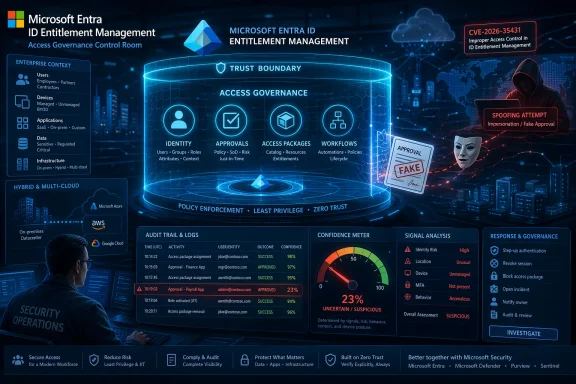
Microsoft has assigned CVE-2026-35431 to a Microsoft Entra ID Entitlement Management spoofing vulnerability, but the public confidence signal attached to the entry is what makes this disclosure especially important. Microsoft’s Security Update Guide uses that metric to express how certain it is that the vulnerability truly exists and how credible the technical details are, which matters when an advisory is still thin on implementation detail. In practical terms, the confidence rating helps defenders distinguish between a fully understood bug and a more tentative report that still needs corroboration. That distinction is not academic; it changes how urgently organizations should treat the issue and how much trust they can place in the current attack narrative.
What makes this notable is the product area involved. Entra ID Entitlement Management is part of Microsoft’s identity governance stack, which is designed to control who gets access to what, for how long, and under what approval or review process. A spoofing flaw in that layer is not just a cosmetic identity problem; it can undermine the trust model that governs access packages, reviews, and lifecycle workflows. For enterprises, that means the issue could affect authorization decisions rather than mere sign-in experiences, and those are the decisions that often sit closest to sensitive data, applications, and privileged roles.
Microsoft Entra ID governance has become one of the central control planes in modern Microsoft-heavy environments. Instead of treating access as a one-time grant, entitlement management is meant to make access temporary, auditable, and subject to approval, which is why identity teams increasingly view it as a security function rather than an administrative convenience. The system is buent sprawl, enforce lifecycle discipline, and support least privilege in environments where roles and projects change constantly.
That design goal also explains why a spoofing vulnerability in this area deserves attention even before every technical detail is public. If an attacker can impersonate a trusted identity, object, approval artifact, or workflow state, then the governance layer may accept something that should have been rejected. In identity systems, “looks valid” can be almost as dangerous as is valid if downstream automast the wrong signal. The result can be access that appears authorized in logs but was never meant to exist.
This is part of a broader shift in Microsoft security thinking. The company has increasingly framed governance as a Zero Trust control rather than a compliance checkbox, tying entitlement management to least privilege, unified access, and continual review. That framing matters because the security stakes are no longer limited to human users logging in from managed devices. Modern identity systems now govern apps, services, workfloesses, so a failure in the entitlement layer can cascade far beyond a single account.
The Microsoft security ecosystem has also been shaped by repeated lessons about trust boundaries. Recent Entra-related incidents have shown that even sophisticated identity infrastructure can be vulnerable to cross-tenant abuse, impersonation, and authorization mistakes if the underlying policy logic is wrong. Those cases reinforced a hard lesson for defenders: authentication can be strong and still not be enough if the authorization model or identity mediation layer can be fooled.
At the same time, Microsoft’s vulnerability disclosure model has become more structured and more metadata-rich. The Security Update Guide is intended to tell defenders not only that a vulnerability exists, but also how certain Microsoft is about the report and what technical confidence should be placed in the entry. That is especially useful in cloud identity and governance products, where the impact can be severe even when the public write-up remains intentionally sparse.
For security teams, this kind of signal helps answer a question that appears simple but is operationally difficult: Is this a verified weakness or merely a plausible concern? The answer influences patch urgency, exposure review, compensating controls, and internal escalation. When Microsoft says the confidence is high, the practical assumption should be that the bug is not hypothetical and that attackers may eventually gain enough understanding to weaponize it.
The reason is simple: if you can influence the governance layer, you do not need to attack every application one by one. You can aim for the system that decides who gets access in the first place. That makes entitlement management a force multiplier for both defenders and attackers. If compromised, it can collapse least-privilege boundaries across multiple systems at once rather than exposing just one app.
