A newly published Linux kernel CVE is drawing attention for a reason that should concern anyone running embedded or appliance-class Linux systems: CVE-2026-31485 is a use-after-free-style teardown race in the spi-fsl-lpspi driver, and the upstream fix changes controller registration and removal ordering to stop DMA teardown from colliding with in-flight transfers. The advisory text says the driver used
This CVE is a good example of how kernel bugs often arise not from a single bad pointer, but from a lifecycle mismatch between two pieces of code that each think they own the timeline. In this case, the SPI controller’s lifetime was managed by devres semantics, while the DMA teardown in
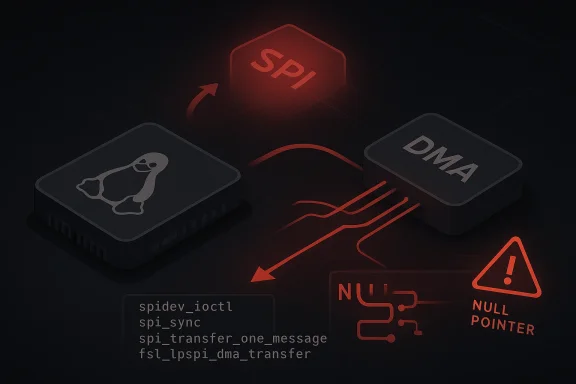
What makes this issue especially instructive is that the failure is not abstract. The CVE description includes a concrete crash trace involving
The fix is straightforward in concept but significant in effect: switch from
There is also an enterprise lesson here. SPI controller bugs are easy to dismiss because they often affect hardware-specific or embedded deployments, but those are exactly the environments where crashes are costly and recoverability is limited. If a board firmware, industrial controller, router, or appliance ships this driver, the vulnerability can become a reliability issue even before anyone asks whether it is exploitable in the classic sense.
The spi-fsl-lpspi driver is for NXP/Freescale-style low-power SPI controllers, which are common in embedded and industrial designs. These drivers tend to be performance-conscious, rely on DMA to reduce CPU overhead, and are expected to cope with tight hardware timing. That makes teardown order more than a code hygiene issue; it is part of the driver’s correctness contract.
The published description points to a familiar kernel pattern: a “managed” registration helper, in this case
The crash trace in the advisory is important because it shows the bug is triggered through spidev, the generic user-space SPI interface. That means a normal application using SPI ioctl calls can be enough to exercise the race if the timing is unlucky. In practice, that is a strong indicator that the bug is not merely theoretical, even if the exact exploitability remains uncertain.
This CVE highlights a classic rule: do not let the object that owns callbacks outlive the resources those callbacks depend on. Here, the SPI controller remained registered long enough for a transfer to enter the path after DMA teardown had started. That is a textbook race condition in kernel driver design.
That order matters because SPI transfers can still be active while the controller is visible to the rest of the subsystem. If a transfer arrives in that window, the driver may attempt DMA operations using structures that have already been destroyed. The advisory describes the outcome as an I/O error in DMA RX followed by a kernel NULL pointer dereference, consistent with use-after-free behavior in the path .
The crash trace shows the path from user space to kernel failure very clearly. The call flow begins at
That is why the fix is not a patch to a single dereference site. The right fix is to change who controls unregistration so the driver can guarantee the controller disappears before DMA teardown begins. That is exactly what the upstream change does by replacing devres-managed registration with explicit register/unregister calls .
This matters because explicit unregistration changes the order of shutdown. The controller is removed from service before remove proceeds to the point where DMA channels are torn down. As a result, late SPI activity can no longer enter the driver through a live controller object while hardware resources are already gone.
That is a very kernel-native fix. Rather than adding broad locks or trying to paper over the symptom at the crash site, it restores a sane ownership boundary. The code now tells the subsystem exactly when the controller is no longer available, which is the safest way to prevent stale callbacks and invalid resource use.
At the same time, the bug is serious enough that downstream maintainers will likely want the patch even on otherwise conservative kernel lines. Teardown-order crashes tend to be hard to reproduce in test labs but easy to hit in real workloads where device removal, hotplug, or service restarts happen under load.
The more important point is that a bug like this can show up as a hard crash, not just a transient error. When teardown races hit a kernel driver, the symptoms often look like device flakiness until a NULL dereference or panic makes the real cause obvious. That makes it especially dangerous in products that are expected to run unattended.
