Google disclosed CVE-2026-7942 on May 6, 2026, as a medium-severity integer overflow in ANGLE affecting Chrome before version 148.0.7778.96, allowing a remote attacker to leak cross-origin data through a crafted HTML page. The bug is not the kind of headline-grabbing browser flaw that screams “remote code execution,” but that is precisely why it deserves attention. It sits in the modern browser’s graphics plumbing, where web content, GPU translation layers, and origin boundaries meet. For Windows users and enterprise admins, the lesson is simple: Chromium security is now part of the operating environment, whether the browser badge says Chrome, Edge, Brave, or something else.
The defining feature of CVE-2026-7942 is not its CVSS score. It is the combination of a memory-safety class, a graphics abstraction layer, and a cross-origin data leak. That combination puts the flaw in the long-running story of browser security: attackers do not need every bug to become code execution if the browser can be persuaded to reveal data that the web’s same-origin model was built to protect.
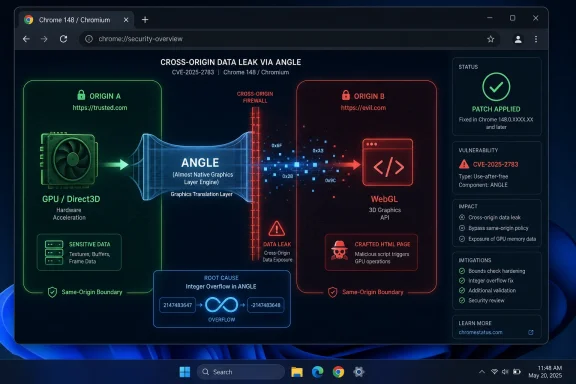
ANGLE is one of those components most users never knowingly touch. It translates graphics APIs so that WebGL and related browser graphics workloads can run across different operating systems and GPU stacks. In practical terms, it helps make rich browser graphics portable, smoothing over the differences between Direct3D on Windows, OpenGL, Vulkan, Metal, and other platform-specific pathways.
That portability is a security tradeoff. The web platform lets untrusted pages ask for increasingly capable graphics operations, while the browser must keep those pages boxed into strict security boundaries. A defect in that layer does not merely threaten pretty animations or 3D demos; it may expose state that should belong to another origin, another tab, or another security context.
The official description says the vulnerability allowed a remote attacker to leak cross-origin data via a crafted HTML page. That phrase is easy to skim past. But “cross-origin data” is browser security’s crown-jewel category: it is the stuff a page from one site should not be able to read from another site.
That is why a medium-severity Chrome bug can matter more operationally than a critical flaw in software buried on a handful of machines. Chrome and Chromium-derived browsers sit on nearly every endpoint class, from developer workstations to finance laptops to kiosk systems. If a flaw can be triggered by a crafted page, then exposure begins wherever users can browse.
CVE-2026-7942 does require user interaction under the CISA-ADP CVSS vector. That lowers the score, but it does not remove the enterprise risk. In browser security, “user interaction required” often means the victim has to visit a page, click a link, open a malicious ad path, or land on compromised content. That is not a heroic requirement for an attacker; it is the ordinary condition of the web.
The confidentiality impact is listed as low, with no integrity or availability impact in the CISA-ADP vector. That makes sense for a reported data leak rather than a takeover primitive. But security teams know the danger of treating confidentiality leaks as harmless simply because they do not crash a machine or drop a payload. A leak that helps defeat isolation can become a useful rung in a broader exploit chain.
That matters especially on Windows. Chrome’s graphics path has historically leaned on translation layers to deliver WebGL and accelerated rendering reliably across a vast hardware ecosystem. The same page may run on a corporate Dell laptop with Intel integrated graphics, a gaming rig with NVIDIA drivers, a Surface device, or a virtual desktop. ANGLE helps hide those differences from the web developer.
The security consequence is that browser graphics code becomes a broker between hostile input and privileged hardware-adjacent subsystems. A crafted HTML page is not supposed to have meaningful leverage over another origin’s data. Yet browser history is full of cases where performance features, graphics acceleration, speculative execution, or memory-management edge cases have opened gaps between the model and the implementation.
An integer overflow is a classic example of that gap. Software expects a calculation to stay inside a safe range; arithmetic wraps or exceeds what the program anticipated; the result drives allocation, indexing, size checks, or state transitions in a way the authors did not intend. In a graphics layer, that kind of mistake can be especially treacherous because dimensions, buffer sizes, texture formats, offsets, and pixel operations are everywhere.
