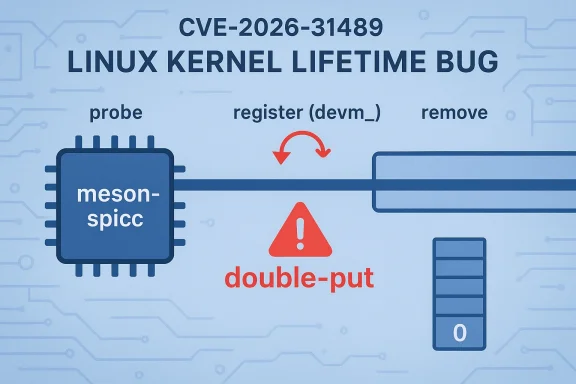
CVE-2026-31489 is a classic Linux kernel lifetime bug with outsized operational meaning: a seemingly small double-put in the Meson SPI controller driver can still turn into a crash, a teardown failure, or a hard-to-debug stability problem when a system removes the device. The issue is simple on its face, but the security and reliability lesson is bigger than the code change itself. The fix matters because it cleans up ownership semantics in a kernel subsystem where reference counting mistakes can ripple outward into platform instability. The published record ties the flaw directly to the
That context is essential for understanding why CVE-2026-31489 was assigned. The affected driver,
The Linux kernel’s own CVE process helps explain why issues like this get tracked publicly even when they don’t map neatly onto a single exploit primitive. The kernel documentation explicitly notes that CVEs are often assigned once a fix is available and merged into a stable tree, and that the project tends to be cautious about security relevance because almost any kernel bug can become security-relevant in the wrong context. That philosophy matters here. A double-put is not a dramatic remote code execution bug, but it is exactly the sort of correctness failure that can become an availability problem or an exploit building block if it is left uncorrected.
Microsoft’s Security Update Guide surfaced the CVE quickly, which is increasingly normal for Linux issues that matter to enterprise administrators. In mixed fleets, a Linux kernel issue is no longer just “a Linux problem”; it is part of a broader vulnerability workflow that many organizations already use to track Windows, Azure, and Linux advisories together. That cross-platform visibility doe, but it absolutely changes the operational urgency.
At a technical level, the flaw is straightforward:
That kind of bug is easy to underestimate if you only look at the surface. The kernel is built on explicit ownership transfer, and reference counting is how it keeps shared objects from disappearing too early. A double-put can break that invariant in two different ways. In the best case, it results in a warning or a harmless underflow that exposes a code bug. In the worst case, it can free an object earlier than intended and leave later cleanup code touching memory it no longer owns.
This is one of those kernel bugs that feels mundane until you remember how much low-level system software depends on precise cleanup. A device-managed registration is meant to reduce boilerplate and eliminate hand-written release logic. If a driver author later adds a manual
It is also worth emphasizing that the issue is not hypothetical. The CVE record was published with stable references and commit links already attached, which is a strong sign that the fix had moved through the normal Linux security workflow rather than remaining a mere code re security, that distinction matters because it tells administrators the bug was important enough to be fixed, tracked, and backported rather than simply discussed.
The SPI documentation makes clear that controllers and drivers are separate roles, with the controller object managing host-side behavior and the driver lifecycle handling registration and unbinding. That division of responsibility is useful, but it also means that a driver author has to respect the lifecycle contract precisely.
That simplicity is a strength. In kernel maintenance, the best fixes are often the ones that restore the original ownership model rather than layering on new special cases. This patch does exactly that. It does not redesign SPI. It does not alter controller semantics. It simply removes the duplicate release so that the remove path matches the registration path.
The enterprise impact is especially relevant for embedded, industrial, and appliance-style Linux systems, where the same kernel image may run for long periods with very little change. Those environments often use vendor kernels, not mainline builds, which means the time between upstream fix and practical exposure reduction can be longer than users expect. The existence of a published CVE does not guarantee a fleet is actually safe; it only means the issue has been formally identified and tracked.
That distinction matters because edge and embedded products often sit in the awkward middle ground between consumer convenience and enterprise criticality. They may be deployed like appliances, managed like infrastructure, and patched like consumer gadgets. When a kernel bug lands in a hardware-facing driver, the exposure depends less on the label attached to the device and more on whether the device uses the affected code path.
That approach is rational. In a codebase as complex as Linux, a reference-count bug is never just a reference-count bug. It can become a crash, a leak, a race, or a stepping stone to worse problems if later code assumes the object is still valid. By assigning and publishing the CVE, the ecosystem creates a shared label for what is ultimately a correctness failure with security consequences.
