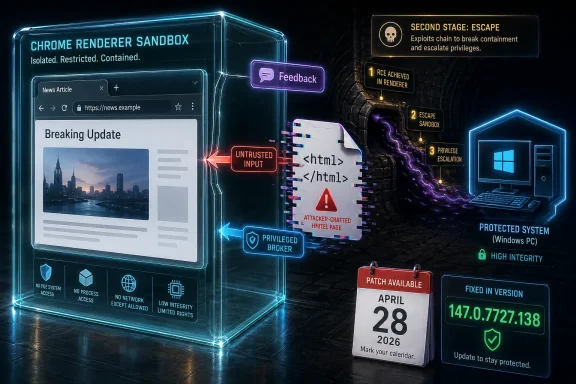
Google disclosed CVE-2026-7345 on April 28, 2026, as a high-severity Chrome vulnerability in the browser’s Feedback component, fixed in Chrome 147.0.7727.138 after allowing a renderer-compromising attacker to potentially escape the sandbox through a crafted HTML page. That sounds narrow, almost bureaucratic, until you unpack the phrase “renderer-compromising attacker.” This is not a bug that starts at the front door; it is a bug that matters because attackers increasingly arrive through a chain, and Chrome’s sandbox is supposed to be the wall that keeps the first compromise from becoming the whole machine. CVE-2026-7345 is therefore less a curiosity in Feedback code than a reminder that browser security now lives in the seams between features most users never think about.
The most interesting thing about CVE-2026-7345 is not that it lives in something called Feedback. It is that a peripheral-sounding feature can still sit close enough to privileged browser plumbing to matter in a sandbox escape scenario. Modern browsers are not single applications in the old desktop sense; they are constellations of processes, brokers, renderers, GPU paths, media stacks, native UI surfaces, permissions gates, and update machinery.
Chrome’s renderer process is intentionally treated as hostile territory. It parses the web, executes JavaScript, handles layout, decodes formats, and touches an endless supply of attacker-controlled input. The browser sandbox exists because Google, Microsoft, Mozilla, and everyone else learned long ago that web-facing code will keep producing bugs no matter how many fuzzers and mitigations are thrown at it.
That is why the wording of this CVE matters. The attacker first needs to have compromised the renderer process. On paper, that raises the attack complexity; in practice, renderer bugs are exactly the kind of primitive that browser exploit chains are built around.
Feedback sounds like an afterthought because users experience it as a menu item, a screenshot tool, or a “send report” workflow. But from a security perspective, anything that moves data from an untrusted web context toward more privileged browser services deserves suspicion. CVE-2026-7345 appears to have been precisely that kind of failure: insufficient validation of untrusted input in a component that should have been stricter about what crossed the line.
CVE-2026-7345 sits in the second act of an attack. The first act is compromise of the renderer. The second act is getting out.
That distinction is crucial for Windows admins because it changes how risk should be understood. A vulnerability requiring a renderer compromise is not “safe” simply because it is not a one-click, unauthenticated, universal code execution bug. It is an escalation component, and escalation components are valuable because exploit developers combine them with other bugs.
The CVSS vector assigned by CISA’s ADP program reflects this shape: network attack vector, no privileges required, user interaction required, high attack complexity, changed scope, and high confidentiality, integrity, and availability impact. In plain English, the victim likely has to load hostile web content, the attacker needs a working chain, and the payoff can be severe if the chain succeeds.
That is the browser security bargain in 2026. A single CVE rarely tells the whole story, but a sandbox escape CVE tells you where an attacker hopes the story ends.
That matters because enterprise risk is rarely about a single shiny CVE. It is about the density of attack surface fixed in a short window. When a Chrome release contains several critical and high-severity memory-safety or validation bugs, the operational response should not be a debate over which one is most elegant; it should be a race to prove that managed endpoints actually moved.
The public vulnerability record for CVE-2026-7345 also shows the usual lag and churn in vulnerability metadata. NVD had not yet supplied its own CVSS score at the time reflected in the record, while CISA-ADP had updated its CVSS 3.1 assessment from an earlier, lower-complexity vector to the more nuanced 8.3 high score. That is not a scandal. It is a normal feature of vulnerability triage: initial metadata is often provisional, and defenders who treat first publication as final truth are setting themselves up for confusion.