CVE-2026-7942’s reported impact is a cross-origin data leak, not a sandbox escape. That distinction matters, but it should not lull anyone. The browser sandbox limits what compromised renderer code can do to the host system; the same-origin policy limits what one website can learn about another. Both are security boundaries, and both are valuable.
For attackers, data leaks are often not the end of the story. They can expose tokens, infer user state, weaken address-space layout randomization, assist phishing, or reveal application-specific secrets. Even when a browser vendor classifies a bug as medium, the surrounding environment may magnify its value.
This is especially true in enterprise web apps. Many internal systems were built under the assumption that browser origin boundaries are robust enough to carry sensitive workflows. If a browser bug weakens that model, the question is not merely whether the browser can be exploited; it is what sensitive services a logged-in user can reach when the malicious page runs.
That matters for patch prioritization. When users or admins ask whether this specific CVE is “bad enough” to justify urgency, they may be asking the wrong question. Browser updates are aggregate risk reducers. A single release can close critical renderer bugs, GPU issues, use-after-free flaws, policy bypasses, and information leaks all at once.
Google’s stable-channel cadence has trained many users to treat browser updates as background noise. The browser updates, relaunches, and resumes. That convenience is good security engineering, but it also dulls attention. When everything is automatic, nothing feels urgent until a zero-day banner appears.
Enterprise IT lives in the space between those two realities. Automatic updates are desirable, but controlled rollouts exist for reasons: compatibility, plugin behavior, regulated environments, virtual desktop images, and change windows. The challenge is to avoid letting “controlled” become a euphemism for “weeks behind.”
This has changed the rhythm of Windows security. Patch Tuesday is still important, but browser security does not wait politely for the second Tuesday of the month. Chromium vulnerabilities arrive through Chrome release notes, MSRC entries, Edge stable-channel updates, and vendor advisories on their own schedule.
For administrators, that creates a two-track discipline. Windows servicing handles the OS and Microsoft platform components; browser servicing handles one of the most exposed application stacks on the machine. Treating Edge as “part of Windows” for inventory purposes but not for update velocity is a mistake.
The same is true beyond Edge. Chromium’s reach extends into Electron applications, embedded browser controls, and alternative browsers that track upstream at different speeds. CVE-2026-7942 is framed as a Chrome vulnerability, but the strategic issue is the shared dependency graph. When Chromium moves, a large part of the desktop software ecosystem has to move with it.
CVSS is deliberately generic. It does not know whether the affected browser is used by a domain admin, a payroll clerk, a developer with production secrets, or a student on a locked-down Chromebook. It does not know whether your users keep SaaS admin consoles open all day or whether your environment enforces site isolation, hardened browser policies, and rapid restarts.
A medium vulnerability on a browser used for privileged workflows may outrank a high vulnerability in an obscure local tool. That does not mean teams should panic over every medium CVE. It means they should classify browser bugs by exposure, exploitability, and business context, not by the base score alone.
The absence of a known exploited-in-the-wild flag is also important. As of the disclosed details, CVE-2026-7942 is not described as an actively exploited zero-day. That should reduce emergency pressure. It should not justify complacency, because browser bug details are often restricted until users update, and exploitability can change as patches are diffed and researchers study the fix.
This creates friction for organizations that use CPE matching and NVD scoring as the backbone of vulnerability management. If the CPE data is loading, incomplete, or still being refined, some scanners and dashboards may underrepresent the issue. The user’s “Are we missing a CPE here?” line captures a real operational pain point: vulnerability records are not born fully formed.
The initial NIST analysis reportedly added a Chrome CPE for versions before 148.0.7778.96 and associated operating-system CPEs for Windows, Linux, and macOS. That reflects the desktop Chrome footprint, but it does not by itself solve the broader Chromium ecosystem question. Vulnerability managers still need to track Edge, Chromium packages, managed browser variants, and potentially embedded runtimes through their own vendor channels.
The practical answer is to treat vendor version guidance as authoritative for remediation. If Chrome before 148.0.7778.96 is affected, then Chrome endpoints below that line should move. If Edge publishes a corresponding Chromium security update, Edge endpoints should follow Microsoft’s stable-channel guidance. Waiting for every database to reach perfect enrichment is a luxury browser attackers do not grant.
