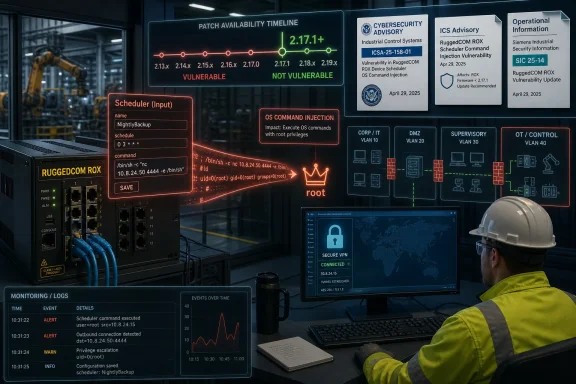
Siemens and CISA warned in mid-May 2026 that RUGGEDCOM ROX devices running versions earlier than 2.17.1 contain a critical Scheduler input-validation flaw that lets an authenticated remote attacker execute arbitrary operating-system commands as root. The advisory lands squarely in the uncomfortable middle of industrial security: the bug is not unauthenticated, but the prize is the whole box. For routers and switches living inside critical manufacturing networks, that distinction matters less than it sounds. Once an attacker has a foothold, “authenticated” can become a speed bump rather than a wall.
The affected Siemens RUGGEDCOM ROX line is not consumer networking gear sitting under a desk. These are ruggedized industrial networking devices used in environments where uptime, environmental tolerance, and operational continuity are the whole point. When a vulnerability in that class of device allows commands to run as root, defenders should read it less like a software bug and more like a potential control-plane compromise.
The flaw is described as an input validation vulnerability in the Scheduler functionality. In plainer terms, a feature designed to accept structured user input can reportedly be manipulated so that the underlying operating system interprets part of that input as a command. That is the classic shape of OS command injection, but the industrial context makes it more severe than the label alone conveys.
Schedulers are especially sensitive surfaces because they often exist to automate administrative tasks. They sit near privileged workflows by design. If a web interface, CLI path, or management feature takes user-controlled data and passes it too trustingly into shell-adjacent machinery, the bug is no longer about a malformed field. It is about whether a legitimate management feature can be turned into a remote shell.
The advisory’s CVSS v3 score of 9.1 reflects that gravity. It is not the highest possible score, and the need for authentication reduces the theoretical blast radius. But root-level command execution on a network device inside an operational technology environment is still the kind of vulnerability that can turn a compromised account into persistent infrastructure control.
An authenticated remote attacker does not have to be a rogue insider in the cinematic sense. It can be an adversary who phished a maintenance account, found reused credentials, compromised a jump host, or moved laterally from a less critical system into the management plane. Industrial networks often have better segmentation on paper than in practice, especially in older facilities where production demands have layered exceptions over the original security model.
The root privilege detail is what changes the risk calculation. A low-privilege management account becoming root on a device is not merely privilege escalation; it can become a launchpad. Network appliances see traffic, enforce routes, terminate management sessions, and sometimes sit in paths administrators barely remember until something breaks.
If an attacker can run arbitrary commands on the underlying operating system, they may be able to implant tooling, alter configurations, interfere with logging, create backdoor access, or disrupt availability. The advisory does not claim active exploitation, and defenders should avoid inventing facts not in evidence. But the possible consequences are broad enough that this is not a “wait until the next maintenance window someday” patch.
Version cutoffs are useful because they turn advisory prose into inventory logic. Security teams can ask a simple question: which ROX devices are below 2.17.1? The harder part is whether asset inventory is accurate enough to answer it.
In Windows-heavy enterprise environments, vulnerability management often leans on endpoint agents, domain inventory, and software update reporting. OT networking equipment rarely fits so neatly into that model. Devices may be monitored by network management platforms, documented in spreadsheets, or known mainly to the engineers who installed them years ago.
That is where a critical advisory becomes an audit of operational maturity. The patch exists, but the question becomes whether the organization can identify every affected device, determine its firmware version, validate compatibility, schedule downtime if needed, and prove completion. For industrial defenders, the distance between “vendor released an update” and “risk materially reduced” can be measured in weeks, months, or sometimes a fiscal year.
