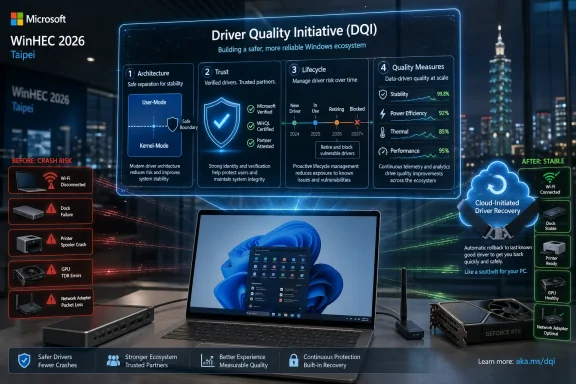
Microsoft introduced the Driver Quality Initiative at WinHEC 2026 in Taipei on May 14, 2026, outlining a Windows ecosystem push with OEMs, silicon vendors, hardware makers, and ODMs to improve driver reliability, security, lifecycle management, and recovery across Windows 11. The announcement sounds technical because it is technical, but the stakes are ordinary: fewer blue screens, fewer broken peripherals, fewer mystery slowdowns after an update. Microsoft is not merely promising better troubleshooting after Windows breaks. It is trying to move the crash boundary itself.
For decades, Windows’ greatest strength has also been its most stubborn liability. It runs on an enormous range of hardware, from boutique gaming desktops to office fleets, industrial controllers, bargain laptops, USB docks, printers, webcams, Wi-Fi adapters, audio interfaces, and machines whose component mix was chosen by procurement rather than engineering elegance.
That variety is why Windows won the PC market. It is also why Windows reliability is never solely Microsoft’s product. Every silicon vendor, OEM image, peripheral utility, firmware package, and third-party driver becomes part of the operating system experience once a user plugs something in or Windows Update decides a driver is ready.
The Driver Quality Initiative, or DQI, is Microsoft’s attempt to formalize that reality. The company is framing it as an ecosystem-wide effort built around architecture, trust, lifecycle management, and broader quality measurement. Translated out of conference language, Microsoft is saying that driver quality can no longer be measured only by whether a component passes a certification gate and avoids an obvious crash.
That matters because driver failures are uniquely punishing. When an app crashes, the user blames the app. When a graphics, storage, network, audio, chipset, or security driver misbehaves, the whole PC can look defective. The real cause may sit three companies away from the Windows shell, but the user sees one thing: Windows failed.
Kernel-mode drivers are not inherently sloppy or unsafe. They exist because hardware often needs low-level access, and Windows’ broad hardware support depends on a model that lets partners extend the system. But this model asks the operating system to trust a vast external supply chain of code that may vary dramatically in age, engineering discipline, test coverage, and update cadence.
Microsoft’s new emphasis on moving more work out of kernel mode is therefore not a minor implementation detail. It is the architectural heart of the story. A user-mode driver that fails can often be restarted or isolated without taking down the entire OS. A kernel-mode driver failure can turn a single faulty component into a system-wide event.
This is not a new dream. Microsoft has been trying, in different ways and across different driver classes, to reduce the danger of privileged third-party code for years. What is different now is the company’s willingness to put that ambition inside a larger quality program and connect it to partner accountability, Windows Update hygiene, and measurable customer impact.
The hard part is that Windows cannot simply banish kernel drivers overnight. Performance, compatibility, device complexity, and years of ecosystem investment all constrain how fast the model can change. The most credible reading of DQI is not that Microsoft has discovered a magic switch, but that it is trying to narrow the set of places where Windows must take that old risk.
Architecture is the most visible pillar because it deals with where driver code runs and how much damage it can do. Microsoft says it is investing in hardening kernel-mode drivers while enabling transitions toward user-mode drivers or Microsoft-authored class drivers. The significance is not only isolation; it is standardization. A Microsoft-maintained class driver can reduce the need for every vendor to ship its own version of a solution to a common hardware problem.
Trust is the pillar that will matter most to partners. Stronger partner verification, automated analysis, and updated Windows Hardware Compatibility Program requirements mean Microsoft is tightening the terms under which driver code earns distribution and credibility. That may make some vendors grumble, but it is exactly where a platform steward has to push if it wants fewer bad packages reaching users.
Lifecycle is the pillar that administrators should watch closely. Driver problems are rarely just about new code being bad. They are also about stale code lingering too long, superseded packages remaining discoverable, and Windows Update catalogs accumulating cruft that looks harmless until a matching rule chooses the wrong thing for the wrong machine.
Quality measures may be the most mature part of the proposal. Microsoft says it wants to measure driver quality beyond crashes, including functionality, performance, stability, and power and thermal impact. That is important because many driver failures do not announce themselves with a blue screen. They show up as battery drain, fan noise, unreliable sleep, flaky Bluetooth, stuttering audio, broken docking, or a machine that feels cursed after Patch Tuesday.
Microsoft’s promise of better catalog hygiene is therefore more meaningful than it may sound. Removing outdated or low-quality drivers from the active distribution path can prevent machines from regressing to unsuitable packages. Better symbols can speed issue analysis when failures occur. SBOM alignment reflects the growing expectation that software components, including low-level ones, must be traceable and auditable.
