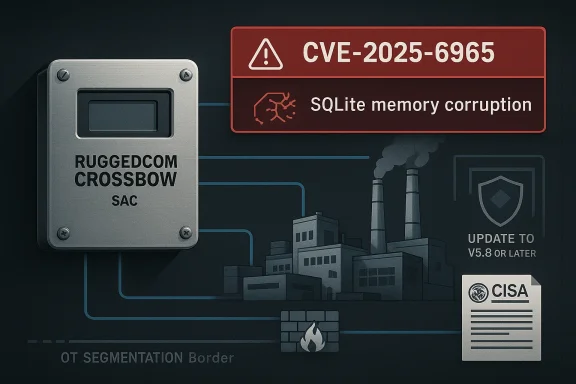
Siemens has published a fresh industrial cybersecurity advisory for RUGGEDCOM CROSSBOW Station Access Controller (SAC), and the headline is serious: a vulnerability in the product can allow arbitrary code execution or a denial-of-service condition. The issue affects SAC versions earlier than V5.8, and Siemens is telling customers to update to the latest version as the primary remediation. CISA has republished the Siemens advisory as ICSA-26-111-08, underscoring that this is not just a vendor notice but a broader critical-infrastructure concern. The flaw is also tied to CVE-2025-6965, a SQLite issue that can corrupt memory when aggregate terms exceed available columns, which helps explain why the bug is severe enough to matter in operational environments. EDCOM CROSSBOW is not a consumer-facing app, nor is it ordinary enterprise software with a routine patch cycle. It is industrial access-control infrastructure, which means it sits in the trust path for who can reach important devices, when they can reach them, and under what permissions. That makes every vulnerability in the platform more than a software defect; it becomes a potential weakness in the governance layer of an industrial environment. Siemens’ own guidance and CISA’s republished advisory both stress hardening, segmentation, and restricted remote access, which is exactly what you would expect when the product helps mediate access to critical systems.
The advisory is espause Siemens identifies the affected sector as Critical Manufacturing, with worldwide deployment and a company headquarters in Germany. That context matters because industrial access systems are rarely isolated in a clean lab-style environment. They are usually embedded in plants, utilities, and distributed manufacturing operations where patch windows are limited, change control is strict, and multiple teams depend on the same management plane. A vulnerability that would be “just a bug” in a small web app can become a serious operational event in a secure-access controller.
The technical root cause, as published ipoints to SQLite versions before 3.50.2, where the number of aggregate terms could exceed the number of available columns, leading to memory corruption. That kind of flaw is important because memory corruption is not merely a reliability problem; it can become a primitive for arbitrary code execution or a crash, depending on how an attacker can shape the inputs and the surrounding conditions. In industrial software, that is especially sensitive because management software often has privileged reach across multiple devices.
Siemens says the vendor fix is to update RUGGEDCOM CROSSBOW Sler (SAC) to V5.8 or later. That is the cleanest kind of remediation notice from a defender’s point of view: a clear version boundary, a known affected range, and a specific target for patch planning. The hard part is not understanding the fix; it is carrying it out safely in environments where uptime, validation, and vendor dependencies can slow deployment.
The CISA republication also repeats the familiar industrial-security playbook: mine, isolate control-system networks, use firewalls and VPNs carefully, and treat remote access as a risk that must be actively managed. That advice often sounds repetitive across advisories, but it persists for a reason. Industrial systems are frequently reachable in ways defenders did not intend, and a management interface with a high-severity flaw can become the easiest point of entry on the network.
The timing is relevant. Siemens issued the advisory on April 14, 2lished it on April 21, 2026**. That short lag suggests the issue is current and operationally important, not an archival finding from an old release train. In industrial security, a one-week gap between vendor disclosure and government republication usually means defenders should already be inventorying exposure and planning remediation.
Memory corruption bugs matter because they can move a system from “unexpected crash” territory into “attacker-controlled behavior” territory. Whether the final impactecution, denial of service, or something in between depends on the implementation and the exact path taken through the vulnerable code. In other words, the same bug can look like a nuisance in one deployment and a serious takeover primitive in another.
This is one reason industrial advisories often feel repetitive. The same classes of vulnerabilities—memory corruption, authentication errors, authorization flaws, and exposure of management functions—show up se the underlying deployment model is long-lived and highly trusted. SAC is part of that pattern: a platform that was designed to simplify secure access can become a high-value target precisely because it centralizes trust.
The CISA note is also important because it frames the issue in practical, defensive language rather than pure code analysis. The agency recommends network isolation, firewalling, and cautious remote access because the risk is notdevice. Once a management product is reachable from a broader network than intended, the attack surface expands beyond the original design assumptions.