The CISA text also frames the issue in critical infrastructure language. The affected sector is listed as critical manufacturing, with worldwide deployment and Siemens headquartered in Germany. That does not mean every vulnerable ROX device sits in a factory. It means the product class and known deployment patterns are important enough for the U.S. cyber agency’s ICS pipeline.
The advisory also names the researchers from Palo Alto Networks’ OT Threat Research Lab who reported the vulnerability to Siemens. That detail matters because it suggests a coordinated disclosure path rather than a public exploit dump. Coordinated disclosure buys defenders time, but it also starts a clock: once the advisory is public, attackers can study the same clues defenders are reading.
The conversion note is worth reading with some skepticism, too. CISA says the item is a verbatim republication of Siemens’ CSAF advisory and is provided as-is. In other words, this is not CISA performing an independent technical teardown. It is a visibility boost for vendor-supplied details, and defenders should treat Siemens’ update guidance as the operational source of truth.
Industrial appliances add another wrinkle: they are built for long service lives. That is an admirable engineering goal, but it clashes with the cadence of modern vulnerability research. A device that once lived on an isolated network may now be reachable through remote access, integrated monitoring, cloud-adjacent workflows, or vendor support paths that did not exist when the asset was deployed.
The RUGGEDCOM ROX case is not the first time Siemens has had to deal with command-injection-style issues in this product ecosystem. Recent years have seen multiple RUGGEDCOM ROX advisories involving third-party components and command execution risks. That does not make Siemens unusual; it makes Siemens part of a broader appliance-security reality in which firmware is an operating system distribution, a management application, and a vendor platform all at once.
The industry’s problem is that appliances have historically been treated as quieter than servers. They are configured, mounted, monitored lightly, and expected to disappear into the background. Attackers have learned the opposite lesson: infrastructure devices are valuable precisely because defenders assume they are static.
That tension is not irrational. Updating industrial network equipment can carry real risk. A failed firmware upgrade can interrupt production, break compatibility with legacy configurations, or trigger emergency work under worse conditions than a planned change. OT teams are not being stubborn when they ask for testing.
But the authentication requirement should not be used as an excuse to defer indefinitely. If management access is reachable from a corporate network segment, a remote access zone, or a shared engineering workstation, then the vulnerability is part of the lateral-movement story. Attackers do not need a direct internet-exposed ROX interface if they can compromise the systems that administrators use to reach it.
The right response is not blind urgency; it is disciplined urgency. Inventory first, exposure review second, patch planning third, monitoring throughout. If the asset cannot be patched immediately, the organization should be able to explain why, for how long, and what compensating controls stand in front of it.
A critical command-injection bug is a forcing function for reviewing who can reach the management interface. If the answer is “only a dedicated management station inside a segmented OT zone,” the organization is in a better place. If the answer is “anyone on the plant network,” the authentication requirement becomes far less reassuring.
Segmentation should not be treated as a diagramming exercise. Firewall rules, VPN group membership, jump-host access, local administrator rights, and shared engineering credentials all determine whether the vulnerable interface is genuinely protected. A network map that says “OT isolated” but allows broad remote maintenance access is a comfort document, not a control.
The same logic applies to logging. If commands can be executed as root, defenders should know what normal administrative activity looks like on ROX devices. They should preserve logs, monitor configuration changes, watch for unexpected scheduled tasks, and investigate anomalous management sessions. Patching removes the known flaw; monitoring helps answer whether anyone reached it first.
Administrators like web interfaces because they reduce friction. Vendors like them because they simplify configuration and support. Attackers like them because they concentrate privileged operations behind forms, parameters, and APIs that can sometimes be bent into unintended behavior.
In consumer and enterprise gear, the industry has learned this lesson repeatedly through router and firewall vulnerabilities. In OT, the lesson is harsher because availability requirements slow remediation and because devices may sit near processes that are expensive, dangerous, or politically difficult to interrupt. A root shell on a ruggedized router is not automatically a plant shutdown, but it can be a foothold in the part of the network where defenders least want improvisation.
The fix for that reality is not to abolish management interfaces. It is to treat them as privileged services. Access should be narrow, authenticated strongly, logged, and separated from ordinary user traffic. If a scheduler can launch tasks, it should be assumed to live near dangerous capability until proven otherwise.
