CVE-2026-31661 is a reminder that kernel security is often decided by small accounting details, not cinematic remote exploits. The newly cataloged Linux kernel flaw affects the brcmsmac Broadcom Wi-Fi driver and centers on a mismatch between the size used for coherent DMA allocation and the size later passed back during cleanup. With a CVSS 3.1 score of 5.5 Medium, this is not a mass-internet emergency, but it is a meaningful availability risk for systems that actually load the affected driver. For WindowsForum readers, the important takeaway is simple: this is primarily a Linux kernel and Linux distribution patching issue, not a Windows Wi-Fi stack vulnerability, but it still matters in mixed Windows, Linux, cloud, lab, and dual-boot environments.
The Linux kernel’s security process has changed dramatically in recent years, and CVE-2026-31661 fits that newer pattern. Instead of waiting for only high-profile vulnerabilities to receive identifiers, the kernel community now routinely assigns CVEs to fixes that correct memory safety, lifetime, locking, reference-counting, and device-driver behavior. That approach produces more CVE noise, but it also gives administrators a more complete view of defects that may matter in specific hardware or deployment contexts.
This vulnerability was published in late April 2026 and attributed to kernel.org as the source. The description is brief because the underlying fix is brief:
The affected component, brcmsmac, is an open-source Broadcom wireless driver used for certain older Broadcom IEEE 802.11n SoftMAC devices. It is distinct from brcmfmac, b43, and Broadcom’s proprietary
The scoring also tells an important story. NVD lists the issue as local attack vector, low attack complexity, low privileges required, no user interaction, and high availability impact, with no direct confidentiality or integrity impact currently assigned. That means defenders should treat it as a denial-of-service or crash-class kernel issue rather than a credential-theft or remote-takeover bug.
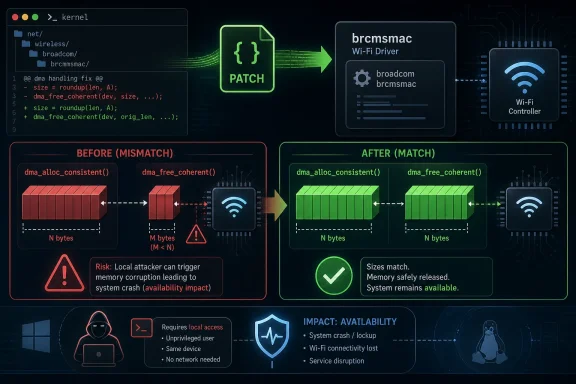
The Linux DMA API expects drivers to pair allocation and free operations precisely. If a driver asks for coherent memory and the allocator rounds, aligns, or otherwise adjusts the actual allocation, the driver must free the allocation using the corresponding size. Passing a different size back can confuse the allocator’s internal accounting, which is exactly the class of defect this patch addresses.
This is the kind of vulnerability that looks almost trivial in a patch diff but carries real operational significance. Kernel allocators are highly optimized and architecture-dependent, so a size mismatch that appears harmless on one platform may behave differently on another. That variability is why conservative kernel maintainers often treat these bugs as security-relevant even when public exploit details are sparse.
Key concepts behind the flaw include:
The most significant part is A:H, indicating a high impact on availability. That usually maps to a kernel crash, device hang, or denial-of-service scenario rather than data disclosure. The C:N and I:N fields indicate that, based on current public assessment, confidentiality and integrity impacts have not been established.
This rating makes the bug more relevant to shared systems, laptops used by multiple local accounts, kiosks, lab machines, and older Linux devices than to ordinary Windows desktops. A single-user Linux laptop with full-disk encryption and no untrusted local accounts faces a different risk profile than a university lab machine with many shell users. Context matters more here than the CVE number alone.
