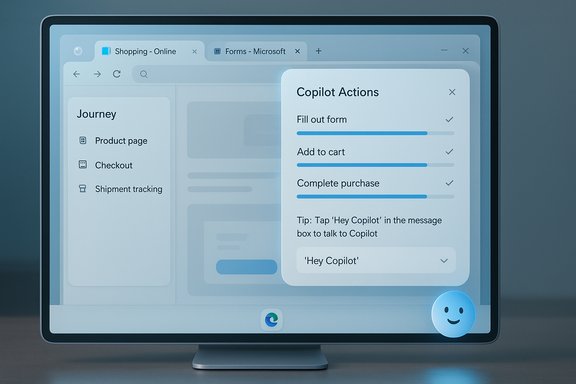
Microsoft Edge’s built‑in payments and autofill capabilities let you move from cart to confirmation in seconds — but recent UI changes and privacy trade‑offs mean a quick, secure setup matters more than ever for Windows 11 users. This guide walks through a fast, practical setup of the Microsoft Edge wallet experience (payments, saved cards, billing addresses and security checks), explains what changed recently, and gives a frank assessment of benefits, limitations, and hardening tips so you can use Edge to pay online without creating new headaches.
Microsoft Edge previously exposed saved cards, addresses and other checkout data under a feature labeled Wallet, but Microsoft has been consolidating that functionality into the browser’s Passwords & autofill / Payment info area. The retirement of the old Wallet label (announced as part of a rework that took effect May 29, 2025) means you’ll find the same data under updated Settings pages rather than a separate “Wallet” entry. This consolidation is intended to simplify access, but it also changes some expected flows and labels in Edge’s UI. Under the hood, Edge’s autofill for payment instruments is a standard browser feature that stores card numbers (with exceptions for CVV), expiry dates, and billing addresses for faster checkouts. Microsoft’s support documentation explains how saved payment info autofills into payment forms and that card verification charges (small temporary holds) may appear in some regions. Edge can sync saved payment data to your Microsoft account in supported geographies, enabling cross‑device use when you sign into Edge.
For high‑risk or shared environments, treat browser autofill as an operational decision: disable saving and filling of payment info through browser settings or enterprise policy and rely on dedicated, centrally managed payment tools. Administrators should use the documented Edge policies to enforce safe defaults.
Microsoft Edge’s payments features are a modern convenience built into Windows 11 — powerful when used correctly, and safe when paired with Windows Hello and sensible sync controls. Follow the short setup steps above, audit saved details regularly, and use enterprise policies where appropriate to reduce the risk surface while enjoying faster checkouts online.
Source: Windows Report How to Set Up Microsoft Edge Wallet in Windows 11 Fast
 Background
Background
Microsoft Edge previously exposed saved cards, addresses and other checkout data under a feature labeled Wallet, but Microsoft has been consolidating that functionality into the browser’s Passwords & autofill / Payment info area. The retirement of the old Wallet label (announced as part of a rework that took effect May 29, 2025) means you’ll find the same data under updated Settings pages rather than a separate “Wallet” entry. This consolidation is intended to simplify access, but it also changes some expected flows and labels in Edge’s UI. Under the hood, Edge’s autofill for payment instruments is a standard browser feature that stores card numbers (with exceptions for CVV), expiry dates, and billing addresses for faster checkouts. Microsoft’s support documentation explains how saved payment info autofills into payment forms and that card verification charges (small temporary holds) may appear in some regions. Edge can sync saved payment data to your Microsoft account in supported geographies, enabling cross‑device use when you sign into Edge. Quick overview: What you’ll accomplish in five minutes
- Add a credit/debit card to Edge’s payment store (the “wallet” experience).
- Link a billing address for smooth checkout.
- Enable Windows Hello authentication so only you can authorize autofill at checkout.
- Confirm sync options if you want cards to follow you across Windows devices.
- Apply a few privacy and policy controls to limit risk on shared machines.
Fast, step‑by‑step: Set up Edge’s Wallet (Payments) in Windows 11
1. Open Edge settings and locate Payments / Passwords & autofill
- Launch Microsoft Edge.
- Click the three‑dot menu (Settings and more) in the top right, then choose Settings.
- Select Profiles in the left column, then open Passwords & autofill or Payment info (label varies by Edge version due to the recent Wallet consolidation). You may also open edge://settings/payments directly in the address bar to jump to the payment area.