That makes Windows hygiene part of the ROX risk surface. A compromised domain account with access to engineering workstations can become the first step toward an authenticated attack on an industrial appliance. A poorly segmented jump server can collapse the boundary between enterprise IT and OT. A stale VPN client can become a bridge into management interfaces that were never meant to be broadly reachable.
This is why IT and OT cannot treat each other as separate kingdoms when a vulnerability like this appears. The OT team may own the firmware update. The IT team may own identity, endpoint protection, remote access, logging, backup, and incident response tooling. The risk lives in the seam.
For Windows-centric shops supporting industrial operations, the practical question is not simply “Do we have Siemens ROX devices?” It is also “Which Windows systems can reach them, which users can authenticate to them, and how would we know if those systems were abused?” That is a more uncomfortable set of questions, but it is the set that reflects how intrusions actually unfold.
That is enough information for attackers to begin triage. They know the product family, the affected feature, the vulnerability class, the privilege outcome, and the fixed version. Even without public exploit code, that narrows the search space.
Defenders often overestimate the time between advisory publication and adversary experimentation. For internet-facing enterprise products, that window can be brutally short. OT devices are less uniformly exposed, but the research value is still there, especially for adversaries interested in persistence inside industrial environments.
The absence of reported exploitation is welcome, if it holds. It should not be mistaken for evidence that the flaw is uninteresting. A vulnerability that requires authentication may be especially useful after initial access, and post-compromise exploitation is harder to observe from the outside than mass scanning.
That is why root-level flaws in infrastructure equipment deserve a higher level of seriousness than comparable flaws in isolated applications. An attacker who compromises a workstation gains access to that workstation and perhaps its user context. An attacker who compromises a network device may gain access to traffic paths, management planes, routing decisions, and trust relationships that many other systems depend on.
In an industrial network, that trust has operational meaning. Engineers may assume that device behavior reflects configuration. Monitoring tools may assume that routes and logs are reliable. Incident responders may assume that network appliances are part of the defensive foundation rather than part of the adversary’s foothold.
The RUGGEDCOM ROX advisory is therefore not just about patching a scheduler. It is about preserving confidence in the devices that make segmentation, remote maintenance, and operational visibility possible. When those devices become questionable, the entire security model gets foggier.
The Siemens RUGGEDCOM ROX vulnerability is a reminder that the most consequential bugs are often not spectacular zero-click miracles but mundane input-validation failures in trusted administrative features. Siemens has drawn the patch line at 2.17.1, and CISA has amplified the warning; what happens next depends on whether operators treat this as a firmware chore or as a test of how well they understand the networks their production environments depend on.
Source: CISA Siemens Ruggedcom Rox | CISA
 The Dangerous Word Here Is Not “Scheduler,” It Is “Root”
The Dangerous Word Here Is Not “Scheduler,” It Is “Root”
The affected Siemens RUGGEDCOM ROX line is not consumer networking gear sitting under a desk. These are ruggedized industrial networking devices used in environments where uptime, environmental tolerance, and operational continuity are the whole point. When a vulnerability in that class of device allows commands to run as root, defenders should read it less like a software bug and more like a potential control-plane compromise.The flaw is described as an input validation vulnerability in the Scheduler functionality. In plainer terms, a feature designed to accept structured user input can reportedly be manipulated so that the underlying operating system interprets part of that input as a command. That is the classic shape of OS command injection, but the industrial context makes it more severe than the label alone conveys.
Schedulers are especially sensitive surfaces because they often exist to automate administrative tasks. They sit near privileged workflows by design. If a web interface, CLI path, or management feature takes user-controlled data and passes it too trustingly into shell-adjacent machinery, the bug is no longer about a malformed field. It is about whether a legitimate management feature can be turned into a remote shell.
The advisory’s CVSS v3 score of 9.1 reflects that gravity. It is not the highest possible score, and the need for authentication reduces the theoretical blast radius. But root-level command execution on a network device inside an operational technology environment is still the kind of vulnerability that can turn a compromised account into persistent infrastructure control.