The dirty secret of driver management is that “latest” is not always best. A newer driver may fix one platform while breaking another. A vendor-provided package may be tuned for a specific OEM system image, while a generic driver may be technically compatible but functionally incomplete. A Windows Update-supplied package may solve a security problem but create a device-specific support mess.
DQI will be judged by whether it reduces those mismatches. Microsoft can talk about ecosystem collaboration all it wants, but the user experience is decided at the moment a machine receives a package, installs it, reboots, and either keeps working or does not. In that moment, architecture and trust become very practical.
But recovery is not the same as reliability. A rollback system reduces the blast radius after something goes wrong. DQI is aimed at reducing the number of things that go wrong in the first place. The distinction matters because Microsoft’s credibility problem with Windows quality has never been limited to catastrophic failures; it is the accumulation of small breakages that make users distrust the update pipeline.
Cloud-initiated recovery also has practical limits. It is most naturally suited to drivers delivered through Microsoft’s update mechanisms, not every package a user downloads from a vendor utility, a gaming app, a motherboard support page, or a peripheral installer. It also depends on Microsoft detecting the problem, identifying affected devices, and having a safe fallback path available.
That does not make it unimportant. In fact, it may be one of the more useful pieces of the broader resiliency push. But it should be understood as part of a layered strategy: better driver architecture, stricter admission controls, cleaner lifecycle management, richer telemetry, and faster recovery when prevention fails.
The seat belt analogy is apt. Nobody argues against seat belts because brakes exist. But nobody should call seat belts a substitute for brakes, either. Windows needs both.
Security vendors are not the same as hardware driver vendors, and it would be lazy to collapse every privileged-code problem into one incident. Still, the lesson is shared. Once code is close enough to the core of the system, one partner’s failure can become everyone’s outage. In enterprises, that means delayed flights, inaccessible terminals, offline point-of-sale systems, and IT teams rebuilding machines under pressure.
DQI looks like part of Microsoft’s answer to that broader concern. The company is not only trying to harden Windows against attackers; it is trying to harden Windows against trusted code behaving badly. That is a more uncomfortable problem because it cannot be solved by drawing a clean line between good and malicious software.
The future Windows model will likely involve fewer assumptions of permanent trust. Partners may still need deep access in some cases, but Microsoft is signaling that access will come with more scrutiny, more measurement, and more pressure to adopt safer models where available. For vendors used to treating driver distribution as a compatibility checkbox, that is a cultural shift.
The same is true for OEMs and ODMs. A laptop is not just a CPU and a copy of Windows. It is a bundle of firmware, thermal policy, sensors, audio routing, camera components, wireless modules, touchpad behavior, power profiles, and vendor utilities. If any part of that stack is poorly maintained, Windows becomes the visible face of someone else’s engineering debt.
Microsoft’s challenge is political as much as technical. The company needs partners to move faster, test better, retire bad packages, and accept tighter requirements without feeling that Windows is becoming a closed platform. That is a delicate balance because the Windows ecosystem’s openness is not an accident. It is the product’s market identity.
The most optimistic version of DQI is that it creates shared incentives. Better telemetry tells a vendor where users are suffering. Stricter certification catches risky packages before release. Cleaner lifecycle rules prevent obsolete drivers from resurfacing. User-mode transitions reduce the consequences when defects slip through.
The cynical version is that it gives Microsoft a new set of phrases to deploy after the next driver debacle. The truth will be visible only over time, in crash rates, support incidents, update rollbacks, and the everyday absence of drama.
Enterprises already try to manage this risk with rings, staged rollouts, vendor validation, Intune policy, Windows Update for Business controls, and device standardization. But those controls do not eliminate the upstream quality problem. They mostly slow it down and give IT a chance to detect damage before it spreads everywhere.
If DQI works, administrators should eventually see fewer driver packages that require emergency blocking, fewer regressions after routine maintenance, and clearer signals about which drivers are safe for which devices. Better symbols and faster issue analysis could also matter for escalations, where the difference between “known issue under investigation” and “here is the bad driver and affected hardware ID” is the difference between a long outage and a contained incident.
There is also a security angle. Vulnerable drivers are a favored path for attackers seeking privileged access, and the industry has spent years dealing with signed but exploitable drivers. Stronger trust requirements and better lifecycle management can help reduce that attack surface, especially if Microsoft becomes more aggressive about retiring drivers that should no longer be accepted as normal.
But enterprises will also ask a fair question: who controls the override? If Microsoft can remotely initiate recovery actions or more aggressively curate drivers, administrators will want transparent policy controls, reporting, and predictable behavior. Fleet owners do not want surprise breakage from bad drivers, but they also do not want surprise remediation actions they cannot audit.
That is why driver reliability has outsized emotional weight. A bad driver can make users feel powerless because the failure often appears unrelated to anything they intentionally changed. The machine rebooted, Windows said it was updating, and suddenly audio vanished, a monitor stopped waking, a game stutters, the trackpad misbehaves, or Wi-Fi becomes unreliable.