A CVSS score in this range is especially significant for industrial environments because high integrity impact is often more dangerous than a simple crash. If an attacker can influence how a control-plane product behaves, the result can be unauthorized configuration changes, access manipulaten behavior that looks legitimate in logs. That creates the kind of silent operational risk defenders hate most.
The no user interaction piece matters too. There is no need for a victim to click a malicious file or approve a prompt. That lowers the friction for abuse and makes the flaw more suitable for unattended or semi-unattended environments, where access brokers are used as part of routine operations. In industrial settings, that is eg that can sit quietly until someone finds a way to use it.
The scope changed component also deserves attention. When a flaw crosses boundaries inside a trusted management layer, the blast radius can extend beyond the original process or component. That is a subtle but important signal that the effect is not merely local instability; it can spill into other parts of the system’s security model.
For enterprises, the risk often shows up as unauthorized administrative reach, lateral movement, or loss of trust in privileged access workflows. That can still be serious, especially if the same controller is used across multiple sites or by centralized support teams. The key problem is that a secure-access tool tends to be trusted by design, and trusted tools are exactly where attackers like to hide.
The fact that CISA classifies the sector as Critical Mnges the tone of the response. In that environment, “patch later” often becomes “patch under pressure,” because defenders must balance business continuity against the risk of compromise. The best response is to avoid that false tradeoff by planning remediation quickly and validating it in a controlled window.
CISA’s guidance adds the standard but necessary control-system hardening advice. The agency recommends minimizing network exposure, placing control-syfirewalls, isolating them from business networks, and using VPNs when remote access is needed. Those recommendations are familiar, but they are still the foundation for reducing exposure to management-plane flaws.
The version boundary helps, though. When a vendor clearly states that versions prior to V5.8 are affected, defenders can turn the advisory into an inventory problem and then into a change-management task. That is far more actionable than a vague warning ” or “certain configurations.”
There is also a useful side effect to remediation: teams get a chance to review whether the product’s access paths are broader than they should be. Often, the act of patching reveals policy drift, old service accounts, or forgotten remote-access routes that deserve cleanup. In that sense, the advisory is not only a risk notification but also a chance to improve the security posture around the wh## The cost of delay
Delayed patching is especially risky here because the vulnerability sits in a management product. If an attacker gains leverage there, the consequences can ripple outward faster than in a single-host compromise. For that reason, the usual industrial excuse that “patchingason to deprioritize the issue; it is a reason to plan the fix carefully and move quickly.
Industrial systems increasingly depend on layers of embedded libraries, web interfaces, remote management software, and long-lived policy engines. That makes them efficient to deploy and hard to requalify, but it also creates the perfect conditions for lingerisure. A single flaw in a shared component can affect a vendor’s whole product line if the component sits deep enough in the stack.
This iry’s impact statement is more important than the specific CVE label. Arbitrary code execution and denial of service are the symptoms, but the underlying issue is that a trusted industrial access controller can be pushed into unsafe behavior. Once that happens, the attacker has not just broken a tool; they may have compromised a control path.
The broader lesson is simple: industrial software lives or dies by t trust boundaries. When those boundaries fail, the effect is rarely confined to one appliance. It reaches into maintenance workflows, administrative roles, and the systems that depend on the controller’s authority.
There is also the problem of hidden exposure. Industrial organizations often discover too late that older mages, or vendor-managed systems are still running in corners of the network. If those instances are below V5.8, the vulnerability may remain active even after the main fleet is patched.
It will also be worth watching whether Siemens or CISA publish follow-up technical detail on the exact code path, the affected workflows, or any mitigation nuance beyond patching. Sometimes the first advisory is intentionally concise, and later updates help operators understand whether to a specific configuration or more broadly reachable. That additional detail can shape detection, verification, and the urgency of field upgrades.
Source: CISA Siemens RUGGEDCOM CROSSBOW Station Access Controller (SAC) | CISA
The advisory is espause Siemens identifies the affected sector as Critical Manufacturing, with worldwide deployment and a company headquarters in Germany. That context matters because industrial access systems are rarely isolated in a clean lab-style environment. They are usually embedded in plants, utilities, and distributed manufacturing operations where patch windows are limited, change control is strict, and multiple teams depend on the same management plane. A vulnerability that would be “just a bug” in a small web app can become a serious operational event in a secure-access controller.