Authentication Is a Control, Not a Comfort Blanket
The most tempting mistake is to downgrade the incident mentally because the attacker must be authenticated. In enterprise IT, that qualifier often means the exploit is downstream of another failure. In OT, it can mean something different: shared accounts, long-lived credentials, flat management networks, vendor access paths, stale VPN configurations, and devices that are hard to patch because the plant schedule owns the calendar.An authenticated remote attacker does not have to be a rogue insider in the cinematic sense. It can be an adversary who phished a maintenance account, found reused credentials, compromised a jump host, or moved laterally from a less critical system into the management plane. Industrial networks often have better segmentation on paper than in practice, especially in older facilities where production demands have layered exceptions over the original security model.
The root privilege detail is what changes the risk calculation. A low-privilege management account becoming root on a device is not merely privilege escalation; it can become a launchpad. Network appliances see traffic, enforce routes, terminate management sessions, and sometimes sit in paths administrators barely remember until something breaks.
If an attacker can run arbitrary commands on the underlying operating system, they may be able to implant tooling, alter configurations, interfere with logging, create backdoor access, or disrupt availability. The advisory does not claim active exploitation, and defenders should avoid inventing facts not in evidence. But the possible consequences are broad enough that this is not a “wait until the next maintenance window someday” patch.
Siemens Fixes the Line at 2.17.1, Which Gives Administrators a Clear Cutoff
The remediation is straightforward on paper: update affected RUGGEDCOM ROX products to version 2.17.1 or later. The affected list includes MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000 devices running versions earlier than 2.17.1. That broad family coverage matters because many organizations standardize on RUGGEDCOM across sites, substations, production lines, or transport-heavy industrial networks.Version cutoffs are useful because they turn advisory prose into inventory logic. Security teams can ask a simple question: which ROX devices are below 2.17.1? The harder part is whether asset inventory is accurate enough to answer it.
In Windows-heavy enterprise environments, vulnerability management often leans on endpoint agents, domain inventory, and software update reporting. OT networking equipment rarely fits so neatly into that model. Devices may be monitored by network management platforms, documented in spreadsheets, or known mainly to the engineers who installed them years ago.
That is where a critical advisory becomes an audit of operational maturity. The patch exists, but the question becomes whether the organization can identify every affected device, determine its firmware version, validate compatibility, schedule downtime if needed, and prove completion. For industrial defenders, the distance between “vendor released an update” and “risk materially reduced” can be measured in weeks, months, or sometimes a fiscal year.
CISA’s Republication Is a Signal to Broaden the Audience
CISA republished the Siemens ProductCERT advisory through its industrial control systems channel on May 14, 2026, after Siemens’ May 12 advisory. That republication is not just bureaucratic mirroring. It is a distribution mechanism aimed at organizations that may not follow every vendor portal but do track CISA ICS advisories as part of their risk process.The CISA text also frames the issue in critical infrastructure language. The affected sector is listed as critical manufacturing, with worldwide deployment and Siemens headquartered in Germany. That does not mean every vulnerable ROX device sits in a factory. It means the product class and known deployment patterns are important enough for the U.S. cyber agency’s ICS pipeline.
The advisory also names the researchers from Palo Alto Networks’ OT Threat Research Lab who reported the vulnerability to Siemens. That detail matters because it suggests a coordinated disclosure path rather than a public exploit dump. Coordinated disclosure buys defenders time, but it also starts a clock: once the advisory is public, attackers can study the same clues defenders are reading.
The conversion note is worth reading with some skepticism, too. CISA says the item is a verbatim republication of Siemens’ CSAF advisory and is provided as-is. In other words, this is not CISA performing an independent technical teardown. It is a visibility boost for vendor-supplied details, and defenders should treat Siemens’ update guidance as the operational source of truth.
The Scheduler Bug Fits a Larger Pattern in Appliance Security
Command injection in network appliances is an old class of flaw, but it keeps resurfacing because appliances are complicated computers disguised as infrastructure. They expose web interfaces, APIs, CLIs, configuration parsers, diagnostic tools, certificate utilities, logging systems, and automated jobs. Each feature is a place where user input may eventually touch privileged operating-system functions.Industrial appliances add another wrinkle: they are built for long service lives. That is an admirable engineering goal, but it clashes with the cadence of modern vulnerability research. A device that once lived on an isolated network may now be reachable through remote access, integrated monitoring, cloud-adjacent workflows, or vendor support paths that did not exist when the asset was deployed.