Administrators should interpret the rating this way:
Linux users often treat “Broadcom Wi-Fi” as one category, but that is misleading. Broadcom support on Linux has long been split among open drivers, firmware-dependent drivers, older SoftMAC stacks, and proprietary packages. A system using
The practical test is not the marketing name of the wireless card but the loaded kernel module. If
Useful checks for Linux users include:
CPEs are useful for vulnerability scanners, but Linux kernel packaging complicates them. Distributions backport individual fixes without changing the upstream version number in a way that casual users expect. A Red Hat, Debian, Ubuntu, SUSE, Fedora, Arch, or enterprise appliance kernel may include the patch while still reporting a base version that appears vulnerable in a generic upstream range.
That is why the “are we missing a CPE” prompt commonly seen in vulnerability databases should not be read as a definitive asset inventory. It is a signal that automated product mapping remains imperfect. For kernel CVEs, the distribution’s own advisory and package changelog are often more authoritative than a scanner’s raw upstream version comparison.
A careful reading of affected status should separate:
For a standard Windows 10 or Windows 11 PC using Microsoft’s native Wi-Fi drivers, CVE-2026-31661 is not the relevant patch item. Windows does not load Linux’s
The nuance comes with WSL, Hyper-V, Azure, and mixed-platform environments. WSL2 uses a Linux kernel, but normal WSL2 instances do not directly control the host’s PCIe Wi-Fi adapter through
For WindowsForum readers, the practical distinction is:
Administrators should resist the temptation to manually cherry-pick kernel patches unless they already maintain custom kernels. For most environments, the right answer is to wait for the distribution’s security update, test it, and deploy it through the existing kernel lifecycle. Kernel hotpatching may help in some enterprise distributions, but driver changes can still require careful validation.
A practical remediation sequence looks like this:
For CVE-2026-31661, a high-quality triage process should combine version checks with driver presence. A server with no Wi-Fi hardware, no
Security teams should create a small decision tree rather than relying on one scanner column. The outcome should classify assets as confirmed affected, potentially affected, not affected by configuration, or already remediated by vendor backport. That classification improves patch prioritization and reduces alert fatigue.
Recommended triage signals include:
The highest-priority assets are likely to be Linux laptops, field devices, lab systems, industrial PCs, classroom machines, and specialized appliances. These systems may have older Broadcom Wi-Fi chipsets and local user access patterns that make denial-of-service more relevant. A student lab machine or shared engineering workstation is a better fit for the CVSS assumptions than a locked-down headless server.
Enterprises also need to think about fleet visibility. Endpoint management systems that track Windows hardware may miss dual-boot Linux partitions or unmanaged Linux installations on the same physical laptops. That is especially common in developer organizations where users install Linux for testing, firmware work, or container development.
Enterprise teams should prioritize:
The visible symptom of a vulnerability like this may not be obvious. Users should not expect a warning dialog, browser alert, or Wi-Fi icon change. A vulnerable system may behave normally until a crafted local workload, unusual driver path, or error condition stresses the allocation and free logic.
If your distribution offers a kernel update, install it. If you are using a custom kernel, pull the stable branch containing the fix or apply the backport corresponding to your branch. If your hardware does not need
Consumer checklist:
The better approach is contextual vulnerability management. A Wi-Fi driver bug should be mapped against Wi-Fi hardware, loaded modules, and local user risk. A filesystem bug should be mapped against mounted filesystem types. A network stack bug should be mapped against reachable services and packet paths.
This CVE also illustrates the long tail of hardware support. Older wireless drivers remain in the kernel because users still depend on them, but their maintenance burden does not disappear. Every supported driver carries allocator rules, firmware interactions, suspend/resume paths, and architecture-specific behavior that must remain correct over time.
The broader lessons are clear:
That cross-platform visibility is a competitive advantage when it gives defenders a unified view. It becomes a liability when advisories are misunderstood as applying to the wrong platform. Microsoft, Canonical, Red Hat, SUSE, Debian, and security scanner vendors all face the same challenge: presenting Linux kernel CVEs in a way that distinguishes theoretical package exposure from actual runtime exposure.
