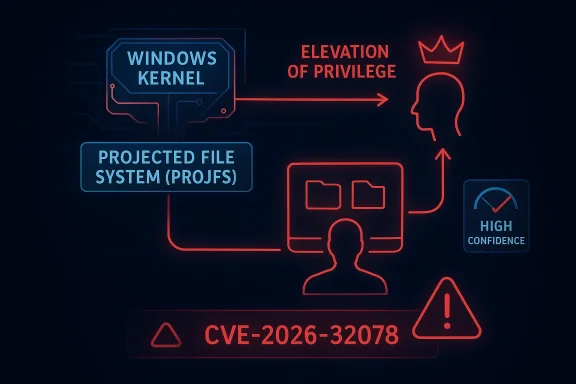
Microsoft’s CVE-2026-32078 entry for the Windows Projected File System is exactly the kind of advisory that security teams should not dismiss as routine. The label alone tells us the risk class: Elevation of Privilege in a kernel-adjacent storage component, which means a local attacker who already has a foothold may be able to turn that access into something far more powerful. Just as important, Microsoft’s vulnerability metadata uses a confidence-oriented framing that speaks not only to impact, but to how certain the vendor is that the bug exists and how much credible technical detail is available to defenders. That distinction matters because certainty changes urgency.
Projected File System, usually shortened to ProjFS, is part of the Windows storage and file-system ecosystem that lets a user-mode provider present virtualized content as if it were ordinary files and folders. That sounds abstract, but in practice it underpins use cases where applications need large, on-demand, or remotely sourced datasets that should appear locally without being fully materialized on disk. It is a convenience feature, a developer feature, and a systems feature all at once, which is exactly why it deserves security attention.
The security risk around ProjFS is not new. Windows has spent years dealing with privilege-escalation bugs in kernel-mode components, file-system drivers, and subsystems that bridge user mode and privileged code. Those pathways are attractive to attackers because they often combine complex state handling, file operations, and trust decisions that are difficult to reason about at scale. A single flaw can become a local privilege-escalation primitive, and once a low-privileged user can influence kernel behavior, the blast radius grows quickly.
Microsoft’s approach to these entries has also evolved. Rather than treating every advisory as a simple binary “patched or not patched” event, the company increasingly exposes metadata that helps defenders understand how solid the report is and how much technical confidence exists behind it. That is especially helpful in cases where public details are sparse, because the security team can still make an informed call about patch urgency, exposure, and validation.
CVE-2026-32078 fits squarely into that pattern. The advisory title identifies the affected component and the broad impact, but the public description is intentionally limited. That lack of detail does not mean the issue is speculative; it means Microsoft has chosen to disclose only what it deems necessary while still signaling to administrators that the issue is real enough to track, patch, and prioritize. In the world of Windows security, that is a meaningful distinction.
This is also part of a broader trend in Microsoft vulnerability management. Storage, virtualization, accessibility, driver, and service-based bugs continue to dominate local escalation scenarios because they live in the layers attackers value most: the layers that translate normal user activity into privileged system behavior. ProjFS is one more reminder that the most dangerous bugs are often not flashy remote-code-execution issues, but local flaws that help an intruder go from “present” to “powerful.”
That also changes the defensive posture. Local EoP flaws are often the second act of an intrusion rather than the first. They are used after phishing, malware delivery, or another initial access technique has already succeeded, which means they are frequently paired with persistence, credential theft, or lateral movement. In enterprise environments, that makes the advisory more important than the single CVE label might suggest.
The fact that this is a ProjFS issue adds another layer of concern. Kernel-facing storage code tends to be highly trusted by the operating system, but it is also exposed to complicated inputs and edge cases. If an attacker can manipulate file projection behavior, they may be able to influence how privileged code interprets paths, file states, or metadata. Even without public exploit detail, that is a familiar and dangerous shape.
That distinction is valuable because vulnerability records are not equally mature. Some are based on clear vendor-confirmed flaws with reproducible behavior. Others are based on researcher reports, partial observations, or classes of bugs that are plausible but not fully characterized publicly. A confidence-oriented metric helps defenders decide whether they are looking at a noisy hypothesis or a solid advisory.
For administrators, this means the CVE should not be triaged only by severity label. A lower-verbosity entry with strong confidence may deserve more attention than a louder but less certain bug report, especially if the affected component is security-sensitive. That is especially true for Windows subsystems that live close to the kernel, where the consequences of getting it wrong are broad.