The consumer PC market also has more chaos than Microsoft’s clean diagrams can convey. Users install GPU drivers directly from AMD, Intel, or Nvidia. Motherboard utilities offer their own update mechanisms. Peripheral makers bundle services and background tools. Laptop vendors maintain support pages unevenly across product lifetimes. Windows Update is one participant in a crowded driver economy, not the only gatekeeper.
Still, Microsoft has leverage. Windows Update remains a default path for many drivers, and Windows’ built-in class drivers shape how much third-party software is necessary for common hardware. If Microsoft can make more devices work well with first-party class drivers, and make dangerous third-party failures less catastrophic, consumers may never know DQI exists. That would be the ideal outcome.
A reliability initiative succeeds when it disappears. Nobody praises the update that did not break the USB dock. Nobody writes a forum post about the blue screen that never happened. But those non-events are exactly what Windows needs more of.
Some classes of drivers are better candidates for user-mode isolation than others. Many peripheral and component interactions can tolerate the added abstraction or can be redesigned around safer frameworks. Other areas, particularly those involving high-performance graphics, storage, security enforcement, or specialized hardware, may remain closer to the kernel for longer.
Microsoft’s mention of performance updates for PCIe devices with DMA support is important in this context. Moving driver work to user mode is only credible if it does not impose unacceptable performance costs or break expectations for hardware vendors. The company cannot simply say “safer” and expect partners to accept “slower.”
The Wi-Fi stack reference is also worth watching. Wireless reliability is one of those areas where users rarely care whose code is at fault. If a laptop drops networks after sleep or behaves inconsistently across access points, the platform feels bad. Improvements there would be felt immediately, especially on mobile devices where connectivity and power management intersect.
The broader class-driver push may be the quietest but most consequential part. Standardized Microsoft-authored drivers for common hardware reduce duplicated vendor effort and narrow the space for inconsistent implementations. The tradeoff is that vendors may have fewer ways to differentiate, but for many device classes, reliability is more valuable than novelty.
A driver can wake the CPU too often and ruin battery life. It can mishandle sleep states and make a laptop unreliable in a bag. It can produce intermittent device disconnects that users interpret as hardware failure. It can cause thermal spikes, audio glitches, input latency, or application hangs that never show up as a traditional driver crash.
Measuring power and thermal impact is especially relevant as Windows laptops compete more directly on battery life, standby behavior, and perceived responsiveness. Modern PCs are judged not only by benchmark peaks but by whether they stay quiet, wake reliably, and preserve charge. Drivers sit directly in that path.
Functionality measurement is harder but necessary. A device that avoids crashing but fails under common workflows is not high quality. The industry has too often treated “does not blue-screen” as a sufficient bar. Users experience quality as a chain of small expectations being met repeatedly.
If DQI gives partners clearer feedback on these subtler failures, it could improve the parts of Windows reliability that have historically felt anecdotal. The challenge will be separating signal from noise across a massive install base where hardware combinations, workloads, regional driver packages, and OEM configurations all differ.
That is why stronger partner verification and expanded automated analysis matter. Trust can no longer be just a business relationship, a signing process, or a badge acquired once and treated as durable. It has to be continuously earned through observed quality, secure development practices, and responsible maintenance.
Automated analysis will not catch everything. Static and dynamic testing can miss device-specific timing problems, firmware interactions, and rare workload combinations. But stronger analysis can raise the floor, especially against obvious unsafe patterns, known vulnerable components, or packages that do not meet modern expectations.
The same applies to updated compatibility requirements. Certification programs are only meaningful if they evolve with the threat model and user expectations. A driver model that was acceptable when PCs were less connected, less managed, and less security-sensitive may not be acceptable in 2026.
The risk for Microsoft is overreach. If the company tightens the gates too aggressively, smaller hardware vendors may struggle, legacy device support may suffer, and enthusiasts may complain that Windows is becoming less flexible. If it moves too gently, the initiative becomes another quality slogan. The art is in making the safe path the easy path without turning Windows into a locked appliance.
This fragmentation creates slow accountability. Everyone has partial evidence, and no one owns the complete user experience. DQI’s language about joint accountability is therefore more than corporate diplomacy. It is a recognition that the old blame chain is too slow for modern update velocity.
Better driver symbols and faster issue analysis could shorten that chain. If Microsoft and partners can identify failures more precisely, the ecosystem can move from anecdote to diagnosis faster. That matters for both consumer support and enterprise escalation.
There is also a reputational incentive. Windows quality complaints often bundle unrelated frustrations together: update timing, driver regressions, UI changes, performance variance, security prompts, OEM bloat, and hardware defects. Improving driver reliability will not solve all of that, but it removes one major source of unpredictable pain.
Microsoft’s broader “Windows K2” quality push is best understood in that light. The company appears to be acknowledging that feature velocity is not enough. Windows 11 does not need only new AI buttons, redesigned dialogs, or cloud integrations. It needs to feel less random.
