. Each one is a possible bridge from user-controlled input to trusted file operations.That does not mean all of them are vulnerable. It does mean the blast radius of any local EoP flaw can be wider than it looks on paper. The vulnerability may be exploited by one component, but the impact may land in another.
Microsoft’s recent Windows hardening behavior changes show that the company knows this. The January 2026 update, for instance, altered behavior around credential autofill in remote support and automated authentication workflows, indicating a willingness to break convenience to reduce abuse. (support.microsoft.com)
Operational implications for admins
Administrators should read CVE-2026-32069 as a patch-priority issue, not a theoretical note. If the affected systems include developer machines, CI/CD hosts, virtualization layers, or systems with privileged filesystem activity, the urgency rises. Even where exploitation is not publicly documented, the class is attractive to post-exploitation tooling.A sensible enterprise response usually includes:
- Identify affected Windows versions and rollout channels.
- Prioritize devices with elevated local privilege activity.
- Patch before attackers have a chance to chain the flaw.
- Watch for unusual filesystem redirection or permission anomalies.
- Reassess service accounts and local admin sprawl.
- Developer endpoints often carry the richest attack value
- Services running as SYSTEM can turn a local bug into full takeover
- Automation and image-building hosts deserve special scrutiny
- Patch speed matters more when the flaw is easy to chain
Consumer and Small Business Impact
For consumers, the issue may seem abstract at first because most people do not knowingly use Projected File System features. But that is precisely why local privilege bugs are dangerous: users usually do not need to understand the vulnerable component to become victims of the chain that leads into it. A malicious download, a compromised browser session, or a trojanized installer can be enough to land an attacker on the machine.Once an attacker has limited access, a local escalation flaw becomes the next step toward ransomware deployment, credential harvesting, or persistence. The user may never know the original foothold was low privilege; they only see the aftermath.
Why home users still matter
Consumer Windows systems are often less segmented than enterprise ones. The primary account may have broad access, security software may be inconsistent, and administrative habits can be looser. That makes any EoP bug especially useful to threat actors who prefer to pair social engineering with privilege escalation.Small businesses face a similar problem, but with less administrative depth. They may not have full-time endpoint security teams or rapid patch orchestration. That can turn a “local only” flaw into a practical business risk.
The issue also lands in a year where Microsoft is doing substantial platform hardening. That can improve security over time, but it can also create compatibility friction and confusion for users who do not know why something changed. The January 2026 update already caused cloud-storage-related file issues for some users, showing that even protective changes can have side effects. (support.microsoft.com)
What non-enterprise users should take away
For individual users, the best defense remains boring but effective: keep Windows updated, avoid running unknown code, and treat privilege escalation as a reason to be extra careful about endpoint hygiene. The vulnerability is not a call for panic; it is a reminder that local bugs become dangerous when paired with other compromise steps.- Keep Windows fully patched
- Avoid untrusted executables and scripts
- Use standard accounts where possible
- Treat unexpected elevation prompts as suspicious
- Maintain reputable security software and backups
Microsoft’s Mitigation Strategy
Microsoft is not just patching discrete bugs; it is also trying to reduce the amount of filesystem trust the platform grants by default. That strategy is visible in the RedirectionGuard initiative, in Windows update hardening, and in other behavior changes aimed at shrinking attacker opportunities. The company clearly understands that path-based privilege escalation is a platform problem, not just a bug-fix problem.The existence of CVE-2026-32069 suggests that mitigation and vulnerability discovery are moving in parallel. New security controls can reduce exploitability, but they also uncover edge cases that were previously hidden inside normal behavior. That is often what happens when a platform starts enforcing stricter assumptions.
Platform hardening versus compatibility
This is the classic Windows security trade-off. The stricter the platform gets about paths, redirections, and privileged operations, the more likely it is to break something that relied on undocumented flexibility. Microsoft has to balance security, compatibility, and manageability across millions of endpoints.That balance is visible in the way Windows updates are now described. The January 2026 update includes not just fixes, but also behavior changes and known-issue notes. That suggests Microsoft is increasingly comfortable changing runtime behavior to close attack paths even when the result is some short-term friction. (support.microsoft.com)
In security terms, that is the right direction. Compatibility pain is painful; compromise is worse.
The larger security architecture trend
CVE-2026-32069 also fits a broader industry trend: vendors are hardening not just code, but classes of operations. Rather than waiting for every junction, projection, or path bug to be discovered individually, Microsoft is introducing guardrails that can blunt entire families of attacks. That is a more scalable model of defense, even if it never eliminates the need for patches.- Hardening reduces the value of old attack techniques
- Behavioral changes can preempt whole exploit classes
- Patch cycles are becoming more architectural
- The operating system is being taught to distrust more defaults
Competitive and Ecosystem Implications
Security issues in Windows filesystem components ripple outward into the broader ecosystem. Third-party EDR vendors, backup platforms, dev tools, filesystem virtualizers, and cloud-sync clients all have to account for behavior changes and new assumptions. When Microsoft tightens a subsystem, everyone downstream has to revalidate how their software behaves under that stricter model.That matters because ProjFS-like components often sit inside developer and enterprise workflows. If a security fix changes the trust model, software that was built around prior assumptions may need updates. In the short term, that can create friction. In the long term, it can improve baseline safety across the platform.