The RUGGEDCOM ROX case is not the first time Siemens has had to deal with command-injection-style issues in this product ecosystem. Recent years have seen multiple RUGGEDCOM ROX advisories involving third-party components and command execution risks. That does not make Siemens unusual; it makes Siemens part of a broader appliance-security reality in which firmware is an operating system distribution, a management application, and a vendor platform all at once.
The industry’s problem is that appliances have historically been treated as quieter than servers. They are configured, mounted, monitored lightly, and expected to disappear into the background. Attackers have learned the opposite lesson: infrastructure devices are valuable precisely because defenders assume they are static.
The Patch Is Simple; the Deployment Politics Are Not
For a WindowsForum audience, it is tempting to compare this to Patch Tuesday: identify vulnerable systems, test, deploy, report compliance. Industrial firmware updates rarely move with that rhythm. A router or switch supporting production traffic may require a formal outage window, rollback plan, vendor coordination, and signoff from operations managers who are judged on availability rather than theoretical security exposure.That tension is not irrational. Updating industrial network equipment can carry real risk. A failed firmware upgrade can interrupt production, break compatibility with legacy configurations, or trigger emergency work under worse conditions than a planned change. OT teams are not being stubborn when they ask for testing.
But the authentication requirement should not be used as an excuse to defer indefinitely. If management access is reachable from a corporate network segment, a remote access zone, or a shared engineering workstation, then the vulnerability is part of the lateral-movement story. Attackers do not need a direct internet-exposed ROX interface if they can compromise the systems that administrators use to reach it.
The right response is not blind urgency; it is disciplined urgency. Inventory first, exposure review second, patch planning third, monitoring throughout. If the asset cannot be patched immediately, the organization should be able to explain why, for how long, and what compensating controls stand in front of it.
Segmentation Is Where the Advisory Becomes an Architecture Review
CISA’s recommended practices are familiar: minimize network exposure, keep control-system devices off the internet, place control networks and remote devices behind firewalls, isolate them from business networks, and use secure remote access methods such as updated VPNs when remote access is required. The familiarity is the problem. These recommendations are repeated so often because organizations still fail at them in practical, boring ways.A critical command-injection bug is a forcing function for reviewing who can reach the management interface. If the answer is “only a dedicated management station inside a segmented OT zone,” the organization is in a better place. If the answer is “anyone on the plant network,” the authentication requirement becomes far less reassuring.
Segmentation should not be treated as a diagramming exercise. Firewall rules, VPN group membership, jump-host access, local administrator rights, and shared engineering credentials all determine whether the vulnerable interface is genuinely protected. A network map that says “OT isolated” but allows broad remote maintenance access is a comfort document, not a control.
The same logic applies to logging. If commands can be executed as root, defenders should know what normal administrative activity looks like on ROX devices. They should preserve logs, monitor configuration changes, watch for unexpected scheduled tasks, and investigate anomalous management sessions. Patching removes the known flaw; monitoring helps answer whether anyone reached it first.
The Web Interface Is the New Perimeter for Old Infrastructure
The advisory language points to Scheduler functionality, and secondary reporting has described exploitation through management-facing functionality. Even when details are sparse, the lesson is clear: web management interfaces have become one of the most important security boundaries in infrastructure equipment. They are also among the easiest to underestimate.Administrators like web interfaces because they reduce friction. Vendors like them because they simplify configuration and support. Attackers like them because they concentrate privileged operations behind forms, parameters, and APIs that can sometimes be bent into unintended behavior.
In consumer and enterprise gear, the industry has learned this lesson repeatedly through router and firewall vulnerabilities. In OT, the lesson is harsher because availability requirements slow remediation and because devices may sit near processes that are expensive, dangerous, or politically difficult to interrupt. A root shell on a ruggedized router is not automatically a plant shutdown, but it can be a foothold in the part of the network where defenders least want improvisation.
The fix for that reality is not to abolish management interfaces. It is to treat them as privileged services. Access should be narrow, authenticated strongly, logged, and separated from ordinary user traffic. If a scheduler can launch tasks, it should be assumed to live near dangerous capability until proven otherwise.