The first visible test will be Windows Update behavior. If Microsoft improves catalog hygiene, users should encounter fewer cases where Windows installs an inappropriate or stale driver over a vendor-preferred package. Enthusiasts will be watching GPU drivers closely because graphics stacks are among the most visible and emotionally charged driver domains.
The second test will be recovery. Cloud-Initiated Driver Recovery sounds promising, but it has to be fast, accurate, and transparent. Rolling back the wrong systems, rolling back too slowly, or failing to communicate what happened would trade one kind of confusion for another.
The third test will be partner discipline. Microsoft can build frameworks and telemetry, but AMD, Intel, Nvidia, Qualcomm, Realtek, Dell, HP, Lenovo, peripheral vendors, and countless others must do the unglamorous work of testing, maintaining, and retiring driver packages responsibly. The ecosystem is only as strong as the least careful participant with privileged code.
The fourth test will be whether Microsoft resists turning DQI into another compliance maze that produces paperwork instead of quality. Checklists are useful, but they can become theater. Real reliability improvement requires incentives tied to user outcomes, not just submission requirements.
The caveat is that driver ecosystems move slowly. Devices in the field will not magically become modern. Old packages will not all disappear at once. Vendors will vary in how quickly they adapt. Enterprises will still need staged rollouts, hardware baselines, and rollback plans.
Consumers should not expect the next Windows update to eliminate driver weirdness. But over time, a more disciplined driver pipeline could reduce the kind of silent regressions that make ordinary users afraid of updates. The best version of this program is not exciting; it is boring reliability.
For IT pros, the announcement is a reason to watch Microsoft’s driver reporting, Windows Update controls, and recovery policies closely over the next several release cycles. DQI may eventually change how driver risk is assessed inside fleets. But until the tooling and reporting mature, it remains one layer in a larger endpoint management strategy.
Apple solves part of this problem by controlling far more of the hardware and software stack. Microsoft cannot copy that model without breaking what makes Windows Windows. Instead, it has to govern a sprawling market with contracts, certification, telemetry, update policy, and architectural nudges.
That is harder, messier, and less satisfying than a clean platform reset. But it is also more realistic. The PC ecosystem is not going to become vertically integrated because driver crashes are annoying. Millions of users and businesses depend on the messy abundance of Windows hardware choice.
DQI is Microsoft’s attempt to make that abundance less hazardous. It is a governance project disguised as a driver project. The company is trying to decide which risks belong in the kernel, which belong in user mode, which belong behind stricter partner gates, and which should be removed from the update stream entirely.
If it works, Windows users will not celebrate DQI by name. They will simply notice that the machine wakes from sleep, the dock stays connected, the GPU driver does not get surprise-replaced, and a bad package does not turn into a weekend support ordeal.
Source: Windows Central Microsoft is changing how Windows talks to hardware to stop system crashes
 Microsoft Is Finally Treating Drivers as a Platform Problem
Microsoft Is Finally Treating Drivers as a Platform Problem
For decades, Windows’ greatest strength has also been its most stubborn liability. It runs on an enormous range of hardware, from boutique gaming desktops to office fleets, industrial controllers, bargain laptops, USB docks, printers, webcams, Wi-Fi adapters, audio interfaces, and machines whose component mix was chosen by procurement rather than engineering elegance.That variety is why Windows won the PC market. It is also why Windows reliability is never solely Microsoft’s product. Every silicon vendor, OEM image, peripheral utility, firmware package, and third-party driver becomes part of the operating system experience once a user plugs something in or Windows Update decides a driver is ready.
The Driver Quality Initiative, or DQI, is Microsoft’s attempt to formalize that reality. The company is framing it as an ecosystem-wide effort built around architecture, trust, lifecycle management, and broader quality measurement. Translated out of conference language, Microsoft is saying that driver quality can no longer be measured only by whether a component passes a certification gate and avoids an obvious crash.
That matters because driver failures are uniquely punishing. When an app crashes, the user blames the app. When a graphics, storage, network, audio, chipset, or security driver misbehaves, the whole PC can look defective. The real cause may sit three companies away from the Windows shell, but the user sees one thing: Windows failed.
Kernel Mode Was the Bargain Windows Could Not Escape
The central technical issue is old, blunt, and still relevant: many third-party drivers run in kernel mode. That gives them privileged access to the deepest parts of the operating system, where performance-sensitive hardware interaction can happen with minimal overhead. It also means a bad driver can destabilize the machine in ways ordinary software cannot.Kernel-mode drivers are not inherently sloppy or unsafe. They exist because hardware often needs low-level access, and Windows’ broad hardware support depends on a model that lets partners extend the system. But this model asks the operating system to trust a vast external supply chain of code that may vary dramatically in age, engineering discipline, test coverage, and update cadence.
Microsoft’s new emphasis on moving more work out of kernel mode is therefore not a minor implementation detail. It is the architectural heart of the story. A user-mode driver that fails can often be restarted or isolated without taking down the entire OS. A kernel-mode driver failure can turn a single faulty component into a system-wide event.