For home users, the fix may be as simple as opening the browser menu, checking the version, and relaunching. For enterprise admins, the question is policy. Managed browsers can enforce update checks, set relaunch notification periods, and eventually force restarts. Those controls are often unpopular until a browser CVE becomes a board-level question.
The restart gap is particularly stubborn on machines that rarely reboot: developer workstations, shared kiosks, conference-room PCs, point-of-sale terminals, and virtual desktops. Users suspend laptops, restore sessions, and keep dozens of tabs alive for weeks. A green update icon or quiet background installer does not mean the old code is gone from memory.
This is where vulnerability management must meet user experience. If forced relaunch windows are too aggressive, users learn to resent security policy. If they are too loose, patch SLAs become fiction. The right answer is not theatrical urgency for every browser update, but a consistent standard: security releases get staged quickly and activated within a defined, short window.
But browser information disclosure bugs deserve a different instinct. The web is an information-routing machine. Every tab is a conversation with a server, every cookie is a credential-shaped object, every authenticated page is a potential data source, and every origin boundary is a promise about who can read what.
A cross-origin leak can be damaging even when it reveals only fragments. Attackers often compose fragments into decisions: whether a user is logged into a target service, whether an internal hostname exists, whether a document contains a marker, whether a token-shaped value can be inferred, or whether a victim belongs to a particular organization. Side channels and direct leaks both thrive on partial knowledge.
The public description of CVE-2026-7942 does not say what data could be leaked or under what exact conditions. That uncertainty cuts both ways. It should prevent exaggeration, but it should also prevent dismissal. Medium severity is not synonymous with trivial.
ANGLE exists because the web’s graphics ambitions exceeded what a single platform API could provide. That is not a criticism. Without layers like ANGLE, browser graphics would be more fragmented, less reliable, and less capable. The component is a success story of compatibility engineering.
Compatibility engineering, however, creates translation surfaces. Translation surfaces are where assumptions go to die. A value safe in one API model may need different bounds in another. A format conversion may introduce unexpected dimensions. A driver workaround may preserve functionality while complicating invariants.
Integer overflows are especially revealing in this context. They are not exotic. They are old, well-understood, and still persistent because complex software is full of arithmetic that security depends on indirectly. In a browser graphics stack, the difference between “this size is valid” and “this size wrapped” can be the difference between isolation and leakage.
For organizations, the interesting work begins after the patch exists. Admins need to know which browsers are installed, which channel they are on, which version is running, whether relaunch has occurred, and whether unmanaged browsers are hiding outside the standard software inventory. Chrome installed per-user under a profile can be just as relevant as the managed system installation everyone remembers.
Edge adds another layer. Some organizations manage Edge with Microsoft Intune, Group Policy, Configuration Manager, or third-party endpoint tools. Others assume Windows Update or Edge Update will take care of it. That assumption may be reasonable in many environments, but it should still be verified with telemetry.
The worst patch outcome is a dashboard that says “updated” because the installer landed while the process table says users are still running the vulnerable build. Browser patching has to measure execution state, not just package state. In a world where browsers restore sessions indefinitely, the distinction matters.
The first step is recognizing Chromium as a platform dependency. Chrome is one manifestation. Edge is another. Electron apps and embedded browser runtimes complicate the picture further, though they do not necessarily inherit every Chrome CVE in the same way or on the same schedule. The point is not to flatten all Chromium-based software into one bucket, but to stop pretending the bucket does not exist.
The second step is channel discipline. Stable, Extended Stable, Beta, Dev, and Canary channels serve different purposes. Enterprises often use Extended Stable to reduce change frequency, but security updates still arrive. Admins should know which endpoints are on which channel and why.
The third step is relaunch enforcement. Browser vendors have built mature enterprise policies for update notifications and forced relaunches because they know background updating alone is insufficient. Those controls should be tuned before a high-profile zero-day forces hasty policy changes.
Finally, security teams should map browser use to privilege. A privileged access workstation used for cloud administration should not be treated like a casual browsing machine. If the browser is the console for production, identity, finance, or HR, browser security belongs in the same risk conversation as VPNs and endpoint detection.
