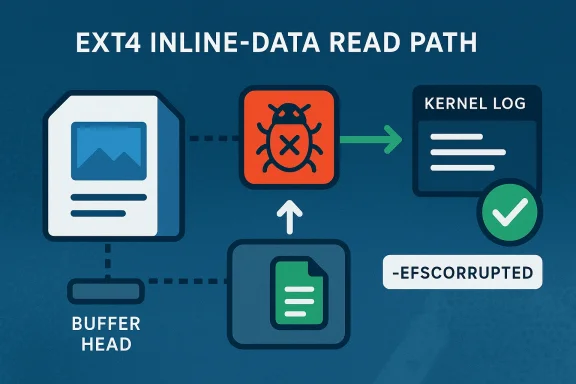
In the Linux kernel’s ext4 filesystem, a small logic change has been turned into a security-relevant reliability fix: the code path that reads inline data now avoids a kernel-panic-style BUG_ON() when the inline payload is larger than a page. Instead of crashing the system, the kernel now logs the corruption, releases the buffer head to avoid leaking resources, and returns -EFSCORRUPTED so the filesystem can fail safely. That shift matters because it converts a hard stop into a recoverable error, and it does so in one of the most sensitive places in storage code: the path that turns on-disk corruption into in-memory execution.
For Windows and Linux administrators, the practical message is simple: this is not just a cosmetic cleanup. The issue is tracked as CVE-2026-31451, was published on April 22, 2026, and is already present in Microsoft’s update guide alongside the Linux kernel references that describe the upstream fix. The vulnerability description states plainly that the patch replaces a crash condition with proper error handling in
That complexity is where the risk emerges. In the old behavior, if inline data unexpectedly exceeded PAGE_SIZE, the code hit a BUG_ON() assertion in
The upstream fix is therefore as much about philosophy as code. Modern kernel hardening increasingly tries to replace fatal assertions with explicit checks, error logging, and controlled unwinding. The ext4 change follows that pattern: detect the impossible condition, report it as filesystem corruption, release any held resources, and return an error that callers can handle.
There is also a clear operational reason this matters. Filesystems are routinely exposed to imperfect shutdowns, storage errors, fault injection, and adversarial test cases. In those environments, a panic is not merely a crash; it can become an availability event that affects clusters, virtual machines, container hosts, and recovery automation. A safe error return, by contrast, lets the system isolate the damage and keep running.
For Microsoft’s security ecosystem, the publication of a Linux kernel CVE in the update guide reflects a broader reality: kernel-level storage bugs matter across cloud, virtualization, and hybrid environments. Even when the vulnerable component is upstream Linux, it can affect the support posture of products and platforms that rely on Linux kernels under the hood. That is why Microsoft tracks it alongside other security-relevant issues, even when the underlying fix comes from kernel.org and the ext4 maintainers.
At the code level, the change is straightforward but important. The vulnerable path assumed that inline data would never exceed a page, and it used BUG_ON() to enforce that assumption. The patch replaces that assertion with a proper conditional failure path, so the kernel now treats oversized inline data as corruption rather than as an invariant violation worthy of immediate panic.
The code also releases the buffer head before returning. That detail sounds mundane, but in kernel code, small cleanup steps are critical. Without them, the transition from crash-on-corruption to error-on-corruption could create new leaks or undefined behavior. The fix therefore addresses both safety and hygiene.
The result is a more mature failure mode:
That defensive posture was not defensive enough before this fix. A BUG_ON() is acceptable only when the condition truly indicates an unrecoverable kernel invariant failure. Here, the maintainers judged that the situation should be handled as corrupted input instead, which aligns better with the realities of storage systems.
The ext4 change fits the broader Linux trend toward fail closed, not fail hard. If corruption is detected, the right outcome is to mark the inode or filesystem as corrupted, stop relying on the bad state, and let higher layers decide whether to remount, repair, or continue in read-only mode.
That is not just a theoretical ideal. It is the same design logic behind many kernel fixes that convert crashes into explicit errors. The patch acknowledges that filesystem corruption is not an abstract logic bug; it is a runtime condition that should be handled as gracefully as possible.