This is not a new dream. Microsoft has been trying, in different ways and across different driver classes, to reduce the danger of privileged third-party code for years. What is different now is the company’s willingness to put that ambition inside a larger quality program and connect it to partner accountability, Windows Update hygiene, and measurable customer impact.
The hard part is that Windows cannot simply banish kernel drivers overnight. Performance, compatibility, device complexity, and years of ecosystem investment all constrain how fast the model can change. The most credible reading of DQI is not that Microsoft has discovered a magic switch, but that it is trying to narrow the set of places where Windows must take that old risk.
The Four Pillars Are Really One Argument About Control
Microsoft describes DQI through four pillars: architecture, trust, lifecycle, and quality measures. The language sounds like a familiar platform vendor diagram, but the underlying argument is sharper. Windows reliability depends on Microsoft gaining more control over code it does not always write.Architecture is the most visible pillar because it deals with where driver code runs and how much damage it can do. Microsoft says it is investing in hardening kernel-mode drivers while enabling transitions toward user-mode drivers or Microsoft-authored class drivers. The significance is not only isolation; it is standardization. A Microsoft-maintained class driver can reduce the need for every vendor to ship its own version of a solution to a common hardware problem.
Trust is the pillar that will matter most to partners. Stronger partner verification, automated analysis, and updated Windows Hardware Compatibility Program requirements mean Microsoft is tightening the terms under which driver code earns distribution and credibility. That may make some vendors grumble, but it is exactly where a platform steward has to push if it wants fewer bad packages reaching users.
Lifecycle is the pillar that administrators should watch closely. Driver problems are rarely just about new code being bad. They are also about stale code lingering too long, superseded packages remaining discoverable, and Windows Update catalogs accumulating cruft that looks harmless until a matching rule chooses the wrong thing for the wrong machine.
Quality measures may be the most mature part of the proposal. Microsoft says it wants to measure driver quality beyond crashes, including functionality, performance, stability, and power and thermal impact. That is important because many driver failures do not announce themselves with a blue screen. They show up as battery drain, fan noise, unreliable sleep, flaky Bluetooth, stuttering audio, broken docking, or a machine that feels cursed after Patch Tuesday.
Windows Update Needs to Become Less of a Driver Slot Machine
The driver story cannot be separated from Windows Update. For consumers, Windows Update is the pipeline through which many driver packages arrive. For enterprise IT, it is one of several tools in a more controlled deployment chain. In both cases, the update mechanism is only as good as the quality of the metadata, targeting, testing, rollback path, and partner discipline behind it.Microsoft’s promise of better catalog hygiene is therefore more meaningful than it may sound. Removing outdated or low-quality drivers from the active distribution path can prevent machines from regressing to unsuitable packages. Better symbols can speed issue analysis when failures occur. SBOM alignment reflects the growing expectation that software components, including low-level ones, must be traceable and auditable.
The dirty secret of driver management is that “latest” is not always best. A newer driver may fix one platform while breaking another. A vendor-provided package may be tuned for a specific OEM system image, while a generic driver may be technically compatible but functionally incomplete. A Windows Update-supplied package may solve a security problem but create a device-specific support mess.
DQI will be judged by whether it reduces those mismatches. Microsoft can talk about ecosystem collaboration all it wants, but the user experience is decided at the moment a machine receives a package, installs it, reboots, and either keeps working or does not. In that moment, architecture and trust become very practical.
Cloud Recovery Is the Seat Belt, Not the Brakes
The timing of DQI is notable because Microsoft has also been discussing Cloud-Initiated Driver Recovery, a capability designed to roll affected devices back to a known-good driver after a problematic update. That is an important safety mechanism, especially for large fleets where a bad driver can become a help desk crisis in hours.But recovery is not the same as reliability. A rollback system reduces the blast radius after something goes wrong. DQI is aimed at reducing the number of things that go wrong in the first place. The distinction matters because Microsoft’s credibility problem with Windows quality has never been limited to catastrophic failures; it is the accumulation of small breakages that make users distrust the update pipeline.
Cloud-initiated recovery also has practical limits. It is most naturally suited to drivers delivered through Microsoft’s update mechanisms, not every package a user downloads from a vendor utility, a gaming app, a motherboard support page, or a peripheral installer. It also depends on Microsoft detecting the problem, identifying affected devices, and having a safe fallback path available.
That does not make it unimportant. In fact, it may be one of the more useful pieces of the broader resiliency push. But it should be understood as part of a layered strategy: better driver architecture, stricter admission controls, cleaner lifecycle management, richer telemetry, and faster recovery when prevention fails.
The seat belt analogy is apt. Nobody argues against seat belts because brakes exist. But nobody should call seat belts a substitute for brakes, either. Windows needs both.
The CrowdStrike Shadow Still Hangs Over Windows Engineering
Microsoft’s driver push arrives in a post-CrowdStrike world, even when the company is not making every sentence about CrowdStrike. The 2024 outage, caused by a faulty security content update interacting with privileged endpoint software, exposed how fragile the modern Windows endpoint ecosystem can be when trusted low-level components fail at scale. It also forced a public conversation about how much third-party code should be allowed to run in the kernel.Security vendors are not the same as hardware driver vendors, and it would be lazy to collapse every privileged-code problem into one incident. Still, the lesson is shared. Once code is close enough to the core of the system, one partner’s failure can become everyone’s outage. In enterprises, that means delayed flights, inaccessible terminals, offline point-of-sale systems, and IT teams rebuilding machines under pressure.