The key fixed version for Chrome on desktop is the cleaner signal. If you are below 147.0.7727.138 on Windows or Mac, you are in the affected range described for this CVE. If you are managing Linux fleets, the corresponding stable build listed by Google is 147.0.7727.137.
Microsoft Edge, Google Chrome, Brave, Opera, Vivaldi, Electron-based desktop apps, embedded WebView controls, and vendor-wrapped Chromium runtimes do not all move in lockstep. Some consume Chromium patches quickly. Some lag. Some are pinned inside line-of-business products that pretend not to be browsers until a CVE like this forces the issue.
This is why the modern Windows security inventory has to include browser engines, not just browser icons. The executable named chrome.exe is only one part of the exposure. Edge has its own update mechanism and enterprise policies. WebView2 has its own runtime servicing model. Third-party applications may bundle Chromium in ways that standard browser update dashboards never see.
CVE-2026-7345 is a Chrome CVE, but the lesson is a Windows fleet lesson: the browser engine is now shared infrastructure. Treating it as a consumer app is operational malpractice.
The browser is a user-interaction machine. Its entire job is to process remote content because a human asked it to. That does not make every browser bug equally exploitable, but it does weaken the reassurance value of UI:R as a triage shortcut.
CVE-2026-7345 also carries high attack complexity, which should temper panic. A renderer compromise prerequisite is not trivial, and Google has not publicly said this specific CVE is being exploited in the wild. Public bug details may remain restricted until enough users have updated, which means defenders should not expect a full technical exploit narrative immediately.
But the absence of public exploitation is not the same as irrelevance. Browser exploit chains are assembled from parts, and sandbox escapes are among the more useful parts. A high-complexity bug can still be strategically valuable when paired with another flaw that supplies the initial renderer foothold.
Feedback workflows are especially interesting because they may handle screenshots, page metadata, logs, diagnostic state, user text, attachments, environment information, or browser-internal routing. Even if a given vulnerability does not involve all of those things, the category should make defenders attentive. Diagnostic and reporting features often exist to collect messy reality and hand it to more privileged code.
Improper input validation is one of the oldest weakness classes because it is not a single bug pattern so much as a failure of boundary discipline. A component receives data that originated somewhere untrusted and does not sufficiently constrain, canonicalize, verify, or reject it before making a security-relevant decision. In a sandboxed browser, that kind of mistake is especially costly when it appears near a privileged broker or service.
The story is not that Feedback is uniquely reckless. The story is that every convenience feature added to a browser must be designed as if hostile content will eventually try to reach it through a weird path. In 2026, that is not paranoia; it is table stakes.
That distinction should be familiar to any admin who has watched users keep 73 tabs open for three weeks. A green dashboard showing “update available” or “update installed” may not mean the active browser process has crossed the fixed-version line. The only version that matters is the one actually running after restart.
Enterprise policy can help, but only if it is used assertively. Chrome and Edge both support controls for update cadence, relaunch notification, and forced relaunch windows. Those controls exist because the browser is too important to leave entirely to user convenience.
The practical response to CVE-2026-7345 is therefore not exotic. Inventory versions. Push the update. Force relaunch where risk justifies it. Verify that endpoints report a fixed running build. Repeat the same logic for Edge and other Chromium-based software rather than assuming one browser update solves the shared-engine problem.
But CPEs are only as good as the software inventory behind them. A scanner can match Google Chrome if it knows Chrome is installed. It may not catch every embedded Chromium runtime in a packaged enterprise application. It may not understand portable browser installs, per-user installs, stale profiles, kiosk images, or nonstandard update channels.
This is where vulnerability management drifts into asset management. The CVE tells you what is affected. The fleet tells you whether you can prove it is gone.
For WindowsForum readers, the uncomfortable operational truth is that many organizations still have better visibility into monthly Windows cumulative updates than into browser runtime versions. That imbalance no longer matches the risk. Browser patching has become a first-class endpoint security function, not a side effect of desktop hygiene.
Publishing exploit-relevant details while hundreds of millions of browsers are still waiting for rollout would be a gift to attackers. The browser ecosystem lives under a disclosure rhythm that tries to balance research transparency with herd immunity. That rhythm is imperfect, but it is not arbitrary.