That is why replacing a BUG_ON with error handling is more than defensive coding. It reduces the blast radius of corruption. Instead of turning one damaged inode into a machine-wide outage, the kernel can confine the damage to the relevant filesystem object and continue serving unaffected workloads.
That has a second-order benefit: downstream vendors can align their own updates with the upstream fix rather than engineering separate mitigation logic. In practice, that speeds up patch adoption for enterprise Linux distributions, cloud images, and hypervisor stacks.
A few practical implications follow:
The ext4 fix reduces that risk by ensuring corruption is reported rather than detonated. It does not eliminate the corruption itself, but it transforms the response into one that administrators can script around, monitor, and recover from.
The corrected ext4 path gives operators better odds of surviving a bad inode without taking down the machine. That may not sound dramatic, but in hyperscale terms, small reduction in crash probability translates into large improvements in fleet reliability.
The distinction is important. In consumer terms, the new behavior is less catastrophic, not magically safe. A corrupted inode still represents a problem that should be investigated, but the system itself will be better able to stay alive through it.
That can reduce troubleshooting time and improve the odds that the real issue is fixed rather than masked by a reboot. It also means users are less likely to blame a general OS defect when the actual culprit is a damaged filesystem structure.
That is why the change here feels familiar. It is not a dramatic redesign; it is a correction to a failure assumption. But those corrections are often the most important ones, because they reduce the number of ways corrupted metadata can crash a live system.
The lesson for admins is simple: don’t confuse “rare” with “safe.” If a code path can be reached through corrupted metadata, fuzzing will eventually find it, and real hardware failures can too.
The next thing to watch is how quickly the fix reaches downstream kernels and vendor builds. In many environments, the real security question is not whether the patch exists upstream, but whether it has been incorporated into the exact kernel your fleet runs today. That gap is where exposure lives.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
For Windows and Linux administrators, the practical message is simple: this is not just a cosmetic cleanup. The issue is tracked as CVE-2026-31451, was published on April 22, 2026, and is already present in Microsoft’s update guide alongside the Linux kernel references that describe the upstream fix. The vulnerability description states plainly that the patch replaces a crash condition with proper error handling in
ext4_read_inline_folio, which is exactly the kind of change that improves resilience under filesystem corruption, fuzzing, or malformed metadata. xt4 filesystem has long balanced performance, compatibility, and a relatively conservative storage model. One of its more specialized features is inline data, which stores very small file contents directly inside the inode rather than allocating a separate data block. That optimization reduces I/O for tiny files, but it also adds complexity to the read and write paths, because the filesystem must decide when data still fits inside the inode and when it needs to spill into regular blocks.That complexity is where the risk emerges. In the old behavior, if inline data unexpectedly exceeded PAGE_SIZE, the code hit a BUG_ON() assertion in
ext4_read_inline_folio. In kernel terms, that is not a graceful error path; it is an intentional stop-the-world failure. A malformed or corrupted filesystem state therefore had the power to bring down the entire system, which is precisely the sort of failure mode security engineers dislike most.The upstream fix is therefore as much about philosophy as code. Modern kernel hardening increasingly tries to replace fatal assertions with explicit checks, error logging, and controlled unwinding. The ext4 change follows that pattern: detect the impossible condition, report it as filesystem corruption, release any held resources, and return an error that callers can handle.
There is also a clear operational reason this matters. Filesystems are routinely exposed to imperfect shutdowns, storage errors, fault injection, and adversarial test cases. In those environments, a panic is not merely a crash; it can become an availability event that affects clusters, virtual machines, container hosts, and recovery automation. A safe error return, by contrast, lets the system isolate the damage and keep running.
For Microsoft’s security ecosystem, the publication of a Linux kernel CVE in the update guide reflects a broader reality: kernel-level storage bugs matter across cloud, virtualization, and hybrid environments. Even when the vulnerable component is upstream Linux, it can affect the support posture of products and platforms that rely on Linux kernels under the hood. That is why Microsoft tracks it alongside other security-relevant issues, even when the underlying fix comes from kernel.org and the ext4 maintainers.