DQI looks like part of Microsoft’s answer to that broader concern. The company is not only trying to harden Windows against attackers; it is trying to harden Windows against trusted code behaving badly. That is a more uncomfortable problem because it cannot be solved by drawing a clean line between good and malicious software.
The future Windows model will likely involve fewer assumptions of permanent trust. Partners may still need deep access in some cases, but Microsoft is signaling that access will come with more scrutiny, more measurement, and more pressure to adopt safer models where available. For vendors used to treating driver distribution as a compatibility checkbox, that is a cultural shift.
Hardware Partners Are Being Asked to Share the Blame
AMD’s public support for the initiative is not a decorative quote. Silicon vendors sit close to the fault line between operating system design and real-world hardware behavior. Graphics, chipset, storage, power management, and platform drivers can define whether a machine feels polished or perpetually unstable.The same is true for OEMs and ODMs. A laptop is not just a CPU and a copy of Windows. It is a bundle of firmware, thermal policy, sensors, audio routing, camera components, wireless modules, touchpad behavior, power profiles, and vendor utilities. If any part of that stack is poorly maintained, Windows becomes the visible face of someone else’s engineering debt.
Microsoft’s challenge is political as much as technical. The company needs partners to move faster, test better, retire bad packages, and accept tighter requirements without feeling that Windows is becoming a closed platform. That is a delicate balance because the Windows ecosystem’s openness is not an accident. It is the product’s market identity.
The most optimistic version of DQI is that it creates shared incentives. Better telemetry tells a vendor where users are suffering. Stricter certification catches risky packages before release. Cleaner lifecycle rules prevent obsolete drivers from resurfacing. User-mode transitions reduce the consequences when defects slip through.
The cynical version is that it gives Microsoft a new set of phrases to deploy after the next driver debacle. The truth will be visible only over time, in crash rates, support incidents, update rollbacks, and the everyday absence of drama.
Enterprise IT Will Care Less About the Branding Than the Failure Modes
For enterprise administrators, the DQI announcement is not interesting because it has a new acronym. It is interesting because driver quality sits at the intersection of security, compliance, device lifecycle, and user productivity. A flaky consumer webcam is annoying. A flawed network, storage, VPN, or endpoint security driver deployed across a fleet can become a business interruption.Enterprises already try to manage this risk with rings, staged rollouts, vendor validation, Intune policy, Windows Update for Business controls, and device standardization. But those controls do not eliminate the upstream quality problem. They mostly slow it down and give IT a chance to detect damage before it spreads everywhere.
If DQI works, administrators should eventually see fewer driver packages that require emergency blocking, fewer regressions after routine maintenance, and clearer signals about which drivers are safe for which devices. Better symbols and faster issue analysis could also matter for escalations, where the difference between “known issue under investigation” and “here is the bad driver and affected hardware ID” is the difference between a long outage and a contained incident.
There is also a security angle. Vulnerable drivers are a favored path for attackers seeking privileged access, and the industry has spent years dealing with signed but exploitable drivers. Stronger trust requirements and better lifecycle management can help reduce that attack surface, especially if Microsoft becomes more aggressive about retiring drivers that should no longer be accepted as normal.
But enterprises will also ask a fair question: who controls the override? If Microsoft can remotely initiate recovery actions or more aggressively curate drivers, administrators will want transparent policy controls, reporting, and predictable behavior. Fleet owners do not want surprise breakage from bad drivers, but they also do not want surprise remediation actions they cannot audit.
Consumers Just Want the Printer, GPU, and Wi-Fi to Keep Working
For home users, all of this lands differently. They do not think in terms of kernel-mode isolation, WHCP requirements, SBOM alignment, or telemetry-based quality measures. They think: my PC updated, and now the thing that worked yesterday does not work today.That is why driver reliability has outsized emotional weight. A bad driver can make users feel powerless because the failure often appears unrelated to anything they intentionally changed. The machine rebooted, Windows said it was updating, and suddenly audio vanished, a monitor stopped waking, a game stutters, the trackpad misbehaves, or Wi-Fi becomes unreliable.
The consumer PC market also has more chaos than Microsoft’s clean diagrams can convey. Users install GPU drivers directly from AMD, Intel, or Nvidia. Motherboard utilities offer their own update mechanisms. Peripheral makers bundle services and background tools. Laptop vendors maintain support pages unevenly across product lifetimes. Windows Update is one participant in a crowded driver economy, not the only gatekeeper.
Still, Microsoft has leverage. Windows Update remains a default path for many drivers, and Windows’ built-in class drivers shape how much third-party software is necessary for common hardware. If Microsoft can make more devices work well with first-party class drivers, and make dangerous third-party failures less catastrophic, consumers may never know DQI exists. That would be the ideal outcome.