For defenders, the lack of technical detail should not stall action. You do not need a proof-of-concept to justify deploying a stable-channel update that fixes a high-severity sandbox escape. Waiting for the bug tracker to open before patching is like waiting for smoke in the hallway before checking whether the fire door closes.
The better posture is to treat restricted detail as a signal that the vendor believes premature disclosure could increase risk. In other words, the absence of detail is itself part of the security communication.
CVE-2026-7345 belongs to that chain-shaped world. It is not necessarily the first bug an attacker would use. It may be the one that makes the first bug worth using.
This is why patch prioritization based only on standalone exploitability can mislead. A vulnerability with high complexity and a prerequisite can still be urgent if the prerequisite is common in the attacker’s toolbox. Browser renderer bugs are not hypothetical. They are a recurring product of the web’s complexity, and attackers have every incentive to pair them with escape paths.
The other lesson is architectural. Sandboxes reduce blast radius, but they also create high-value boundaries. Every interface that allows a less-trusted process to ask a more-trusted process for help becomes a place where validation must be unforgiving. Feedback, GPU, accessibility, media, printing, file handling, permissions, and diagnostics all become potential border crossings.
Chrome stable updates land when Chrome stable updates land. Edge security releases land on Microsoft’s browser schedule, not necessarily the OS cumulative-update schedule. Zero-days and high-severity Chromium fixes have repeatedly arrived outside the comfortable monthly cadence.
CVE-2026-7345 was published at the end of April, not on a neat Microsoft calendar boundary. That is the world administrators now live in. If the browser is a major ingress path, then browser patching must be continuous enough to match browser risk.
That does not mean every Chrome update needs an emergency bridge call. It does mean organizations should have a defined browser emergency lane: a path for accelerating updates, forcing restarts, validating versions, and communicating to users without waiting for the next full endpoint patch cycle.
The same logic applies to other Chromium browsers, but the version numbers may differ because downstream vendors ship their own builds. Edge users should check Edge’s About page and rely on Microsoft’s security release channel for the corresponding Chromium uptake. Users of Brave, Vivaldi, Opera, and similar browsers should verify that their vendor has shipped a release incorporating the relevant Chromium fixes.
There is no credible mitigation that beats updating. Disabling Feedback is not a practical general answer, and speculative hardening tweaks are not substitutes for a patched browser. Site isolation, sandboxing, exploit mitigations, endpoint protection, and least privilege all help, but the vulnerable code still needs to be replaced.
The browser restart is the part users skip. It is also the part that turns an update from a downloaded promise into a running fix.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The Feedback Button Was Sitting on a Security Boundary
The Feedback Button Was Sitting on a Security Boundary
The most interesting thing about CVE-2026-7345 is not that it lives in something called Feedback. It is that a peripheral-sounding feature can still sit close enough to privileged browser plumbing to matter in a sandbox escape scenario. Modern browsers are not single applications in the old desktop sense; they are constellations of processes, brokers, renderers, GPU paths, media stacks, native UI surfaces, permissions gates, and update machinery.Chrome’s renderer process is intentionally treated as hostile territory. It parses the web, executes JavaScript, handles layout, decodes formats, and touches an endless supply of attacker-controlled input. The browser sandbox exists because Google, Microsoft, Mozilla, and everyone else learned long ago that web-facing code will keep producing bugs no matter how many fuzzers and mitigations are thrown at it.
That is why the wording of this CVE matters. The attacker first needs to have compromised the renderer process. On paper, that raises the attack complexity; in practice, renderer bugs are exactly the kind of primitive that browser exploit chains are built around.
Feedback sounds like an afterthought because users experience it as a menu item, a screenshot tool, or a “send report” workflow. But from a security perspective, anything that moves data from an untrusted web context toward more privileged browser services deserves suspicion. CVE-2026-7345 appears to have been precisely that kind of failure: insufficient validation of untrusted input in a component that should have been stricter about what crossed the line.
A Sandbox Escape Is Not Just Another Browser Crash
Most Chrome vulnerabilities never become household names because most of them do not need to. A heap buffer overflow in a codec, a use-after-free in a graphics path, or a type confusion bug in JavaScript machinery may be serious, but the browser’s defenses are layered so that one failure does not automatically equal system compromise. The sandbox is the difference between “the tab got owned” and “the endpoint may now be in play.”CVE-2026-7345 sits in the second act of an attack. The first act is compromise of the renderer. The second act is getting out.