The technical root cause, as published ipoints to SQLite versions before 3.50.2, where the number of aggregate terms could exceed the number of available columns, leading to memory corruption. That kind of flaw is important because memory corruption is not merely a reliability problem; it can become a primitive for arbitrary code execution or a crash, depending on how an attacker can shape the inputs and the surrounding conditions. In industrial software, that is especially sensitive because management software often has privileged reach across multiple devices.
Siemens says the vendor fix is to update RUGGEDCOM CROSSBOW Sler (SAC) to V5.8 or later. That is the cleanest kind of remediation notice from a defender’s point of view: a clear version boundary, a known affected range, and a specific target for patch planning. The hard part is not understanding the fix; it is carrying it out safely in environments where uptime, validation, and vendor dependencies can slow deployment.
The CISA republication also repeats the familiar industrial-security playbook: mine, isolate control-system networks, use firewalls and VPNs carefully, and treat remote access as a risk that must be actively managed. That advice often sounds repetitive across advisories, but it persists for a reason. Industrial systems are frequently reachable in ways defenders did not intend, and a management interface with a high-severity flaw can become the easiest point of entry on the network.
 Why this advisory matters now
Why this advisory matters now
The timing is relevant. Siemens issued the advisory on April 14, 2lished it on April 21, 2026**. That short lag suggests the issue is current and operationally important, not an archival finding from an old release train. In industrial security, a one-week gap between vendor disclosure and government republication usually means defenders should already be inventorying exposure and planning remediation.What makes SAC different from a generic web service
SAC is not just “another admin portal.” It helps gate access to ind means a compromise can have downstream effects far beyond the controller itself. If an attacker can abuse the management layer, they may not need to attack field devices directly. That is why access-control software in OT environments deserves a higher bar than ordinary IT utilities.The Vulnerability in Context
At the center of this disclosure is CVE-2025-6965, a SQLite memory-corruption issue involving aggregatent handling. The advisory describes the problem as a condition where the number of aggregate terms can exceed the number of columns available, which can lead to memory corruption. That is a classic example of a small-seeming logic mismatch producing a security problem with large consequences.Memory corruption bugs matter because they can move a system from “unexpected crash” territory into “attacker-controlled behavior” territory. Whether the final impactecution, denial of service, or something in between depends on the implementation and the exact path taken through the vulnerable code. In other words, the same bug can look like a nuisance in one deployment and a serious takeover primitive in another.
Why SQLite bugs show up in industrial software
SQLite is widely used in embedded and appliance-style products because it is lightweight, self-contained, and easy to ship. That convenbut it also creates a familiar risk pattern: third-party components get embedded deeply into products that are expected to run for years. When the underlying library receives a security fix, the downstream vendor must validate and ship its own update, which can introduce delay even when the issue itself is already understood.This is one reason industrial advisories often feel repetitive. The same classes of vulnerabilities—memory corruption, authentication errors, authorization flaws, and exposure of management functions—show up se the underlying deployment model is long-lived and highly trusted. SAC is part of that pattern: a platform that was designed to simplify secure access can become a high-value target precisely because it centralizes trust.
The CISA note is also important because it frames the issue in practical, defensive language rather than pure code analysis. The agency recommends network isolation, firewalling, and cautious remote access because the risk is notdevice. Once a management product is reachable from a broader network than intended, the attack surface expands beyond the original design assumptions.
The practical exploitability question
Even when a vulnerability is technically serious, the real-world risk depends on how the product is deployed. If SAC is tucked behind tight segmentation and only reachable from a small set of hardened manageion becomes harder. If it is reachable from a flat internal network, a vendor support VLAN, or worse, a route that is broader than intended, the risk profile changes quickly.Severity and Scoring
The advisory labels the issue as CVSS v3.1 7.7 High, with the vector AV:N/AC:H/PR:L/UI:N/S:C/C:L/I:H/A:L. That combination is revealing. It says the issue is network-reachable, requires low privileges, needs no user interaction, and integrity impact even if confidentiality and availability effects are more limited. In plain English, this is the kind of flaw that deserves urgent patch planning rather than deferred maintenance.A CVSS score in this range is especially significant for industrial environments because high integrity impact is often more dangerous than a simple crash. If an attacker can influence how a control-plane product behaves, the result can be unauthorized configuration changes, access manipulaten behavior that looks legitimate in logs. That creates the kind of silent operational risk defenders hate most.
