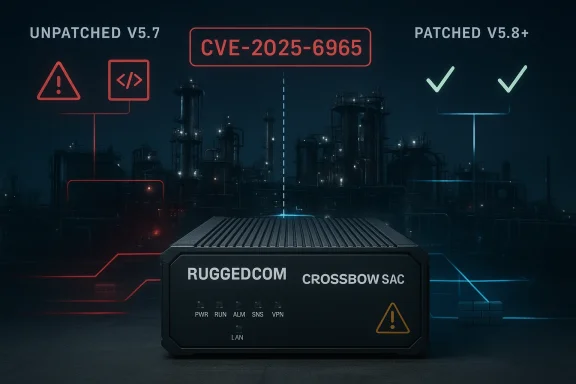
Siemens’ latest industrial cybersecurity advisory for RUGGEDCOM CROSSBOW Station Access Controller (SAC) is a reminder that access-management software can be just as dangerous to critical operations as the field devices it protects. The flaw, tracked as CVE-2025-6965, affects RUGGEDCOM CROSSBOW SAC versions earlier than 5.8 and carries a CVSS 3.1 score of 7.7, with Siemens and CISA indicating that exploitation could lead to arbitrary code execution and a denial-of-service condition. Siemens has already shipped a fixed release and is recommending customers move to V5.8 or later, while CISA is republishing the advisory with its standard industrial-defense guidance for segmentation, exposure reduction, and secure remote access.
RUGGEDCOM CROSSBOW sits in a very specific part of the industrial stack. It is not a general-purpose enterprise app, and it is not a field sensor or controller either; it is a secure access management platform that brokers who can reach critical operational assets and under what conditions. That makes it part of the trust boundary for industrial environments, which means a flaw in the platform can have effects that ripple far beyond the product itself.
That context matters because access-control systems are force multipliers. If a bug sits inside the layer that decides who gets to touch downstream devices, then the attacker does not need to own the device directly to cause damage. They only need a path into the control plane, and once there, they may be able to pivot into more sensitive operational assets.
The affected vulnerability is being described as a numeric truncation error, and the underlying CVE text ties it to SQLite versions before 3.50.2, where aggregate-term handling can exceed the number of columns available and lead to memory corruption. Siemens’ advisory says the product line is affected and that the practical fix is to upgrade to V5.8 or later. That combination suggests the issue is not just a business-logic problem; it is a genuine memory-safety defect with execution impact.
Industrial advisories of this type are also notable because they tend to sit at the intersection of IT patching and OT operational constraints. The patch exists, but the deployment often has to be validated against access workflows, maintenance windows, and site-specific rules. That slows remediation, which is exactly why these advisories keep stressing segmentation, restricted exposure, and defense-in-depth.
The practical takeaway is straightforward: this is not a cosmetic update notice. It is a vulnerability in a privileged management product that can potentially become a foothold for broader compromise if left unpatched. In industrial environments, those are the bugs that deserve immediate attention, even when they do not dominate the news cycle.
The description also makes clear that the issue can affect both confidentiality and integrity, with the added possibility of availability loss through denial of service. That is a serious combination, especially for an industrial access-management product where stability and trust are the whole point. If the management plane can be crashed or manipulated, the consequences can spread into the operational network behind it.
The vendor’s guidance does not suggest a clever workaround that can safely substitute for patching. That matters because it implies the intended defense is a full upgrade, not a temporary configuration tweak. In industrial operations, that can be inconvenient, but it is also helpful because it removes ambiguity from the response plan.
The important point is that this is not merely an authorization mistake or a harmless crash. A memory-corruption flaw in a management platform is often a stepping stone to broader compromise because it can provide control over the process that decides access to everything else. That is why the advisory deserves urgent operational treatment.
The scoring also hints at how real-world abuse could unfold. If an attacker already has a foothold on the network or a low-privilege account, they may be able to turn that access into a much more dangerous exploit path. That does not mean every environment is equally exposed, but it does mean the threshold for concern should be low.
The low-privilege requirement is equally important. It suggests the attacker may not need a highly privileged administrator account to trigger the flaw, which is exactly why industrial teams should be suspicious of “just a basic account” assumptions. In a control environment, even low-privilege accounts can become powerful if the software’s internal trust boundaries are weak.