For Broadcom and other hardware vendors, the case reinforces the importance of upstream driver quality. Wi-Fi support remains a reputational issue in the Linux community, especially for older Broadcom devices that have historically required careful driver and firmware selection. Even when the fix is in open-source kernel code, users often associate the experience with the hardware brand.
The competitive implications include:
Security teams should also monitor whether exploitability research changes the impact assessment. At present, the public scoring frames the issue as a local availability problem. If researchers demonstrate a stronger primitive, such as reliable memory corruption with broader consequences, prioritization may need to change.
Items to watch include:
CVE-2026-31661 is a small bug with a large teaching surface. It reminds us that kernel reliability depends on exact API contracts, that old Wi-Fi hardware remains part of the security landscape, and that modern vulnerability feeds require interpretation rather than reflex. The right response is measured: identify systems using brcmsmac, apply the fixed kernel from a trusted vendor, reboot, verify, and then use the incident to improve how your organization handles hardware-specific Linux kernel CVEs in an increasingly mixed-platform world.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux kernel’s security process has changed dramatically in recent years, and CVE-2026-31661 fits that newer pattern. Instead of waiting for only high-profile vulnerabilities to receive identifiers, the kernel community now routinely assigns CVEs to fixes that correct memory safety, lifetime, locking, reference-counting, and device-driver behavior. That approach produces more CVE noise, but it also gives administrators a more complete view of defects that may matter in specific hardware or deployment contexts.This vulnerability was published in late April 2026 and attributed to kernel.org as the source. The description is brief because the underlying fix is brief:
dma_alloc_consistent() may adjust an allocation size for alignment, store that adjusted size in an alloced field, and therefore the free path must pass the same adjusted size back to dma_free_coherent(). In plain English, the driver was not consistently remembering how much coherent DMA memory it really received.The affected component, brcmsmac, is an open-source Broadcom wireless driver used for certain older Broadcom IEEE 802.11n SoftMAC devices. It is distinct from brcmfmac, b43, and Broadcom’s proprietary
wl driver, which is where many Linux users get confused when reading advisories. A system with a Broadcom Wi-Fi card is not automatically affected; the relevant question is whether the running kernel includes and loads the vulnerable brcmsmac code path.The scoring also tells an important story. NVD lists the issue as local attack vector, low attack complexity, low privileges required, no user interaction, and high availability impact, with no direct confidentiality or integrity impact currently assigned. That means defenders should treat it as a denial-of-service or crash-class kernel issue rather than a credential-theft or remote-takeover bug.
The Technical Core: A DMA Size Mismatch
Why coherent DMA accounting matters
At the heart of CVE-2026-31661 is Direct Memory Access, the mechanism that lets hardware devices read from or write to system memory without the CPU copying every byte. Wi-Fi drivers use DMA for performance-sensitive tasks such as transmit and receive buffers, descriptor rings, and hardware queues. When DMA bookkeeping goes wrong, the consequences can be more severe than an ordinary userspace memory leak because the kernel and hardware are sharing a view of memory.The Linux DMA API expects drivers to pair allocation and free operations precisely. If a driver asks for coherent memory and the allocator rounds, aligns, or otherwise adjusts the actual allocation, the driver must free the allocation using the corresponding size. Passing a different size back can confuse the allocator’s internal accounting, which is exactly the class of defect this patch addresses.
This is the kind of vulnerability that looks almost trivial in a patch diff but carries real operational significance. Kernel allocators are highly optimized and architecture-dependent, so a size mismatch that appears harmless on one platform may behave differently on another. That variability is why conservative kernel maintainers often treat these bugs as security-relevant even when public exploit details are sparse.
Key concepts behind the flaw include:
- Coherent DMA memory shared between a device and the CPU
- Allocation alignment that may increase the effective allocation size
- Driver-owned bookkeeping that records the adjusted size
- Free-path correctness when returning memory to the kernel
- Availability risk if allocator metadata or memory lifetime assumptions are violated
Why the Severity Is Medium, Not Critical
Reading the CVSS vector correctly
The published CVSS vector for CVE-2026-31661 is important because it prevents overreaction. The AV:L portion means an attacker needs local access, not merely network reachability. The PR:L portion means the attacker is assumed to have some low-privileged capability on the system, while UI:N means no victim click or desktop interaction is required once the attacker has that foothold.The most significant part is A:H, indicating a high impact on availability. That usually maps to a kernel crash, device hang, or denial-of-service scenario rather than data disclosure. The C:N and I:N fields indicate that, based on current public assessment, confidentiality and integrity impacts have not been established.