Enterprises should also think in terms of hardware inventory, not just distribution version numbers. A system might run a patched kernel branch but still carry vendor backports or board support package code with subtle differences. The question is not only “is the kernel updated?” but also “does this specific board or SoC driver include the teardown fix?”
That matters because availability is a legitimate security property. If a bug can take down a device in a critical control path, it affects safety, uptime, and service continuity. For embedded and industrial systems, those outcomes can be more serious than a conventional desktop crash because recovery may require physical access or a full power cycle.
There is also a broader kernel-security principle at play here: lifetime errors are often the first step in more serious memory-safety problems. Not every use-after-free becomes a weaponized exploit, but every use-after-free deserves scrutiny because it means code is still touching memory after the system has decided that memory is no longer valid.
For hardware vendors, the competitive implication is straightforward. Customers notice who ships stable backports fast, who documents them clearly, and who avoids introducing regressions in embedded firmware updates. In an environment where devices are often deployed for years, remediation quality becomes part of product quality.
For enterprises running mixed fleets, the lesson is to track hardware-specific CVEs alongside general OS advisories. A broad patch cycle may not catch a driver like this if the affected controller only exists on a subset of systems. That can leave a blind spot where the OS appears current but a board-specific kernel path remains vulnerable.
If your environment exposes SPI to user-space through
Testing should focus on stop-start cycles, device removal, service restarts, and any automation that might interrupt SPI activity. In other words, try to recreate the conditions under which teardown can overlap with active transfers. That is where this class of bug lives.
It also preserves the existing architecture. There is no hint in the advisory that the driver needed a redesign of its DMA engine, message pump, or SPI transfer semantics. The issue was one of ordering and ownership, not a broken controller model. That makes the correction easier to reason about and easier to backport.
In a broader sense, this is exactly how mature kernel maintenance should work: identify the lifetime bug, fix the teardown sequence, and keep the behavioral surface area small. That reduces the chance that a security patch itself becomes a new source of regressions.
It also creates an opportunity for hardware vendors and distribution maintainers to demonstrate patch discipline in a part of the stack that is often under-tested compared with server networking or desktop graphics. Good embedded patch hygiene is a real differentiator, especially for customers who care about uptime and predictability.
A second concern is patch visibility. Vendor kernels may contain the fix in some branches but not others, and board support packages can lag mainline by a wide margin. If administrators rely only on generic version checks, they may miss the vulnerable path entirely.
A third concern is that teardown races are hard to reproduce. That means the bug may survive through casual QA, only to surface in the field during rare but perfectly ordinary operations like device reset, service restart, or hardware replacement.
The other thing to watch is whether the disclosure prompts closer attention to teardown ordering in other SPI drivers. Kernel bugs often cluster around similar patterns, and any place that combines managed registration, DMA teardown, and asynchronous transfers deserves extra review. This is especially true in subsystems where hardware callbacks can still be live while device removal is underway.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
devm_spi_register_controller(), which delayed controller unregistration until after fsl_lpspi_remove() returned, while the remove path synchronously tore down DMA channels; if a transfer was still running, the result could be a NULL dereference in fsl_lpspi_dma_transfer() and a crash in the SPI stack . Although the NVD entry does not yet provide a CVSS score, the issue is already public, already mapped to a kernel fix, and already relevant to any fleet that depends on this SPI controller path .
 Overview
Overview
This CVE is a good example of how kernel bugs often arise not from a single bad pointer, but from a lifecycle mismatch between two pieces of code that each think they own the timeline. In this case, the SPI controller’s lifetime was managed by devres semantics, while the DMA teardown in fsl_lpspi_remove() assumed the controller was no longer active. Those assumptions were not aligned, and the result was a race window where a transfer could still execute after DMA resources had already been dismantled .What makes this issue especially instructive is that the failure is not abstract. The CVE description includes a concrete crash trace involving
spidev_ioctl(), spi_sync(), __spi_pump_transfer_message(), spi_transfer_one_message(), fsl_lpspi_transfer_one(), and finally fsl_lpspi_dma_transfer() before the NULL pointer dereference occurs . That trace shows the bug lives in a normal operational path, not in some obscure debug hook, which raises its importance for systems that use SPI devices under load.The fix is straightforward in concept but significant in effect: switch from
devm_spi_register_controller() to spi_register_controller() in probe, then explicitly call spi_unregister_controller() in remove . That gives the driver direct control over teardown ordering, ensuring the SPI controller is unregistered before DMA channels are synchronously torn down. In kernel terms, that is often the difference between a clean shutdown and a race that can crash the machine.There is also an enterprise lesson here. SPI controller bugs are easy to dismiss because they often affect hardware-specific or embedded deployments, but those are exactly the environments where crashes are costly and recoverability is limited. If a board firmware, industrial controller, router, or appliance ships this driver, the vulnerability can become a reliability issue even before anyone asks whether it is exploitable in the classic sense.