A second thing to watch is whether maintainers use this bug as a cue to audit other SPI drivers for mismatched managed and manual cleanup patterns. Those reviews are often where the real long-term value of a CVE emerges, because they can prevent the same mistake from appearing in neighboring code.
CVE-2026-31489 is not a headline-grabbing exploit story, but it is a very Linux kind of security issue: technical, precise, and rooted in the discipline of object ownership. The patch is small because the problem is local, yet the operational meaning is larger because kernel lifetimes are foundational. In modern systems, correctness in teardown is not a housekeeping detail; it is part of the security contract, and this fix is a reminder that the contract only works when the kernel keeps its promises exactly once.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
meson-spicc remove path and to the stable kernel fix chain already visible in upstream references Linux kernel treats object lifetime as a first-class security concern, especially in subsystems that must coordinate device discovery, registration, and teardown. The SPI framework is one of those subsystems. Its controller objects are registered, referenced, unregistered, and ultimately freed through tightly choreographed flows, and a small mismatch in that choreography can produce bugs that are more about trust and ownership than about flashy memory corruption. The kernel documentation for SPI makes clear that controllers are managed through struct spi_controller, while drivers bind and unbind through explicit registration and removal hooks.That context is essential for understanding why CVE-2026-31489 was assigned. The affected driver,
spi: meson-spicc, uses devm_spi_register_controller during probe. In the Linux device-managed model, devm_ helpers deliberately tie resource release to device teardown, which means cleanup is supposed to happen automatically when the device goes away. If a driver then manually decrements the same reference again in its own .remove callback, the kernel can end up releasing the object twice. In other words, the bug is not that the controller is hard to free; it is that it is being freed in two different ways that aly exclusive.The Linux kernel’s own CVE process helps explain why issues like this get tracked publicly even when they don’t map neatly onto a single exploit primitive. The kernel documentation explicitly notes that CVEs are often assigned once a fix is available and merged into a stable tree, and that the project tends to be cautious about security relevance because almost any kernel bug can become security-relevant in the wrong context. That philosophy matters here. A double-put is not a dramatic remote code execution bug, but it is exactly the sort of correctness failure that can become an availability problem or an exploit building block if it is left uncorrected.
Microsoft’s Security Update Guide surfaced the CVE quickly, which is increasingly normal for Linux issues that matter to enterprise administrators. In mixed fleets, a Linux kernel issue is no longer just “a Linux problem”; it is part of a broader vulnerability workflow that many organizations already use to track Windows, Azure, and Linux advisories together. That cross-platform visibility doe, but it absolutely changes the operational urgency.
 What the Vulnerability Is
What the Vulnerability Is
At a technical level, the flaw is straightforward: meson_spicc_probe registers the SPI controller with devm_spi_register_controller, which means the device-managed cleanup path already owns teardown. The driver’s meson_spicc_remove path then calls spi_controller_put again, effectively decrementing the reference a second time. The CVE record’s wording is blunt because the problem is bluference is being dropped twice.That kind of bug is easy to underestimate if you only look at the surface. The kernel is built on explicit ownership transfer, and reference counting is how it keeps shared objects from disappearing too early. A double-put can break that invariant in two different ways. In the best case, it results in a warning or a harmless underflow that exposes a code bug. In the worst case, it can free an object earlier than intended and leave later cleanup code touching memory it no longer owns.
Why double-put bugs are dangerous
The risk is not just “a crash” in the abstract. It is that the kernel can no longer trust its own bookkeeping once reference counts are wrong. That creates uncertainty about when an object disappears, whether callbacks still have valid state, and whether teardown paths remain safe under concurrency. In device drivers, those uncertainties are operationally nasty because they show up when a device is removed, reset, suspended, or hot-unplugged—exactly the moments when systems are already stressed.- Reference counts are ownership contracts.
- A second put can invalidate teardown assumptions.
- Driver removal paths are especially sensitive to cleanup ordering.
- Device-managed helpers are meant to reduce this exact class of bug.
- Manual cleanup after a managed registration is often a red flag.
How the Bug Happened
The CVE description points to a classic mismatch between two different resource-management styles.devm_spi_register_controller tells the device core to clean up the controller automatically. spi_controller_put is a manual reference release. Combining both on the same object is conceptually redundant and practically dangerous. The remove callback should not be doing a second release for an object am cleanup.This is one of those kernel bugs that feels mundane until you remember how much low-level system software depends on precise cleanup. A device-managed registration is meant to reduce boilerplate and eliminate hand-written release logic. If a driver author later adds a manual
put “just to be safe,” the result can be the opposite of safe. The driver becomes responsible for a resource twice, and the kernel can no longer distinguish intended release from accidental duplication.The teardown chain in plain language
Here is the lifecycle in simplified form:- The controller is registered with a managed helper during probe.