That boundary becomes more delicate when privileged processes interact with projected content. If a system service, management agent, or backup tool reads from a path that is mediated by ProjFS, it may be relying on assumptions about file identity, state, or ownership that can be altered by an attacker with the right local access. That is why file-system projection bugs so often become privilege-escalation bugs rather than simple crashes.
The broader lesson is that modern Windows security depends on many layers of mediation. The operating system has to decide what is a file, what is a mapping, what is an on-demand artifact, and what can be trusted to behave consistently. Every one of those decisions can be exploited if the state machine is wrong, incomplete, or raced.
That matters because defenders should not read each CVE as a standalone surprise. Instead, they should see it as part of a chronic security problem in which complex Windows subsystems repeatedly become the final rung in an attack chain. The exact subsystem changes, but the operational effect is similar: once the attacker reaches a local foothold, the bug lets them turn that foothold into elevated control.
Historically, Microsoft has had to patch a steady flow of EoP flaws in components such as AFD.sys, NTFS, graphics subsystems, accessibility services, and virtualization drivers. The pattern is consistent enough that security teams now treat many of these advisories as default high-priority endpoint issues, especially when no compensating controls are available.
Workstations and developer endpoints are especially important to review. ProjFS is more likely to appear in environments with source-code tooling, package virtualization, large data sets, or custom software distribution flows. Those are also the environments where developers and operators frequently have elevated rights, making local escalation more dangerous.
Servers are a different story, but not a safer one. On servers, privilege escalation can quickly become domain-wide impact if the compromised host has service accounts, management access, or security tooling that can be abused. A local flaw on a server is often more damaging than the same flaw on a consumer PC because the server’s credentials and trust relationships are richer.
The larger consumer concern is post-compromise escalation. If malware lands through a browser exploit, malicious download, or phishing campaign, a local elevation bug can remove the remaining barriers between the attacker and the system. That means data theft, ransomware deployment, or persistence can happen more cleanly and with fewer warnings.
Power users and enthusiasts deserve special attention. They often run preview builds, experimental software, or toolchains that are more likely to activate unusual Windows subsystems. That makes them early adopters in both functionality and risk, and they should treat ProjFS-related advisories with the same seriousness they would give to any kernel or driver patch.
That complexity is the reason file-system vulnerabilities appear again and again. Developers focus on performance, compatibility, and transparency for applications, but the attacker focuses on edge conditions: racing state changes, odd paths, malformed metadata, and privilege mismatches. If one of those edge cases maps to kernel behavior, the result can be severe.
Microsoft’s recent direction suggests the company knows this. The RedirectionGuard work showed an explicit effort to reduce unsafe junction traversal and prevent privileged services from being tricked by path manipulation. CVE-2026-32078 should be read in that same context: a sign that file-system mediation remains one of Windows’ most sensitive security surfaces.
The safest operational stance is to treat the advisory as part of a broader local-privilege-escalation threat model. If an attacker can get code execution as a standard user, any ProjFS weakness becomes a path toward stronger persistence, better stealth, and broader control. That makes remediation a race between patching and post-compromise escalation.
This is also where patch management maturity matters. Organizations that can rapidly inventory exposed hosts, validate update compliance, and isolate risky endpoints will absorb this kind of issue much better than organizations that rely on monthly cleanup. The gap between those two states is often the difference between a blocked incident and a serious breach.
There is also a bigger strategic question here. Microsoft has been steadily improving its filesystem-redirection defenses, and CVE-2026-32078 may be another signal that the company will continue hardening projection-related paths rather than relying only on point fixes. That is good for the platform, but it also means administrators should expect more security scrutiny around features that mediate file identity and privileged access.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Projected File System, usually shortened to ProjFS, is part of the Windows storage and file-system ecosystem that lets a user-mode provider present virtualized content as if it were ordinary files and folders. That sounds abstract, but in practice it underpins use cases where applications need large, on-demand, or remotely sourced datasets that should appear locally without being fully materialized on disk. It is a convenience feature, a developer feature, and a systems feature all at once, which is exactly why it deserves security attention.The security risk around ProjFS is not new. Windows has spent years dealing with privilege-escalation bugs in kernel-mode components, file-system drivers, and subsystems that bridge user mode and privileged code. Those pathways are attractive to attackers because they often combine complex state handling, file operations, and trust decisions that are difficult to reason about at scale. A single flaw can become a local privilege-escalation primitive, and once a low-privileged user can influence kernel behavior, the blast radius grows quickly.
Microsoft’s approach to these entries has also evolved. Rather than treating every advisory as a simple binary “patched or not patched” event, the company increasingly exposes metadata that helps defenders understand how solid the report is and how much technical confidence exists behind it. That is especially helpful in cases where public details are sparse, because the security team can still make an informed call about patch urgency, exposure, and validation.