This rating makes the bug more relevant to shared systems, laptops used by multiple local accounts, kiosks, lab machines, and older Linux devices than to ordinary Windows desktops. A single-user Linux laptop with full-disk encryption and no untrusted local accounts faces a different risk profile than a university lab machine with many shell users. Context matters more here than the CVE number alone.
Administrators should interpret the rating this way:
- Not remotely exploitable under the published CVSS assessment
- No confirmed data theft impact in the public scoring
- Potentially serious local denial-of-service if the vulnerable path is reachable
- Hardware and driver dependent, not universal across Linux systems
- Worth patching through normal kernel update channels
The brcmsmac Driver and Its Hardware Footprint
Not every Broadcom Wi-Fi device is affected
The brcmsmac driver supports a specific slice of Broadcom wireless history, especially certain PCIe and AXI SoftMAC devices. Commonly referenced chips include families such as BCM4313, BCM43224, and BCM43225, along with some related SoC/AXI configurations. That is a narrow but still relevant footprint, especially among older laptops, small-form-factor systems, embedded boards, and repurposed hardware.Linux users often treat “Broadcom Wi-Fi” as one category, but that is misleading. Broadcom support on Linux has long been split among open drivers, firmware-dependent drivers, older SoftMAC stacks, and proprietary packages. A system using
brcmfmac or wl is not the same as one using brcmsmac, even if both are connected to Broadcom-branded hardware.The practical test is not the marketing name of the wireless card but the loaded kernel module. If
lsmod shows brcmsmac, or if lspci -k associates the wireless controller with brcmsmac, then this advisory becomes materially relevant. If another driver is in use, the specific CVE may not apply, though the system may still need other kernel updates.Useful checks for Linux users include:
lsmodto see whether brcmsmac is loadedlspci -nnkto map the Wi-Fi controller to its kernel drivermodinfo brcmsmacto inspect the installed module- Distribution security trackers for package-specific status
- Kernel package changelogs for the stable backport
Affected Kernel Ranges and the CPE Problem
Why version lists look broader than reality
NVD’s CPE data for this CVE lists broad Linux kernel ranges, including multiple long-term and stable branches. The published affected ranges indicate fixes landing before versions such as 5.10.253, 5.15.203, 6.1.169, 6.6.135, 6.12.82, 6.18.23, and 6.19.13, along with release-candidate references in the 7.0 line. That does not mean every machine running an earlier kernel is equally exposed.CPEs are useful for vulnerability scanners, but Linux kernel packaging complicates them. Distributions backport individual fixes without changing the upstream version number in a way that casual users expect. A Red Hat, Debian, Ubuntu, SUSE, Fedora, Arch, or enterprise appliance kernel may include the patch while still reporting a base version that appears vulnerable in a generic upstream range.
That is why the “are we missing a CPE” prompt commonly seen in vulnerability databases should not be read as a definitive asset inventory. It is a signal that automated product mapping remains imperfect. For kernel CVEs, the distribution’s own advisory and package changelog are often more authoritative than a scanner’s raw upstream version comparison.