Why the vector details matter
The low privileges required part is the most unsettling from an operations standpoint. It means the flaw is not necessarily limited to an administrator with deep system control. Even a limited foothold can sometimes become a stepping stone if the affected code path is reachaccount or service condition. That is one reason authorization and management-plane flaws are often more dangerous than they first appear.The no user interaction piece matters too. There is no need for a victim to click a malicious file or approve a prompt. That lowers the friction for abuse and makes the flaw more suitable for unattended or semi-unattended environments, where access brokers are used as part of routine operations. In industrial settings, that is eg that can sit quietly until someone finds a way to use it.
The scope changed component also deserves attention. When a flaw crosses boundaries inside a trusted management layer, the blast radius can extend beyond the original process or component. That is a subtle but important signal that the effect is not merely local instability; it can spill into other parts of the system’s security model.
What 7.
A 7.7 score is not theoretical. It is high enough that asset owners should treat the advisory as a near-term remediation item, especially because the vendor fix is already available. The security question shifts from “Is this real?” to “How quickly can we safely move affected systems to V5.8 or later?”Enterprise, OT, and Critical
The impact of this advisory is strongest in OT and critical manufacturing environments because the product is part of the access path to industrial assets. In those settings, a management-plane flaw can become a force multiplier. The attacker may not need to compromise a production device directly if they can instead influence the so gets to talk to it.For enterprises, the risk often shows up as unauthorized administrative reach, lateral movement, or loss of trust in privileged access workflows. That can still be serious, especially if the same controller is used across multiple sites or by centralized support teams. The key problem is that a secure-access tool tends to be trusted by design, and trusted tools are exactly where attackers like to hide.
Why maally exposed
Manufacturing organizations often run with a mix of modern network controls and legacy operational habits. That combination can leave remote-access systems in place far longer than they should remain exposed. If SAC is serving as a bridge between operators and devices, then a flaw in that bridge can affect production scheduling, access control, and potentially the integrity of related workflloyment note matters too. A vulnerability with worldwide reach is a supply-chain and fleet-management problem, not just a site-specific issue. Enterprises with multiple plants or regions may have to verify different deployment patterns, different maintenance windows, and different supporting teams. That makes inventory accuracy a security control, not just an administrative convenience.The fact that CISA classifies the sector as Critical Mnges the tone of the response. In that environment, “patch later” often becomes “patch under pressure,” because defenders must balance business continuity against the risk of compromise. The best response is to avoid that false tradeoff by planning remediation quickly and validating it in a controlled window.
Enterprise vs. OT priorities
In enterprise IT, the immediate concern is usually unauthorble persistence. In OT, the same issue can also touch uptime and operational safety. That difference matters because an enterprise team may measure risk in terms of data exposure, while an OT team may measure it in terms of production stability and control integrity.What Siemens and CISA Recommend
Siemens’ primary recommendation is simple: update to V5.8 or later. That ecause it gives defenders a concrete target instead of a vague “apply patches when possible” message. In industrial security, a direct remediation path is often the difference between a manageable advisory and a lingering exposure.CISA’s guidance adds the standard but necessary control-system hardening advice. The agency recommends minimizing network exposure, placing control-syfirewalls, isolating them from business networks, and using VPNs when remote access is needed. Those recommendations are familiar, but they are still the foundation for reducing exposure to management-plane flaws.
Immediate action checklist
- Identify every SAC deployment in the environment.
- Confirm whether any instance is running earlier than V5.8.
- Pring or broadly reachable management paths.
- Schedule an upgrade to V5.8 or later in a validated maintenance window.
- Review network segmentation and remote-access paths around the product.
- Preserve logs for any suspicious administrative activity before and after remediation.
Why compensating controls still matter
Industrial patch cycles are often slower than security teams would prefer. Change windows are limited, compatibility has to be checked, and operational teams may need assurance that the update won’t disr In that gap between disclosure and deployment, segmentation, restricted access, and hardened remote connections are not substitutes for patching, but they are meaningful risk reducers.Patch Management and Operational Reality
The hard part of an advisory like this is not understanding the bug. It is coordinating the remediatial environment without breaking the workflows that rely on the product. That tension is common in OT: the same system that needs to be fixed may also be the system that operators depend on every day.The version boundary helps, though. When a vendor clearly states that versions prior to V5.8 are affected, defenders can turn the advisory into an inventory problem and then into a change-management task. That is far more actionable than a vague warning ” or “certain configurations.”
A sensible remediation sequence
- Build a complete asset list for SAC instances.
- Map each instance to its current version and network exposure.
- Validate whether the product is part of a critical access path.
- Test V5.8 or later in a staging or maintenance environment.
- Roll the update out in priority order by exposut.
- Recheck administrative roles, logs, and access policies after the upgrade.