Zero Trust assumes that identity, context, and authorization must be continuously validated. A spoofing weakness in Entra entitlement management directly challenges that idea by potentially convincing the platform that a request, user, or state transition is legitimate when it is not. In other words, the attack target is not just the system; it is the assumptions embedded in the system.
Another reason spoofing is dangerous in Entra is that modern identity systems rarely operate alone. They are connected to downstream SaaS apps, Microsoft 365 resources, privileged roles, and automated provisioning workflows. If the governance layer accepts a forged or misrepresented signal, the consequences can propagate very quickly. That is how a narrowly described vulnerability can become a broad enterprise risk.
Enterprises also have a larger attack surface because governance systems are often connected to hybrid identity, delegated administration, third-party SaaS apps, and internal approval chains. A spoofing flaw can therefore affect far more than one resource. In large arrow authorization error can spread through business processes that depend on trusted access events.
That is especially relevant for a spoofing issue inside entitlement management. The broader pattern across identity security is that attackers are increasingly willing to invest in policy abuse, token misuse, and trust boundary manipulation rather than rare-style payload delivery. Identity is attractive because it can provide durable access and blend into normal administrative workflows.
There is also a competitive implication here. Microsoft’s position in enterprise identity means its advisory posture influences the wider market, including third-party governance vendors and MSPs that integrate with Entra. When Microsoft strengthens or exposes weaknesses in its own governance model, the ecosystem tends to follow both technically and operationally. That is one reason the confidence metric matters: it shapes how the entire market calibrates response.
For CVE-2026-35431, the fact that Microsoft has published a specific advisory entry at all indicates that it is not treating the issue as a theoretical concern. Even though public technical detail remains limited, the disclosure itself communicates that the vendor believes the issue is real enough to track formally. That is the kind of signal security teams should act on even before external researchers publish deeper analysis.
Patch deployment is the obvious first move, but it should not be the only move. ew whether any access package logic, entitlement workflows, or review cycles depend on assumptions that a spoofing flaw could undermine. If a platform can be tricked into trusting a false signal, then reviewing the integrity of the decision path becomes as important as applying the update.
The broader story is bigger than one CVE. Microsoft is increasingly operating in a world where identity governance, access automation, and Zero Trust controls are all intertwined, which means flaws in that layer have platform-wide consequences. If CVE-2026-35431 proves anything, it is that the trust architecture behind access is now just as important as the access itself. That is the central lesson enterprises should carry forward.
Source: MSRC Security Update Guide - Microsoft Security Response Center
What makes this notable is the product area involved. Entra ID Entitlement Management is part of Microsoft’s identity governance stack, which is designed to control who gets access to what, for how long, and under what approval or review process. A spoofing flaw in that layer is not just a cosmetic identity problem; it can undermine the trust model that governs access packages, reviews, and lifecycle workflows. For enterprises, that means the issue could affect authorization decisions rather than mere sign-in experiences, and those are the decisions that often sit closest to sensitive data, applications, and privileged roles.
 Background
Background
Microsoft Entra ID governance has become one of the central control planes in modern Microsoft-heavy environments. Instead of treating access as a one-time grant, entitlement management is meant to make access temporary, auditable, and subject to approval, which is why identity teams increasingly view it as a security function rather than an administrative convenience. The system is buent sprawl, enforce lifecycle discipline, and support least privilege in environments where roles and projects change constantly.That design goal also explains why a spoofing vulnerability in this area deserves attention even before every technical detail is public. If an attacker can impersonate a trusted identity, object, approval artifact, or workflow state, then the governance layer may accept something that should have been rejected. In identity systems, “looks valid” can be almost as dangerous as is valid if downstream automast the wrong signal. The result can be access that appears authorized in logs but was never meant to exist.
This is part of a broader shift in Microsoft security thinking. The company has increasingly framed governance as a Zero Trust control rather than a compliance checkbox, tying entitlement management to least privilege, unified access, and continual review. That framing matters because the security stakes are no longer limited to human users logging in from managed devices. Modern identity systems now govern apps, services, workfloesses, so a failure in the entitlement layer can cascade far beyond a single account.