- The device core assumes responsibility for cleanup.
- The device is later removed.
- The devm subsystem releases the controller automatically.
- The driver’s
.removecallback also callsspi_controller_put. - The reference count is decremented twice.
It is also worth emphasizing that the issue is not hypothetical. The CVE record was published with stable references and commit links already attached, which is a strong sign that the fix had moved through the normal Linux security workflow rather than remaining a mere code re security, that distinction matters because it tells administrators the bug was important enough to be fixed, tracked, and backported rather than simply discussed.
Why the SPI Subsystem Makes This Matter
SPI controller code sits close to hardware, and hardware-facing code tends to punish sloppy lifecycle handling more quickly than higher-level software does. A controller object is not just a software abstraction; it is a representation of real bus state, device state, and driver ownership. When that state is torn down incorrectly, the fallout can affect more than one peripheral or one driver. It can destabilize the bus, confuse dependent drivers, or produce symptoms that look unrelated to the original bug.The SPI documentation makes clear that controllers and drivers are separate roles, with the controller object managing host-side behavior and the driver lifecycle handling registration and unbinding. That division of responsibility is useful, but it also means that a driver author has to respect the lifecycle contract precisely.
remove is the place to detach from the device, not to reassert ownership over resources that devm already knows how to free.Managed cleanup versus manual cleanup
Managed cleanup is a convenience, but it is also a promise. When code usesdevm_ helpers, it is saying the framework will own release order. Manual cleanup code that duplicates that work is a warning sign because it increases the risk of double free, double put, or teardown-order bugs. Those are not cosmetic mistakes. They are the kind of errors that can cause intermittent failures long after the original call path has finished.- Managed helpers reduce boilerplate.
- Manual cleanup must not duplicate managed release.
- Teardown order is part of the API contract.
- Reference-count errors are often delayed failures.
- Bus-level bugs can affect system stability even without exploitation.
The Fix and Why It Is Correct
The fix is conceptually simple: remove the extraspi_controller_put from meson_spicc_remove. Once the controller is registered through devm_spi_register_controller, devm teardown already handles the release. The remove path no longer needs to doand in fact should not do it at all.That simplicity is a strength. In kernel maintenance, the best fixes are often the ones that restore the original ownership model rather than layering on new special cases. This patch does exactly that. It does not redesign SPI. It does not alter controller semantics. It simply removes the duplicate release so that the remove path matches the registration path.
Why the patch is low-risk
A good fix for a kernel lifetime bug should be narrow, understandable, and easy to backport. This one checks all three boxes. The logic change is localized. It preserves the intended managed lifecycle. And it reduces the chance that downstream maintainers will need to reconcile multiple competing cleanup paths.- The patch is surgical.
- The ownership model becomes internally consistent again.
- Backporting should be straightforward.
- The fix avoids changing normal controller behavior.
- It removes a failure condition instead of introducing a workaround.
What It Means for Enterprise Systems
For enterprise administrators, the practical concern is not whether the bug sounds dramatic. It is whether the affected kernel line is in their fleet and whether the driver is present on systems that matter. That is the right lens for a bug like this. The issue is localized, but kernel teardown bugs can still become support incidents if they interfere with device removal, module unloading, or platform lifecycle operations.The enterprise impact is especially relevant for embedded, industrial, and appliance-style Linux systems, where the same kernel image may run for long periods with very little change. Those environments often use vendor kernels, not mainline builds, which means the time between upstream fix and practical exposure reduction can be longer than users expect. The existence of a published CVE does not guarantee a fleet is actually safe; it only means the issue has been formally identified and tracked.
Operational implications
A teardown bug is not always about immediate crashability. Sometimes it is about hidden instability that surfaces during maintenance windows, firmware updates, or hardware resets. That makes patch planning important even when the visible severity seems modest.- Module unload and device removal paths deserve patch attention.
- Managed resource bugs can appear only during maintenance events.
- Vendor kernels may lag upstream fixes.
- Appliance environments often keep drivers loaded for years.
- A “minor” CVE can still affect uptime and supportability.
Why It Matters for Consumer and Edge Devices
For everyday consumer desktops, the practical risk from this specific CVE is probably limited. Most users will never notice a SPI controller lifetime issue, and many consumer systems won’t exercise the affected driver in a way that exposes the bug at all. But consumer is not the same as irrelevant. Some devices that feel like consumer hardware are actually edge systems, routers, media platforms, or single-purpose appliances that depend heavily on embedded Linux.That distinction matters because edge and embedded products often sit in the awkward middle ground between consumer convenience and enterprise criticality. They may be deployed like appliances, managed like infrastructure, and patched like consumer gadgets. When a kernel bug lands in a hardware-facing driver, the exposure depends less on the label attached to the device and more on whether the device uses the affected code path.