2. Add a new credit or debit card
- In the Payments / Wallet area click Add payment method (or Add card).
- Enter the card number, expiration date, and the cardholder name exactly as printed on the card.
- Decide whether to enable Save this card for autofill. For most users who shop frequently, leaving this on reduces checkout time; for shared or public devices, leave it off.
- Click Save. Edge stores the card details securely and will then offer the card when it detects a payment field on a checkout page.
3. Add or confirm your billing address
- Still under Profiles > Passwords & autofill (or the Personal info section), choose Add address.
- Enter the billing name, street address, city, postal code and country.
- Save the address so Edge can attach it to the card automatically during autofill. Having this linked eliminates form mismatches at checkout that can trigger declines or manual verification steps.
4. Turn on the autofill and confirm security requirements
- Navigate to Settings → Profiles → Passwords & autofill → Payment info (or Payment info directly) and make sure Save and fill payment info is turned On.
- Enable Require Windows Hello to confirm payments (or the “Require authentication before autofill” toggle). This makes Edge ask for your Windows Hello PIN, fingerprint or face recognition before inserting saved card numbers. If you don’t have Windows Hello set up, the dialog will guide you to Windows Settings → Accounts → Sign‑in options to register a PIN or biometric. The Windows Hello step keeps stored payment data protected by local device authentication.
5. Use the stored card at checkout
- On any checkout page with a payment field, click inside the card number input.
- Edge will display a dropdown with saved cards and addresses; pick the correct card.
- Edge may prompt you to authenticate with Windows Hello before filling the fields. Complete the verification, review the details and confirm the purchase on the merchant’s page. For faster paths, Edge’s Express Checkout features may also appear when you’ve saved personal info and payment methods.
Where the labels changed — and why it matters
Microsoft’s May 29, 2025 change retires the “Wallet” label and consolidates payment, password and personal info management under Passwords & autofill. That means older guides that say “Wallet > Add card” may no longer match your UI exactly; the new flow centralizes these controls and hides Wallet as a separate menu. Expect the same functionality (payment saves, address management, authentication) in the updated settings pages. If you prefer the old phrasing, look for Payment info or Personal info under Profiles.What Microsoft actually stores (and what it doesn’t)
- Edge stores card numbers, expiry dates and billing addresses for autofill. CVV codes are not stored by Edge; the browser uses CVV only for one‑time authorization when adding or verifying cards. That protects an important secret value from long‑term storage.
- If you sign into Edge with a Microsoft account, saved payment data may be synced to your account in supported countries (US, AU, UK, CA, DK, FR, JP, MX, KR, BR, and more over time). If you don’t want cross‑device syncing, turn Off Payment info sync in Profiles → Sync.
Security analysis: protections, gaps, and hardening tips
Strong points
- Windows Hello authentication: Requiring Windows Hello before autofill adds local, biometric or PIN protection, using the device’s secure path to unlock card data. This is a robust barrier against casual misuse on an unlocked or unattended machine.
- No CVV retention: Edge’s policy not to store CVV reduces the risk of full card cloning from saved browser data — a meaningful design choice for browser wallets.
- Policy & enterprise controls: Administrators can control autofill and payment storage via Group Policy or Edge browser policies (for example, the AutofillCreditCardEnabled policy), which helps enterprises prevent sensitive data from being stored on managed devices.
Risks and limitations
- Local device compromise: If an attacker obtains physical access to an unlocked device or can bypass Windows Hello (rare but possible with advanced hardware attacks or stolen credentials), saved cards could be exposed. That risk increases on shared or public machines.
- Syncing to the cloud: Syncing cards to your Microsoft Account is convenient but concentrates risk. A compromised Microsoft account could expose your autofill data if it’s synced. Use multi‑factor authentication and a strong account recovery setup.
- Browser autofill bugs and UX quirks: Community reports show Edge occasionally saves irrelevant fields or misapplies autofill entries to incorrect fields. That means auditing saved entries periodically is wise to avoid shipping incorrect info to merchants.
Hardening checklist (recommended)
- Only enable Save and fill payment info on personal devices.
- Turn on Require Windows Hello for payment autofill.
- Keep your Microsoft account protected with MFA and a unique strong password if you enable sync.
- Review saved payment methods periodically and delete old cards you no longer use.
- For shared corporate machines, have IT disable autofill via Group Policy (AutofillCreditCardEnabled = Disabled) so sensitive payment info cannot be stored.