Background
The Linux SPI subsystem sits beneath a broad range of peripherals: flash chips, sensors, radios, display controllers, and embedded management chips. On many systems, SPI is not “optional plumbing”; it is a core bus used to move data between the SoC and attached hardware. That means a bug in one controller driver can have consequences far beyond the driver itself, especially when transfer handling is coupled with DMA for performance.The spi-fsl-lpspi driver is for NXP/Freescale-style low-power SPI controllers, which are common in embedded and industrial designs. These drivers tend to be performance-conscious, rely on DMA to reduce CPU overhead, and are expected to cope with tight hardware timing. That makes teardown order more than a code hygiene issue; it is part of the driver’s correctness contract.
The published description points to a familiar kernel pattern: a “managed” registration helper, in this case
devm_spi_register_controller(), is convenient because it ties cleanup to device lifetime. But convenience becomes risky when driver-specific teardown requires a particular sequence. If the controller remains registered while DMA resources are being torn down, a user-space-triggered SPI transaction can still enter the transfer path and touch resources that are already gone .The crash trace in the advisory is important because it shows the bug is triggered through spidev, the generic user-space SPI interface. That means a normal application using SPI ioctl calls can be enough to exercise the race if the timing is unlucky. In practice, that is a strong indicator that the bug is not merely theoretical, even if the exact exploitability remains uncertain.
Why teardown order matters
Kernel subsystems often appear robust in the steady state and fragile during teardown. That is because teardown is where object lifetimes overlap and where “still referenced” becomes “already freed” with very little warning. If asynchronous work, DMA, or queued I/O can continue while cleanup is in progress, then the removal path must be synchronized very carefully.This CVE highlights a classic rule: do not let the object that owns callbacks outlive the resources those callbacks depend on. Here, the SPI controller remained registered long enough for a transfer to enter the path after DMA teardown had started. That is a textbook race condition in kernel driver design.
What Actually Broke
At the center of the bug is a mismatch between registration lifetime and hardware teardown lifetime.devm_spi_register_controller() defers controller unregistration until the device-managed cleanup phase, which happens after the driver’s remove callback returns. But fsl_lpspi_remove() apparently tears down DMA channels synchronously inside remove, before the controller has been fully unregistered .That order matters because SPI transfers can still be active while the controller is visible to the rest of the subsystem. If a transfer arrives in that window, the driver may attempt DMA operations using structures that have already been destroyed. The advisory describes the outcome as an I/O error in DMA RX followed by a kernel NULL pointer dereference, consistent with use-after-free behavior in the path .
The crash trace shows the path from user space to kernel failure very clearly. The call flow begins at
spidev_ioctl(), passes through spi_sync(), then into spi_transfer_one_message(), and finally reaches the driver’s DMA transfer logic. That chain tells us this is not a one-off fault in a helper; it is a failure of teardown sequencing under normal subsystem execution .The role of DMA
DMA makes this class of bug more delicate because the hardware engine and the driver both participate in transfer completion. Once the channels are torn down, callbacks or error handling paths may still assume those channels exist. If the driver does not fence off new transfers before tearing down DMA, it can end up with a controller still accepting work but no backing engine to complete it.That is why the fix is not a patch to a single dereference site. The right fix is to change who controls unregistration so the driver can guarantee the controller disappears before DMA teardown begins. That is exactly what the upstream change does by replacing devres-managed registration with explicit register/unregister calls .
The Fix and Why It Works
The published remedy is clean and minimal. Infsl_lpspi_probe(), the driver no longer uses devm_spi_register_controller(). Instead, it calls spi_register_controller(), and in fsl_lpspi_remove() it adds the matching spi_unregister_controller() call . That reasserts driver control over the controller’s lifetime.This matters because explicit unregistration changes the order of shutdown. The controller is removed from service before remove proceeds to the point where DMA channels are torn down. As a result, late SPI activity can no longer enter the driver through a live controller object while hardware resources are already gone.
That is a very kernel-native fix. Rather than adding broad locks or trying to paper over the symptom at the crash site, it restores a sane ownership boundary. The code now tells the subsystem exactly when the controller is no longer available, which is the safest way to prevent stale callbacks and invalid resource use.