Windows Administrators Are Still Part of This Story
At first glance, a Siemens industrial router advisory may look outside the Windows admin lane. It is not. In many organizations, the workstations used to manage OT equipment run Windows, the identity systems that govern access are connected to Microsoft infrastructure, and the remote access stack often passes through Windows servers, VPN clients, jump boxes, or management consoles.That makes Windows hygiene part of the ROX risk surface. A compromised domain account with access to engineering workstations can become the first step toward an authenticated attack on an industrial appliance. A poorly segmented jump server can collapse the boundary between enterprise IT and OT. A stale VPN client can become a bridge into management interfaces that were never meant to be broadly reachable.
This is why IT and OT cannot treat each other as separate kingdoms when a vulnerability like this appears. The OT team may own the firmware update. The IT team may own identity, endpoint protection, remote access, logging, backup, and incident response tooling. The risk lives in the seam.
For Windows-centric shops supporting industrial operations, the practical question is not simply “Do we have Siemens ROX devices?” It is also “Which Windows systems can reach them, which users can authenticate to them, and how would we know if those systems were abused?” That is a more uncomfortable set of questions, but it is the set that reflects how intrusions actually unfold.
The Disclosure Timeline Leaves Little Room for Complacency
The public sequence is compact. Siemens published the advisory on May 12, 2026. CISA republished it on May 14, 2026. The affected versions are all releases earlier than 2.17.1, and Siemens says updated versions are available.That is enough information for attackers to begin triage. They know the product family, the affected feature, the vulnerability class, the privilege outcome, and the fixed version. Even without public exploit code, that narrows the search space.
Defenders often overestimate the time between advisory publication and adversary experimentation. For internet-facing enterprise products, that window can be brutally short. OT devices are less uniformly exposed, but the research value is still there, especially for adversaries interested in persistence inside industrial environments.
The absence of reported exploitation is welcome, if it holds. It should not be mistaken for evidence that the flaw is uninteresting. A vulnerability that requires authentication may be especially useful after initial access, and post-compromise exploitation is harder to observe from the outside than mass scanning.
The Real Asset Is Trust in the Network Itself
Network infrastructure has a special role in incident response because it is both a target and an instrument. Defenders rely on routers, switches, firewalls, and logging paths to understand what is happening during an intrusion. If those devices are compromised, visibility and control degrade at the same time.That is why root-level flaws in infrastructure equipment deserve a higher level of seriousness than comparable flaws in isolated applications. An attacker who compromises a workstation gains access to that workstation and perhaps its user context. An attacker who compromises a network device may gain access to traffic paths, management planes, routing decisions, and trust relationships that many other systems depend on.
In an industrial network, that trust has operational meaning. Engineers may assume that device behavior reflects configuration. Monitoring tools may assume that routes and logs are reliable. Incident responders may assume that network appliances are part of the defensive foundation rather than part of the adversary’s foothold.
The RUGGEDCOM ROX advisory is therefore not just about patching a scheduler. It is about preserving confidence in the devices that make segmentation, remote maintenance, and operational visibility possible. When those devices become questionable, the entire security model gets foggier.
The Version Number That Should Drive the Next Maintenance Meeting
The immediate lesson is refreshingly concrete: 2.17.1 is the line administrators should use to separate patched from potentially vulnerable ROX deployments. But the broader lesson is that industrial infrastructure vulnerabilities are rarely solved by reading the advisory alone. The advisory starts the work; asset knowledge and operational discipline finish it.- Organizations running affected RUGGEDCOM ROX MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, or RX5000 devices should identify any installations below version 2.17.1.
- Administrators should prioritize devices whose management interfaces are reachable from broader enterprise networks, remote access environments, shared engineering workstations, or vendor support paths.
- Teams that cannot patch immediately should narrow management access, review firewall rules, validate VPN exposure, and monitor for suspicious Scheduler activity or unexpected configuration changes.
- Windows and identity administrators should verify which accounts and workstations can reach ROX management interfaces, because authenticated appliance exploitation often begins with ordinary credential compromise.
- Incident response teams should treat network-device integrity as part of their investigation plan, not as an assumption baked into the environment.
The Siemens RUGGEDCOM ROX vulnerability is a reminder that the most consequential bugs are often not spectacular zero-click miracles but mundane input-validation failures in trusted administrative features. Siemens has drawn the patch line at 2.17.1, and CISA has amplified the warning; what happens next depends on whether operators treat this as a firmware chore or as a test of how well they understand the networks their production environments depend on.
Source: CISA Siemens Ruggedcom Rox | CISA