Microsoft’s title and the CVSS vector are describing two different things, so they are not actually in conflict.
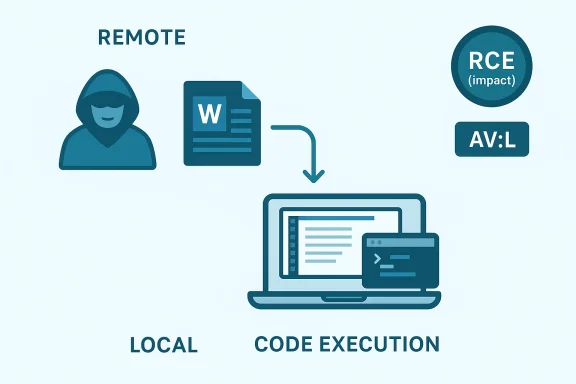
The “Remote Code Execution” label in the CVE title is about the impact and the attacker’s ability to reach the victim indirectly: an attacker can send a malicious Word document or otherwise get the victim to process crafted content, and the result can be code execution on the victim machine. That is why Microsoft can still call it RCE even when the exploit is not executed over the network in the classic sense. Microsoft has used this framing for years in Office cases where a remote attacker delivers a payload that is triggered locally when Word opens or parses the file.
By contrast, AV:L in CVSS is a scoring field, and it describes where the vulnerable code is triggered: locally on the target system, through a local file-processing path. In other words, the exploit happens when Word on the victim’s computer processes the malicious input, even if the attacker who supplied that input is remote. That is why you often see Microsoft Office vulnerabilities described as “remote code execution” while still being scored with a local attack vector.
So the clean way to read CVE-2026-33095 is this:
- A remote attacker can deliver the malicious document or lure the user into opening it.
- The trigger occurs locally inside Word on the victim’s machine.
- The impact is code execution, which is why Microsoft uses the RCE label.
- The CVSS vector uses AV:L because the exploit path is local from the scoring perspective.
Source: MSRC Security Update Guide - Microsoft Security Response Center