The Microsoft security ecosystem has also been shaped by repeated lessons about trust boundaries. Recent Entra-related incidents have shown that even sophisticated identity infrastructure can be vulnerable to cross-tenant abuse, impersonation, and authorization mistakes if the underlying policy logic is wrong. Those cases reinforced a hard lesson for defenders: authentication can be strong and still not be enough if the authorization model or identity mediation layer can be fooled.
At the same time, Microsoft’s vulnerability disclosure model has become more structured and more metadata-rich. The Security Update Guide is intended to tell defenders not only that a vulnerability exists, but also how certain Microsoft is about the report and what technical confidence should be placed in the entry. That is especially useful in cloud identity and governance products, where the impact can be severe even when the public write-up remains intentionally sparse.
What the Confidence Metric Really Signals
The confidence metric in Microsoft’s advisory framework is more than a bureaucratic label. It is effectively a statement about evidentiary strength: how certain Microsoft is that the vulnerability exists and how credible the details are that surround it. In a case like CVE-2026-35431, that matters because the public description is brief, yet the product area is security-critical. A high-confidence disclosure would suggest defenders can treat the issue as materially real even if exploitation mechanics are not yet fully public.For security teams, this kind of signal helps answer a question that appears simple but is operationally difficult: Is this a verified weakness or merely a plausible concern? The answer influences patch urgency, exposure review, compensating controls, and internal escalation. When Microsoft says the confidence is high, the practical assumption should be that the bug is not hypothetical and that attackers may eventually gain enough understanding to weaponize it.
Why confidence matters more
Identity and governance flaws often move faster than traditional software bugs once they are understood. That is because they can be used to alter access patterns without necessarily tripping classic endpoint defenses. A spoofing issue in entitlement management may not look like malware, but it can still produce the same business result: inappropriate access, privilege drift, or fraudulent approval state.- It can affect how access is granted rather than how software runs.
- It may leave fewer obvious forensic artifacts than a crash or exploit.
- It can be chained with phishing, token abuse, or role misuse.
- It may bypass assumptions built into review and approval workflows.
- It can be more damaging in SaaS environments than a local-only bug.
Why Entit High-Value Target
Entitlement management sits at a particularly sensitive point in the identity stack because it controls delegated access decisions. It can bundle groups, applications, SharePoint or other resources, and role assignments into governed access packages, creating a structured way to provision and review entitlements. That structure is supposed to reduce chaos, but it also creates a single poliers would love to manipulate.The reason is simple: if you can influence the governance layer, you do not need to attack every application one by one. You can aim for the system that decides who gets access in the first place. That makes entitlement management a force multiplier for both defenders and attackers. If compromised, it can collapse least-privilege boundaries across multiple systems at once rather than exposing just one app.
Governance bugs are not ordinary oofing bug in a consumer application might trick a user into trusting a fake dialog or a counterfeit sender. In entitlement management, spoofing can be far more consequential because trust is operationalized. Approval workflows, recertifications, and access package assignments may automatically propagate the spoofed signal into real permissions. That turns a visual or logical deception into a durable access problem.
- Access packages can encode multiple downstream permissions.
- Automated workflows reduce human scrutiny at scale.
- Identity governance is often integrated with HR and compliance systems.
- Misleading state can become persistentckly.
- The blast radius can extend across cloud and hybrid environments.
The Spoofing Problem in a Zero Trust World
Spoofing is often misunderstood as a comparatively mild class of vulnerability because it does not always imply code execution. That is a mistake in identity systems. When the object being spoofed is trust itself — an identity, an approval, a package, a workflow state, or a governance signal — the attacker may not need code execution to achieve serious business impact. ([msrc.micrc.microsoft.com/update-guide/vulnerability/CVE-2026-35431/))Zero Trust assumes that identity, context, and authorization must be continuously validated. A spoofing weakness in Entra entitlement management directly challenges that idea by potentially convincing the platform that a request, user, or state transition is legitimate when it is not. In other words, the attack target is not just the system; it is the assumptions embedded in the system.