CVE-2026-32078 fits squarely into that pattern. The advisory title identifies the affected component and the broad impact, but the public description is intentionally limited. That lack of detail does not mean the issue is speculative; it means Microsoft has chosen to disclose only what it deems necessary while still signaling to administrators that the issue is real enough to track, patch, and prioritize. In the world of Windows security, that is a meaningful distinction.
This is also part of a broader trend in Microsoft vulnerability management. Storage, virtualization, accessibility, driver, and service-based bugs continue to dominate local escalation scenarios because they live in the layers attackers value most: the layers that translate normal user activity into privileged system behavior. ProjFS is one more reminder that the most dangerous bugs are often not flashy remote-code-execution issues, but local flaws that help an intruder go from “present” to “powerful.”
What the Vulnerability Class Tells Us
At a minimum, the advisory tells us the bug lives in a local privilege-escalation category, not a remote attack class. That matters because it changes the attacker model. Instead of a drive-by compromise that reaches across the network, the likely attacker already has an account, a process, or a foothold on the host and is trying to climb the privilege ladder.That also changes the defensive posture. Local EoP flaws are often the second act of an intrusion rather than the first. They are used after phishing, malware delivery, or another initial access technique has already succeeded, which means they are frequently paired with persistence, credential theft, or lateral movement. In enterprise environments, that makes the advisory more important than the single CVE label might suggest.
The fact that this is a ProjFS issue adds another layer of concern. Kernel-facing storage code tends to be highly trusted by the operating system, but it is also exposed to complicated inputs and edge cases. If an attacker can manipulate file projection behavior, they may be able to influence how privileged code interprets paths, file states, or metadata. Even without public exploit detail, that is a familiar and dangerous shape.
Why local still means urgent
A local vulnerability is sometimes misread as “less severe” because it requires an account on the machine. That is a mistake. In modern attacks, local access is often the easy part, especially after malware lands through a browser, script, macro, or stolen credentials.- Local EoP frequently converts a limited foothold into full system compromise.
- Kernel and driver bugs often bypass application-layer security assumptions.
- Privilege escalation can disable security tools, tamper with logs, and expand persistence.
- Attackers rarely need a local flaw to be internet-facing for it to be valuable.
- In enterprise incidents, local escalation is often what turns an intrusion into an outage.
Understanding Microsoft’s Confidence Metric
The user-provided description of the metric is the key to interpreting this advisory. Microsoft is not merely saying “there may be a bug here.” It is signaling how confident it is in the existence of the vulnerability and in the technical credibility of the details surrounding it. In other words, the metric is partly about proof strength and partly about disclosure quality.That distinction is valuable because vulnerability records are not equally mature. Some are based on clear vendor-confirmed flaws with reproducible behavior. Others are based on researcher reports, partial observations, or classes of bugs that are plausible but not fully characterized publicly. A confidence-oriented metric helps defenders decide whether they are looking at a noisy hypothesis or a solid advisory.
For administrators, this means the CVE should not be triaged only by severity label. A lower-verbosity entry with strong confidence may deserve more attention than a louder but less certain bug report, especially if the affected component is security-sensitive. That is especially true for Windows subsystems that live close to the kernel, where the consequences of getting it wrong are broad.
What high confidence implies
A high-confidence advisory usually suggests that Microsoft has enough internal verification to treat the flaw as real and actionable. That may come from an internal reproduction, a reliable external report, or a fix path that has already been engineered and validated.- The issue is likely reproducible in Microsoft’s environment.
- The technical signal is strong enough to justify patching.
- Attackers may have enough information to begin reverse-engineering the bug class.
- Defender urgency should be based on trust in the vendor’s claim, not just on exploit chatter.
- Confidence is not the same as exploitation, but it is often the reason patching should not wait.
ProjFS in the Windows Security Stack
ProjFS is interesting because it sits at the intersection of usability and trust. It enables file virtualization, which is helpful for large repositories, developer tools, and on-demand content rendering. But anything that turns abstract or remote content into locally accessible file paths has to be treated as a security boundary.That boundary becomes more delicate when privileged processes interact with projected content. If a system service, management agent, or backup tool reads from a path that is mediated by ProjFS, it may be relying on assumptions about file identity, state, or ownership that can be altered by an attacker with the right local access. That is why file-system projection bugs so often become privilege-escalation bugs rather than simple crashes.
The broader lesson is that modern Windows security depends on many layers of mediation. The operating system has to decide what is a file, what is a mapping, what is an on-demand artifact, and what can be trusted to behave consistently. Every one of those decisions can be exploited if the state machine is wrong, incomplete, or raced.