A careful reading of affected status should separate:
- Upstream kernel version ranges
- Distribution-specific backports
- Whether CONFIG_BRCMSMAC is enabled
- Whether brcmsmac.ko is installed
- Whether the driver is actually loaded
- Whether compatible Broadcom hardware exists
The Windows Angle: Why This Appears in Microsoft Contexts
MSRC visibility does not equal Windows kernel exposure
The presence of CVE-2026-31661 in a Microsoft security context can easily confuse Windows users. Microsoft’s ecosystem now spans Windows, Azure, Linux-based services, container hosts, developer tooling, and security products that track non-Windows CVEs. Seeing a Linux kernel CVE near Microsoft guidance does not mean the Windows Wi-Fi stack has inherited the vulnerability.For a standard Windows 10 or Windows 11 PC using Microsoft’s native Wi-Fi drivers, CVE-2026-31661 is not the relevant patch item. Windows does not load Linux’s
brcmsmac kernel module to operate Wi-Fi. The vulnerable code lives in the Linux kernel driver tree, not in the Windows networking stack.The nuance comes with WSL, Hyper-V, Azure, and mixed-platform environments. WSL2 uses a Linux kernel, but normal WSL2 instances do not directly control the host’s PCIe Wi-Fi adapter through
brcmsmac. Azure and enterprise Linux workloads may be different, especially where Linux kernels are deployed on physical machines, edge appliances, lab hardware, or custom images.For WindowsForum readers, the practical distinction is:
- Windows desktop Wi-Fi users should not panic over this CVE
- Dual-boot Linux users should patch their Linux installation
- WSL users should keep WSL updated, but typical WSL networking is not the same exposure
- Azure Linux administrators should follow their distribution or image vendor guidance
- Security teams should avoid treating the CVE as a Windows driver issue
Patch Management and Remediation Strategy
Update the kernel, not just the firmware
The remediation path for CVE-2026-31661 is a kernel update containing thebrcmsmac fix. Updating Wi-Fi firmware files alone will not address the driver’s DMA free-size logic. The affected code is in the kernel module, so the fix must come through the kernel package, a stable kernel update, or a vendor-provided backport.Administrators should resist the temptation to manually cherry-pick kernel patches unless they already maintain custom kernels. For most environments, the right answer is to wait for the distribution’s security update, test it, and deploy it through the existing kernel lifecycle. Kernel hotpatching may help in some enterprise distributions, but driver changes can still require careful validation.
A practical remediation sequence looks like this:
- Identify affected assets by checking whether
brcmsmacis present and loaded. - Confirm vendor status through the Linux distribution’s security tracker or advisory feed.
- Stage the updated kernel in a representative test system with similar Wi-Fi hardware.
- Reboot into the patched kernel and verify that the system is not still running the old kernel.
- Retest wireless connectivity under suspend, resume, roaming, and throughput conditions.
- Document exceptions for systems that cannot be patched immediately.
- Remove or blacklist unused drivers where
brcmsmacis unnecessary.
Detection, Triage, and Scanner Noise
Avoid false positives from version-only scanning
Kernel CVEs are notoriously noisy in vulnerability management platforms because scanners often compare upstream version strings against NVD CPE ranges. That method can flag a distribution kernel as vulnerable even when the vendor has already backported the fix. Conversely, a custom kernel may appear safe by version naming but lack the relevant patch.For CVE-2026-31661, a high-quality triage process should combine version checks with driver presence. A server with no Wi-Fi hardware, no
brcmsmac module, and no realistic path to load it is not the same risk as an older laptop actively using the driver. The CVSS score assumes a reachable vulnerable component, not merely a source file somewhere in a package repository.Security teams should create a small decision tree rather than relying on one scanner column. The outcome should classify assets as confirmed affected, potentially affected, not affected by configuration, or already remediated by vendor backport. That classification improves patch prioritization and reduces alert fatigue.
Recommended triage signals include:
- Running kernel version and vendor package release
- Loaded module list showing whether
brcmsmacis active - Kernel configuration indicating whether CONFIG_BRCMSMAC is built
- Hardware inventory for Broadcom PCIe/AXI Wi-Fi devices
- Vendor advisory status for the exact distribution build
- Reboot status after installing the fixed kernel
Enterprise Impact: Mostly Edge Cases, But Real Ones
Where the vulnerability matters most
In large enterprises, CVE-2026-31661 is unlikely to top the risk register unless the organization operates Linux endpoints with affected Broadcom hardware. Most data-center servers do not use consumer Broadcom Wi-Fi adapters, and cloud virtual machines generally do not expose that class of physical wireless device. That said, enterprises are full of exceptions.The highest-priority assets are likely to be Linux laptops, field devices, lab systems, industrial PCs, classroom machines, and specialized appliances. These systems may have older Broadcom Wi-Fi chipsets and local user access patterns that make denial-of-service more relevant. A student lab machine or shared engineering workstation is a better fit for the CVSS assumptions than a locked-down headless server.