 What the
What the
At the code level, the change is straightforward but important. The vulnerable path assumed that inline data would never exceed a page, and it used BUG_ON() to enforce that assumption. The patch replaces that assertion with a proper conditional failure path, so the kernel now treats oversized inline data as corruption rather than as an invariant violation worthy of immediate panic.From panic to controlled failure
The most significant change is the error-handling model. Instead of asserting, ext4 now records the problem viaext4_error_inode() and returns -EFSCORRUPTED. That matters because -EFSCORRUPTED tells upper layers and userspace tools that the filesystem metadata is damaged, not that the operating system itself is unstable.The code also releases the buffer head before returning. That detail sounds mundane, but in kernel code, small cleanup steps are critical. Without them, the transition from crash-on-corruption to error-on-corruption could create new leaks or undefined behavior. The fix therefore addresses both safety and hygiene.
The result is a more mature failure mode:
- The system keeps running.
- The filesystem reports the corruption.
- The damaged inode is not silently trusted.
- Resources are cleaned up before exit.
Why inline data is special
Inline data is optimized for tiny files, and that makes it a performance feature with sharp edges. The filesystem is trying to conserve space and avoid block allocation, so it stores content in the inode itself. When data size and metadata accounting become inconsistent, the read path is forced into a defensive posture.That defensive posture was not defensive enough before this fix. A BUG_ON() is acceptable only when the condition truly indicates an unrecoverable kernel invariant failure. Here, the maintainers judged that the situation should be handled as corrupted input instead, which aligns better with the realities of storage systems.
- Inline data is a space-saving optimization.
- It complicates read-path validation.
- Corruption should trigger a recoverable error, not a kernel panic.
- The new behavior is safer for production workloads.
Why BUG_ON() Is the Wrong Tool Here
The Linux kernel has historically used BUG_ON() in places where developers wanted to enforce impossible assumptions. In a debugging context, that can be useful. In production storage code, it can be dangerous, because attackers, bad media, or edge-case corruption can transform “impossible” into “routine enough to exploit.”Assertions are not resilience
A BUG_ON() is effectively a promise that the code path cannot happen. But filesystem code lives at the edge of trust: it parses on-disk structures that may be damaged, partially updated, or deliberately malformed. In that environment, the right response is usually validation and error propagation, not immediate termination.The ext4 change fits the broader Linux trend toward fail closed, not fail hard. If corruption is detected, the right outcome is to mark the inode or filesystem as corrupted, stop relying on the bad state, and let higher layers decide whether to remount, repair, or continue in read-only mode.
That is not just a theoretical ideal. It is the same design logic behind many kernel fixes that convert crashes into explicit errors. The patch acknowledges that filesystem corruption is not an abstract logic bug; it is a runtime condition that should be handled as gracefully as possible.
Operational impact in real deployments
For a workstation, a kernel panic is annoying. For a server, it can be expensive. For a virtualized host, it can knock multiple guests offline. For a storage node, it can trigger cascading retries, delayed writes, or failover events.That is why replacing a BUG_ON with error handling is more than defensive coding. It reduces the blast radius of corruption. Instead of turning one damaged inode into a machine-wide outage, the kernel can confine the damage to the relevant filesystem object and continue serving unaffected workloads.
- A panic can take down more than the corrupted file.
- Error handling limits the blast radius.
- Production systems need graceful degradation.
- Corruption should be diagnosable, not terminal.
The Linux Kernel Fix Path
The CVE entry includes multiple stable kernel references, which indicates the fix has been propagated through the normal upstream and backport pipeline. That is a strong sign that maintainers considered the issue worthy of coordinated distribution across supported trees, not just a one-off cleanup. The references listed in the CVE record point to several kernel.org stable commits, reinforcing that this is an upstream-resolved problem rather than a downstream-only patch.Upstream hygiene matters
Kernel stands alone. A small change in ext4 often rides alongside related maintenance in the same subsystem, because filesystem bugs tend to cluster around shared assumptions: buffer lifetime, page boundaries, inode accounting, and corruption semantics. The fact that this issue was handled in the stable workflow suggests the maintainers wanted the safer behavior broadly available as quickly as possible.That has a second-order benefit: downstream vendors can align their own updates with the upstream fix rather than engineering separate mitigation logic. In practice, that speeds up patch adoption for enterprise Linux distributions, cloud images, and hypervisor stacks.