The issue tracker reference is permission-restricted, as is common for Chromium bugs soon after disclosure. That means defenders cannot yet inspect the full technical trail. They have to make decisions with partial public data. This asymmetry is uncomfortable but normal: vendors limit details until a critical mass of users has patched, while attackers can still diff code changes and hunt for the bug class.
The CWE listed in the user-provided detail is also worth noticing. It mentions external control of an assumed-immutable web parameter, while other vulnerability databases may classify the issue under integer overflow. That mismatch is not unusual in early vulnerability metadata. Weakness enumeration is useful, but it is not a substitute for reading the vendor description and understanding the affected component.
This is why mature vulnerability management resists fetishizing any single field. CVSS, CWE, CPE, EPSS, KEV status, vendor severity, and scanner plugin output all tell part of the story. Browser CVEs demand synthesis because the exposure is broad and the public detail is often intentionally sparse.
That does not mean treating every Chrome release as a red-alert incident. Alert fatigue is real, and browser vendors ship security fixes constantly. But it does mean recognizing that the browser has become too central to leave in the unmanaged gray zone between desktop engineering and security operations.
A good browser governance model answers a few basic questions. Who owns Chrome and Edge configuration? Who approves extension policy? Who can force relaunch? Who validates version compliance after a security release? Who tracks unmanaged Chromium derivatives? Who decides when a browser CVE requires user communication?
Those questions sound bureaucratic until they prevent confusion. When a Chrome stable update patches 100-plus vulnerabilities, including a medium ANGLE data leak and several more severe issues, the organization should not be inventing its response in Slack. It should be executing a familiar routine.
That is exactly why it is a useful test. Security programs prove themselves not only in the spectacular incidents but in the ordinary cadence of closing exposed paths before they become interesting to attackers. A crafted HTML page, low attack complexity, no privileges required, and a browser component present on millions of endpoints is not nothing.
The best response is proportionate urgency. Patch quickly. Verify relaunch. Confirm managed coverage across Chrome and Chromium-based Edge where applicable. Watch for downstream vendor updates. Do not overstate the bug, but do not let the word “medium” become a sedative.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Medium Bug in the Place Browsers Cannot Afford to Be Soft
A Medium Bug in the Place Browsers Cannot Afford to Be Soft
The defining feature of CVE-2026-7942 is not its CVSS score. It is the combination of a memory-safety class, a graphics abstraction layer, and a cross-origin data leak. That combination puts the flaw in the long-running story of browser security: attackers do not need every bug to become code execution if the browser can be persuaded to reveal data that the web’s same-origin model was built to protect.ANGLE is one of those components most users never knowingly touch. It translates graphics APIs so that WebGL and related browser graphics workloads can run across different operating systems and GPU stacks. In practical terms, it helps make rich browser graphics portable, smoothing over the differences between Direct3D on Windows, OpenGL, Vulkan, Metal, and other platform-specific pathways.
That portability is a security tradeoff. The web platform lets untrusted pages ask for increasingly capable graphics operations, while the browser must keep those pages boxed into strict security boundaries. A defect in that layer does not merely threaten pretty animations or 3D demos; it may expose state that should belong to another origin, another tab, or another security context.
The official description says the vulnerability allowed a remote attacker to leak cross-origin data via a crafted HTML page. That phrase is easy to skim past. But “cross-origin data” is browser security’s crown-jewel category: it is the stuff a page from one site should not be able to read from another site.
The Browser Is the Perimeter Now, Whether IT Likes It or Not
There was a time when browser patching felt like workstation hygiene. Today it is perimeter management. The browser is where identity providers, SaaS dashboards, admin consoles, password managers, device enrollment portals, cloud storage, line-of-business apps, and helpdesk tooling all converge.That is why a medium-severity Chrome bug can matter more operationally than a critical flaw in software buried on a handful of machines. Chrome and Chromium-derived browsers sit on nearly every endpoint class, from developer workstations to finance laptops to kiosk systems. If a flaw can be triggered by a crafted page, then exposure begins wherever users can browse.
CVE-2026-7942 does require user interaction under the CISA-ADP CVSS vector. That lowers the score, but it does not remove the enterprise risk. In browser security, “user interaction required” often means the victim has to visit a page, click a link, open a malicious ad path, or land on compromised content. That is not a heroic requirement for an attacker; it is the ordinary condition of the web.