Edge deployment risk
In edge environments, uptime is usually more important than elegance. That makes bugs in device teardown especially unpleasant because they can interfere with maintenance and recovery. If a system cannot safely remove or reinitialize a controller, it becomes harder to recover from transient failures or hardware replacement events.- Edge devices often run long-lived kernels.
- Hardware-specific drivers may be present for years.
- Maintenance events are where latent bugs show up.
- Consumer-branded devices can still carry enterprise-like risk.
- Patch timing matters more than product category labels.
The Broader Kernel Security Pattern
CVE-2026-31489 fits a familiar kernel pattern: a bug that is not inherently dramatic, but that reflects a failure to respect object ownership boundaries. The Linux kernel often turns these issues into CVEs because they matter not only for security in the traditional sense, but also for robustness, predictability, and safe recovery. The kernel documentation explicitly notes that even bugs whose exploitability is not obvious may be assigned CVEs once the fix exists, because the project prefers caution when there is a plausible security angle.That approach is rational. In a codebase as complex as Linux, a reference-count bug is never just a reference-count bug. It can become a crash, a leak, a race, or a stepping stone to worse problems if later code assumes the object is still valid. By assigning and publishing the CVE, the ecosystem creates a shared label for what is ultimately a correctness failure with security consequences.
Why these bugs get tracked
Kernel CVEs are often about trust boundaries, not just exploit primitives. The system depends on the assumption that an object is released exactly once, that teardown happens in the expected order, and that managed APIs are not duplicated by hand-written cleanup logic. When any of those assumptions fail, the risk is broader than one line of code.- Correctness bugs can still be security-relevant.
- Lifecycle mistakes are common in low-level code.
- Device-managed APIs reduce but do not eliminate human error.
- Availability issues are real security issues.
- Small fixes can prevent larger future bugs.
Strengths and Opportunities
The best thing about this vulnerability is that it was caught in a place where the kernel can fix it cleanly and cheaply. The patch is small, the logic is obvious, and the result restores the intended ownership model. That is exactly the kind of fix downstream maintainers want because it lowers regression risk while improving correctness.- The fix is narrow and easy to audit.
- The managed cleanup model remains intact.
- The change should backport cleanly.
- The bug is easy to explain to operators and vendors.
- It reinforces disciplined resource ownership in drivers.
- It gives maintainers a concrete example of a teardown anti-pattern.
- It improves confidence in driver lifecycle handling.
Risks and Concerns
The main risk is underestimation. A double-put can sound trivial to people outside kernel development, but in a low-level subsystem it is a genuine reliability bug. The second risk is patch lag: upstream fixes do not automatically reach all supported vendor kernels at the same time, and enterprise fleets often run backported builds that need explicit verification.- Vendors may backport at different speeds.
- Users may assume devm makes all cleanup safe automatically.
- Teardown bugs can hide until maintenance events.
- Embedded and appliance kernels may remain exposed longer.
- Administrators may not know the driver is present.
- A stability bug can be dismissed before it is patched.
- Reference-count bugs are notoriously easy to repeat elsewhere.
What to Watch Next
The next step is downstream adoption. Enterprises and vendors should verify not just that the CVE exists, but that their specific kernel builds include the fix. That is especially important for long-term-support distributions and vendor-supplied appliance kernels, where version numbers alone may not reveal whether the backport is present.A second thing to watch is whether maintainers use this bug as a cue to audit other SPI drivers for mismatched managed and manual cleanup patterns. Those reviews are often where the real long-term value of a CVE emerges, because they can prevent the same mistake from appearing in neighboring code.
Key items to monitor
- Stable backports across supported kernel branches
- Vendor advisories for appliance and embedded Linux
- Other drivers using
devm_registration plus manual release - Regression reports involving SPI controller teardown
- Fleet validation for systems that actually ship
meson-spicc - Distribution-specific security update timelines
CVE-2026-31489 is not a headline-grabbing exploit story, but it is a very Linux kind of security issue: technical, precise, and rooted in the discipline of object ownership. The patch is small because the problem is local, yet the operational meaning is larger because kernel lifetimes are foundational. In modern systems, correctness in teardown is not a housekeeping detail; it is part of the security contract, and this fix is a reminder that the contract only works when the kernel keeps its promises exactly once.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center