That distinction is crucial for Windows admins because it changes how risk should be understood. A vulnerability requiring a renderer compromise is not “safe” simply because it is not a one-click, unauthenticated, universal code execution bug. It is an escalation component, and escalation components are valuable because exploit developers combine them with other bugs.
The CVSS vector assigned by CISA’s ADP program reflects this shape: network attack vector, no privileges required, user interaction required, high attack complexity, changed scope, and high confidentiality, integrity, and availability impact. In plain English, the victim likely has to load hostile web content, the attacker needs a working chain, and the payoff can be severe if the chain succeeds.
That is the browser security bargain in 2026. A single CVE rarely tells the whole story, but a sandbox escape CVE tells you where an attacker hopes the story ends.
Chrome 147’s April Patch Was a Cluster, Not a Footnote
Google’s April 28 desktop stable-channel update was not a small fix release. Chrome moved to 147.0.7727.137/138 for Windows and Mac, and 147.0.7727.137 for Linux, with 30 security fixes listed in the release. CVE-2026-7345 was one high-severity entry among a crowded field that included critical use-after-free flaws and several other high-severity issues across GPU, ANGLE, Navigation, Media, Skia, WebRTC, Cast, WebMIDI, Tint, and more.That matters because enterprise risk is rarely about a single shiny CVE. It is about the density of attack surface fixed in a short window. When a Chrome release contains several critical and high-severity memory-safety or validation bugs, the operational response should not be a debate over which one is most elegant; it should be a race to prove that managed endpoints actually moved.
The public vulnerability record for CVE-2026-7345 also shows the usual lag and churn in vulnerability metadata. NVD had not yet supplied its own CVSS score at the time reflected in the record, while CISA-ADP had updated its CVSS 3.1 assessment from an earlier, lower-complexity vector to the more nuanced 8.3 high score. That is not a scandal. It is a normal feature of vulnerability triage: initial metadata is often provisional, and defenders who treat first publication as final truth are setting themselves up for confusion.
The key fixed version for Chrome on desktop is the cleaner signal. If you are below 147.0.7727.138 on Windows or Mac, you are in the affected range described for this CVE. If you are managing Linux fleets, the corresponding stable build listed by Google is 147.0.7727.137.
The Microsoft Angle Is Bigger Than Edge
The user-facing source for this issue on many Windows desks may be Microsoft’s Security Update Guide rather than Google’s release blog. That is natural because Chromium vulnerabilities propagate through Microsoft’s vulnerability ecosystem as Edge-relevant advisories, even when the bug originates upstream in Chromium. For Windows shops, the question is not “Is this a Google problem or a Microsoft problem?” It is “Which Chromium-based browsers are present, and which update channels control them?”Microsoft Edge, Google Chrome, Brave, Opera, Vivaldi, Electron-based desktop apps, embedded WebView controls, and vendor-wrapped Chromium runtimes do not all move in lockstep. Some consume Chromium patches quickly. Some lag. Some are pinned inside line-of-business products that pretend not to be browsers until a CVE like this forces the issue.
This is why the modern Windows security inventory has to include browser engines, not just browser icons. The executable named chrome.exe is only one part of the exposure. Edge has its own update mechanism and enterprise policies. WebView2 has its own runtime servicing model. Third-party applications may bundle Chromium in ways that standard browser update dashboards never see.
CVE-2026-7345 is a Chrome CVE, but the lesson is a Windows fleet lesson: the browser engine is now shared infrastructure. Treating it as a consumer app is operational malpractice.
“User Interaction Required” Is Comfort Food for the Wrong Audience
Security teams often relax when they see user interaction in a CVSS vector. That instinct made more sense when “user interaction” meant opening an obviously suspicious attachment or clicking through a visibly hostile prompt. On the web, user interaction can mean visiting a page, following a link, loading an ad, opening a compromised legitimate site, or being routed through content that appears ordinary.The browser is a user-interaction machine. Its entire job is to process remote content because a human asked it to. That does not make every browser bug equally exploitable, but it does weaken the reassurance value of UI:R as a triage shortcut.