Why stable backports are important
Stable backports are often the difference between a theoretical fix and an actually protected fleet. Many organizations do not run the latest mainline kernel, so a CVE can remain relevant long after the original patch lands upstream. The stable references in the CVE record mean the fix was intended to reach those older maintained branches as well.A few practical implications follow:
- Long-term-support tly.
- Cloud images can incorporate the fix during normal refresh cycles.
- Enterprise distributions can backport without rewriting behavior.
- Administrators should not assume “only mainline” applies.
Enterprise and Cloud Impact
The main enterprise concern with this CVE is not remote code execution or privilege escalation; it is availability. In many environments, that can still be a serious security issue, because a kernel panic in a storage layer can force a failover, interrupt transactions, or cause data loss if services were depending on in-flight state.Why availability is a security issue
Security teams increasingly treat reliability bugs as part of the security surface. When a corrupted filesystem can crash a host, the attacker or failure condition does not need to steal data to cause harm. It only needs to deny service at the right layer. That is especially relevant in virtualized fleets and container clusters, where a single node can host many workloads.The ext4 fix reduces that risk by ensuring corruption is reported rather than detonated. It does not eliminate the corruption itself, but it transforms the response into one that administrators can script around, monitor, and recover from.
Cloud operators will care first
Cloud infrastructure tends to amplify the value of graceful error handling. Hosts are expected to remain available even when individual tenants or volumes misbehave. A panic in the host kernel is therefore disproportionately costly, because it can affect many customers or services at once.The corrected ext4 path gives operators better odds of surviving a bad inode without taking down the machine. That may not sound dramatic, but in hyperscale terms, small reduction in crash probability translates into large improvements in fleet reliability.
- Shared hosts magnify the cost of a panic.
- Storage corruption is a common real-world failure mode.
- Graceful errors help automated recovery systems.
- Read-only fallback and remount workflows become viable.
Consumer and Desktop Impact
Desktop users may think of filesystem bugs as server problems, but that is a mistake. A local ext4 corruption event can crash a laptop just as easily as a datacenter node, especially after unclean shutdowns, bad disks, or experimental filesystems. The difference is that consumers often have less automation and less redundancy to absorb the failure.What changes for everyday users
For a laptop or desktop running ext4, the immediate win is that an unusual inline-data corruption event is less likely to freeze the whole machine. That does not mean files become recoverable, or that the data problem disappears. It means the operating system is more likely to survive long enough for the user to copy files, run checks, or reboot into repair mode.The distinction is important. In consumer terms, the new behavior is less catastrophic, not magically safe. A corrupted inode still represents a problem that should be investigated, but the system itself will be better able to stay alive through it.
The support burden changes too
Help desks and community support forums often struggle when a system crashes during file access, because the symptom obscures the cause. Returning -EFSCORRUPTED improves diagnostics. It gives logging, monitoring, and repair tools a more explicit signal that the issue lies in the filesystem metadata.That can reduce troubleshooting time and improve the odds that the real issue is fixed rather than masked by a reboot. It also means users are less likely to blame a general OS defect when the actual culprit is a damaged filesystem structure.
- Better error reporting improves diagnosis.
- Panic avoidance helps preserve user sessions.
- Repair tools can work with clearer signals.
- The user experience becomes less abrupt.
How This Fits the Broader ext4 Pattern
This CVE is part of a long-running arc in Linux storage maintenance: move away from fatal assumptions, especially in paths that touch disk metadata. ext4 has repeatedly evolved toward better validation, better cleanup, and better fault signaling. That is not because the filesystem is uniquely fragile, but because it is mature enough to be held to a higher standard.A familiar theme in filesystem hardening
Filesystem maintainers have spent years trimming hard failures out of paths that can be triggered by corruption or error injection. The reason is straightforward: once a path is reachable from untrusted or semi-trusted disk state, the kernel should assume it will eventually be hit in the real world. The old model of “this should never happen” simply does not survive modern testing, fuzzing, and large-scale deployment.That is why the change here feels familiar. It is not a dramatic redesign; it is a correction to a failure assumption. But those corrections are often the most important ones, because they reduce the number of ways corrupted metadata can crash a live system.