- Document the new baseline so drift is easier to detect later.
There is also a useful side effect to remediation: teams get a chance to review whether the product’s access paths are broader than they should be. Often, the act of patching reveals policy drift, old service accounts, or forgotten remote-access routes that deserve cleanup. In that sense, the advisory is not only a risk notification but also a chance to improve the security posture around the wh## The cost of delay
Delayed patching is especially risky here because the vulnerability sits in a management product. If an attacker gains leverage there, the consequences can ripple outward faster than in a single-host compromise. For that reason, the usual industrial excuse that “patchingason to deprioritize the issue; it is a reason to plan the fix carefully and move quickly.
Why This Fits a Larger Industrial Pattern
This advisory fits a familiar industrial-security pattern: a trusted management product exposes a bug in a third-party component, and the resulting flaw reaches beyond the component itself. In other words, the problem is not just the code path; it is the role the code path ture. That is one of the reasons OT advisories carry outsized significance even when the root cause looks like a fairly ordinary software defect.Industrial systems increasingly depend on layers of embedded libraries, web interfaces, remote management software, and long-lived policy engines. That makes them efficient to deploy and hard to requalify, but it also creates the perfect conditions for lingerisure. A single flaw in a shared component can affect a vendor’s whole product line if the component sits deep enough in the stack.
The trust model problem
Access brokers are high-value targets because they decide who gets to do what. If that decision-making layer is flawed, the attacker may inherit the organization’s own trust assumptions. That is why security teams should think of access-control platforms as part of the attack surface, not merely as the thing defending it.This iry’s impact statement is more important than the specific CVE label. Arbitrary code execution and denial of service are the symptoms, but the underlying issue is that a trusted industrial access controller can be pushed into unsafe behavior. Once that happens, the attacker has not just broken a tool; they may have compromised a control path.
The broader lesson is simple: industrial software lives or dies by t trust boundaries. When those boundaries fail, the effect is rarely confined to one appliance. It reaches into maintenance workflows, administrative roles, and the systems that depend on the controller’s authority.
Strengths and Opportunities
The strongest part of this disclosure is its clarity. Siemens gives defenders a clear version thresho and a clear statement of impact, which makes exposure analysis far easier than in many industrial advisories. That clarity also creates an opportunity for teams to do more than patch: they can use the event to review access paths, segmentation, and version hygiene across their broader OT environment.- Clear remediation target: update to V5.8 or later.
- Straightforwarsions earlier than V5.8.
- Strong prioritization signal from a 7.7 High score.
- Meaningful operational impact because the product sits in the access path.
- Good opportunity to review network segmentation and remote-access policy.
- Useful trigger for inventory cleanup and version tracking.
- Chanceadministrative exposure is broader than intended.
Risks and Concerns
The biggest concern is that this is a flaw in a trusted control comral app. When a management platform is vulnerable, the attacker may be able to affect more than one device, more than one site, or more than one administrative workflow. That makes the blast radius potentially much larger than the software footprint alone suggests.- Patch lag in industrial environments can leave exposure open longer than expected.
- Broad management-network access can make exploitation easier.
- Shared admin accounts can complicate accountabiliegacy workflows may resist quick upgrades or validation.
- Compensating controls may be incomplete if segmentation is weak.
- Exploitation could look like legitimate administrative behavior in logs.
- A denial-of-service event could interrupt critical operations at the wrong time.
There is also the problem of hidden exposure. Industrial organizations often discover too late that older mages, or vendor-managed systems are still running in corners of the network. If those instances are below V5.8, the vulnerability may remain active even after the main fleet is patched.
Looking Ahead
The next thing to watch is how quickly defenders inventory SAC and move to V5.8 or later. That will be the best measure of whether the advisory becomes a brief patch cycle or a longer-lived exposure problem. In industrial environments, the difference is often determined less by the severity sity of asset visibility and change control.It will also be worth watching whether Siemens or CISA publish follow-up technical detail on the exact code path, the affected workflows, or any mitigation nuance beyond patching. Sometimes the first advisory is intentionally concise, and later updates help operators understand whether to a specific configuration or more broadly reachable. That additional detail can shape detection, verification, and the urgency of field upgrades.
What defenders should monitor next
- Deployment of V5.8 or later across SAC fleets.
- Any evidence of unusual administrative changes before patching.
- Whether are reachable from more networks than intended.
- New Siemens or CISA follow-up guidance.
- Signs that similar third-party library issues affect adjacent products.
Source: CISA Siemens RUGGEDCOM CROSSBOW Station Access Controller (SAC) | CISA