CVE-2026-7345 also carries high attack complexity, which should temper panic. A renderer compromise prerequisite is not trivial, and Google has not publicly said this specific CVE is being exploited in the wild. Public bug details may remain restricted until enough users have updated, which means defenders should not expect a full technical exploit narrative immediately.
But the absence of public exploitation is not the same as irrelevance. Browser exploit chains are assembled from parts, and sandbox escapes are among the more useful parts. A high-complexity bug can still be strategically valuable when paired with another flaw that supplies the initial renderer foothold.
Feedback Code Shows the Problem With “Non-Core” Features
There is a persistent myth in software security that danger lives mostly in the obvious places: JavaScript engines, graphics stacks, codecs, and kernel interfaces. Those places are indeed dangerous. But browser security history keeps showing that “supporting” features can become attack surface when they bridge trust zones.Feedback workflows are especially interesting because they may handle screenshots, page metadata, logs, diagnostic state, user text, attachments, environment information, or browser-internal routing. Even if a given vulnerability does not involve all of those things, the category should make defenders attentive. Diagnostic and reporting features often exist to collect messy reality and hand it to more privileged code.
Improper input validation is one of the oldest weakness classes because it is not a single bug pattern so much as a failure of boundary discipline. A component receives data that originated somewhere untrusted and does not sufficiently constrain, canonicalize, verify, or reject it before making a security-relevant decision. In a sandboxed browser, that kind of mistake is especially costly when it appears near a privileged broker or service.
The story is not that Feedback is uniquely reckless. The story is that every convenience feature added to a browser must be designed as if hostile content will eventually try to reach it through a weird path. In 2026, that is not paranoia; it is table stakes.
Patch Management Has Become Browser Incident Response
For home users, the answer is simple: update Chrome and restart it. For managed Windows environments, the answer is messier because browsers tend to stay open, sessions linger, and update completion is not the same as update installation. Chrome can download an update and wait patiently for a restart while the vulnerable process continues to run.That distinction should be familiar to any admin who has watched users keep 73 tabs open for three weeks. A green dashboard showing “update available” or “update installed” may not mean the active browser process has crossed the fixed-version line. The only version that matters is the one actually running after restart.
Enterprise policy can help, but only if it is used assertively. Chrome and Edge both support controls for update cadence, relaunch notification, and forced relaunch windows. Those controls exist because the browser is too important to leave entirely to user convenience.
The practical response to CVE-2026-7345 is therefore not exotic. Inventory versions. Push the update. Force relaunch where risk justifies it. Verify that endpoints report a fixed running build. Repeat the same logic for Edge and other Chromium-based software rather than assuming one browser update solves the shared-engine problem.
The CPE Detail Is Useful, but It Is Not the Whole Asset List
The NVD configuration shown for this CVE describes Google Chrome versions up to, but excluding, 147.0.7727.138, with operating-system branches including Windows, Linux, and macOS. That is the formal vulnerability-record view, and it is useful for scanners, SBOM tools, and vulnerability management platforms that rely on CPE matching.But CPEs are only as good as the software inventory behind them. A scanner can match Google Chrome if it knows Chrome is installed. It may not catch every embedded Chromium runtime in a packaged enterprise application. It may not understand portable browser installs, per-user installs, stale profiles, kiosk images, or nonstandard update channels.
This is where vulnerability management drifts into asset management. The CVE tells you what is affected. The fleet tells you whether you can prove it is gone.
For WindowsForum readers, the uncomfortable operational truth is that many organizations still have better visibility into monthly Windows cumulative updates than into browser runtime versions. That imbalance no longer matches the risk. Browser patching has become a first-class endpoint security function, not a side effect of desktop hygiene.
Restricted Bug Details Are a Feature, Not a Cover-Up
Google’s release notes routinely say that access to bug details may remain restricted until a majority of users are updated. This frustrates researchers and admins who want to understand exactly what broke. It also makes sense.Publishing exploit-relevant details while hundreds of millions of browsers are still waiting for rollout would be a gift to attackers. The browser ecosystem lives under a disclosure rhythm that tries to balance research transparency with herd immunity. That rhythm is imperfect, but it is not arbitrary.
For defenders, the lack of technical detail should not stall action. You do not need a proof-of-concept to justify deploying a stable-channel update that fixes a high-severity sandbox escape. Waiting for the bug tracker to open before patching is like waiting for smoke in the hallway before checking whether the fire door closes.