Troubleshooting: common issues and fixes
- Edge doesn’t show your saved card at checkout: Confirm Save and fill payment info is On, confirm you’re signed into the profile with the saved card, and check whether the site’s payment field is non‑standard. If sync is enabled but a card is missing on another device, verify that the other device supports saved cards in your region.
- Edge autofills strange or incorrect fields: Manually edit or delete the offending Personal info entry in Settings → Profiles → Personal info; Edge sometimes collects extraneous entries, so pruning helps.
- You don’t see Express Checkout: Edge shows Express Checkout only when it detects saved personal info and payment methods, and when the “Save time and money with Shopping in Microsoft Edge” service toggle is on. If you’ve turned autofill toggles off, Express Checkout won’t appear.
Advanced options and enterprise considerations
Edge flags and experimental features
Power users sometimes enable Edge flags to test new shopping or autofill behaviors, but flags are experimental and may introduce bugs. Use them only in Dev or Canary builds and avoid flags on production machines. For stable setups, rely on the official Settings UI and Microsoft documentation.Group Policy and MDM control
Enterprises have granular control over autofill and payment storage through ADMX/Group Policy templates and Intune settings. Policies let admins disable saving or filling addresses and payment methods entirely, enforce encryption, or restrict sync. This is crucial for regulated environments or shared workstation scenarios.Cross‑checking the claims: what’s verifiable and what to watch
- Verified: Edge will autofill saved credit/debit card info when Save and fill payment info is enabled, and Edge does not store CVV codes. Microsoft documents these points on its support pages.
- Verified: Express Checkout appears only when you’ve saved personal info and payment methods and when the Shopping feature is enabled. Microsoft Support explains the conditions for Express Checkout’s availability.
- Verified and time‑sensitive: The Wallet label was retired May 29, 2025; settings and controls moved under Passwords & autofill. Guides referencing “Wallet” may be out of date. Treat the label change as authoritative — the functionality remains but the menu path changed.
- Policy verification: Microsoft Learn documents the AutofillCreditCardEnabled policy and admin controls, confirming enterprises can restrict browser payment autofill. This is important for admins who must comply with PCI or internal rules.
Practical recommendations for everyday users
- Use Windows Hello for payment confirmation — it’s fast and significantly reduces the chance someone else can use your saved cards.
- Keep Edge and Windows 11 up to date. Security improvements and bug fixes around autofill happen frequently — updates reduce exposure to known issues.
- Use a dedicated card for online purchases where you can (a card with limited balance or virtual card) to reduce exposure if a site is compromised or you accidentally leak autofill data.
- Consider a password manager with dedicated payment features if you want additional controls or cross‑browser integration; these managers often provide vaults and shared family plans that are independent of browser sync.
- Audit saved payment methods quarterly: delete retired cards, correct obsolete addresses, and remove entries you don’t recognize. Edge’s Personal info and Payment info panels make this straightforward.
Final verdict: speed vs. control
Microsoft Edge’s payments/autofill capability gives Windows 11 users a fast, integrated checkout experience with sensible security defaults — notably Windows Hello gating and no CVV retention. The recent UI consolidation (Wallet → Passwords & autofill) simplifies the settings but does introduce a short help‑text mismatch for users following older tutorials. For most personal users, enabling autofill and Windows Hello strikes the best balance: fast checkouts with local biometric or PIN confirmation.For high‑risk or shared environments, treat browser autofill as an operational decision: disable saving and filling of payment info through browser settings or enterprise policy and rely on dedicated, centrally managed payment tools. Administrators should use the documented Edge policies to enforce safe defaults.
Quick reference (cheat sheet)
- Settings path: edge://settings/payments or Settings → Profiles → Passwords & autofill → Payment info.
- Turn on: Save and fill payment info.
- Enable protection: Require Windows Hello to confirm payments.
- Add billing address: Profiles → Personal info → Add address.
- Admin lock: Use the AutofillCreditCardEnabled policy or Group Policy templates to disable saving/auto‑filling on managed devices.
Microsoft Edge’s payments features are a modern convenience built into Windows 11 — powerful when used correctly, and safe when paired with Windows Hello and sensible sync controls. Follow the short setup steps above, audit saved details regularly, and use enterprise policies where appropriate to reduce the risk surface while enjoying faster checkouts online.
Source: Windows Report How to Set Up Microsoft Edge Wallet in Windows 11 Fast