How ecosystem partners are affected
Security vendors tend to benefit from clearer platform boundaries, because detection becomes easier when the OS is less permissive about ambiguous file behavior. At the same time, they also inherit more edge cases to monitor. For product teams, that means more regression testing, more telemetry review, and more coordination with Microsoft’s update cadence.The same dynamic applies to enterprise software vendors. A solution that shells out to privileged file operations or depends on projected namespace behavior may need to be tested against patch changes. If not, customers may see breakage after updates, even when the security fix is correct.
Microsoft’s recent Windows update notes show that this is not hypothetical. The January 2026 release already addressed issues involving cloud storage file access and RemoteApp connections, which demonstrates how security and usability can intersect in unexpected ways. (support.microsoft.com)
The market message
There is also a competitive signal here. Microsoft is trying to show that Windows security is becoming more proactive and more class-based. That messaging matters in a market where endpoint buyers evaluate not just feature sets, but the quality of the platform’s defensive posture. If Microsoft can keep shrinking common privilege-escalation surfaces, it strengthens the case for Windows as a managed enterprise platform.- More hardening can improve trust in the platform
- Vendors must adapt faster to behavior changes
- Security telemetry becomes more important
- Compatibility testing becomes a competitive differentiator
Strengths and Opportunities
The strongest aspect of Microsoft’s current handling is that the company is increasingly willing to frame these issues as classes of attacks, not just isolated defects. That gives defenders a better mental model for why filesystem-related local EoP bugs keep recurring, and it points toward controls that can help beyond a single CVE. It also suggests the platform is moving toward systemic mitigation, which is a healthier security posture than endless point fixes.- Class-based mitigation can reduce repeated exploitation patterns
- Windows hardening is becoming more proactive
- Administrator guidance is more visible than in the past
- Cumulative updates simplify patch management for many environments
- Behavior changes can blunt whole exploit families
- Telemetry and rollout controls improve staged deployment
- Filesystem security is finally getting the attention it has long deserved
Risks and Concerns
The main concern is that local privilege escalation remains one of the most valuable footholds for attackers, and filesystem bugs continue to provide that foothold with uncomfortable regularity. Even when Microsoft hardens the platform, attackers only need one overlooked service, one vulnerable workflow, or one unpatched machine to turn a local issue into a major incident. The opacity of the public advisory also means defenders must act before the ecosystem has fully absorbed the technical details.- Attack chaining can turn a local bug into full compromise
- Patch lag remains a major enterprise risk
- Opaque advisories make prioritization harder
- Compatibility breakage may slow adoption of mitigations
- Third-party software may not be ready for stricter filesystem rules
- Low-privilege footholds are still common in real incidents
- Filesystem trust assumptions are notoriously hard to audit
What to Watch Next
The next few update cycles should tell us whether Microsoft treats CVE-2026-32069 as a standalone fix or part of a broader ProjFS and filesystem-security tightening effort. If the company publishes more guidance, defenders will learn whether the issue is tied to a specific operation, a trust boundary, or a broader class of redirection behavior. The answer will shape how security teams assess adjacent Windows components.It will also be worth watching whether Microsoft folds additional hardening into cumulative updates rather than leaving the issue to a narrow hotfix. That would be consistent with its recent strategy. For enterprises, the practical question is not just whether the patch exists, but whether future updates change runtime assumptions in ways that affect their software stack.
Watch for these signals
- Additional MSRC guidance or advisory updates
- New hardening behavior in cumulative Windows updates
- References to ProjFS or adjacent filesystem components
- Enterprise compatibility reports after patch deployment
- Evidence of exploitation in the wild
- Security research mapping the vulnerability class
- Third-party vendor advisories about filesystem assumptions
The broader lesson is that Windows security is increasingly being won or lost in the details of path handling, namespace projection, and privilege-aware file operations. CVE-2026-32069 is one more reminder that the filesystem is not just storage; it is a security boundary, an attack surface, and a place where small mistakes can have very large consequences. If Microsoft’s mitigation strategy continues to mature, the long-term result may be a sturdier Windows platform, but the short-term reality remains the same: defenders need to patch quickly, test carefully, and assume that anything involving privileged filesystem behavior deserves close scrutiny.
Source: MSRC Security Update Guide - Microsoft Security Response Center