Where attacker value comes from
Attackers care about ProjFS because it can sit in the path between ordinary user actions and privileged operations. That gives them the chance to influence higher-privileged code indirectly.- It can mediate file access for privileged services.
- It can expose timing or state inconsistencies.
- It can create opportunities for path confusion or redirection.
- It may be reachable in environments that use developer tooling or data virtualization.
- It can become a stepping stone to service abuse or code execution.
How This Compares to Other Windows EoP Bugs
CVE-2026-32078 is not an isolated event. It belongs to a long-running class of Windows privilege-escalation issues that recur across file systems, kernel components, services, and virtualization layers. The common thread is not the exact code path, but the trust boundary that an attacker can manipulate.That matters because defenders should not read each CVE as a standalone surprise. Instead, they should see it as part of a chronic security problem in which complex Windows subsystems repeatedly become the final rung in an attack chain. The exact subsystem changes, but the operational effect is similar: once the attacker reaches a local foothold, the bug lets them turn that foothold into elevated control.
Historically, Microsoft has had to patch a steady flow of EoP flaws in components such as AFD.sys, NTFS, graphics subsystems, accessibility services, and virtualization drivers. The pattern is consistent enough that security teams now treat many of these advisories as default high-priority endpoint issues, especially when no compensating controls are available.
Why ProjFS belongs in the same conversation
ProjFS is different from a network service or an app, but it is not fundamentally safer. It is a kernel-adjacent file-system projection layer, and those are the kinds of components where small logic mistakes can become major escalation avenues.- Attackers value kernel-facing bugs because they are durable and widely reusable.
- Storage subsystems often handle untrusted input at high privilege.
- File virtualization adds state complexity that is hard to test exhaustively.
- Bugs in these areas are usually local, but local is enough after initial compromise.
- The old rule still applies: if the bug touches the kernel, assume the consequences are systemic.
Enterprise Exposure and Real-World Risk
For enterprises, the real question is not whether CVE-2026-32078 can be exploited in theory. It is whether a vulnerable ProjFS deployment exists anywhere in the estate, and whether a local attacker could reach it through normal user activity, malware, or a compromised admin workflow. In large organizations, the answer is often yes somewhere, which is why these advisories deserve immediate triage.Workstations and developer endpoints are especially important to review. ProjFS is more likely to appear in environments with source-code tooling, package virtualization, large data sets, or custom software distribution flows. Those are also the environments where developers and operators frequently have elevated rights, making local escalation more dangerous.
Servers are a different story, but not a safer one. On servers, privilege escalation can quickly become domain-wide impact if the compromised host has service accounts, management access, or security tooling that can be abused. A local flaw on a server is often more damaging than the same flaw on a consumer PC because the server’s credentials and trust relationships are richer.
What enterprises should do first
A measured response is better than panic, but it should still be fast.- Confirm whether the March 2026 or current cumulative update containing the fix is installed.
- Identify endpoints that use ProjFS-enabled tooling or projection-heavy workflows.
- Prioritize systems with developer tools, management agents, or privileged service accounts.
- Review compensating controls such as application allowlisting and least privilege.
- Validate that EDR and logging still function after patching.
Consumer and Power-User Impact
Consumer exposure is usually lower than enterprise exposure for a bug like this, but that does not mean it is negligible. Many home users install developer tools, game modding utilities, sync clients, backup tools, or advanced shell enhancements that may interact with file-system virtualization. The average user may never notice ProjFS by name, but they can still be affected indirectly by software that uses it.The larger consumer concern is post-compromise escalation. If malware lands through a browser exploit, malicious download, or phishing campaign, a local elevation bug can remove the remaining barriers between the attacker and the system. That means data theft, ransomware deployment, or persistence can happen more cleanly and with fewer warnings.
Power users and enthusiasts deserve special attention. They often run preview builds, experimental software, or toolchains that are more likely to activate unusual Windows subsystems. That makes them early adopters in both functionality and risk, and they should treat ProjFS-related advisories with the same seriousness they would give to any kernel or driver patch.
Practical consumer considerations
- Keep cumulative updates current on every Windows device.
- Avoid running untrusted utilities with administrative rights.
- Be cautious with software that virtualizes content or mounts projected file trees.
- Treat unexpected Defender or EDR tampering as a possible escalation sign.
- A local EoP bug is especially dangerous after the first malware foothold.