A reliability initiative succeeds when it disappears. Nobody praises the update that did not break the USB dock. Nobody writes a forum post about the blue screen that never happened. But those non-events are exactly what Windows needs more of.
The User-Mode Future Will Arrive Unevenly
It is tempting to read Microsoft’s user-mode push as the beginning of the end for risky kernel drivers. That would be too clean. Windows supports too many device categories, too much legacy hardware, and too many performance-sensitive scenarios for a single transition story.Some classes of drivers are better candidates for user-mode isolation than others. Many peripheral and component interactions can tolerate the added abstraction or can be redesigned around safer frameworks. Other areas, particularly those involving high-performance graphics, storage, security enforcement, or specialized hardware, may remain closer to the kernel for longer.
Microsoft’s mention of performance updates for PCIe devices with DMA support is important in this context. Moving driver work to user mode is only credible if it does not impose unacceptable performance costs or break expectations for hardware vendors. The company cannot simply say “safer” and expect partners to accept “slower.”
The Wi-Fi stack reference is also worth watching. Wireless reliability is one of those areas where users rarely care whose code is at fault. If a laptop drops networks after sleep or behaves inconsistently across access points, the platform feels bad. Improvements there would be felt immediately, especially on mobile devices where connectivity and power management intersect.
The broader class-driver push may be the quietest but most consequential part. Standardized Microsoft-authored drivers for common hardware reduce duplicated vendor effort and narrow the space for inconsistent implementations. The tradeoff is that vendors may have fewer ways to differentiate, but for many device classes, reliability is more valuable than novelty.
Measuring More Than Crashes Is the Right Move
Microsoft’s decision to expand driver quality measurement beyond crashes is overdue and important. Blue screens are dramatic, easy to count, and politically useful inside engineering organizations because nobody argues that a crash is acceptable. But many driver defects degrade the experience without producing a clean failure signal.A driver can wake the CPU too often and ruin battery life. It can mishandle sleep states and make a laptop unreliable in a bag. It can produce intermittent device disconnects that users interpret as hardware failure. It can cause thermal spikes, audio glitches, input latency, or application hangs that never show up as a traditional driver crash.
Measuring power and thermal impact is especially relevant as Windows laptops compete more directly on battery life, standby behavior, and perceived responsiveness. Modern PCs are judged not only by benchmark peaks but by whether they stay quiet, wake reliably, and preserve charge. Drivers sit directly in that path.
Functionality measurement is harder but necessary. A device that avoids crashing but fails under common workflows is not high quality. The industry has too often treated “does not blue-screen” as a sufficient bar. Users experience quality as a chain of small expectations being met repeatedly.
If DQI gives partners clearer feedback on these subtler failures, it could improve the parts of Windows reliability that have historically felt anecdotal. The challenge will be separating signal from noise across a massive install base where hardware combinations, workloads, regional driver packages, and OEM configurations all differ.
The Windows Ecosystem Is Too Big for Trust Me Engineering
The phrase “trusted partner” has always carried tension in platform ecosystems. Microsoft needs partners to ship drivers and support hardware. Users need Microsoft to protect them from the consequences when those partners make mistakes. Partners need enough access to make their devices work well. Attackers need only one weak link.That is why stronger partner verification and expanded automated analysis matter. Trust can no longer be just a business relationship, a signing process, or a badge acquired once and treated as durable. It has to be continuously earned through observed quality, secure development practices, and responsible maintenance.
Automated analysis will not catch everything. Static and dynamic testing can miss device-specific timing problems, firmware interactions, and rare workload combinations. But stronger analysis can raise the floor, especially against obvious unsafe patterns, known vulnerable components, or packages that do not meet modern expectations.
The same applies to updated compatibility requirements. Certification programs are only meaningful if they evolve with the threat model and user expectations. A driver model that was acceptable when PCs were less connected, less managed, and less security-sensitive may not be acceptable in 2026.
The risk for Microsoft is overreach. If the company tightens the gates too aggressively, smaller hardware vendors may struggle, legacy device support may suffer, and enthusiasts may complain that Windows is becoming less flexible. If it moves too gently, the initiative becomes another quality slogan. The art is in making the safe path the easy path without turning Windows into a locked appliance.
The Support Burden Is the Hidden Cost Microsoft Is Targeting
Driver failures are expensive because they are hard to explain. A user sees Windows. An OEM sees a support ticket. A silicon vendor sees a package version. Microsoft sees telemetry. An enterprise admin sees a fleet pattern. The peripheral maker may see nothing until complaints accumulate.This fragmentation creates slow accountability. Everyone has partial evidence, and no one owns the complete user experience. DQI’s language about joint accountability is therefore more than corporate diplomacy. It is a recognition that the old blame chain is too slow for modern update velocity.
Better driver symbols and faster issue analysis could shorten that chain. If Microsoft and partners can identify failures more precisely, the ecosystem can move from anecdote to diagnosis faster. That matters for both consumer support and enterprise escalation.
There is also a reputational incentive. Windows quality complaints often bundle unrelated frustrations together: update timing, driver regressions, UI changes, performance variance, security prompts, OEM bloat, and hardware defects. Improving driver reliability will not solve all of that, but it removes one major source of unpredictable pain.