What defenders should think about first
The first question is not simply whether the bug is exploitable, but what kind of trust artifact it might distort. Could it influence access package ownership? Could it misrepresent a subject, approver, or entitlement state? Could it make a review or request appear authorized when the underlying conditions are false? Those are the questions that determine whether the vulnerability is a nuisance, a policy bypass, or a serious governacrosoft.com](Security Update Guide - Microsoft Security Response Center))Another reason spoofing is dangerous in Entra is that modern identity systems rarely operate alone. They are connected to downstream SaaS apps, Microsoft 365 resources, privileged roles, and automated provisioning workflows. If the governance layer accepts a forged or misrepresented signal, the consequences can propagate very quickly. That is how a narrowly described vulnerability can become a broad enterprise risk.
Enterprise Impact Versus Consumer Impact
This vulnerability is fundamentally an enterprise risk, not a consumer nuisance. Most home users do not rely on Entitlement Management, but organizations using Microsoft Entra for access governance, app assignment, and lifecycle control may be directly exposed. That distinction matters because the likel personal account takeover and more about organizational access integrity.Enterprises also have a larger attack surface because governance systems are often connected to hybrid identity, delegated administration, third-party SaaS apps, and internal approval chains. A spoofing flaw can therefore affect far more than one resource. In large arrow authorization error can spread through business processes that depend on trusted access events.
How the blast radius can grow
If a spoofed entitlement event is accepted, the immediate effect may look minor: a wrong package, a misplaced approval, or an incorrect assignment. But those small misalignments can open the door to broader privilege accumulation. Once an attacker gets a foothold in the governance layer, the result can be persistent access drift that is hard to distinguish from routine administrative activity.- Access may be granted outside normal review paths.
- Revocation controls may not trigger as expected.
- Approval records may appear legitimate.
- Conditional policies may be bypassed indirectly.
- Incident responders may have to untangle policy state, not just logs.
How This Fits Microsoft’s Recent Identity Security Pattern
Microsoft Entra has been under sustained security scrutiny in the last year because identity has become the crown jewel of cloud control. Prior Entra-related disclosures have shown that bugs affecting token handling, cross-tenant behavior, and authorization logic can have outsized consequences. Those incidents shaped expectations: when Microsoft flags a vulnerability in the identity stack, defenders assume the impact could be broader than the first-line description suggests.That is especially relevant for a spoofing issue inside entitlement management. The broader pattern across identity security is that attackers are increasingly willing to invest in policy abuse, token misuse, and trust boundary manipulation rather than rare-style payload delivery. Identity is attractive because it can provide durable access and blend into normal administrative workflows.
The strategic lesson for defenders
The lesson is not merely “patch faster.” It is to treat identity governance as a live control surface that needs monitoring, review, and exposure mapping just like endpoints or servers. If a vulnerability can alter how access is awarded or represented, organizations should immediately assess whether their governance processes are resilient to false trust signals. That means looking beyond patch installation to entitlement design, approval controls, and audit integrity.There is also a competitive implication here. Microsoft’s position in enterprise identity means its advisory posture influences the wider market, including third-party governance vendors and MSPs that integrate with Entra. When Microsoft strengthens or exposes weaknesses in its own governance model, the ecosystem tends to follow both technically and operationally. That is one reason the confidence metric matters: it shapes how the entire market calibrates response.
What Microsoft’s Advisory Style Tells Us
Microsoft’s Security Update Guide is increasingly designed for machine consumption as much as human reading. That is important because organizations now ingest vulnerability data into patch orchestration, ticketing, and risk platforms. In that environment, confidence and classification fields matter almost as much as the short summary text. A small metadata field can decide whether a vulnerability is automatically escalated or placed in a watch queue.For CVE-2026-35431, the fact that Microsoft has published a specific advisory entry at all indicates that it is not treating the issue as a theoretical concern. Even though public technical detail remains limited, the disclosure itself communicates that the vendor believes the issue is real enough to track formally. That is the kind of signal security teams should act on even before external researchers publish deeper analysis.
Why limited detail is not a reason to wait
Some organizations become hesitant when an advisory lacks exploit chains, proof-of-concept code, or detailed root-cause explanation. That hesitation is understandable, but it can be dangerous in identity security. The absence of public internals often reflects responsible disclosure or ongoing remediation, not absence of risk. In the meantime, attackers may already be studying the same entry and looking for ways to turn a governance flaw into operational access.- Public scarcity can coexist with real risk.