Enterprises also need to think about fleet visibility. Endpoint management systems that track Windows hardware may miss dual-boot Linux partitions or unmanaged Linux installations on the same physical laptops. That is especially common in developer organizations where users install Linux for testing, firmware work, or container development.
Enterprise teams should prioritize:
- Shared Linux workstations with local user accounts
- Developer laptops running Linux on bare metal
- Lab and test benches with older Broadcom wireless hardware
- Embedded Linux devices that include Wi-Fi and allow shell access
- Education environments where many users share physical machines
- Unmanaged dual-boot systems outside normal patch reporting
Consumer and Enthusiast Impact
What Linux desktop users should actually do
For enthusiasts, the advice is less dramatic but still important. If you run Linux on an older laptop with Broadcom Wi-Fi, especially a machine revived from the Windows 7 or Windows 8 era, check which driver is in use. Many of these systems still appear in home labs, retro computing setups, network experiments, and lightweight Linux installations.The visible symptom of a vulnerability like this may not be obvious. Users should not expect a warning dialog, browser alert, or Wi-Fi icon change. A vulnerable system may behave normally until a crafted local workload, unusual driver path, or error condition stresses the allocation and free logic.
If your distribution offers a kernel update, install it. If you are using a custom kernel, pull the stable branch containing the fix or apply the backport corresponding to your branch. If your hardware does not need
brcmsmac, blacklisting the module can reduce attack surface, but it should not be used as a substitute for routine kernel patching.Consumer checklist:
- Run system updates and reboot afterward
- Check the active driver before assuming exposure
- Avoid random out-of-tree Wi-Fi driver packages from unknown sources
- Keep a fallback kernel in the boot menu in case Wi-Fi regression occurs
- Prefer vendor distribution kernels unless you have a reason to build your own
- Document any module blacklist so future troubleshooting is easier
Ecosystem Lessons: Small Driver Bugs, Big Maintenance Burden
The kernel CVE flood is a feature and a burden
CVE-2026-31661 shows why Linux kernel vulnerability management has become more demanding. A one-line or small driver fix can generate a CVE, appear in NVD, propagate to Microsoft-linked visibility, trigger vendor trackers, and light up enterprise scanners. That transparency is valuable, but it can overwhelm teams that treat every kernel CVE as equivalent.The better approach is contextual vulnerability management. A Wi-Fi driver bug should be mapped against Wi-Fi hardware, loaded modules, and local user risk. A filesystem bug should be mapped against mounted filesystem types. A network stack bug should be mapped against reachable services and packet paths.
This CVE also illustrates the long tail of hardware support. Older wireless drivers remain in the kernel because users still depend on them, but their maintenance burden does not disappear. Every supported driver carries allocator rules, firmware interactions, suspend/resume paths, and architecture-specific behavior that must remain correct over time.
The broader lessons are clear:
- Driver code is kernel attack surface
- Hardware-specific bugs still matter
- Automated CVE ingestion needs asset context
- Backports complicate simple version comparisons
- Local denial-of-service can be business-impacting
- Old laptops and lab systems deserve patch governance
Competitive and Market Implications
Security visibility is now cross-platform
For Microsoft, Linux, and enterprise security vendors, CVE-2026-31661 reflects a larger market reality: customers no longer manage operating systems in clean silos. A Windows-centric organization may still run Linux containers, Azure Linux images, WSL development environments, network appliances, and dual-boot engineering laptops. Security portals increasingly surface vulnerabilities from all of those layers.That cross-platform visibility is a competitive advantage when it gives defenders a unified view. It becomes a liability when advisories are misunderstood as applying to the wrong platform. Microsoft, Canonical, Red Hat, SUSE, Debian, and security scanner vendors all face the same challenge: presenting Linux kernel CVEs in a way that distinguishes theoretical package exposure from actual runtime exposure.