The confidentiality impact is listed as low, with no integrity or availability impact in the CISA-ADP vector. That makes sense for a reported data leak rather than a takeover primitive. But security teams know the danger of treating confidentiality leaks as harmless simply because they do not crash a machine or drop a payload. A leak that helps defeat isolation can become a useful rung in a broader exploit chain.
ANGLE Shows Why “Just JavaScript” Was Always a Comforting Fiction
Modern browsers are not JavaScript interpreters with address bars. They are operating systems in miniature, with process isolation, JIT compilers, video pipelines, PDF renderers, network stacks, font parsers, GPU command buffers, and storage subsystems. ANGLE is part of that machinery, and its job is deceptively ambitious: make graphics code behave consistently across incompatible platform graphics worlds.That matters especially on Windows. Chrome’s graphics path has historically leaned on translation layers to deliver WebGL and accelerated rendering reliably across a vast hardware ecosystem. The same page may run on a corporate Dell laptop with Intel integrated graphics, a gaming rig with NVIDIA drivers, a Surface device, or a virtual desktop. ANGLE helps hide those differences from the web developer.
The security consequence is that browser graphics code becomes a broker between hostile input and privileged hardware-adjacent subsystems. A crafted HTML page is not supposed to have meaningful leverage over another origin’s data. Yet browser history is full of cases where performance features, graphics acceleration, speculative execution, or memory-management edge cases have opened gaps between the model and the implementation.
An integer overflow is a classic example of that gap. Software expects a calculation to stay inside a safe range; arithmetic wraps or exceeds what the program anticipated; the result drives allocation, indexing, size checks, or state transitions in a way the authors did not intend. In a graphics layer, that kind of mistake can be especially treacherous because dimensions, buffer sizes, texture formats, offsets, and pixel operations are everywhere.
The Same-Origin Policy Is Not a Feature; It Is the Web’s Constitution
The phrase same-origin policy can sound academic, but it is the rule that lets users remain logged into multiple services while browsing elsewhere. A page from one origin should not be able to read sensitive responses, private documents, authentication state, or application data from another origin. Without that boundary, the web collapses into a single shared memory space with better fonts.CVE-2026-7942’s reported impact is a cross-origin data leak, not a sandbox escape. That distinction matters, but it should not lull anyone. The browser sandbox limits what compromised renderer code can do to the host system; the same-origin policy limits what one website can learn about another. Both are security boundaries, and both are valuable.
For attackers, data leaks are often not the end of the story. They can expose tokens, infer user state, weaken address-space layout randomization, assist phishing, or reveal application-specific secrets. Even when a browser vendor classifies a bug as medium, the surrounding environment may magnify its value.
This is especially true in enterprise web apps. Many internal systems were built under the assumption that browser origin boundaries are robust enough to carry sensitive workflows. If a browser bug weakens that model, the question is not merely whether the browser can be exploited; it is what sensitive services a logged-in user can reach when the malicious page runs.
Chrome 148 Was Not a One-Bug Emergency
The update containing the fix, Chrome 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS, was part of a much larger stable-channel security release. Reporting around the release noted more than 100 security fixes, including several higher-severity issues. CVE-2026-7942 is therefore one item in a broader patch bundle, not an isolated event.That matters for patch prioritization. When users or admins ask whether this specific CVE is “bad enough” to justify urgency, they may be asking the wrong question. Browser updates are aggregate risk reducers. A single release can close critical renderer bugs, GPU issues, use-after-free flaws, policy bypasses, and information leaks all at once.
Google’s stable-channel cadence has trained many users to treat browser updates as background noise. The browser updates, relaunches, and resumes. That convenience is good security engineering, but it also dulls attention. When everything is automatic, nothing feels urgent until a zero-day banner appears.
Enterprise IT lives in the space between those two realities. Automatic updates are desirable, but controlled rollouts exist for reasons: compatibility, plugin behavior, regulated environments, virtual desktop images, and change windows. The challenge is to avoid letting “controlled” become a euphemism for “weeks behind.”
Microsoft Edge Inherits the Chromium Clock
The user-provided MSRC entry is a reminder that Microsoft is downstream of Chromium for many browser vulnerabilities. Edge is not Chrome, but modern Edge is Chromium-based, and that means a large share of its security exposure follows the Chromium project’s component map. If a flaw lands in shared Chromium code, Microsoft has to assess and ship accordingly.This has changed the rhythm of Windows security. Patch Tuesday is still important, but browser security does not wait politely for the second Tuesday of the month. Chromium vulnerabilities arrive through Chrome release notes, MSRC entries, Edge stable-channel updates, and vendor advisories on their own schedule.