Microsoft’s broader “Windows K2” quality push is best understood in that light. The company appears to be acknowledging that feature velocity is not enough. Windows 11 does not need only new AI buttons, redesigned dialogs, or cloud integrations. It needs to feel less random.
The Real Test Begins After the Conference Slides
WinHEC is the right venue for this announcement because driver quality is an engineering ecosystem problem. But conferences are where alignment is declared, not where reliability is proven. The evidence will arrive later, in whether users see fewer bad driver pushes and whether IT departments spend less time firefighting device regressions.The first visible test will be Windows Update behavior. If Microsoft improves catalog hygiene, users should encounter fewer cases where Windows installs an inappropriate or stale driver over a vendor-preferred package. Enthusiasts will be watching GPU drivers closely because graphics stacks are among the most visible and emotionally charged driver domains.
The second test will be recovery. Cloud-Initiated Driver Recovery sounds promising, but it has to be fast, accurate, and transparent. Rolling back the wrong systems, rolling back too slowly, or failing to communicate what happened would trade one kind of confusion for another.
The third test will be partner discipline. Microsoft can build frameworks and telemetry, but AMD, Intel, Nvidia, Qualcomm, Realtek, Dell, HP, Lenovo, peripheral vendors, and countless others must do the unglamorous work of testing, maintaining, and retiring driver packages responsibly. The ecosystem is only as strong as the least careful participant with privileged code.
The fourth test will be whether Microsoft resists turning DQI into another compliance maze that produces paperwork instead of quality. Checklists are useful, but they can become theater. Real reliability improvement requires incentives tied to user outcomes, not just submission requirements.
The Practical Reading for Windows Users and Admins
For now, DQI should be treated as a serious directional signal rather than an immediate fix. It tells us where Microsoft wants Windows hardware interaction to go: less risky kernel dependence, more standardized class drivers, stricter trust, cleaner updates, richer telemetry, and faster remediation. That is the correct direction.The caveat is that driver ecosystems move slowly. Devices in the field will not magically become modern. Old packages will not all disappear at once. Vendors will vary in how quickly they adapt. Enterprises will still need staged rollouts, hardware baselines, and rollback plans.
Consumers should not expect the next Windows update to eliminate driver weirdness. But over time, a more disciplined driver pipeline could reduce the kind of silent regressions that make ordinary users afraid of updates. The best version of this program is not exciting; it is boring reliability.
For IT pros, the announcement is a reason to watch Microsoft’s driver reporting, Windows Update controls, and recovery policies closely over the next several release cycles. DQI may eventually change how driver risk is assessed inside fleets. But until the tooling and reporting mature, it remains one layer in a larger endpoint management strategy.
The Bet Is That Windows Can Stay Open Without Staying Fragile
Microsoft’s move is ultimately a bet that Windows can preserve its vast hardware ecosystem without accepting the old level of fragility as the cost of doing business. That is not guaranteed. Openness and reliability are often in tension, and Windows has historically erred on the side of compatibility.Apple solves part of this problem by controlling far more of the hardware and software stack. Microsoft cannot copy that model without breaking what makes Windows Windows. Instead, it has to govern a sprawling market with contracts, certification, telemetry, update policy, and architectural nudges.
That is harder, messier, and less satisfying than a clean platform reset. But it is also more realistic. The PC ecosystem is not going to become vertically integrated because driver crashes are annoying. Millions of users and businesses depend on the messy abundance of Windows hardware choice.
DQI is Microsoft’s attempt to make that abundance less hazardous. It is a governance project disguised as a driver project. The company is trying to decide which risks belong in the kernel, which belong in user mode, which belong behind stricter partner gates, and which should be removed from the update stream entirely.
If it works, Windows users will not celebrate DQI by name. They will simply notice that the machine wakes from sleep, the dock stays connected, the GPU driver does not get surprise-replaced, and a bad package does not turn into a weekend support ordeal.
The Driver Story Windows Users Should Actually Remember
The important lesson is not that Microsoft has announced another quality initiative. It is that the company is attacking driver reliability from multiple angles at once, which is the only plausible way to improve a problem this distributed. The initiative’s success will depend less on the acronym and more on whether Microsoft and its partners change the daily mechanics of driver design, validation, delivery, and retirement.- Microsoft introduced DQI at WinHEC 2026 as a partner-wide effort to improve Windows driver reliability, security, lifecycle management, and real-world quality.
- The most important architectural shift is the continued movement of risky third-party driver work away from kernel mode where practical.
- Better Windows Update catalog hygiene could reduce stale, low-quality, or poorly targeted drivers reaching user machines.
- Cloud-Initiated Driver Recovery is a useful fallback, but it does not replace the need to prevent bad driver updates in the first place.
- Enterprise administrators should watch for policy controls, reporting, and auditability around driver recovery and quality signals.
- Consumers should expect gradual reliability gains rather than an overnight end to driver-related Windows problems.
Source: Windows Central Microsoft is changing how Windows talks to hardware to stop system crashes