Why the patch is likely backport-friendly
The change appears narrow enough to backport cleanly into stable and vendor kernels. It does not redesign the SPI core or DMA framework, and it does not alter the controller’s functional behavior during normal operation. That kind of small, targeted lifetime fix is usually preferred for long-term support branches because it reduces regression risk.At the same time, the bug is serious enough that downstream maintainers will likely want the patch even on otherwise conservative kernel lines. Teardown-order crashes tend to be hard to reproduce in test labs but easy to hit in real workloads where device removal, hotplug, or service restarts happen under load.
Practical Impact
For consumer desktops, the direct impact is probably limited, because most users do not interact with an NXP low-power SPI controller in a way that exposesspidev and active transfer teardown. But for embedded Linux, industrial automation, edge appliances, and custom hardware, this is a much more relevant class of bug. Those systems often depend on SPI peripherals continuously and may reboot or restart services under operational stress.The more important point is that a bug like this can show up as a hard crash, not just a transient error. When teardown races hit a kernel driver, the symptoms often look like device flakiness until a NULL dereference or panic makes the real cause obvious. That makes it especially dangerous in products that are expected to run unattended.
Enterprises should also think in terms of hardware inventory, not just distribution version numbers. A system might run a patched kernel branch but still carry vendor backports or board support package code with subtle differences. The question is not only “is the kernel updated?” but also “does this specific board or SoC driver include the teardown fix?”
Where the exposure is highest
- Embedded Linux devices using NXP/Freescale LPSPI hardware
- Industrial controllers with long-lived SPI peripherals
- Appliances that expose SPI through user-space interfaces
- Boards with DMA-backed SPI transfers
- Systems that may stop and restart SPI consumers under load
- Vendor kernels where backport status is uncertain
- Automation platforms where reliability failures become service incidents
Why This Becomes a Security Issue
At first glance, this may look like a stability bug rather than a security flaw. But kernel crashes are security-relevant whenever they can be triggered reliably enough to deny service, especially in privileged code paths. A local user with access tospidev or an application stack that invokes SPI transfers can potentially trigger the fault during a race window .That matters because availability is a legitimate security property. If a bug can take down a device in a critical control path, it affects safety, uptime, and service continuity. For embedded and industrial systems, those outcomes can be more serious than a conventional desktop crash because recovery may require physical access or a full power cycle.
There is also a broader kernel-security principle at play here: lifetime errors are often the first step in more serious memory-safety problems. Not every use-after-free becomes a weaponized exploit, but every use-after-free deserves scrutiny because it means code is still touching memory after the system has decided that memory is no longer valid.
What makes the bug hard to dismiss
The crash trace is not speculative, and the fix is not cosmetic. The advisory describes a reproducible failure mode involving a running SPI transfer during teardown, which is enough to justify treating the issue as real operational risk . Even if exploitation is unlikely, denial-of-service potential alone makes the bug worth patching promptly.Enterprise and Vendor Implications
This CVE also highlights how modern Linux security is shaped by the vendor backport pipeline. Most enterprise users will never manually patch the mainline kernel; they rely on distribution kernels, board support packages, or device vendor updates. That means the effective security posture depends on how quickly and accurately vendors carry the fix.For hardware vendors, the competitive implication is straightforward. Customers notice who ships stable backports fast, who documents them clearly, and who avoids introducing regressions in embedded firmware updates. In an environment where devices are often deployed for years, remediation quality becomes part of product quality.
For enterprises running mixed fleets, the lesson is to track hardware-specific CVEs alongside general OS advisories. A broad patch cycle may not catch a driver like this if the affected controller only exists on a subset of systems. That can leave a blind spot where the OS appears current but a board-specific kernel path remains vulnerable.
The operational downside of delay
- A crash in an SPI controller can look like a hardware fault
- Support teams may chase the wrong root cause for days
- Vendor kernels may lag upstream fixes
- Backports can vary in implementation quality
- Embedded devices are often patched less frequently than servers
- Reboots may be the only practical recovery method
- Small driver bugs can become expensive field incidents
How Administrators Should Think About It
The immediate response should be inventory, not panic. Identify whether your hardware uses thespi-fsl-lpspi controller and whether your kernel tree includes the explicit unregister fix. If you manage custom board images, verify the driver source or vendor patch set rather than assuming a version string tells the whole story.If your environment exposes SPI to user-space through
spidev, pay even closer attention. The advisory’s call trace shows the issue can be reached through a normal spi_sync() path initiated from user space, which means local workloads may be enough to trigger it during a teardown race .Testing should focus on stop-start cycles, device removal, service restarts, and any automation that might interrupt SPI activity. In other words, try to recreate the conditions under which teardown can overlap with active transfers. That is where this class of bug lives.