The better posture is to treat restricted detail as a signal that the vendor believes premature disclosure could increase risk. In other words, the absence of detail is itself part of the security communication.
Attack Chains Care About Boring Components
The modern browser exploit chain is a study in specialization. One bug gains code execution in a renderer. Another leaks information or defeats a mitigation. Another escapes the sandbox. Another pivots into the OS, steals tokens, drops a payload, or hands control to a post-exploitation framework.CVE-2026-7345 belongs to that chain-shaped world. It is not necessarily the first bug an attacker would use. It may be the one that makes the first bug worth using.
This is why patch prioritization based only on standalone exploitability can mislead. A vulnerability with high complexity and a prerequisite can still be urgent if the prerequisite is common in the attacker’s toolbox. Browser renderer bugs are not hypothetical. They are a recurring product of the web’s complexity, and attackers have every incentive to pair them with escape paths.
The other lesson is architectural. Sandboxes reduce blast radius, but they also create high-value boundaries. Every interface that allows a less-trusted process to ask a more-trusted process for help becomes a place where validation must be unforgiving. Feedback, GPU, accessibility, media, printing, file handling, permissions, and diagnostics all become potential border crossings.
Windows Admins Should Stop Waiting for Patch Tuesday
One of the more dangerous habits in Windows environments is the gravitational pull of Patch Tuesday. It gives organizations a predictable cycle, a change-control ritual, and a reporting structure. Browser security does not care.Chrome stable updates land when Chrome stable updates land. Edge security releases land on Microsoft’s browser schedule, not necessarily the OS cumulative-update schedule. Zero-days and high-severity Chromium fixes have repeatedly arrived outside the comfortable monthly cadence.
CVE-2026-7345 was published at the end of April, not on a neat Microsoft calendar boundary. That is the world administrators now live in. If the browser is a major ingress path, then browser patching must be continuous enough to match browser risk.
That does not mean every Chrome update needs an emergency bridge call. It does mean organizations should have a defined browser emergency lane: a path for accelerating updates, forcing restarts, validating versions, and communicating to users without waiting for the next full endpoint patch cycle.
The Home User Version Is Still Brutally Simple
For enthusiasts and home users, the defensive guidance is almost disappointingly mundane. Open Chrome’s About page, let it update, and relaunch. Then check the version. If it is Chrome on Windows or Mac, the fixed line for this CVE is 147.0.7727.138 or later.The same logic applies to other Chromium browsers, but the version numbers may differ because downstream vendors ship their own builds. Edge users should check Edge’s About page and rely on Microsoft’s security release channel for the corresponding Chromium uptake. Users of Brave, Vivaldi, Opera, and similar browsers should verify that their vendor has shipped a release incorporating the relevant Chromium fixes.
There is no credible mitigation that beats updating. Disabling Feedback is not a practical general answer, and speculative hardening tweaks are not substitutes for a patched browser. Site isolation, sandboxing, exploit mitigations, endpoint protection, and least privilege all help, but the vulnerable code still needs to be replaced.
The browser restart is the part users skip. It is also the part that turns an update from a downloaded promise into a running fix.
This Chrome Fix Deserves a Short, Unromantic Checklist
The right response to CVE-2026-7345 is not panic, but it is also not passive acknowledgment. Treat it as a browser-boundary bug that belongs in the same operational bucket as other sandbox escape fixes: patch quickly, verify completely, and broaden the search beyond the obvious browser icon.- Chrome on Windows and Mac should be updated to 147.0.7727.138 or later to clear the affected range for CVE-2026-7345.
- Chrome on Linux should be checked against the corresponding 147.0.7727.137 stable-channel build listed for the April 28 desktop update.
- Administrators should confirm that browsers have relaunched after updating, because downloaded updates do not protect still-running vulnerable processes.
- Edge and other Chromium-based browsers should be tracked separately, since Chromium fixes flow downstream on vendor-specific schedules.
- Vulnerability scanners should be backed by real asset inventory, because CPE matching may miss embedded or nonstandard Chromium runtimes.
- The absence of a public exploit report should not delay patching, because sandbox escapes are valuable as components in larger exploit chains.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center