This matters because the flaw is not just “in the application” in some abstract sense. It points to a dependency-layer issue, which is a growing theme in modern industrial and embedded software. Even when the vendor is shipping a polished appliance or management product, the underlying components can still carry upstream defects that become exploitable in downstream deployments.
There is also a lifecycle problem. Industrial products tend to live longer than ordinary consumer software, which means the same dependency can be deployed for years in environments that are slow to replace, revalidate, or reboot. That is where a vulnerability becomes operationally relevant: not because it is novel, but because it persists.
In practical terms, a memory-safety bug in a privileged management system deserves more urgency than a generic “administrative glitch.” It can provide attackers with an entry point, a denial path, or both. That dual-use risk is exactly why industrial operators should treat the patch as time-sensitive.
CISA’s republication also reinforces the operational angle. Its standard guidance recommends minimizing network exposure, placing control networks behind firewalls, isolating them from business networks, and using VPNs carefully when remote access is necessary. Those recommendations are routine in ICS advisories, but they remain relevant because the easiest bug to exploit is the one that was exposed too broadly.
This is where industrial security differs from ordinary IT patching. A flaw that would be “high” in a normal enterprise app can become far more consequential in an OT environment because the software may be part of the chain that authorizes plant access, contractor access, or maintenance access. That is the real blast radius.
That difference explains why Siemens and CISA emphasize protected environments and restricted reachability. The more tightly the management plane is segmented, the less likely a vulnerability can be used to touch the systems it protects. In industrial security, segmentation is not a best practice; it is an enabling control.
For organizations running the product in production, the key question is not whether the upgrade is available; it is how quickly it can be validated and rolled out without breaking access workflows. Industrial patching almost always involves maintenance windows, change control, and regression checks, so the sooner the process starts, the better.
Those controls do not eliminate the bug, but they can reduce the odds of easy exploitation. In the real world, that matters because patch timing in industrial operations is often measured in days or weeks rather than hours. Buying time safely is a useful outcome when the fix is already available but not yet deployed.
There is also a broader opportunity here. Because the issue sits in an access-management platform, organizations can use the advisory as a trigger to audit nearby trust boundaries, role assignments, and segmentation. Sometimes a single CVE reveals a wider policy problem that was already lurking in the environment.
A second concern is underestimation. A high-severity memory corruption bug in a management tool can be dismissed as “just another vendor advisory,” but that framing misses the point. If the product governs access to critical devices, then compromise of the product can matter more than compromise of a single endpoint.
Another risk is that teams will focus on the software update and ignore the access model around it. If the product remains reachable from broad networks or overly permissive administrative zones, the patch will reduce risk but not eliminate it. That is why network design still matters after remediation.
It will also be worth watching whether Siemens or downstream integrators publish additional notes about deployment validation, upgrade sequencing, or compatibility issues around V5.8. In industrial environments, the technical fix is only part of the story; the operational rollout determines when the risk really goes away.
Siemens has done the important part by publishing the advisory and the fix path, but the real work now shifts to operators. In industrial security, the difference between a well-documented flaw and a real incident is often patch speed, asset visibility, and how honestly an organization reviews its own trust boundaries. The dangerous access is often the access a system mistakenly believes is perfectly normal.
Source: CISA Siemens RUGGEDCOM CROSSBOW Station Access Controller (SAC) | CISA
 Background
Background
RUGGEDCOM CROSSBOW sits in a very specific part of the industrial stack. It is not a general-purpose enterprise app, and it is not a field sensor or controller either; it is a secure access management platform that brokers who can reach critical operational assets and under what conditions. That makes it part of the trust boundary for industrial environments, which means a flaw in the platform can have effects that ripple far beyond the product itself.That context matters because access-control systems are force multipliers. If a bug sits inside the layer that decides who gets to touch downstream devices, then the attacker does not need to own the device directly to cause damage. They only need a path into the control plane, and once there, they may be able to pivot into more sensitive operational assets.
The affected vulnerability is being described as a numeric truncation error, and the underlying CVE text ties it to SQLite versions before 3.50.2, where aggregate-term handling can exceed the number of columns available and lead to memory corruption. Siemens’ advisory says the product line is affected and that the practical fix is to upgrade to V5.8 or later. That combination suggests the issue is not just a business-logic problem; it is a genuine memory-safety defect with execution impact.