- Governance flaws often have delayed but significant impact.
- Identity bugs are frequently chained with phishing or token abuse.
- Attackers may benefit from ambiguity more than defenders do.
- Patch prioritization should not wait for a full exploit narrative.
Operational Implications for Security Teams
Security operations teams should treat CVE-2026-35431 as a governance integrity issue first and a patching item second. The vulnerability appears to touch the part of Microsoft’s identity stack that determines how access is represented and administered, which means remediation is likely to involve both technical and procedural steps. That is particularly true in organizations that automate provisioning or rely on delegated administration.Patch deployment is the obvious first move, but it should not be the only move. ew whether any access package logic, entitlement workflows, or review cycles depend on assumptions that a spoofing flaw could undermine. If a platform can be tricked into trusting a false signal, then reviewing the integrity of the decision path becomes as important as applying the update.
A practical triage sequence
- Confirm whether the organization uses Entra ID Entitlement Management in production.
- Identify access packages, approvals, and workflows tied to privileged or sensitive access.
- Review whether any automation depends on the affected governance path.
- Prioritize patching and validation on the most sensitive tenants first.
- Reconcile recent entitlement changes with access-review expectations.
- Increase monitoring for unusual governance actions or unexpected assignments.
Strengths and Opportunities
Microsoft’s handling of this vulnerability reflects some real strengths in modern disclosure and identity design, even if the bug ihe advisory structure gives defenders a confidence signal, the product boundary is specific, and the issue lands in an area where most enterprises already know governance matters. That creates an opportunity to use the incident as a catalyst for better identity hygiene.- The advisory is specific enough to anchor response planning.
- The confidence metric helps prioritize without waiting for perfect detail.
- The product area is well understood by mature identity teams.
- Enterprises can fold remediation into broader governance reviews.
- Security teams can use this as a test of identity resilience.
- The issue may prompt tighter auditing of entitlement workflows.
- Microsoft’s structured disclosure model supports automation and triage.
Risks and Concerns
The most obvious risk is that a spoofing flaw in entitlement management could let attackers distort access decisions or create false trust artifacts inside the identity plane. Even if the public technical detail is limited, the impact profile of such a bug can be serious because it affects who gets access, not just how software behaves. That makes the issue especially dangerous in environments with automated workflows and delegated approvals.- Spoofing may bypass human review if the workflow trusts the wrong signal.
- Misleading identity state can persist longer than a one-time exploit.
- The issue could affect sensitive access packages and privileged roles.
- Hybrid and SaaS integrations may widen the blast radius.
- Forensics may be difficult if the artifact looks administratively legitimate.
- Delayed patching increases the chance of downstream abuse.
- Confidence in the governance layer itself may erode after disclosure.
at organizations may underestimate the vulnerability because it is categorized as spoofing rather than code execution. That would be a mistake. In identity and entitlement systems, spoofing is often an authorization problem in disguise, and authorization failures can be just as damaging as more obviously dangerous bugs.
Looking Ahead
The next few weeks will determine how much technical detail becomes public and whether external researchers can corroborate Microsoft’s entry with independent analysis. If more detail emerges, defenders will be able to better judge whether the weakness is limited to a narrow trust artifact or could affect larger entitlement workflows. Until then, the safest assumption is that the issue is real, sensitive, and worth immediate attention.The broader story is bigger than one CVE. Microsoft is increasingly operating in a world where identity governance, access automation, and Zero Trust controls are all intertwined, which means flaws in that layer have platform-wide consequences. If CVE-2026-35431 proves anything, it is that the trust architecture behind access is now just as important as the access itself. That is the central lesson enterprises should carry forward.
- Watch for Microsoft to publish richer technical clarification.
- Check whether identity governance tools or partner integrations are affected.
- Validate access packages and approval workflows tied to sensitive resources.
- Monitor for unusual entitlement changes or policy-state inconsistencies.
- Treat governance compromise as a serious incident scenario, not a niche concern.
Source: MSRC Security Update Guide - Microsoft Security Response Center