For administrators, that creates a two-track discipline. Windows servicing handles the OS and Microsoft platform components; browser servicing handles one of the most exposed application stacks on the machine. Treating Edge as “part of Windows” for inventory purposes but not for update velocity is a mistake.
The same is true beyond Edge. Chromium’s reach extends into Electron applications, embedded browser controls, and alternative browsers that track upstream at different speeds. CVE-2026-7942 is framed as a Chrome vulnerability, but the strategic issue is the shared dependency graph. When Chromium moves, a large part of the desktop software ecosystem has to move with it.
CVSS Helps, but It Does Not Know Your Users
CISA-ADP assigned a CVSS 3.1 base score of 4.3, with network attack vector, low attack complexity, no privileges required, user interaction required, unchanged scope, low confidentiality impact, and no integrity or availability impact. That is a coherent score for the public description. It is also not a complete risk decision.CVSS is deliberately generic. It does not know whether the affected browser is used by a domain admin, a payroll clerk, a developer with production secrets, or a student on a locked-down Chromebook. It does not know whether your users keep SaaS admin consoles open all day or whether your environment enforces site isolation, hardened browser policies, and rapid restarts.
A medium vulnerability on a browser used for privileged workflows may outrank a high vulnerability in an obscure local tool. That does not mean teams should panic over every medium CVE. It means they should classify browser bugs by exposure, exploitability, and business context, not by the base score alone.
The absence of a known exploited-in-the-wild flag is also important. As of the disclosed details, CVE-2026-7942 is not described as an actively exploited zero-day. That should reduce emergency pressure. It should not justify complacency, because browser bug details are often restricted until users update, and exploitability can change as patches are diffed and researchers study the fix.
NVD’s Metadata Lag Is Not an Excuse to Wait
The NVD record described enrichment activity and showed that NIST had not yet provided its own CVSS assessment at the time of the entry, while CISA-ADP had contributed a CVSS vector. That is increasingly common in the vulnerability-management pipeline. The CVE can be public, vendor guidance can be available, CISA enrichment can exist, and NVD analysis can still be incomplete.This creates friction for organizations that use CPE matching and NVD scoring as the backbone of vulnerability management. If the CPE data is loading, incomplete, or still being refined, some scanners and dashboards may underrepresent the issue. The user’s “Are we missing a CPE here?” line captures a real operational pain point: vulnerability records are not born fully formed.
The initial NIST analysis reportedly added a Chrome CPE for versions before 148.0.7778.96 and associated operating-system CPEs for Windows, Linux, and macOS. That reflects the desktop Chrome footprint, but it does not by itself solve the broader Chromium ecosystem question. Vulnerability managers still need to track Edge, Chromium packages, managed browser variants, and potentially embedded runtimes through their own vendor channels.
The practical answer is to treat vendor version guidance as authoritative for remediation. If Chrome before 148.0.7778.96 is affected, then Chrome endpoints below that line should move. If Edge publishes a corresponding Chromium security update, Edge endpoints should follow Microsoft’s stable-channel guidance. Waiting for every database to reach perfect enrichment is a luxury browser attackers do not grant.
The Quiet Risk Is the Restart Gap
Chrome and Edge are good at downloading updates. They are less magical at forcing users to restart at the right time without disrupting work. That creates the restart gap: the period when an update is staged but the vulnerable browser process is still running.For home users, the fix may be as simple as opening the browser menu, checking the version, and relaunching. For enterprise admins, the question is policy. Managed browsers can enforce update checks, set relaunch notification periods, and eventually force restarts. Those controls are often unpopular until a browser CVE becomes a board-level question.
The restart gap is particularly stubborn on machines that rarely reboot: developer workstations, shared kiosks, conference-room PCs, point-of-sale terminals, and virtual desktops. Users suspend laptops, restore sessions, and keep dozens of tabs alive for weeks. A green update icon or quiet background installer does not mean the old code is gone from memory.
This is where vulnerability management must meet user experience. If forced relaunch windows are too aggressive, users learn to resent security policy. If they are too loose, patch SLAs become fiction. The right answer is not theatrical urgency for every browser update, but a consistent standard: security releases get staged quickly and activated within a defined, short window.