For Broadcom and other hardware vendors, the case reinforces the importance of upstream driver quality. Wi-Fi support remains a reputational issue in the Linux community, especially for older Broadcom devices that have historically required careful driver and firmware selection. Even when the fix is in open-source kernel code, users often associate the experience with the hardware brand.
The competitive implications include:
- Security portals must explain platform boundaries clearly
- Linux distributions gain trust through timely backports
- Hardware vendors benefit from well-maintained upstream drivers
- Scanner vendors need better module-aware detection
- Enterprise endpoint tools must understand dual-boot and Linux fleets
- Cloud providers must distinguish guest-kernel risk from host risk
Strengths and Opportunities
CVE-2026-31661 is not a headline-grabbing remote code execution flaw, but the response around it shows several strengths in the modern vulnerability ecosystem. The issue was publicly cataloged, mapped to upstream stable patches, scored with a clear availability-focused CVSS vector, and picked up by major distribution and security tracking systems. That gives defenders enough information to act without relying on rumor or exploit speculation.- Fast public visibility through coordinated CVE publication
- Clear technical root cause involving mismatched DMA allocation and free sizing
- Stable-branch patch availability across multiple kernel lines
- Manageable severity because the attack vector is local rather than remote
- Good opportunity to improve scanner logic for kernel modules and hardware presence
- Useful reminder to patch older Linux endpoints that may otherwise be ignored
- Stronger cross-platform awareness for Windows-heavy organizations that also run Linux
Risks and Concerns
The main risk is not that CVE-2026-31661 will suddenly become the next internet-scale worm. The concern is that organizations will either overreact because they see a Linux kernel CVE in a Microsoft-facing context, or underreact because the bug seems too small to matter. Both mistakes are common in modern vulnerability management.- Version-only scanners may generate false positives against backported vendor kernels
- Unmanaged Linux laptops may remain exposed after corporate Windows patching succeeds
- Shared systems could face local denial-of-service from low-privileged users
- Custom kernels may miss the fix if maintainers do not track stable branches
- Driver blacklisting can break Wi-Fi if administrators apply it without hardware checks
- CPE data may be too broad for precise operational decisions
- Old Broadcom hardware may receive less testing than mainstream modern Wi-Fi chipsets
Looking Ahead
What defenders should monitor next
The next phase is distribution follow-through. Administrators should watch for fixed kernel packages, updated security tracker statuses, and any vendor-specific notes about whether a shipped configuration enablesbrcmsmac. The most important operational milestone is not the publication date of the CVE but the date your fleet actually reboots into a corrected kernel.Security teams should also monitor whether exploitability research changes the impact assessment. At present, the public scoring frames the issue as a local availability problem. If researchers demonstrate a stronger primitive, such as reliable memory corruption with broader consequences, prioritization may need to change.
Items to watch include:
- Distribution advisories for Debian, Ubuntu, Red Hat, SUSE, Fedora, Arch, and derivatives
- Kernel package changelogs confirming the brcmsmac DMA free-size fix
- Scanner plugin updates that account for backports and loaded modules
- Reports of Wi-Fi regressions after applying fixed kernels
- Any revised CVSS or CWE assignment from vulnerability databases
CVE-2026-31661 is a small bug with a large teaching surface. It reminds us that kernel reliability depends on exact API contracts, that old Wi-Fi hardware remains part of the security landscape, and that modern vulnerability feeds require interpretation rather than reflex. The right response is measured: identify systems using brcmsmac, apply the fixed kernel from a trusted vendor, reboot, verify, and then use the incident to improve how your organization handles hardware-specific Linux kernel CVEs in an increasingly mixed-platform world.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center