Fuzzing and fault injection drive these fixes
Many ext4 fixes originate in aggressive testing, including fault injection, malformed images, and syzkaller-style reproduction. That ecosystem has changed kernel development. Bugs that once survived for years are now exposed earlier because developers expect failure paths to be exercised, not merely theorized.The lesson for admins is simple: don’t confuse “rare” with “safe.” If a code path can be reached through corrupted metadata, fuzzing will eventually find it, and real hardware failures can too.
- Corruption paths deserve first-class handling.
- Fuzzing has made hidden assumptions visible.
- Recovery behavior is as important as correctness.
- Kernel hardening is an ongoing process, not a one-time patch.
What Administrators Should Do
The immediate administrative question is not how to exploit this CVE, but how to reduce exposure. Because the issue is in the Linux kernel’s ext4 path, the right response is to track your kernel vendor’s patch status and confirm whether your distribution has backported the fix. For Microsoft-linked Linux environments, the publication in the update guide is a useful indicator that the vulnerability has entered enterprise security workflows.Practical response checklist
- Identify systems using ext4 with ker the fix.
- Check your distribution advisories for the backported patch.
- Prioritize hosts that serve critical or shared workloads.
- Review filesystem health and recent unclean shutdowns.
- Ensure monitoring is alerting on ext4 corruption messages.
- Plan maintenance windows for kernel updates where needed.
When to worry most
Systems with a history of disk errors, abrupt power loss, or storage-layer anomalies deserve more attention. So do fleets that rely heavily on inline-data-heavy workloads, though in practice the corruption condition is still about metadata integrity rather than normal file size behavior. Administrators should treat the CVE as a reminder to inspect the health of any filesystem that has already shown signs of stress.- Pay attention to machines with recent I/O errors.
- Review any ext4 warnings in logs.
- Rebooting is not the fix; updating is.
- Corruption should be investigated, not ignored.
Strengths and Opportunities
The strongest aspect of this fix is that it improves system survivability without changing the core design of ext4. It also reflects a healthy security posture: stop asserting on corruption, start treating corruption as a managed error. For organizations that value uptime, this is a clean win.- Reduces the chance of a full kernel panic from filesystem corruption.
- Improves diagnostic clarity through explicit error reporting.
- Protects availability in server and cloud environments.
- Lowers the risk of resource leaks by releasing the buffer head.
- Aligns with modern kernel hardening practices.
- Supports better remediation workflows for administrators.
- Makes ext4 more resilient in the face of malformed or damaged metadata.
Risks and Concerns
The main concern is that replacing a crash with an error does not remove the underlying corruption. If operators misread the fix as a cure rather than a containment measure, they may underinvest in storage health monitoring. The change is valuable, but it is not a substitute for disk checks, backups, or root-cause analysis.- Existing filesystem corruption still needs investigation.
- Vendors may backport at different times, creating patch variability.
- Some environments may continue running older kernels for longer than expected.
- Error handling can hide the severity of an issue if logs are not monitored.
- Systems that rely on ext4 across large fleets may need coordinated rollouts.
- Administrators might assume the panic risk is gone everywhere when it is not.
- The CVE primarily affects reliability, but availability failures can still be serious.
Looking Ahead
This CVE is another sign that Linux storage maintenance is steadily moving toward safer failure semantics. That matters because the kernel is increasingly expected to behave like infrastructure, not like a debugging environment. As deployments grow larger and more automated, the cost of a panic becomes harder to justify when an error return can preserve service long enough for remediation.The next thing to watch is how quickly the fix reaches downstream kernels and vendor builds. In many environments, the real security question is not whether the patch exists upstream, but whether it has been incorporated into the exact kernel your fleet runs today. That gap is where exposure lives.
- Confirm your distro’s backport status.
- Watch for vendor advisories tied to your kernel line.
- Verify ext4 health alerts are being captured centrally.
- Update golden images and cluster baselines.
- Reassess reboot and recovery procedures after patching.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center