Information Disclosure Still Counts as a Breach Ingredient
Security teams sometimes reserve their strongest reactions for remote code execution, privilege escalation, and sandbox escape. That hierarchy is understandable. Those classes map neatly to compromise narratives. Information disclosure can feel softer, especially when the public description offers no exploit details.But browser information disclosure bugs deserve a different instinct. The web is an information-routing machine. Every tab is a conversation with a server, every cookie is a credential-shaped object, every authenticated page is a potential data source, and every origin boundary is a promise about who can read what.
A cross-origin leak can be damaging even when it reveals only fragments. Attackers often compose fragments into decisions: whether a user is logged into a target service, whether an internal hostname exists, whether a document contains a marker, whether a token-shaped value can be inferred, or whether a victim belongs to a particular organization. Side channels and direct leaks both thrive on partial knowledge.
The public description of CVE-2026-7942 does not say what data could be leaked or under what exact conditions. That uncertainty cuts both ways. It should prevent exaggeration, but it should also prevent dismissal. Medium severity is not synonymous with trivial.
Graphics Acceleration Keeps Reopening the Same Argument
Every few years, browser security returns to the same uncomfortable bargain: users want fast graphics, smooth video, web apps that feel native, GPU acceleration, and increasingly complex client-side workloads. Security architects want small attack surfaces, simple parsers, deterministic isolation, and minimal hardware exposure. The modern browser gives us both, then spends the rest of its life reconciling the conflict.ANGLE exists because the web’s graphics ambitions exceeded what a single platform API could provide. That is not a criticism. Without layers like ANGLE, browser graphics would be more fragmented, less reliable, and less capable. The component is a success story of compatibility engineering.
Compatibility engineering, however, creates translation surfaces. Translation surfaces are where assumptions go to die. A value safe in one API model may need different bounds in another. A format conversion may introduce unexpected dimensions. A driver workaround may preserve functionality while complicating invariants.
Integer overflows are especially revealing in this context. They are not exotic. They are old, well-understood, and still persistent because complex software is full of arithmetic that security depends on indirectly. In a browser graphics stack, the difference between “this size is valid” and “this size wrapped” can be the difference between isolation and leakage.
The Patch Is Easy; Proving Coverage Is the Hard Part
For individual users, remediation is almost boring: update Chrome to 148.0.7778.96 or later, or the corresponding 148.0.7778.96/97 build on Windows and macOS, and relaunch. The browser’s About page should trigger an update check if automatic updating has not already done its work. That is the simple part.For organizations, the interesting work begins after the patch exists. Admins need to know which browsers are installed, which channel they are on, which version is running, whether relaunch has occurred, and whether unmanaged browsers are hiding outside the standard software inventory. Chrome installed per-user under a profile can be just as relevant as the managed system installation everyone remembers.
Edge adds another layer. Some organizations manage Edge with Microsoft Intune, Group Policy, Configuration Manager, or third-party endpoint tools. Others assume Windows Update or Edge Update will take care of it. That assumption may be reasonable in many environments, but it should still be verified with telemetry.
The worst patch outcome is a dashboard that says “updated” because the installer landed while the process table says users are still running the vulnerable build. Browser patching has to measure execution state, not just package state. In a world where browsers restore sessions indefinitely, the distinction matters.
Security Teams Need a Chromium Playbook, Not a Chrome Habit
CVE-2026-7942 is a useful forcing function for a broader question: does the organization have a Chromium playbook, or does it merely hope Chrome updates itself? The difference shows up during every browser security release. A playbook defines ownership, inventory, channels, test rings, relaunch policy, exception handling, and executive communication before the CVE lands.The first step is recognizing Chromium as a platform dependency. Chrome is one manifestation. Edge is another. Electron apps and embedded browser runtimes complicate the picture further, though they do not necessarily inherit every Chrome CVE in the same way or on the same schedule. The point is not to flatten all Chromium-based software into one bucket, but to stop pretending the bucket does not exist.
The second step is channel discipline. Stable, Extended Stable, Beta, Dev, and Canary channels serve different purposes. Enterprises often use Extended Stable to reduce change frequency, but security updates still arrive. Admins should know which endpoints are on which channel and why.
The third step is relaunch enforcement. Browser vendors have built mature enterprise policies for update notifications and forced relaunches because they know background updating alone is insufficient. Those controls should be tuned before a high-profile zero-day forces hasty policy changes.