Industrial advisories of this type are also notable because they tend to sit at the intersection of IT patching and OT operational constraints. The patch exists, but the deployment often has to be validated against access workflows, maintenance windows, and site-specific rules. That slows remediation, which is exactly why these advisories keep stressing segmentation, restricted exposure, and defense-in-depth.
The practical takeaway is straightforward: this is not a cosmetic update notice. It is a vulnerability in a privileged management product that can potentially become a foothold for broader compromise if left unpatched. In industrial environments, those are the bugs that deserve immediate attention, even when they do not dominate the news cycle.
What Siemens Disclosed
Siemens’ disclosure is relatively direct about the affected software and the remediation path. The advisory identifies RUGGEDCOM CROSSBOW Station Access Controller (SAC) as the impacted product, says versions before 5.8 are affected, and instructs customers to update to V5.8 or later. That kind of clarity is useful because it gives administrators a specific target instead of a vague “apply a patch” directive.The description also makes clear that the issue can affect both confidentiality and integrity, with the added possibility of availability loss through denial of service. That is a serious combination, especially for an industrial access-management product where stability and trust are the whole point. If the management plane can be crashed or manipulated, the consequences can spread into the operational network behind it.
Why the version boundary matters
A fixed version boundary is more than a technical detail. It lets security teams build a clean inventory of exposure and avoid treating the product as a broad, open-ended risk. In practice, that means the first question is simple: is any deployed SAC instance still below V5.8? If the answer is yes, the system should be treated as vulnerable.The vendor’s guidance does not suggest a clever workaround that can safely substitute for patching. That matters because it implies the intended defense is a full upgrade, not a temporary configuration tweak. In industrial operations, that can be inconvenient, but it is also helpful because it removes ambiguity from the response plan.
What the CVE implies technically
The advisory’s own CVE text ties the issue to SQLite before 3.50.2 and a condition where aggregate-term counts can exceed available columns, leading to memory corruption. That is the kind of bug that can be difficult to reason about from the outside, but easy to understand from a security standpoint: if attacker-influenced input can push the database layer into the wrong memory state, the bug can become a path to code execution or denial of service.The important point is that this is not merely an authorization mistake or a harmless crash. A memory-corruption flaw in a management platform is often a stepping stone to broader compromise because it can provide control over the process that decides access to everything else. That is why the advisory deserves urgent operational treatment.
Why the Severity Matters
A CVSS v3.1 base score of 7.7 places the issue firmly in the high severity range. The vector tells the story: it is network-reachable, requires low privileges, needs no user interaction, and can affect confidentiality, integrity, and availability. In plain language, that is the profile defenders dislike most because it is both reachable and impactful.The scoring also hints at how real-world abuse could unfold. If an attacker already has a foothold on the network or a low-privilege account, they may be able to turn that access into a much more dangerous exploit path. That does not mean every environment is equally exposed, but it does mean the threshold for concern should be low.
Interpreting the vector in operational terms
The network attack vector matters because it expands the attack surface beyond a local workstation or direct physical access. If the product is reachable from a business LAN, a vendor jump host, or any broader management zone, then the pool of potential attackers grows quickly.The low-privilege requirement is equally important. It suggests the attacker may not need a highly privileged administrator account to trigger the flaw, which is exactly why industrial teams should be suspicious of “just a basic account” assumptions. In a control environment, even low-privilege accounts can become powerful if the software’s internal trust boundaries are weak.
- Network reachability raises exposure across the environment.
- Low privileges required increase the odds of realistic abuse.
- No user interaction reduces the chance of human intervention stopping the attack.
- High impact on C/I/A means the flaw can affect more than one security objective.
- High severity supports immediate remediation, not routine scheduling.
The SQLite Angle
The advisory’s most interesting technical detail is the SQLite relationship. Siemens says the vulnerability is tied to SQLite versions before 3.50.2, where aggregate-term handling can exceed the available columns and trigger memory corruption. That puts the issue squarely into a class of bugs security teams take seriously because memory corruption can lead to unpredictable behavior, code execution, or crashes.This matters because the flaw is not just “in the application” in some abstract sense. It points to a dependency-layer issue, which is a growing theme in modern industrial and embedded software. Even when the vendor is shipping a polished appliance or management product, the underlying components can still carry upstream defects that become exploitable in downstream deployments.