Why File-System Bugs Keep Coming Back
File systems are hard to secure because they are not just storage abstractions. They are also policy engines, metadata managers, synchronization systems, and trust translators. Every time Windows adds a new layer of virtualization or projection, it creates more code that must correctly preserve identity, ownership, state, and privilege boundaries.That complexity is the reason file-system vulnerabilities appear again and again. Developers focus on performance, compatibility, and transparency for applications, but the attacker focuses on edge conditions: racing state changes, odd paths, malformed metadata, and privilege mismatches. If one of those edge cases maps to kernel behavior, the result can be severe.
Microsoft’s recent direction suggests the company knows this. The RedirectionGuard work showed an explicit effort to reduce unsafe junction traversal and prevent privileged services from being tricked by path manipulation. CVE-2026-32078 should be read in that same context: a sign that file-system mediation remains one of Windows’ most sensitive security surfaces.
The underlying engineering challenge
The hardest part is that secure file handling has to remain compatible with years of legacy behavior. Windows cannot simply remove complex path semantics or projection features without breaking large parts of the ecosystem.- Compatibility pushes against simplification.
- Performance pushes against repeated validation.
- Usability pushes against restrictive security checks.
- Legacy behavior can preserve old attack surfaces.
- Security engineering in this area is a constant balancing act.
What Administrators Should Assume
Administrators should assume that CVE-2026-32078 is real, actionable, and worth immediate attention, even if Microsoft has not published much technical detail publicly. That is the whole point of the confidence-oriented framing: the vendor is telling defenders that the evidence is strong enough to drive response.The safest operational stance is to treat the advisory as part of a broader local-privilege-escalation threat model. If an attacker can get code execution as a standard user, any ProjFS weakness becomes a path toward stronger persistence, better stealth, and broader control. That makes remediation a race between patching and post-compromise escalation.
This is also where patch management maturity matters. Organizations that can rapidly inventory exposed hosts, validate update compliance, and isolate risky endpoints will absorb this kind of issue much better than organizations that rely on monthly cleanup. The gap between those two states is often the difference between a blocked incident and a serious breach.
Administrative priorities
- Verify patch deployment status across all Windows SKUs in scope.
- Focus first on systems with high privilege density.
- Pay attention to developer and IT admin workstations.
- Ensure incident response teams know this is an escalation issue, not just a stability issue.
- Assume the advisory matters even if exploit details remain sparse.
Strengths and Opportunities
The upside of Microsoft’s current approach is that it gives defenders more than a binary warning. By pairing a component-specific advisory with a confidence signal, Microsoft helps security teams judge both the likely reality of the flaw and the maturity of the technical evidence. That creates room for better prioritization and more precise risk communication.- Better triage through confidence signaling
- Clearer patch urgency for local EoP issues
- Improved defender awareness of kernel-adjacent attack surfaces
- Useful context for differentiating speculation from confirmed risk
- Stronger alignment between advisory severity and operational action
- Opportunity to harden file-system redirection and projection paths
- Motivation to reduce privileged service exposure to user-controlled paths
Risks and Concerns
The biggest concern is not simply that a flaw exists, but that the public technical details are limited enough to make external validation harder. That can create uncertainty for defenders who need to know exactly how the bug is triggered, what products are affected, and whether exploitation is feasible in their specific environment. In practice, that uncertainty often pushes teams to delay remediation, which is the wrong conclusion.- Sparse public detail can slow validation
- Local foothold requirement can encourage underestimation
- Kernel-adjacent exposure raises the consequences of success
- Potential for post-exploitation chaining increases practical danger
- Exposure may be broader than administrators initially assume
- Attackers may learn enough from the patch to reverse-engineer the weakness
- Complex filesystem semantics can make future variants likely
Looking Ahead
The most important thing to watch next is whether Microsoft adds more detail to the advisory, whether third-party trackers surface a plausible weakness pattern, and whether the issue becomes associated with active exploitation. If that happens, the advisory will move from a theoretical local escalation bug to a concrete incident-response concern. Even without that, the current metadata already justifies immediate patching.There is also a bigger strategic question here. Microsoft has been steadily improving its filesystem-redirection defenses, and CVE-2026-32078 may be another signal that the company will continue hardening projection-related paths rather than relying only on point fixes. That is good for the platform, but it also means administrators should expect more security scrutiny around features that mediate file identity and privileged access.
What to watch
- Whether Microsoft publishes updated guidance or mitigation notes
- Whether independent researchers identify a common ProjFS weakness pattern
- Whether exploit activity or proof-of-concept code appears
- Whether related filesystem or redirection bugs are disclosed in the same cycle
- Whether patching introduces compatibility issues for projection-heavy software
Source: MSRC Security Update Guide - Microsoft Security Response Center