Finally, security teams should map browser use to privilege. A privileged access workstation used for cloud administration should not be treated like a casual browsing machine. If the browser is the console for production, identity, finance, or HR, browser security belongs in the same risk conversation as VPNs and endpoint detection.
The Database Record Is Only the Start of the Story
The CVE entry gives us the skeleton: CVE-2026-7942, integer overflow, ANGLE, Chrome before 148.0.7778.96, crafted HTML page, cross-origin data leak, medium severity. That is enough to act. It is not enough to understand the full operational story.The issue tracker reference is permission-restricted, as is common for Chromium bugs soon after disclosure. That means defenders cannot yet inspect the full technical trail. They have to make decisions with partial public data. This asymmetry is uncomfortable but normal: vendors limit details until a critical mass of users has patched, while attackers can still diff code changes and hunt for the bug class.
The CWE listed in the user-provided detail is also worth noticing. It mentions external control of an assumed-immutable web parameter, while other vulnerability databases may classify the issue under integer overflow. That mismatch is not unusual in early vulnerability metadata. Weakness enumeration is useful, but it is not a substitute for reading the vendor description and understanding the affected component.
This is why mature vulnerability management resists fetishizing any single field. CVSS, CWE, CPE, EPSS, KEV status, vendor severity, and scanner plugin output all tell part of the story. Browser CVEs demand synthesis because the exposure is broad and the public detail is often intentionally sparse.
The Real Fix Is Faster Browser Governance
The practical remediation for CVE-2026-7942 is straightforward. The strategic remediation is governance. Organizations need browser update processes that are fast by default, observable by design, and capable of escalating when a routine medium bug becomes part of a larger exploit chain.That does not mean treating every Chrome release as a red-alert incident. Alert fatigue is real, and browser vendors ship security fixes constantly. But it does mean recognizing that the browser has become too central to leave in the unmanaged gray zone between desktop engineering and security operations.
A good browser governance model answers a few basic questions. Who owns Chrome and Edge configuration? Who approves extension policy? Who can force relaunch? Who validates version compliance after a security release? Who tracks unmanaged Chromium derivatives? Who decides when a browser CVE requires user communication?
Those questions sound bureaucratic until they prevent confusion. When a Chrome stable update patches 100-plus vulnerabilities, including a medium ANGLE data leak and several more severe issues, the organization should not be inventing its response in Slack. It should be executing a familiar routine.
This ANGLE Bug Is Small Enough to Ignore and Important Enough Not To
CVE-2026-7942 will probably not be remembered as the defining browser vulnerability of 2026. It has no public active-exploitation claim in the supplied details, no remote-code-execution label, and no dramatic sandbox-escape language. It is a medium-severity information disclosure bug in a component many users have never heard of.That is exactly why it is a useful test. Security programs prove themselves not only in the spectacular incidents but in the ordinary cadence of closing exposed paths before they become interesting to attackers. A crafted HTML page, low attack complexity, no privileges required, and a browser component present on millions of endpoints is not nothing.
The best response is proportionate urgency. Patch quickly. Verify relaunch. Confirm managed coverage across Chrome and Chromium-based Edge where applicable. Watch for downstream vendor updates. Do not overstate the bug, but do not let the word “medium” become a sedative.
Chrome 148 Turns a Quiet CVE Into a Practical Checklist
CVE-2026-7942 is less a panic button than a reminder that browser security is operational security. The concrete steps are familiar, but familiarity is not the same as completion.- Chrome installations older than 148.0.7778.96 should be updated to a fixed build, with Windows and macOS fleets accounting for the 148.0.7778.96/97 stable release line.
- Microsoft Edge administrators should track Microsoft’s Chromium-based Edge security releases rather than assuming Chrome advisories are irrelevant to Windows environments.
- Vulnerability teams should not wait for perfect NVD enrichment or scanner CPE matching before acting on clear vendor version guidance.
- Browser update compliance should measure whether users have relaunched into the fixed build, not merely whether an installer has downloaded.
- Higher-risk users, including admins and staff who live inside sensitive SaaS consoles, should sit in faster browser update rings than general-purpose endpoints.
- Information-disclosure bugs that cross origin boundaries should be treated as meaningful security boundary failures, even when their standalone CVSS score is moderate.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center