Why dependency vulnerabilities are so hard
Dependency flaws are hard because they often sit below the features that operators actually see. The user experiences a management console, policy editor, or device access workflow, while the vulnerability lives in the database engine or another embedded component under the hood. That makes the issue less visible during normal functional testing and more dangerous when exposed to real-world inputs.There is also a lifecycle problem. Industrial products tend to live longer than ordinary consumer software, which means the same dependency can be deployed for years in environments that are slow to replace, revalidate, or reboot. That is where a vulnerability becomes operationally relevant: not because it is novel, but because it persists.
Why memory corruption changes the risk profile
Memory corruption often carries a different weight than a pure logic bug. Even when the vulnerability is difficult to exploit cleanly, it can still allow code execution or crash a service in a way that is difficult to predict or contain. For an access-management product, that means the exploit impact can extend into both platform stability and trust relationships.In practical terms, a memory-safety bug in a privileged management system deserves more urgency than a generic “administrative glitch.” It can provide attackers with an entry point, a denial path, or both. That dual-use risk is exactly why industrial operators should treat the patch as time-sensitive.
- Dependency flaws can hide below the visible UI.
- Industrial lifecycles keep vulnerable components in service longer.
- Memory corruption can support both crash and code execution outcomes.
- Under-the-hood bugs are harder to detect during functional testing.
- A management-plane dependency flaw can affect downstream trust.
Industrial Impact
The product’s inclusion in a critical manufacturing context is not an abstract label. It means the issue affects an environment where downtime, access control, and reliability have real operational consequences. In other words, this is not just another CVE in a catalog; it is a flaw in software used to govern access to infrastructure that matters.CISA’s republication also reinforces the operational angle. Its standard guidance recommends minimizing network exposure, placing control networks behind firewalls, isolating them from business networks, and using VPNs carefully when remote access is necessary. Those recommendations are routine in ICS advisories, but they remain relevant because the easiest bug to exploit is the one that was exposed too broadly.
Why access-management software is a force multiplier
Access-management platforms sit upstream of everything else. If they fail, the attacker may not need to attack each field device individually; they can instead target the system that decides who gets to reach those devices. That makes the software a multiplier for both risk and opportunity.This is where industrial security differs from ordinary IT patching. A flaw that would be “high” in a normal enterprise app can become far more consequential in an OT environment because the software may be part of the chain that authorizes plant access, contractor access, or maintenance access. That is the real blast radius.
Enterprise vs. plant-floor consequences
For enterprise IT teams, the concern is usually whether a service can be compromised, crashed, or used as a stepping stone. For plant operators, the question is often whether the flaw can disrupt access to critical equipment, break authentication workflows, or interfere with remote operations. Both matter here, but the industrial side carries the heavier operational burden.That difference explains why Siemens and CISA emphasize protected environments and restricted reachability. The more tightly the management plane is segmented, the less likely a vulnerability can be used to touch the systems it protects. In industrial security, segmentation is not a best practice; it is an enabling control.
- Management-plane compromise can affect downstream device access.
- Critical manufacturing sites face higher operational consequences.
- Segmentation reduces the number of paths into the vulnerable product.
- Remote access should be tightly controlled and monitored.
- Industrial trust boundaries are narrower than enterprise assumptions.
Patch Guidance and Remediation
The remediation story here is thankfully simple: update to V5.8 or later. That is the fix Siemens recommends, and it is the only response that should be considered definitive. Everything else is a temporary risk reduction measure, not a substitute for remediation.For organizations running the product in production, the key question is not whether the upgrade is available; it is how quickly it can be validated and rolled out without breaking access workflows. Industrial patching almost always involves maintenance windows, change control, and regression checks, so the sooner the process starts, the better.
A practical response sequence
- Inventory every RUGGEDCOM CROSSBOW SAC deployment.
- Confirm whether each instance is running earlier than 5.8.
- Prioritize systems exposed to broader management networks.