A practical checklist
- Confirm whether your hardware uses NXP/Freescale LPSPI.
- Check whether your kernel has the spi_register_controller / spi_unregister_controller change.
- Review vendor backports for board support package kernels.
- Audit any systems exposing SPI through spidev.
- Test device removal or service restart scenarios under load.
- Watch for DMA RX errors or NULL pointer crashes in kernel logs.
- Prioritize embedded and appliance fleets over general-purpose desktops.
Why the Fix Is a Good Kernel Change
One reason this CVE is reassuring, despite the bug, is that the fix is conceptually tidy. It does not force the SPI subsystem to learn about every possible driver teardown hazard. Instead, it restores control to the driver that owns the hardware lifetime. That is the kind of surgical change kernel maintainers usually prefer.It also preserves the existing architecture. There is no hint in the advisory that the driver needed a redesign of its DMA engine, message pump, or SPI transfer semantics. The issue was one of ordering and ownership, not a broken controller model. That makes the correction easier to reason about and easier to backport.
In a broader sense, this is exactly how mature kernel maintenance should work: identify the lifetime bug, fix the teardown sequence, and keep the behavioral surface area small. That reduces the chance that a security patch itself becomes a new source of regressions.
What this says about kernel hygiene
- Explicit lifetime management beats implied cleanup
- Teardown must be serialized with in-flight work
- Managed-resource helpers are convenient but not always sufficient
- DMA-backed drivers need especially careful shutdown logic
- Small patches are often the safest patches
- Driver ownership boundaries matter for security as well as stability
Strengths and Opportunities
The strength of this fix is that it is precise. It addresses the root cause by correcting the controller lifecycle, and it does so without broad collateral changes. That makes the CVE easier to understand, easier to backport, and easier for operators to validate in vendor builds.It also creates an opportunity for hardware vendors and distribution maintainers to demonstrate patch discipline in a part of the stack that is often under-tested compared with server networking or desktop graphics. Good embedded patch hygiene is a real differentiator, especially for customers who care about uptime and predictability.
- The fix is narrow and surgical
- The root cause is clearly identified
- The remedy should be backport-friendly
- It improves driver ownership clarity
- It reduces the chance of late DMA callbacks
- It reinforces better teardown sequencing
- It gives administrators a concrete verification target
- It supports more reliable embedded and appliance uptime
Risks and Concerns
The main concern is underestimation. A lot of teams hear “SPI driver” and assume the issue is limited to niche hardware. In reality, embedded and industrial fleets can be large, critical, and long-lived, which makes even a narrow driver bug operationally important.A second concern is patch visibility. Vendor kernels may contain the fix in some branches but not others, and board support packages can lag mainline by a wide margin. If administrators rely only on generic version checks, they may miss the vulnerable path entirely.
A third concern is that teardown races are hard to reproduce. That means the bug may survive through casual QA, only to surface in the field during rare but perfectly ordinary operations like device reset, service restart, or hardware replacement.
- The bug may be easy to overlook
- Vendor backports may be inconsistent
- Embedded fleets are often slow to update
- Reproduction can be timing-sensitive
- Crashes may be misattributed to hardware instability
- User-space SPI access can expand the attack surface
- Recovery on deployed devices may be costly or disruptive
Looking Ahead
What matters next is not whether the fix exists upstream — it does — but how quickly it reaches the kernels actually shipping in devices. For Linux operators, especially in embedded environments, the right question is whether the affected board support package or vendor kernel already contains the change, not whether a generic upstream release note mentions it .The other thing to watch is whether the disclosure prompts closer attention to teardown ordering in other SPI drivers. Kernel bugs often cluster around similar patterns, and any place that combines managed registration, DMA teardown, and asynchronous transfers deserves extra review. This is especially true in subsystems where hardware callbacks can still be live while device removal is underway.
- Vendor advisories mapping the fix to shipped kernel builds
- Backports into long-term support branches
- Board-specific firmware updates for embedded systems
- Any follow-up SPI lifetime or DMA teardown fixes
- Crash reports involving
spidevorfsl_lpspi_dma_transfer() - Evidence of similar teardown-order issues in neighboring drivers
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center