- Validate the upgrade path in a controlled maintenance window.
- Roll affected systems to V5.8 or later as soon as feasible.
- Recheck access paths and role assignments after remediation.
Compensating controls while patching
CISA’s advice is still useful while the fix is staged. Defenders should minimize network exposure, place control-system devices behind firewalls, and isolate them from broader business networks. If remote access is required, a VPN can help, but only if it is fully updated and treated as part of a wider defense-in-depth design.Those controls do not eliminate the bug, but they can reduce the odds of easy exploitation. In the real world, that matters because patch timing in industrial operations is often measured in days or weeks rather than hours. Buying time safely is a useful outcome when the fix is already available but not yet deployed.
- Inventory first, then patch.
- Prioritize internet-reachable or broadly reachable management paths.
- Validate the upgrade before deploying it widely.
- Restrict administrative access to approved jump hosts.
- Review logs for unusual policy or group changes.
- Retain records for future incident correlation.
Strengths and Opportunities
The strongest feature of this advisory is its clarity. Siemens identifies the product, the vulnerable range, the severity, and the fix path in a way that gives defenders a clean decision point. That is exactly what industrial security teams need when they are trying to balance uptime and risk.There is also a broader opportunity here. Because the issue sits in an access-management platform, organizations can use the advisory as a trigger to audit nearby trust boundaries, role assignments, and segmentation. Sometimes a single CVE reveals a wider policy problem that was already lurking in the environment.
- Clear version boundary makes exposure easy to define.
- The remediation path is straightforward and vendor-backed.
- The advisory supports fast prioritization by security teams.
- Access-control review can be folded into the patch project.
- Segmentation improvements can reduce future attack surface.
- Log review may reveal suspicious access patterns.
- The issue provides a useful audit checkpoint for OT governance.
Risks and Concerns
The biggest concern is remediation delay. Industrial systems are notorious for slow patch cycles because validation, uptime, and change-control requirements are strict. That delay can leave a known vulnerability exposed long after the advisory is public.A second concern is underestimation. A high-severity memory corruption bug in a management tool can be dismissed as “just another vendor advisory,” but that framing misses the point. If the product governs access to critical devices, then compromise of the product can matter more than compromise of a single endpoint.
Where defenders may stumble
Teams may not know where all SAC instances are deployed. They may also underestimate how much trust they have placed in the management plane, especially if the product was originally installed for convenience and later became operationally essential. Convenience often becomes dependency, and dependency becomes risk.Another risk is that teams will focus on the software update and ignore the access model around it. If the product remains reachable from broad networks or overly permissive administrative zones, the patch will reduce risk but not eliminate it. That is why network design still matters after remediation.
- Patch lag can outlast disclosure.
- Mixed fleets make version tracking harder.
- Management-plane flaws can be underestimated.
- Broad network exposure increases exploitability.
- Role and access assumptions may be overly optimistic.
- A fix without segmentation leaves residual risk.
- Inventory gaps can hide vulnerable instances.
Looking Ahead
The next thing to watch is how quickly affected organizations move from awareness to actual remediation. Advisories like this often expose the gap between what a team thinks its access layer does and what the product actually permits. That gap only closes when administrators verify deployed versions, review access paths, and confirm the patch really landed.It will also be worth watching whether Siemens or downstream integrators publish additional notes about deployment validation, upgrade sequencing, or compatibility issues around V5.8. In industrial environments, the technical fix is only part of the story; the operational rollout determines when the risk really goes away.
What defenders should monitor next
- Whether SAC instances below V5.8 remain widespread.
- Whether internet-exposed or broadly reachable management paths are being reduced.
- Whether suspicious group or role changes appear in logs.
- Whether related Siemens access products show similar weaknesses.
- Whether upgrade validation uncovers compatibility issues.
Siemens has done the important part by publishing the advisory and the fix path, but the real work now shifts to operators. In industrial security, the difference between a well-documented flaw and a real incident is often patch speed, asset visibility, and how honestly an organization reviews its own trust boundaries. The dangerous access is often the access a system mistakenly believes is perfectly normal.
Source: CISA Siemens RUGGEDCOM CROSSBOW Station Access Controller (SAC) | CISA